Endpoint Sources - Policies
Endpoint Sources - PoliciesEndpoint Sources - Policies
Note: The information in this topic applies to NetWitness Version 11.3 and later.
The  (Admin) > Endpoint Sources view contains two tabs: Groups and Policies.
(Admin) > Endpoint Sources view contains two tabs: Groups and Policies.
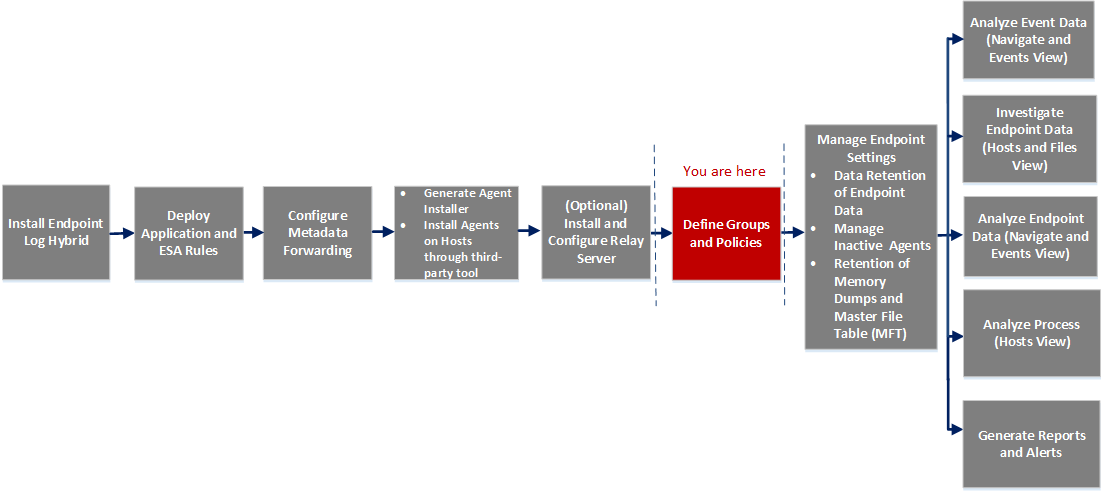
Workflow
What do you want to do?
*You can perform this task in the current view
Related Topics
Quick Look
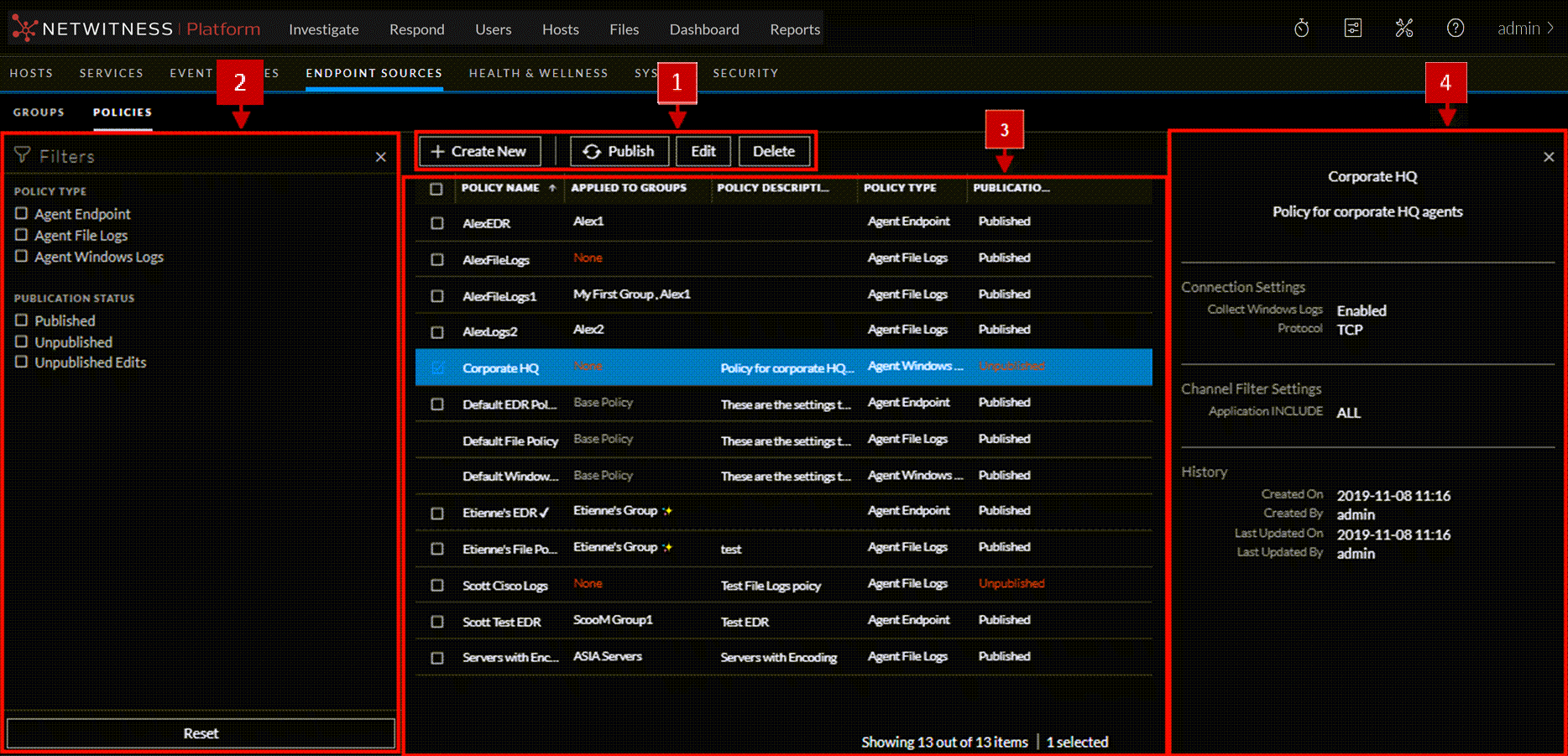
Below is an example of the Policies tab:
Create Policy
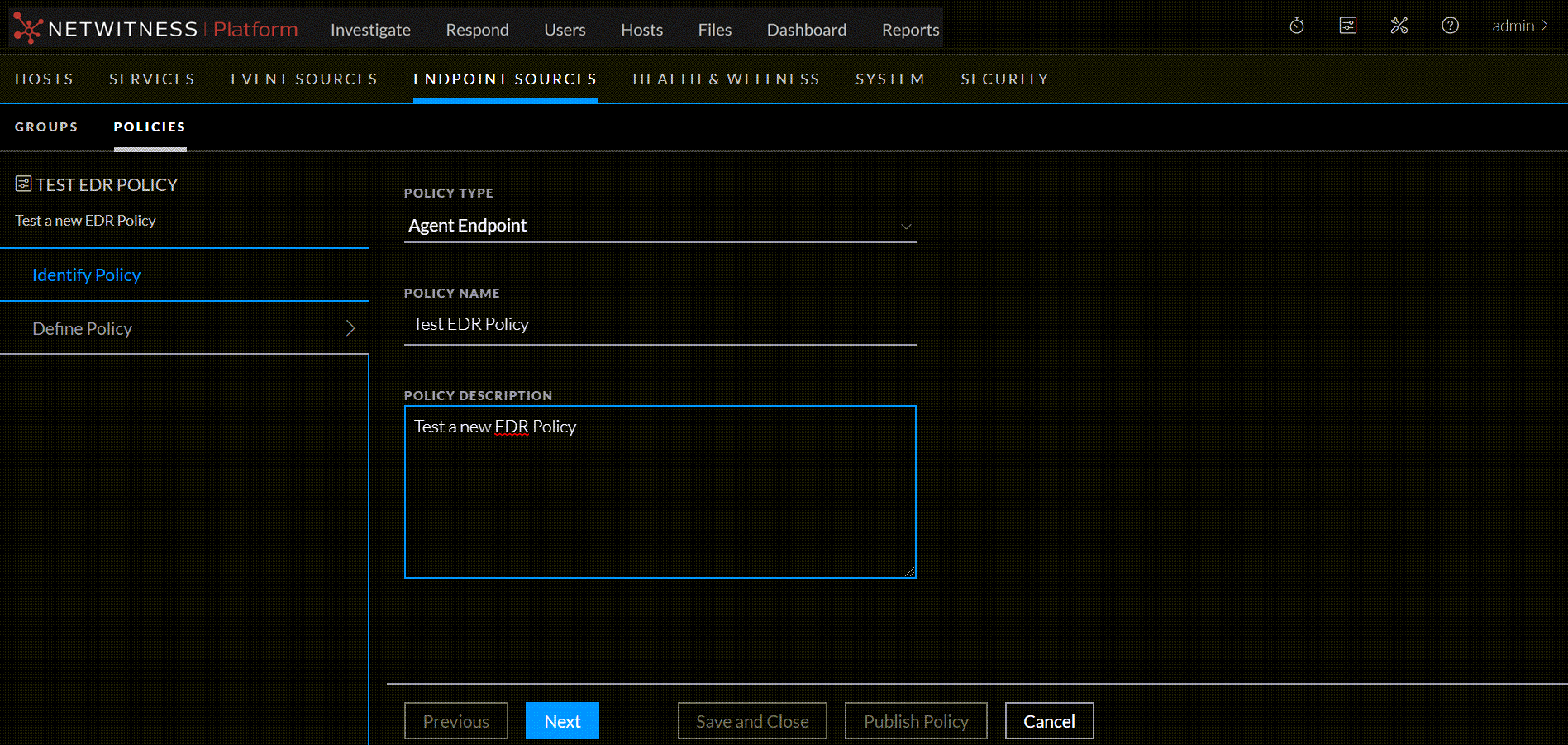
Below is an example of the Create Policy dialog. The table describes the information and options in the Create Policy dialog.
Panels for Log File PolicyPanels for Log File Policy
There are two panels for defining the parameters for an Agent Log File Policy: Define Connection Settings and Define File Policy Settings.
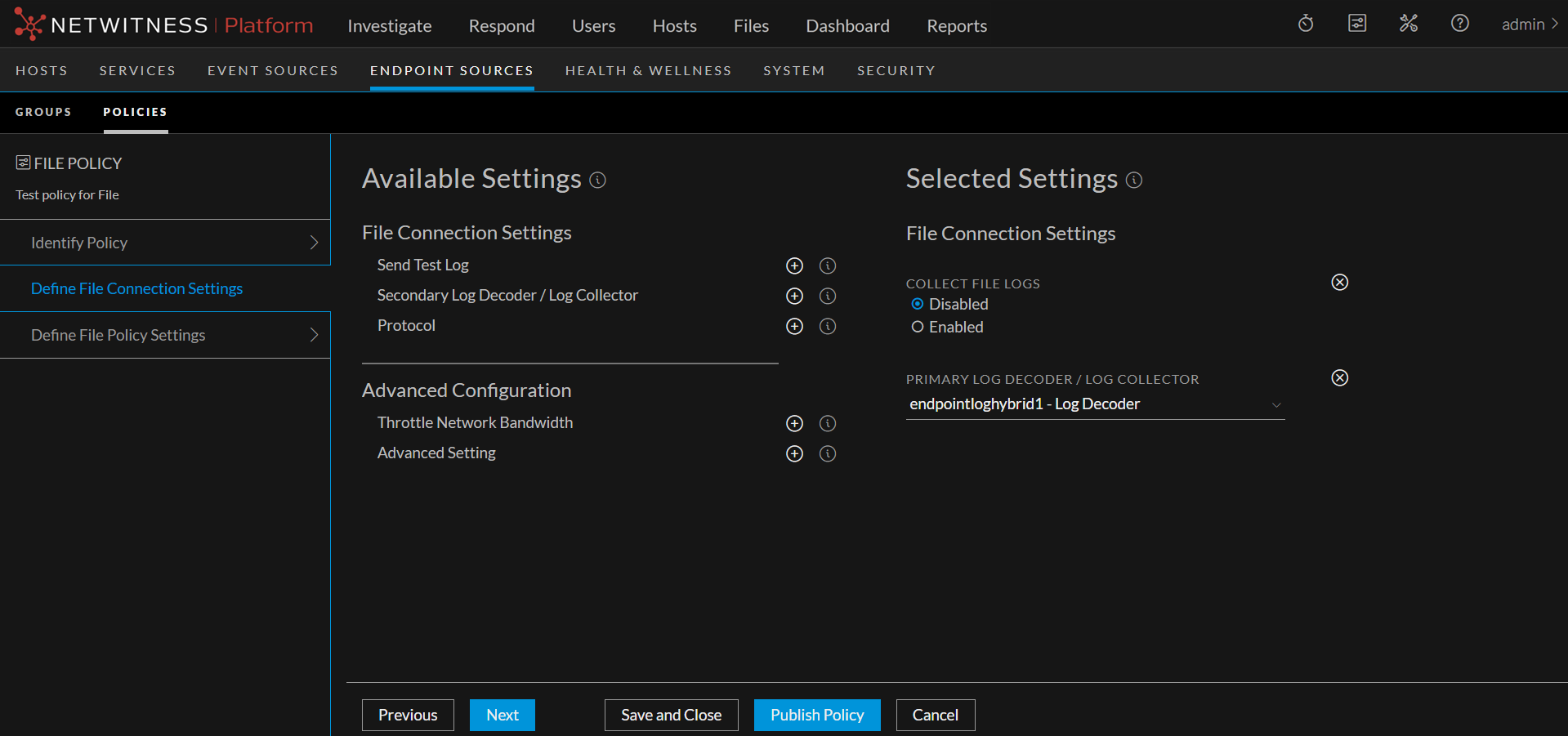
Define Connection Settings
Below is an example of Define Connection Settings panel. The table describes the information and available options.
Define File Policy Settings
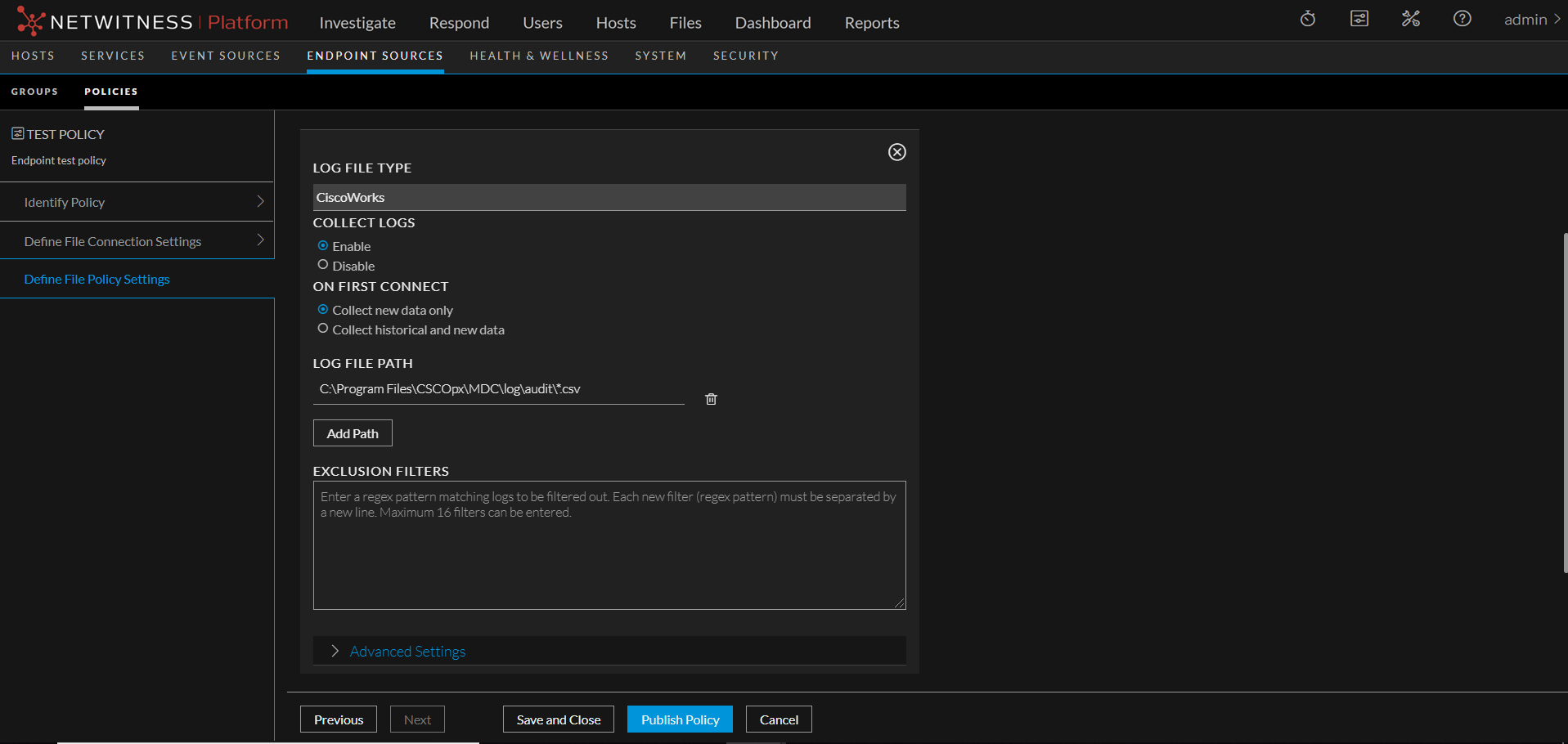
For a list of the currently supported types, see Currently Supported File Log Event Source Types.
Define Policy Panel for Agent Endpoint PolicyDefine Policy Panel for Agent Endpoint Policy
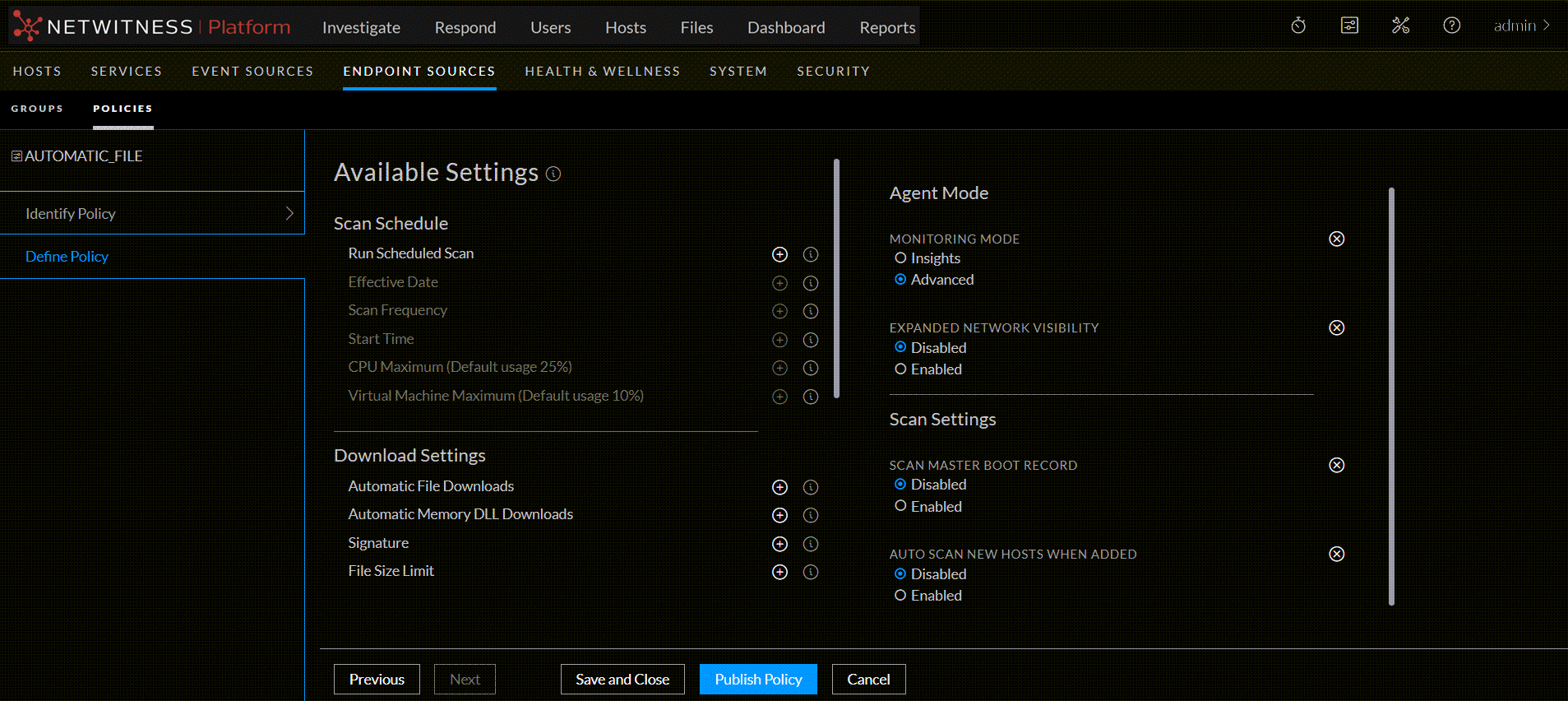
Below is an example of Define policy panel. The table describes the information and options for Agent Endpoint policy: