Hosts View - Details Tab
Hosts View - Details TabHosts View - Details Tab
Note: The information in this topic applies to NetWitness Version 11.1 and later.
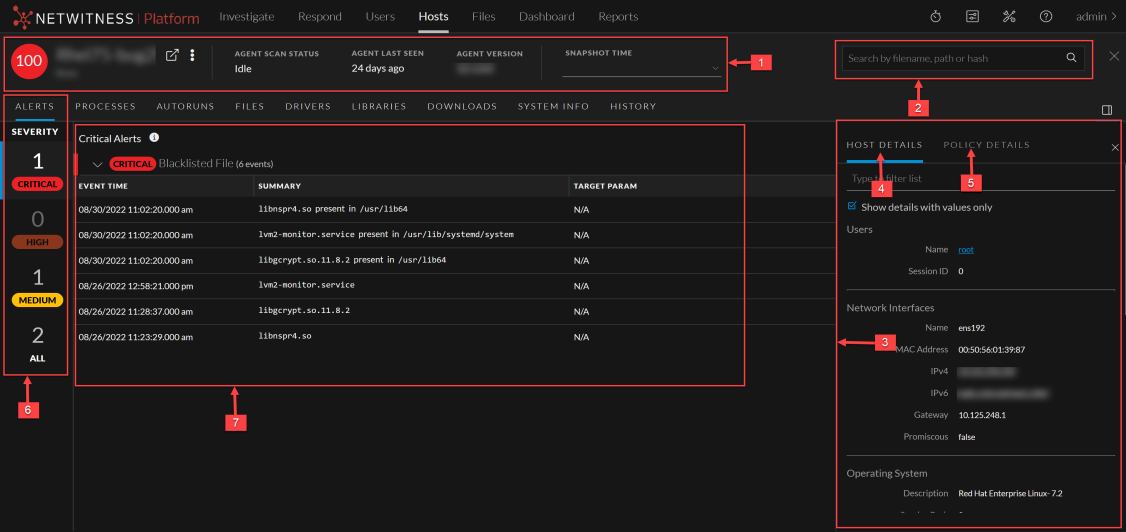
The Details tab provides details of the selected host. To access this view, go to Hosts view, and select a host.
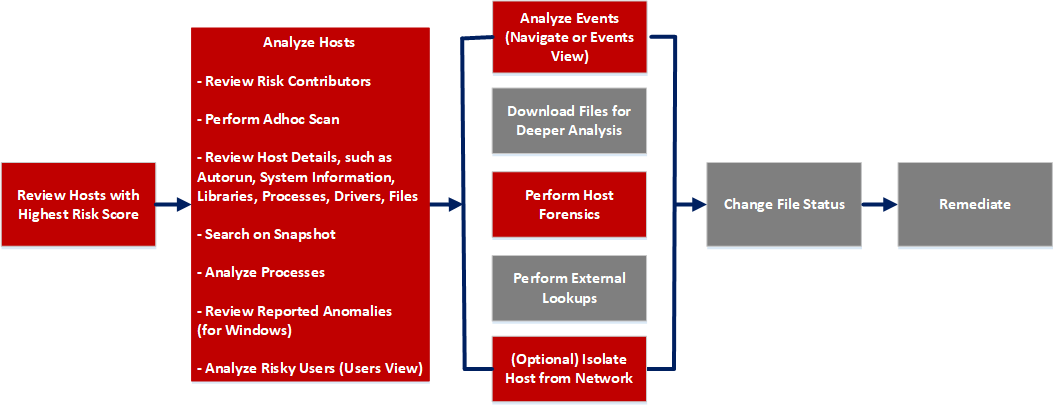
Workflow
What do you want to do?
*You can perform this task in the current view.
Related Topics
- Focusing on Endpoint Analysis
- Investigating Hosts
- Analyzing Events
- Performing Host Forensics
- Isolating Hosts from Network
Quick Look
Below is an example of the Details tab: