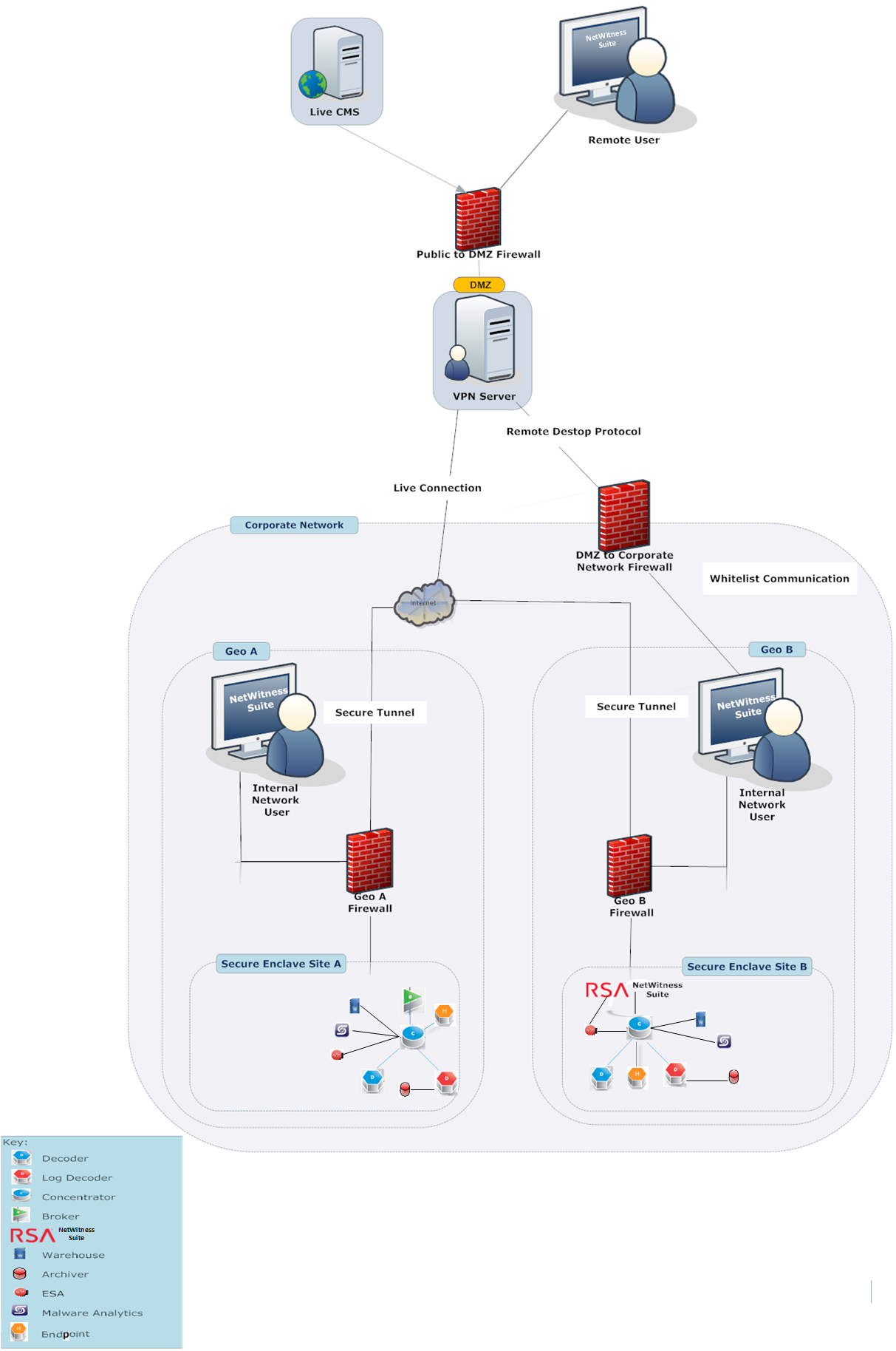
Security Configuration: Security Controls Map
Tags: Version 11.4
This topic describes the security controls map. An RSA NetWitness Platform deployment can consist of the following components:
- Decoder
- Log Decoder
- Concentrator
- Broker
- Log Collector
- Context Hub
- Malware
- ESA
- Archiver
- NetWitness Warehouse
- NetWitness Server
- External Warehouse - Hortonworks
- External CMS Library (Live)
- Endpoint
- UEBA Server
NetWitness Platform supports integration with products such as RSA NetWitness Platform 4.x and RSA Archer.
RSA recommends that you access the host on secure client machines within the network. If you must access the host through remote access, RSA recommends that you connect to the network through a secure VPN connection. Only allow remote access to NetWitness Platform hosts for secure maintenance using the Remote Desktop Protocol (RDP) through a secure VPN connection.
Caution: RSA recommends that you deploy the hosts in a secure location, where physical access to the hosts are restricted only to the personnel who manage the hosts.
Secure Enclave
To help protect NetWitness Platform against unauthorized authentication and access by end users or machines, RSA recommends that you deploy NetWitness Platform hosts such as Broker, Concentrator, and Decoder.
You can help create a secure enclave by separating the low security corporate network from the high security network with firewalls. To help create a secure enclave, RSA recommends that you:
- Implement basic physical security elements, policies, procedures, and processes for the low security network.
- Provide access to the hosts within the secure enclave through a secure virtual private network (VPN) tunnel only, such as IPSec tunnel, to establish encryption and authentication of all network traffic to and from the hosts.
Note: The client machines through which you access NetWitness Platform can be present outside of the Secure Enclave.
Secure Deployment Guidelines
To help ensure a secure deployment, RSA recommends that you:
- Deploy multiple hosts in the corporate network. The multiple hosts in the example are in two geographic locations and include the following components:
- NetWitness Platform
- Broker
- Packet Decoder
- Log Decoder
- Concentrator
- ESA
- Archiver
- NetWitness Warehouse
- Malware Analysis
- Endpoint
- UEBA Server
- Ensure that all the components are connected to the same subnetwork.
- Deploy firewalls at each site to ensure the secure transfer of data from an instance of NetWitness Platform at one site to another instance of NetWitness Platform located at a different site.
- Configure firewall rules to control all communication between different sites and other components in the network as depicted in the previous figure.
- Implement data transfer between sites using a secure tunnel IPSec.
The following figures show the deployment of multiple sites within a corporate network: