During this 3rd quarter of 2017, several malspam campaigns have been successfully distributing the Hancitor Downloader. The dropper uses strategies and obfuscation techniques on infected PCs, and has been observed delivering a variety of payloads.
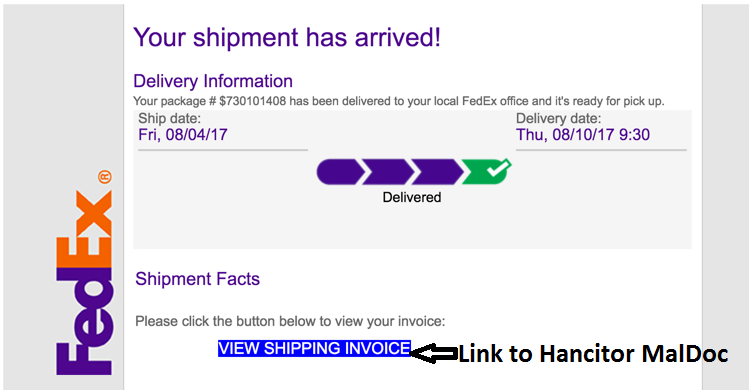
The early August "Shipment Arrived" malspam campaign masquerades as a FedEx shipment delivery notice and attempts to trick victims into clicking a link to download the invoice document which contains malicious macros. This variant uses native API calls within Visual Basic code to carve out and decrypt embedded malware from malicious Word documents. In this case the payload is Zbot.
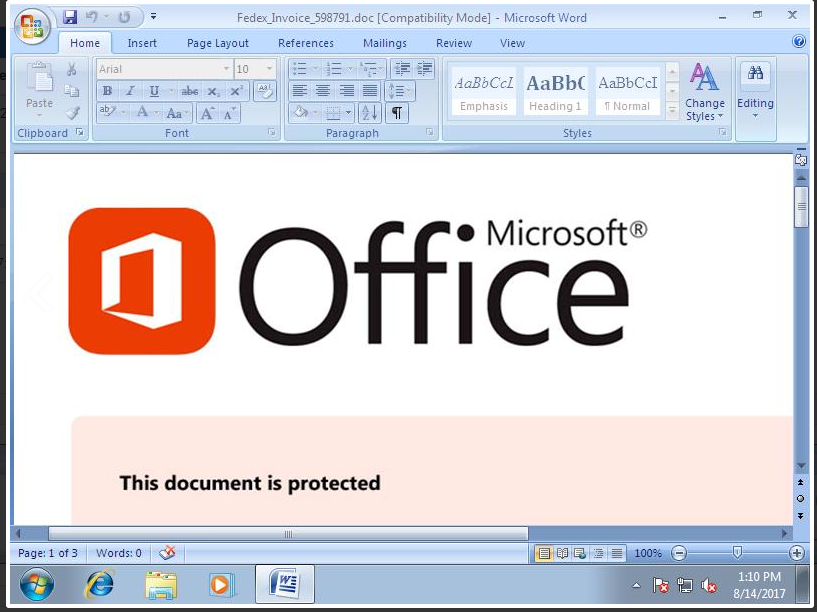
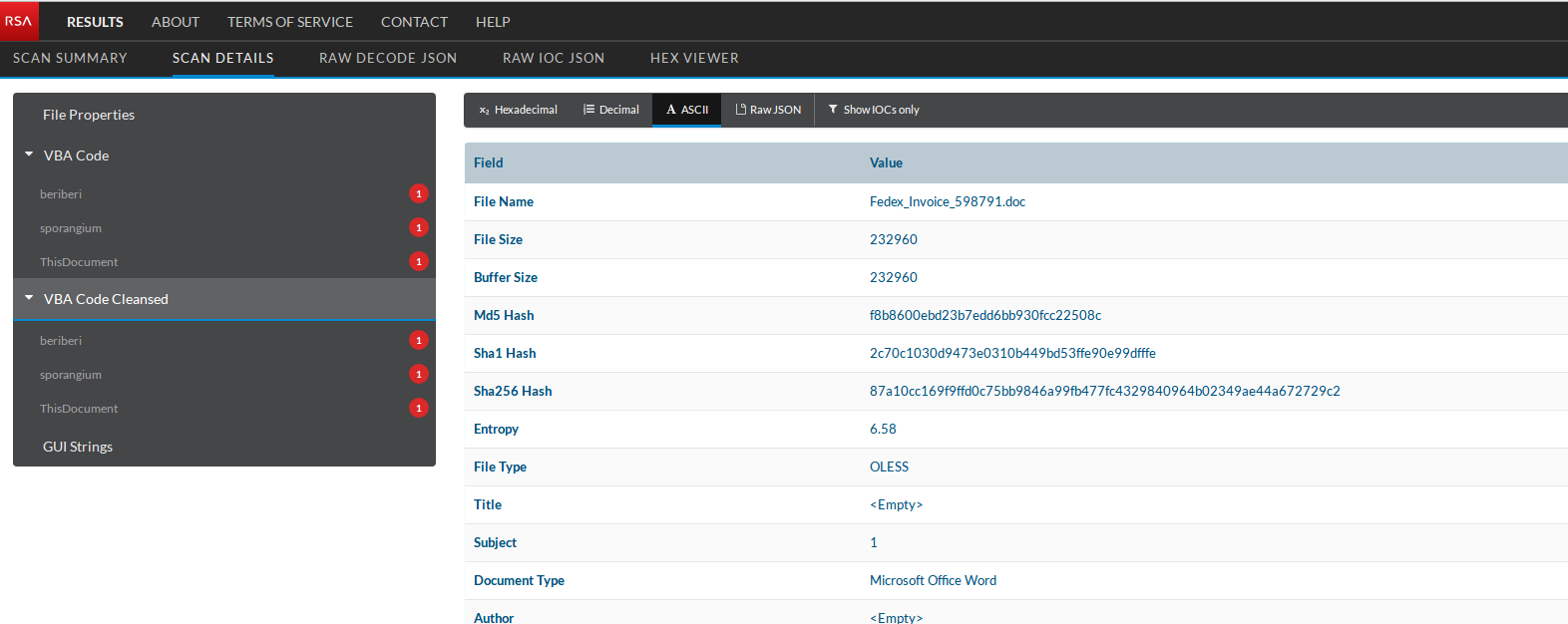
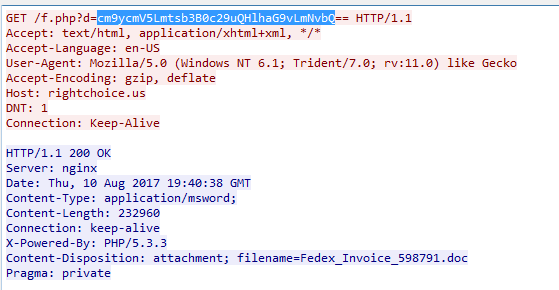
Once clicked on link, following word document gets downloaded.
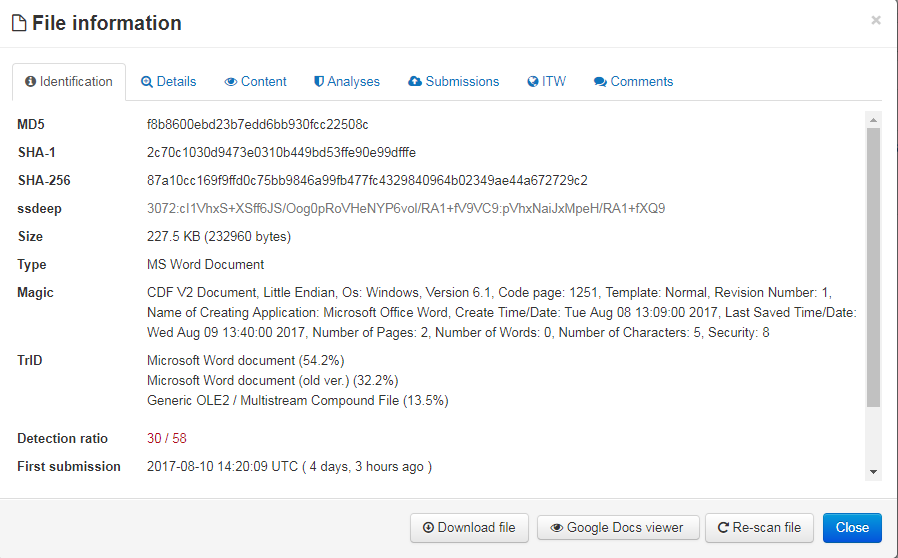
VirusTotal Analysis of Fedex_Invoice_598791.doc :
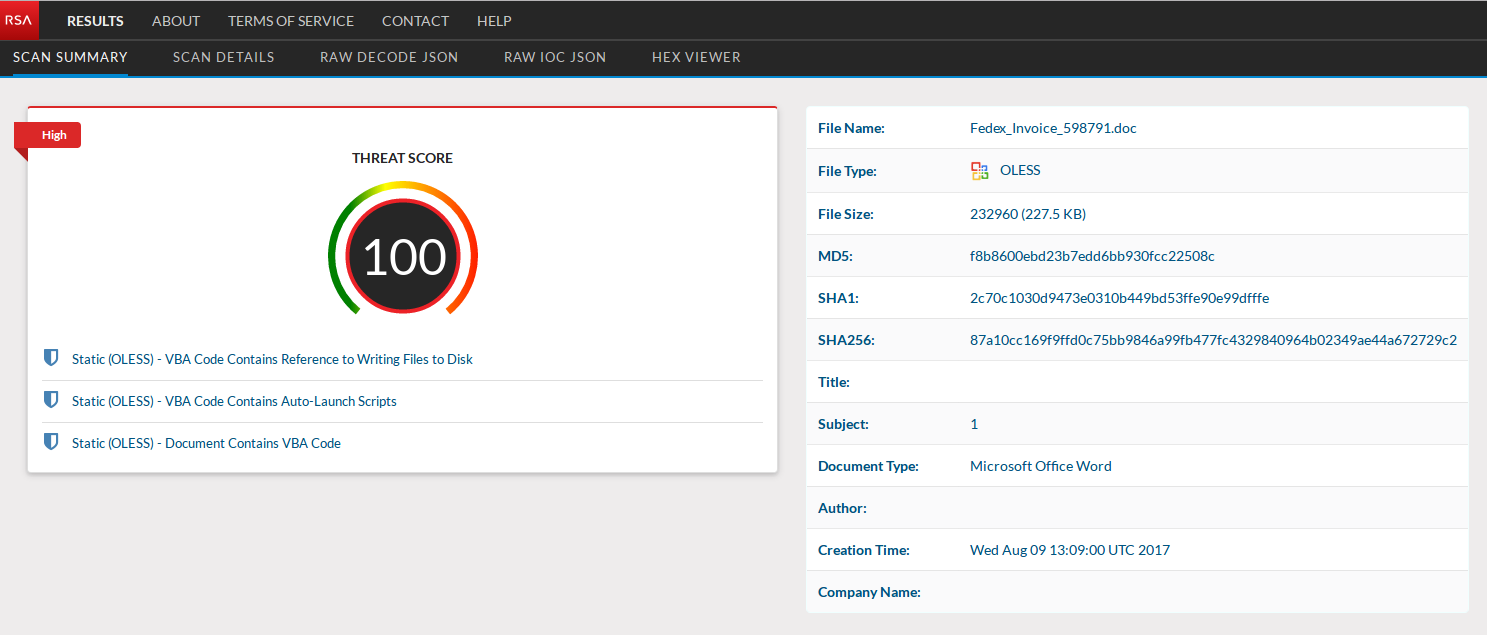
Submitting the delivery document to What's This File service shows more information about the malicious word document.
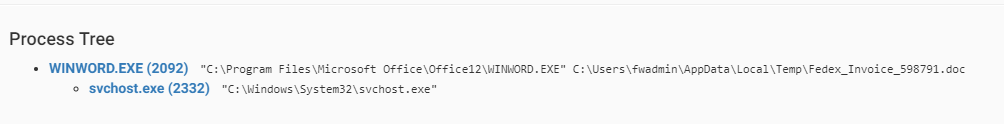
This activity is captured in the process tree below, which downloads and executes the payload:
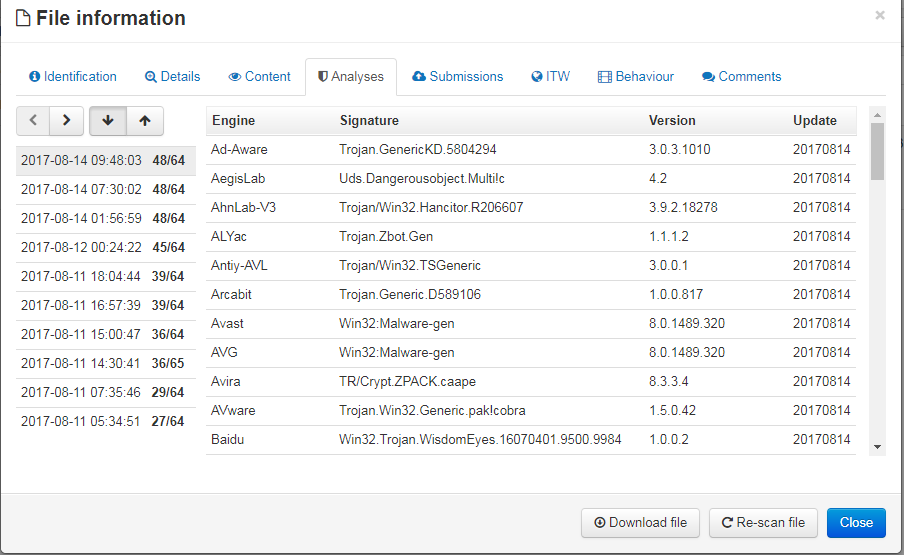
VirusTotal Analysis of the dropped file confirms that it’s Zbot Malware delivered by Hancitor:
More information about Zbot variants detection and RSA FirstWatch feed :
- https://community.rsa.com/community/products/netwitness/blog/2014/01/22/you-can-install-the-firstwatch-zbot-feed
- https://community.rsa.com/community/products/netwitness/blog/2014/04/30/the-kargen-zbot-and-how-to-detect-it
- https://community.rsa.com/community/products/netwitness/blog/2013/07/15/its-raining-zbot-new-variant-turns-to-cloud-for-strength
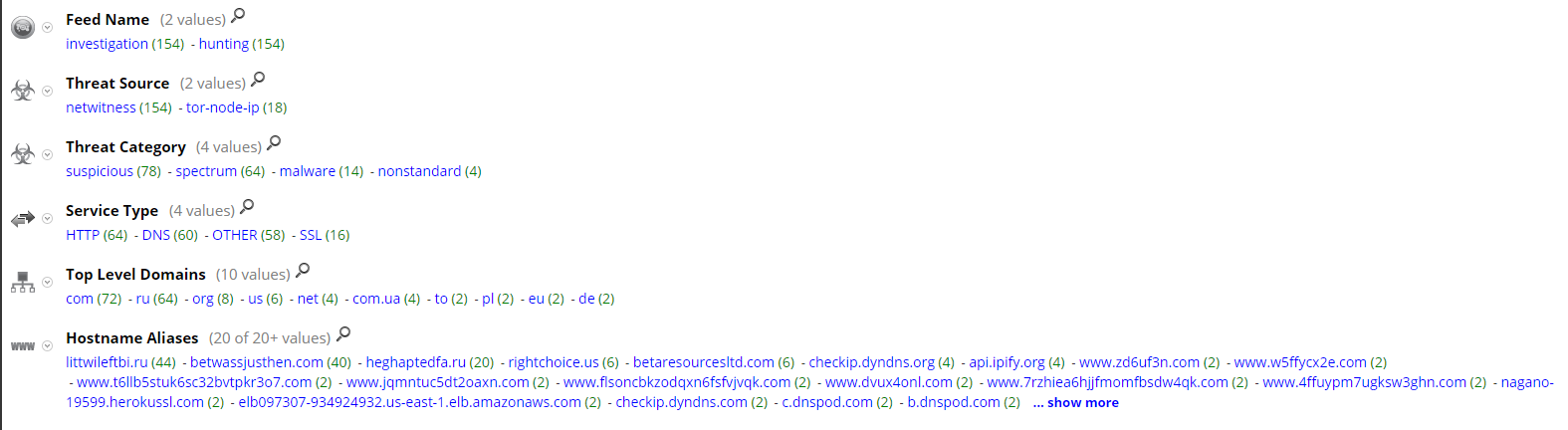
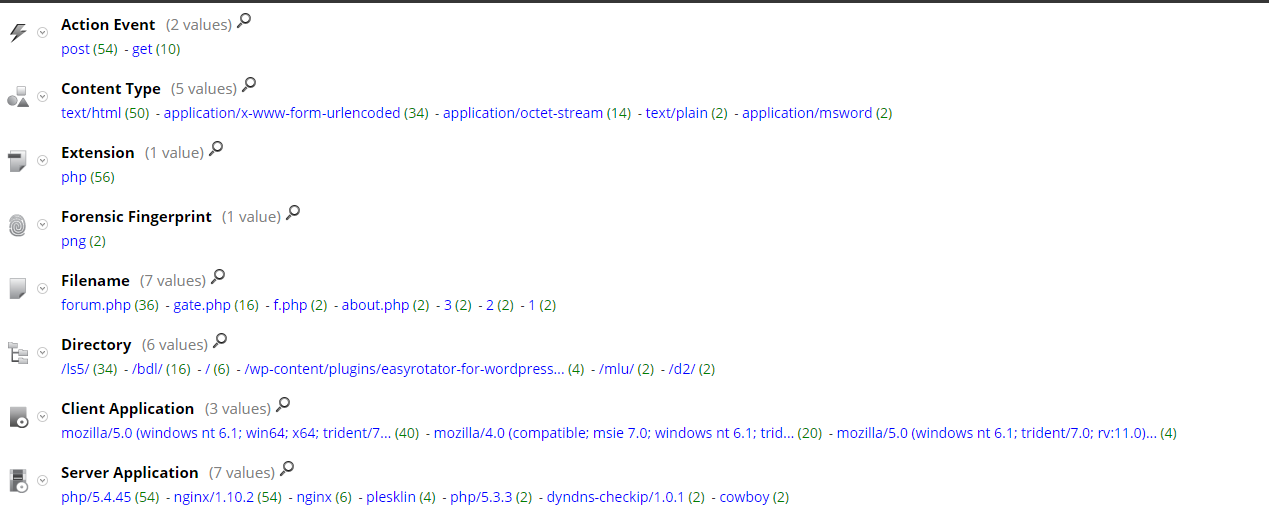
Current RSA NetWitness detection populates following meta:
Thanks go to Ahmed Sonbol and Kevin Stear for contributing to this threat advisory.

Reference:
