How to obtain and add the SSL Certificate PEM to NetWitness's truststore to connect to HTTPS enabled Feed Servers (recurring feeds)
Issue
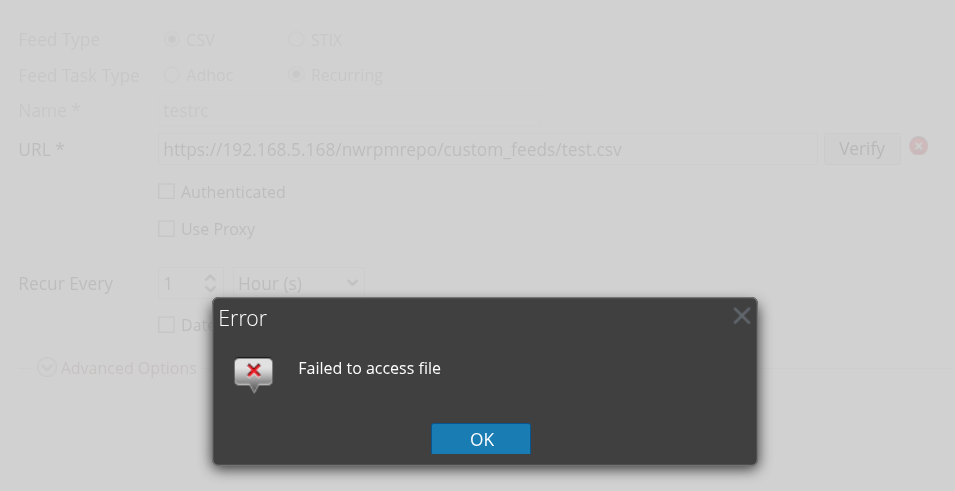
When attempting to validate a URL on the NetWitness Recurring Feed wizard interface, you get a message similar to this:
And messages similar to this in /var/netwitness/uax/logs/sa.log:
2025-06-23 18:36:32,629 [qtp2050019814-42214] ERROR com.rsa.smc.sa.core.service.DefaultHttpClientService - https://192.168.5.168/nwrpmrepo/custom_feeds/test.csv
javax.net.ssl.SSLPeerUnverifiedException: Certificate for <192.168.5.168> doesn't match any of the subject alternative names: []
OR
2025-06-04 19:32:07,452 [qtp2050019814-231616] ERROR com.rsa.smc.sa.core.service.DefaultHttpClientService - https://testserver:8000/nw_api/blocked_ips.csv
javax.net.ssl.SSLHandshakeException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
This is because the certificate for the Feed Repo server has not been imported to NetWitness' jetty cacerts truststore.
Tasks
Before importing into the NetWitnesds jetty cacerts truststore, you must first obtain the server's PEM certificate file, either from the system owner, or you may attempt to manually retrieve it using openssl. Below is an example of how to do so with the "openssl" utility, using https://google.com as an example:
Command:
openssl s_client -showcerts -connect www.google.com:443
Output:
Connecting to 142.251.16.104
CONNECTED(00000003)
depth=2 C=US, O=Google Trust Services LLC, CN=GTS Root R1
verify return:1
depth=1 C=US, O=Google Trust Services, CN=WR2
verify return:1
depth=0 CN=www.google.com
verify return:1
---
Certificate chain
0 s:CN=www.google.com
i:C=US, O=Google Trust Services, CN=WR2
a:PKEY: id-ecPublicKey, 256 (bit); sigalg: RSA-SHA256
v:NotBefore: Jun 2 08:37:21 2025 GMT; NotAfter: Aug 25 08:37:20 2025 GMT
-----BEGIN CERTIFICATE-----
MIIEVzCCAz+gAwIBAgIRAJa84vpaZta7CVk5RnZgjTEwDQYJKoZIhvcNAQELBQAw
OzELMAkGA1UEBhMCVVMxHjAcBgNVBAoTFUdvb2dsZSBUcnVzdCBTZXJ2aWNlczEM
MAoGA1UEAxMDV1IyMB4XDTI1MDYwMjA4MzcyMVoXDTI1MDgyNTA4MzcyMFowGTEX
MBUGA1UEAxMOd3d3Lmdvb2dsZS5jb20wWTATBgcqhkjOPQIBBggqhkjOPQMBBwNC
AASy2pq6BElHzPbnAPzc8t9qbTjvDMQqtmhdp3BM/cZwK7TFIqxM47nEeG9iujgr
yvYuOJmx4p5YY9NeAgHN/Sy+o4ICQTCCAj0wDgYDVR0PAQH/BAQDAgeAMBMGA1Ud
JQQMMAoGCCsGAQUFBwMBMAwGA1UdEwEB/wQCMAAwHQYDVR0OBBYEFNb5gNTqLqcU
antI+vGe4ZjDarJPMB8GA1UdIwQYMBaAFN4bHu15FdQ+NyTDIbvsNDltQrIwMFgG
CCsGAQUFBwEBBEwwSjAhBggrBgEFBQcwAYYVaHR0cDovL28ucGtpLmdvb2cvd3Iy
MCUGCCsGAQUFBzAChhlodHRwOi8vaS5wa2kuZ29vZy93cjIuY3J0MBkGA1UdEQQS
MBCCDnd3dy5nb29nbGUuY29tMBMGA1UdIAQMMAowCAYGZ4EMAQIBMDYGA1UdHwQv
MC0wK6ApoCeGJWh0dHA6Ly9jLnBraS5nb29nL3dyMi9vQkZZWWFoemdWSS5jcmww
ggEEBgorBgEEAdZ5AgQCBIH1BIHyAPAAdgDd3Mo0ldfhFgXnlTL6x5/4PRxQ39sA
OhQSdgosrLvIKgAAAZcwALX+AAAEAwBHMEUCIQC1/t8kNXv/dBkecXrDcefKda9h
sz9+6saUnFKXjG50RgIgMorAX/uvslpLx1fsHzM2cO/IjVtffIJQVVjzVR3WBI8A
dgDM+w9qhXEJZf6Vm1PO6bJ8IumFXA2XjbapflTA/kwNsAAAAZcwALbRAAAEAwBH
MEUCIQCEfx3rL+LxW+g3Q4OsLN30yJx1EIbGj57aURh08eoQrgIgMnJ8MscBMv6F
0QN08hMtnu+Do6AvX6IIsxnz2o/VQRswDQYJKoZIhvcNAQELBQADggEBAFFVoF4j
dyCWmgNbxNzS7+NEIV5Q8pgODvx98g9sqv8vASBkvVlcxAqZJtfbNg6TwunkZbTl
HcVR/0RYffYs2loGvNyVTXkcXOkxYejLA2jI1C5o7ZQdTc1oO+YwQn/r7VPj8mes
Qj10+3Z7T3p2LlZjbgZF5fa5bUzHHyVVhSDC9tZVVDul2+srxZ3NRE/IXvJN3ApT
IHiFVq7JhpnQZ+XCrIHfmftj3s4Q0N4IScAZtlqdfZqMJ6boLfLW3dHtnYP5ci/M
AMZ3V4WUCr/X4gIPgpeKItsRdmdnEyE7JakanN2uXkWg86ScSZGuGxag2Lk7SveN
TAdu7/69Ac428Ks=
-----END CERTIFICATE-----
1 s:C=US, O=Google Trust Services, CN=WR2
i:C=US, O=Google Trust Services LLC, CN=GTS Root R1
a:PKEY: rsaEncryption, 2048 (bit); sigalg: RSA-SHA256
v:NotBefore: Dec 13 09:00:00 2023 GMT; NotAfter: Feb 20 14:00:00 2029 GMT
-----BEGIN CERTIFICATE-----
MIIFCzCCAvOgAwIBAgIQf/AFoHxM3tEArZ1mpRB7mDANBgkqhkiG9w0BAQsFADBH
MQswCQYDVQQGEwJVUzEiMCAGA1UEChMZR29vZ2xlIFRydXN0IFNlcnZpY2VzIExM
QzEUMBIGA1UEAxMLR1RTIFJvb3QgUjEwHhcNMjMxMjEzMDkwMDAwWhcNMjkwMjIw
MTQwMDAwWjA7MQswCQYDVQQGEwJVUzEeMBwGA1UEChMVR29vZ2xlIFRydXN0IFNl
cnZpY2VzMQwwCgYDVQQDEwNXUjIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
AoIBAQCp/5x/RR5wqFOfytnlDd5GV1d9vI+aWqxG8YSau5HbyfsvAfuSCQAWXqAc
+MGr+XgvSszYhaLYWTwO0xj7sfUkDSbutltkdnwUxy96zqhMt/TZCPzfhyM1IKji
aeKMTj+xWfpgoh6zySBTGYLKNlNtYE3pAJH8do1cCA8Kwtzxc2vFE24KT3rC8gIc
LrRjg9ox9i11MLL7q8Ju26nADrn5Z9TDJVd06wW06Y613ijNzHoU5HEDy01hLmFX
xRmpC5iEGuh5KdmyjS//V2pm4M6rlagplmNwEmceOuHbsCFx13ye/aoXbv4r+zgX
FNFmp6+atXDMyGOBOozAKql2N87jAgMBAAGjgf4wgfswDgYDVR0PAQH/BAQDAgGG
MB0GA1UdJQQWMBQGCCsGAQUFBwMBBggrBgEFBQcDAjASBgNVHRMBAf8ECDAGAQH/
AgEAMB0GA1UdDgQWBBTeGx7teRXUPjckwyG77DQ5bUKyMDAfBgNVHSMEGDAWgBTk
rysmcRorSCeFL1JmLO/wiRNxPjA0BggrBgEFBQcBAQQoMCYwJAYIKwYBBQUHMAKG
GGh0dHA6Ly9pLnBraS5nb29nL3IxLmNydDArBgNVHR8EJDAiMCCgHqAchhpodHRw
Oi8vYy5wa2kuZ29vZy9yL3IxLmNybDATBgNVHSAEDDAKMAgGBmeBDAECATANBgkq
hkiG9w0BAQsFAAOCAgEARXWL5R87RBOWGqtY8TXJbz3S0DNKhjO6V1FP7sQ02hYS
TL8Tnw3UVOlIecAwPJQl8hr0ujKUtjNyC4XuCRElNJThb0Lbgpt7fyqaqf9/qdLe
SiDLs/sDA7j4BwXaWZIvGEaYzq9yviQmsR4ATb0IrZNBRAq7x9UBhb+TV+PfdBJT
DhEl05vc3ssnbrPCuTNiOcLgNeFbpwkuGcuRKnZc8d/KI4RApW//mkHgte8y0YWu
ryUJ8GLFbsLIbjL9uNrizkqRSvOFVU6xddZIMy9vhNkSXJ/UcZhjJY1pXAprffJB
vei7j+Qi151lRehMCofa6WBmiA4fx+FOVsV2/7R6V2nyAiIJJkEd2nSi5SnzxJrl
Xdaqev3htytmOPvoKWa676ATL/hzfvDaQBEcXd2Ppvy+275W+DKcH0FBbX62xevG
iza3F4ydzxl6NJ8hk8R+dDXSqv1MbRT1ybB5W0k8878XSOjvmiYTDIfyc9acxVJr
Y/cykHipa+te1pOhv7wYPYtZ9orGBV5SGOJm4NrB3K1aJar0RfzxC3ikr7Dyc6Qw
qDTBU39CluVIQeuQRgwG3MuSxl7zRERDRilGoKb8uY45JzmxWuKxrfwT/478JuHU
/oTxUFqOl2stKnn7QGTq8z29W+GgBLCXSBxC9epaHM0myFH/FJlniXJfHeytWt0=
-----END CERTIFICATE-----
2 s:C=US, O=Google Trust Services LLC, CN=GTS Root R1
i:C=BE, O=GlobalSign nv-sa, OU=Root CA, CN=GlobalSign Root CA
a:PKEY: rsaEncryption, 4096 (bit); sigalg: RSA-SHA256
v:NotBefore: Jun 19 00:00:42 2020 GMT; NotAfter: Jan 28 00:00:42 2028 GMT
-----BEGIN CERTIFICATE-----
MIIFYjCCBEqgAwIBAgIQd70NbNs2+RrqIQ/E8FjTDTANBgkqhkiG9w0BAQsFADBX
MQswCQYDVQQGEwJCRTEZMBcGA1UEChMQR2xvYmFsU2lnbiBudi1zYTEQMA4GA1UE
CxMHUm9vdCBDQTEbMBkGA1UEAxMSR2xvYmFsU2lnbiBSb290IENBMB4XDTIwMDYx
OTAwMDA0MloXDTI4MDEyODAwMDA0MlowRzELMAkGA1UEBhMCVVMxIjAgBgNVBAoT
GUdvb2dsZSBUcnVzdCBTZXJ2aWNlcyBMTEMxFDASBgNVBAMTC0dUUyBSb290IFIx
MIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAthECix7joXebO9y/lD63
ladAPKH9gvl9MgaCcfb2jH/76Nu8ai6Xl6OMS/kr9rH5zoQdsfnFl97vufKj6bwS
iV6nqlKr+CMny6SxnGPb15l+8Ape62im9MZaRw1NEDPjTrETo8gYbEvs/AmQ351k
KSUjB6G00j0uYODP0gmHu81I8E3CwnqIiru6z1kZ1q+PsAewnjHxgsHA3y6mbWwZ
DrXYfiYaRQM9sHmklCitD38m5agI/pboPGiUU+6DOogrFZYJsuB6jC511pzrp1Zk
j5ZPaK49l8KEj8C8QMALXL32h7M1bKwYUH+E4EzNktMg6TO8UpmvMrUpsyUqtEj5
cuHKZPfmghCN6J3Cioj6OGaK/GP5Afl4/Xtcd/p2h/rs37EOeZVXtL0m79YB0esW
CruOC7XFxYpVq9Os6pFLKcwZpDIlTirxZUTQAs6qzkm06p98g7BAe+dDq6dso499
iYH6TKX/1Y7DzkvgtdizjkXPdsDtQCv9Uw+wp9U7DbGKogPeMa3Md+pvez7W35Ei
Eua++tgy/BBjFFFy3l3WFpO9KWgz7zpm7AeKJt8T11dleCfeXkkUAKIAf5qoIbap
sZWwpbkNFhHax2xIPEDgfg1azVY80ZcFuctL7TlLnMQ/0lUTbiSw1nH69MG6zO0b
9f6BQdgAmD06yK56mDcYBZUCAwEAAaOCATgwggE0MA4GA1UdDwEB/wQEAwIBhjAP
BgNVHRMBAf8EBTADAQH/MB0GA1UdDgQWBBTkrysmcRorSCeFL1JmLO/wiRNxPjAf
BgNVHSMEGDAWgBRge2YaRQ2XyolQL30EzTSo//z9SzBgBggrBgEFBQcBAQRUMFIw
JQYIKwYBBQUHMAGGGWh0dHA6Ly9vY3NwLnBraS5nb29nL2dzcjEwKQYIKwYBBQUH
MAKGHWh0dHA6Ly9wa2kuZ29vZy9nc3IxL2dzcjEuY3J0MDIGA1UdHwQrMCkwJ6Al
oCOGIWh0dHA6Ly9jcmwucGtpLmdvb2cvZ3NyMS9nc3IxLmNybDA7BgNVHSAENDAy
MAgGBmeBDAECATAIBgZngQwBAgIwDQYLKwYBBAHWeQIFAwIwDQYLKwYBBAHWeQIF
AwMwDQYJKoZIhvcNAQELBQADggEBADSkHrEoo9C0dhemMXoh6dFSPsjbdBZBiLg9
NR3t5P+T4Vxfq7vqfM/b5A3Ri1fyJm9bvhdGaJQ3b2t6yMAYN/olUazsaL+yyEn9
WprKASOshIArAoyZl+tJaox118fessmXn1hIVw41oeQa1v1vg4Fv74zPl6/AhSrw
9U5pCZEt4Wi4wStz6dTZ/CLANx8LZh1J7QJVj2fhMtfTJr9w4z30Z209fOU0iOMy
+qduBmpvvYuR7hZL6Dupszfnw0Skfths18dG9ZKb59UhvmaSGZRVbNQpsg3BZlvi
d0lIKO2d1xozclOzgjXPYovJJIultzkMu34qQb9Sz/yilrbCgj8=
-----END CERTIFICATE-----
---
Server certificate
subject=CN=www.google.com
issuer=C=US, O=Google Trust Services, CN=WR2
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: ECDSA
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 4106 bytes and written 405 bytes
Verification: OK
---
New, TLSv1.3, Cipher is TLS_AES_256_GCM_SHA384
Server public key is 256 bit
This TLS version forbids renegotiation.
Compression: NONE
Expansion: NONE
No ALPN negotiated
Early data was not sent
Verify return code: 0 (ok)
---
In the above example, we want to take the first certificate and copy it to it's own file. This would be the portion that begins with "-----BEGIN CERTIFICATE-----" and ends with "-----END CERTIFICATE-----"
For example:
-----BEGIN CERTIFICATE-----
MIIEVzCCAz+gAwIBAgIRAJa84vpaZta7CVk5RnZgjTEwDQYJKoZIhvcNAQELBQAw
OzELMAkGA1UEBhMCVVMxHjAcBgNVBAoTFUdvb2dsZSBUcnVzdCBTZXJ2aWNlczEM
MAoGA1UEAxMDV1IyMB4XDTI1MDYwMjA4MzcyMVoXDTI1MDgyNTA4MzcyMFowGTEX
MBUGA1UEAxMOd3d3Lmdvb2dsZS5jb20wWTATBgcqhkjOPQIBBggqhkjOPQMBBwNC
AASy2pq6BElHzPbnAPzc8t9qbTjvDMQqtmhdp3BM/cZwK7TFIqxM47nEeG9iujgr
yvYuOJmx4p5YY9NeAgHN/Sy+o4ICQTCCAj0wDgYDVR0PAQH/BAQDAgeAMBMGA1Ud
JQQMMAoGCCsGAQUFBwMBMAwGA1UdEwEB/wQCMAAwHQYDVR0OBBYEFNb5gNTqLqcU
antI+vGe4ZjDarJPMB8GA1UdIwQYMBaAFN4bHu15FdQ+NyTDIbvsNDltQrIwMFgG
CCsGAQUFBwEBBEwwSjAhBggrBgEFBQcwAYYVaHR0cDovL28ucGtpLmdvb2cvd3Iy
MCUGCCsGAQUFBzAChhlodHRwOi8vaS5wa2kuZ29vZy93cjIuY3J0MBkGA1UdEQQS
MBCCDnd3dy5nb29nbGUuY29tMBMGA1UdIAQMMAowCAYGZ4EMAQIBMDYGA1UdHwQv
MC0wK6ApoCeGJWh0dHA6Ly9jLnBraS5nb29nL3dyMi9vQkZZWWFoemdWSS5jcmww
ggEEBgorBgEEAdZ5AgQCBIH1BIHyAPAAdgDd3Mo0ldfhFgXnlTL6x5/4PRxQ39sA
OhQSdgosrLvIKgAAAZcwALX+AAAEAwBHMEUCIQC1/t8kNXv/dBkecXrDcefKda9h
sz9+6saUnFKXjG50RgIgMorAX/uvslpLx1fsHzM2cO/IjVtffIJQVVjzVR3WBI8A
dgDM+w9qhXEJZf6Vm1PO6bJ8IumFXA2XjbapflTA/kwNsAAAAZcwALbRAAAEAwBH
MEUCIQCEfx3rL+LxW+g3Q4OsLN30yJx1EIbGj57aURh08eoQrgIgMnJ8MscBMv6F
0QN08hMtnu+Do6AvX6IIsxnz2o/VQRswDQYJKoZIhvcNAQELBQADggEBAFFVoF4j
dyCWmgNbxNzS7+NEIV5Q8pgODvx98g9sqv8vASBkvVlcxAqZJtfbNg6TwunkZbTl
HcVR/0RYffYs2loGvNyVTXkcXOkxYejLA2jI1C5o7ZQdTc1oO+YwQn/r7VPj8mes
Qj10+3Z7T3p2LlZjbgZF5fa5bUzHHyVVhSDC9tZVVDul2+srxZ3NRE/IXvJN3ApT
IHiFVq7JhpnQZ+XCrIHfmftj3s4Q0N4IScAZtlqdfZqMJ6boLfLW3dHtnYP5ci/M
AMZ3V4WUCr/X4gIPgpeKItsRdmdnEyE7JakanN2uXkWg86ScSZGuGxag2Lk7SveN
TAdu7/69Ac428Ks=
-----END CERTIFICATE-----
Save that to a file on the Admin Server/Node-Zero under /root/ as:
"import-cert-hostname.pem"
[root@NEW-NW11-NW-NODE-ZERO ~]# ls -lrth /root/import-cert-google.pem
-rw-r--r--. 1 root root 1.6K Jun 23 18:44 /root/import-cert-google.pem
Inspect the cert with openssl to ensure it was extracted properly:
[root@NEW-NW11-NW-NODE-ZERO ~]# openssl x509 -noout -subject -in /root/import-cert-google.pem -text | grep "Not\|Alt\|CN\|Name" -a1
subject=CN = www.google.com
Certificate:
--
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = US, O = Google Trust Services, CN = WR2
Validity
Not Before: Jun 2 08:37:21 2025 GMT
Not After : Aug 25 08:37:20 2025 GMT
Subject: CN = www.google.com
Subject Public Key Info:
--
X509v3 Subject Alternative Name:
DNS:www.google.com
--
Note that the Certificate dates must be within range, and the CN or Subject Alternative Name must match the destination host name you'll be using in the Recurring Feed's wizard.
Once you have the certificate in the appropriate PEM format, move on to the Resolution steps below
Resolution
- Take a backup of the cacerts file:
cp /etc/pki/ca-trust/extracted/java/cacerts /etc/pki/ca-trust/extracted/java/cacerts.BAK - Note how many current certificates are currently in the cacerts file with this command:
[root@NEW-NW11-NW-NODE-ZERO ~]# keytool -list -keystore /etc/pki/ca-trust/extracted/java/cacerts -storepass changeit | wc -l
Warning: use -cacerts option to access cacerts keystore
307
- In the above scenario, I have 307 entries
- Import your new certificate from your PEM file. Be sure to add an alias so it's easy to confirm. The Alias is simply a friendly name and does not need to match the hostname. It will ask you to type "yes" to confirm:
keytool -import -file /root/import-cert-google.pem -alias LabGoogleTest -keystore /etc/pki/ca-trust/extracted/java/cacerts -storepass changeit
.
.
.
.
.
9: ObjectId: 2.5.29.17 Criticality=false
SubjectAlternativeName [
DNSName: www.google.com
]
#10: ObjectId: 2.5.29.14 Criticality=false
SubjectKeyIdentifier [
KeyIdentifier [
0000: D6 F9 80 D4 EA 2E A7 14 6A 7B 48 FA F1 9E E1 98 ........j.H.....
0010: C3 6A B2 4F .j.O
]
]
Trust this certificate? [no]: yes
Certificate was added to keystore - Check again to see if the count of certs has incremented:
[root@NEW-NW11-NW-NODE-ZERO ~]# keytool -list -keystore /etc/pki/ca-trust/extracted/java/cacerts -storepass changeit | wc -l
Warning: use -cacerts option to access cacerts keystore
309
- Note that I have 309 now
- You can also look for the Alias:
[root@NEW-NW11-NW-NODE-ZERO ~]# keytool -list -keystore /etc/pki/ca-trust/extracted/java/cacerts -storepass changeit | grep -i labgoogletest
Warning: use -cacerts option to access cacerts keystore
labgoogletest, Jun 23, 2025, trustedCertEntry, - Restart jetty:
systemctl restart jetty
Once Jetty is back up, you should be able to successfully connect and retrieve the feed from your feed server via the Recurring Feed Wizard.
Product Details
NetWitness Product Set: NetWitness Logs & Network
NetWitness Product/Service Type: NetWitness Content, Feeds, Live
NetWitness Version/Condition: 12.x
Platform: CentOS , AlmaLinux
Approval Reviewer Queue
Technical approval queue