How to properly configure and test a Global Notification ESA output for a Script
Issue
If you configure Global Notification for Script, you may face issues executing the script even though the ESA rule is fired.In this case, It is hard to find the root cause because there is no error message appeared regarding this issue.
There is a document on how to configure("Configure Script as a Notification" in the System Configuration Guide), but it is not enough to cover this topic.
Resolution
To configure successfully, you need to consider followings1. You can use "Default Script Template" as a template.
2. UI pop-up appears when you define script as shown below "Script will be saved to /opt/rsa/esa/scripts" but it is actually saved to mongo db since 11.3.

3. You must locate the script under /tmp, otherwise script will not execute.
4. In case of bash shell, you can use following syntax(echo $*) to get all ESA parameters below and this is sample script output.

#!/bin/bash
echo $(date) > /tmp/bash_test.txt
echo $* >> /tmp/bash.test.txt
exit 0
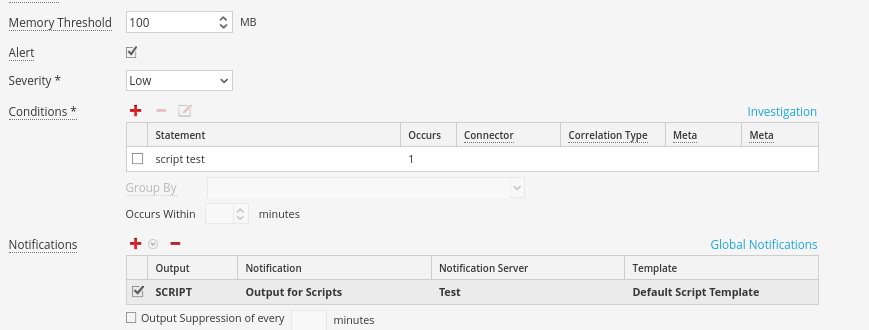
Example Rule Config:
echo $(date) > /tmp/bash_test.txt
echo $* >> /tmp/bash.test.txt
exit 0
 This will write the script output to /tmp/bash_test.txt:
This will write the script output to /tmp/bash_test.txt:
[root@NEW-NW11-NW-NODE-ZERO tmp]# ls -lrth /tmp/ | grep bash
-rw-r--r--. 1 netwitness netwitness 29 Apr 29 21:49 bash_test.txt
-rw-r--r--. 1 netwitness netwitness 1.4M Apr 29 21:49 bash.test.txt
-rw-r--r--. 1 netwitness netwitness 29 Apr 29 21:49 bash_test.txt
-rw-r--r--. 1 netwitness netwitness 1.4M Apr 29 21:49 bash.test.txt
With the resulting output actions looking like:
# cat /tmp/bash_test.txt
Tue Dec 7 08:17:57 UTC 2021
{"id": "41a15340-bb5e-45f9-a049-e2b49f17dca3", "severity":3, "time": "2021-12-07T08:17:57Z", "module_name" : "CS support rule for Script", "events": [{"analysis_session" : ["request no payload", "response no payload", "ratio high transmitted", "host not listening", "zero payload", "session size 0-5k"], "attack_tactic" : "exfiltration", "attack_technique" : "data transfer size limits", "attack_tid" : "T1030", "capture_port" : "eth0", "com_rsa_netwitness_streams_arrival_sequence" : 11, "com_rsa_netwitness_streams_arrival_timestamp" : 1638865076236, "com_rsa_netwitness_streams_source_trail" : ["admin@192.168.26.105:50005"], "com_rsa_netwitness_streams_stream" : "c-s-support-sa-managed-stream", "community_id" : "1:xa3WM28Id5DyRYPnARWOx/BHJ3M=", "did" : "pkthybrid", "direction" : "lateral", "esa_time" : 1638865077237, "eth_dst" : "00:50:56:01:36:82", "eth_dst_vendor" : "VMware, Inc.", "eth_src" : "00:50:56:01:46:75", "eth_src_vendor" : "VMware, Inc.", "eth_type" : 2048, "event_source_id" : "192.168.26.105:50005:1292845", "feed_name" : ["investigation", "investigation", "investigation", "investigation", "investigation", "investigation"], "inv_category" : ["operations", "operations", "operations", "operations", "operations", "operations"], "inv_context" : ["event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis"], "ip_dst" : "192.168.26.109", "ip_proto" : 6, "ip_src" : "192.168.26.105", "lifetime" : 0, "medium" : 1, "netname" : ["private src", "private dst"], "packets" : 2, "payload" : 0, "payload_req" : 0, "payload_res" : 0, "rid" : 1292844, "service" : 0, "sessionid" : 1292845, "size" : 134, "streams" : 2, "tcp_dstport" : 4505, "tcp_flags" : 22, "tcp_flags_desc" : "syn", "tcp_srcport" : 34108, "tcpflags" : "syn", "time" : 1638865011000}]}
Tue Dec 7 08:17:57 UTC 2021
{"id": "41a15340-bb5e-45f9-a049-e2b49f17dca3", "severity":3, "time": "2021-12-07T08:17:57Z", "module_name" : "CS support rule for Script", "events": [{"analysis_session" : ["request no payload", "response no payload", "ratio high transmitted", "host not listening", "zero payload", "session size 0-5k"], "attack_tactic" : "exfiltration", "attack_technique" : "data transfer size limits", "attack_tid" : "T1030", "capture_port" : "eth0", "com_rsa_netwitness_streams_arrival_sequence" : 11, "com_rsa_netwitness_streams_arrival_timestamp" : 1638865076236, "com_rsa_netwitness_streams_source_trail" : ["admin@192.168.26.105:50005"], "com_rsa_netwitness_streams_stream" : "c-s-support-sa-managed-stream", "community_id" : "1:xa3WM28Id5DyRYPnARWOx/BHJ3M=", "did" : "pkthybrid", "direction" : "lateral", "esa_time" : 1638865077237, "eth_dst" : "00:50:56:01:36:82", "eth_dst_vendor" : "VMware, Inc.", "eth_src" : "00:50:56:01:46:75", "eth_src_vendor" : "VMware, Inc.", "eth_type" : 2048, "event_source_id" : "192.168.26.105:50005:1292845", "feed_name" : ["investigation", "investigation", "investigation", "investigation", "investigation", "investigation"], "inv_category" : ["operations", "operations", "operations", "operations", "operations", "operations"], "inv_context" : ["event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis", "event analysis", "protocol analysis"], "ip_dst" : "192.168.26.109", "ip_proto" : 6, "ip_src" : "192.168.26.105", "lifetime" : 0, "medium" : 1, "netname" : ["private src", "private dst"], "packets" : 2, "payload" : 0, "payload_req" : 0, "payload_res" : 0, "rid" : 1292844, "service" : 0, "sessionid" : 1292845, "size" : 134, "streams" : 2, "tcp_dstport" : 4505, "tcp_flags" : 22, "tcp_flags_desc" : "syn", "tcp_srcport" : 34108, "tcpflags" : "syn", "time" : 1638865011000}]}
Product Details
NetWitness Product Set: NetWitness PlatformNetWitness Product/Service Type: Log Decoder
NetWitness Version/Condition: 11.x, 12.x
Platform: CentOS 7 / Alma
Approval Reviewer Queue
Technical approval queue