Files View
Files ViewFiles View
Note: The information in this topic applies to NetWitness Version 11.1 and later.
The Files view provides a holistic view of all files in your deployment. To access this view, go to Files. By default, the Files view displays 100 files. To display more files, click Load More at the bottom of the page.
You can either view files specific to an Endpoint server or view all files from multiple Endpoint servers by selecting the Endpoint Broker.
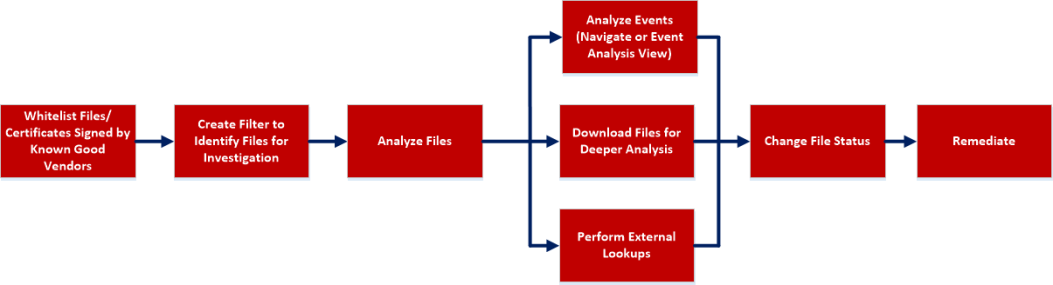
Workflow
What do you want to do?
*You can perform this task in the current view
Related Topics
- Focusing on Endpoint Analysis
- Investigating Hosts
- Analyzing Downloaded Files
- Analyzing Events
- Analyze Certificates
- Manage Blocked File Hashes
- Changing File Status or Remediate
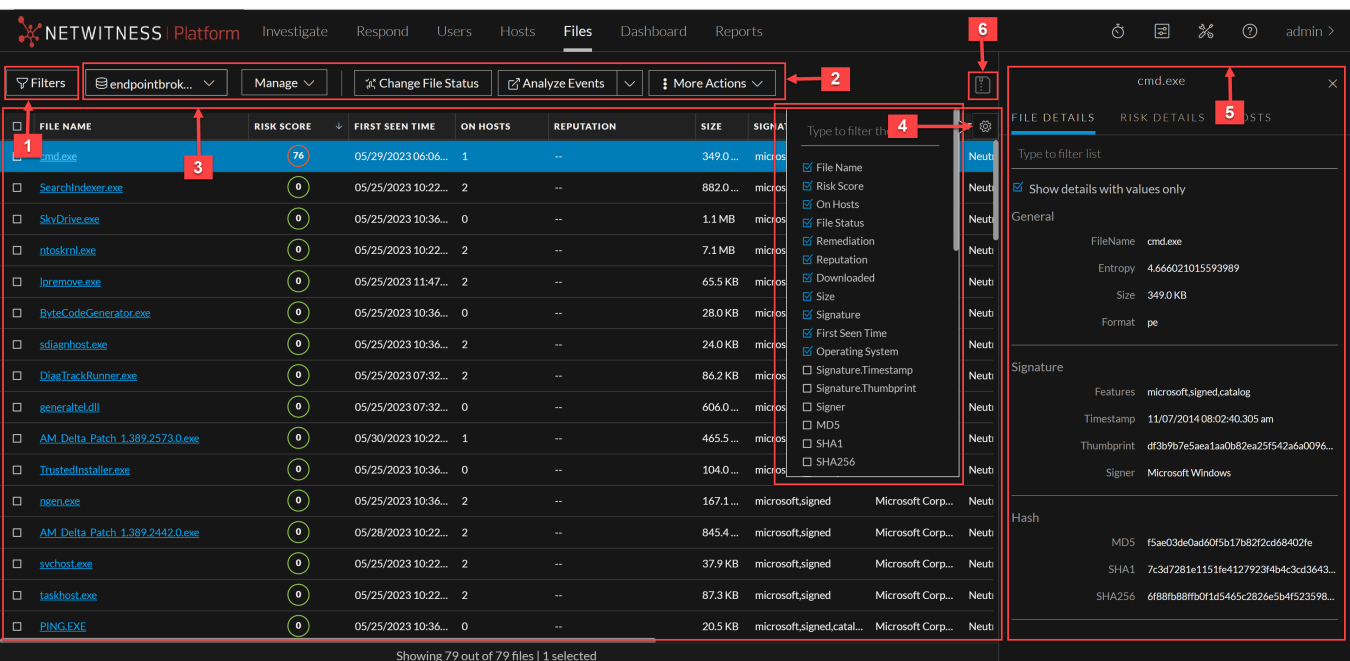
Quick Look
Below is an example of the Files view:
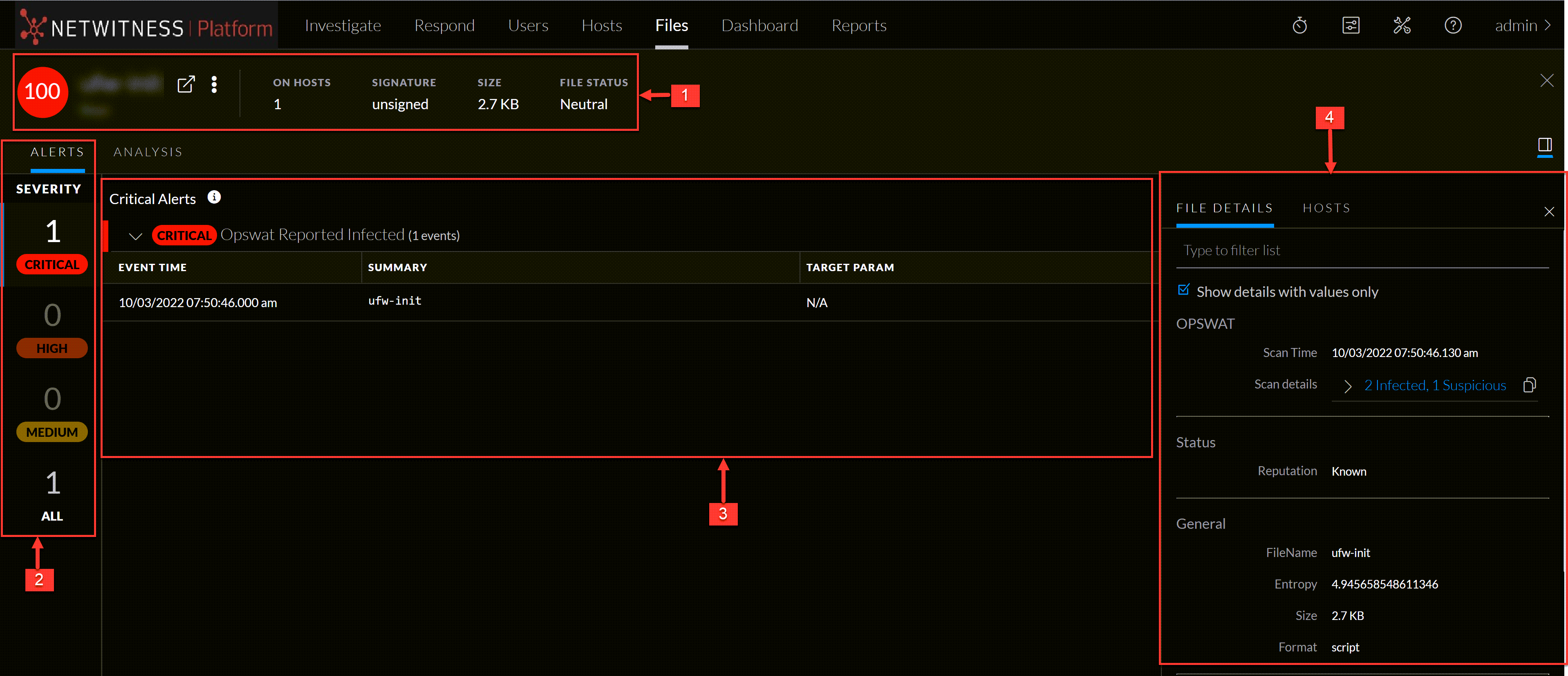
File Details View
To access this view, go to Files, and select a file. Below is an example of the File Details view: