Author: Rajas Save
Introduction
In recent years, the cybersecurity landscape has witnessed the emergence of several sophisticated and notorious ransomware groups that have wreaked havoc on organizations worldwide.
Among these malevolent actors, the LockBit Ransomware-as-a-Service (RaaS) gang has emerged as a dominant force, inflicting significant harm on both large and small enterprises across the globe. Under the RaaS model, LockBit's modus operandi is to maintain the functionality of its ransomware variant and offer access to it, along with its infrastructure, to third-party hackers known as affiliates.
Originating as "ABCD" ransomware with files encrypted under the ".abcd" extension, LockBit has undergone significant metamorphosis since its initial detection in September 2019. Over the years, the threat actors responsible for LockBit have relentlessly updated and fortified the ransomwares' features and capabilities.
This blog delves into the nefarious activities of LockBit, shedding light on its evolution, tactics, and impact on the cybersecurity realm to gain deeper insights into their attack methods and countermeasures.
Impact
LockBit Ransomware and its affiliate network have had a significant negative impact on organizations worldwide. In 2022, LockBit was the most active global ransomware group and RaaS provider, claiming a high number of victims on their data leak site. Operating under the RaaS model, LockBit allows affiliates to access and deploy its ransomware in exchange for a share of the ransom payments. LockBit stands out from other RaaS groups by assuring timely payment to affiliates, engaging in negative publicity against competitors, and offering a user-friendly interface for its ransomware.
Since its first detection in September 2019, LockBit has continuously evolved, advertising itself as the fastest ransomware to encrypt files. It has similarities with Darkside/black matter ransomware and is believed to be part of the LockerGoga & MegaCortex family. LockBit's ransomware is self-spreading but targets specific companies capable of paying large ransoms.
In Australia, LockBit accounted for 18% of reported ransomware incidents from April 2022 to March 2023, while in Canada, it was responsible for 22% of attributed ransomware incidents in 2022. In New Zealand, LockBit ransomware comprised 23% of all ransomware reports in 2022. Within the United States, 16% of State, Local, Tribal, and Tribunal (SLTT) government ransomware incidents reported to the MS-ISAC were identified as LockBit attacks. The FBI has recorded approximately 1,700 LockBit attacks in the U.S. since 2020, with total ransoms paid to LockBit amounting to approximately $91 million since its first observed activity in the U.S. in January 2020. Operational activity related to LockBit in France has been significant, with the National Cybersecurity Agency of France (ANSSI) handling 80 alerts linked to LockBit ransomware, accounting for 11% of all ransomware cases handled by ANSSI since July 2020.
The impact of LockBit has also been felt through leak sites, where attackers publish names and captured data of victims who refuse to pay ransom or hush money. Up until Q1 2023, a total of 1,653 alleged victims were observed on LockBit leak sites. LockBit and its affiliates use the double extortion tactic, exfiltrating data and threatening to disclose it unless the ransom is paid. According to reports, LockBit was responsible for 15% of ransomware attacks in Q1 2022 and 40% in May 2022. Victims are concentrated in North America and Europe, with industries such as professional services, government, and manufacturing being most affected.
Of the confirmed incidents, LockBit 2.0 (LockBit Red) was observed 26 times, LockBit 3.0 (LockBit Black) 23 times, LockBit 21 times and the LockBit Green once. These figures and observations reflect the widespread impact of LockBit Ransomware across different regions and industries, highlighting the urgency for vigilant cybersecurity measures to counter this growing threat.
LockBit Ransomware Evolution
September 2019:
- ABCD Ransomware: The first observed activity of the ABCD ransomware, which later became the predecessor to LockBit. Notable for converting encrypted files to the ".abcd" extension.
January 2020:
- Emergence of LockBit: LockBit-named ransomware surfaced on Russian-language cybercrime forums, signaling its formal entry into the threat landscape.
June 2021:
- LockBit Version 2 (LockBit 2.0): LockBit 2.0, also known as LockBit Red, made its appearance, introducing StealBit, a built-in information-stealing tool that enhanced the ransomwares' capabilities.
October 2021:
- LockBit Linux-ESXi Locker Version 1.0: LockBit expanded its attack surface by introducing LockBit Linux-ESXi Locker version 1.0, enabling the ransomware to target Linux and VMware ESXi systems.
March 2022:
- LockBit Version 3 (LockBit 3.0): LockBit 3.0, also known as LockBit Black, emerged with similarities to BlackMatter and Alphv (also known as BlackCat) ransomware, showcasing its continuous evolution and sophistication.
September 2022:
- LockBit 3.0 Builder Leak: Non-LockBit affiliates gained access to LockBit 3.0 after its builder was leaked, amplifying the ransomware reach and impact.
January 2023:
- LockBit Green with Conti Code: LockBit Green arrived, incorporating source code from the notorious Conti ransomware, adding new capabilities and techniques to the ransomwares' arsenal.
April 2023:
- LockBit Targets macOS: LockBit ransomware encryptors were detected targeting macOS systems, signaling the ransomwares' expansion to new platforms and operating environments.
The timeline above showcases the evolutionary journey of LockBit Ransomware, highlighting its continuous development and adaptation to become a formidable threat in the realm of ransomware attacks. Connections between LockBit and BlackMatter, a rebranded form of the DarkSide ransomware, have been identified by researchers. LockBit's subsequent versions, including LockBit Green with Conti's source code integration and macOS targeting, demonstrate the group's ongoing innovation and determination to remain a significant player in the ransomware landscape. Additionally, the introduction of the world's first ransomware bug bounty program with Zcash cryptocurrency payment option showcases the group's pursuit of innovation and expansion of its operations.
LockBit Ransomware Technical Analysis
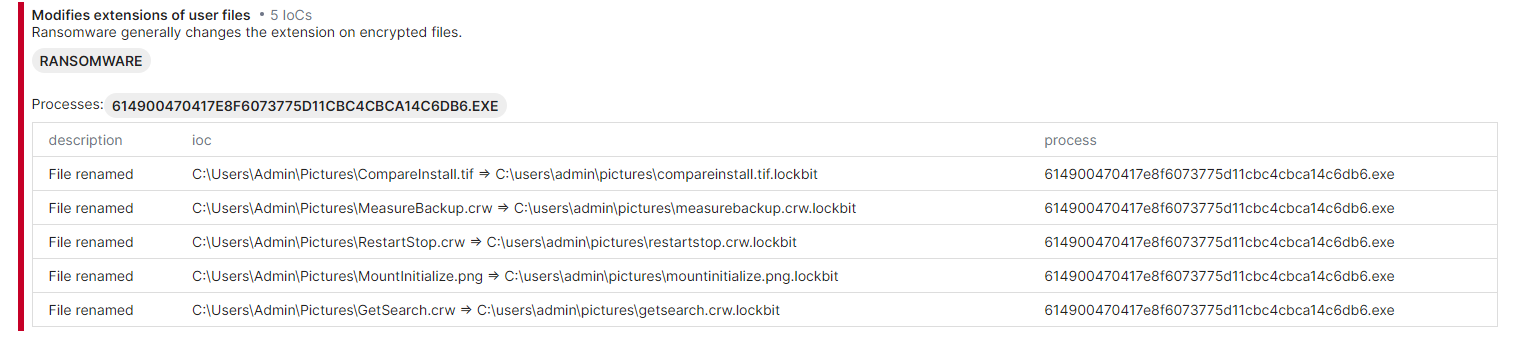
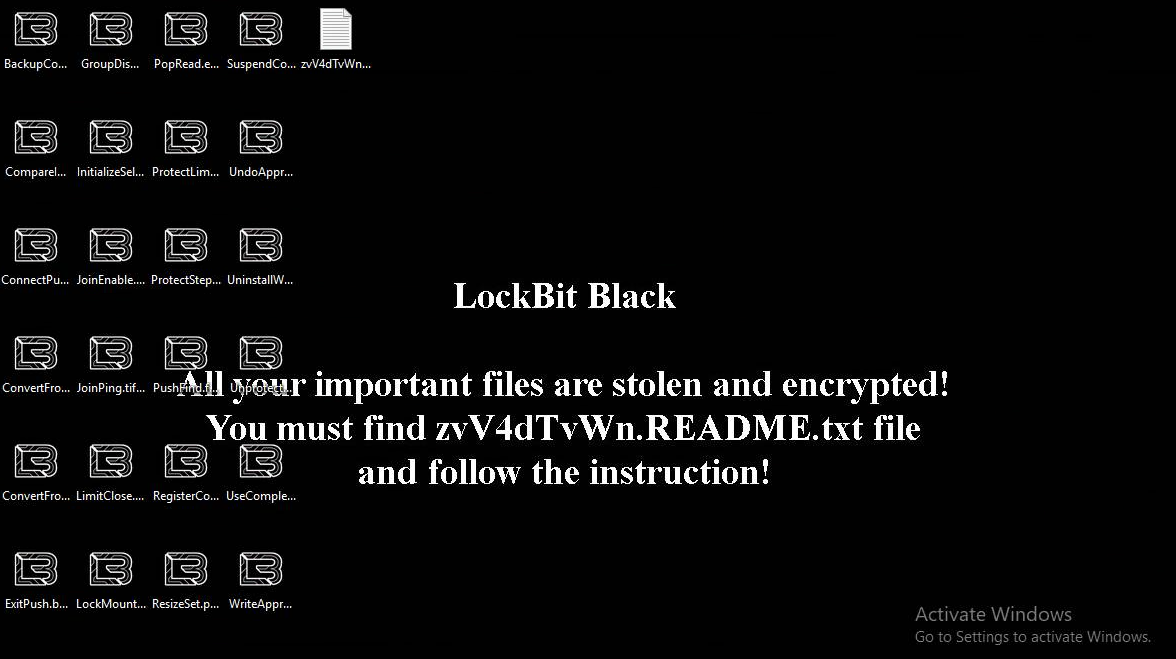
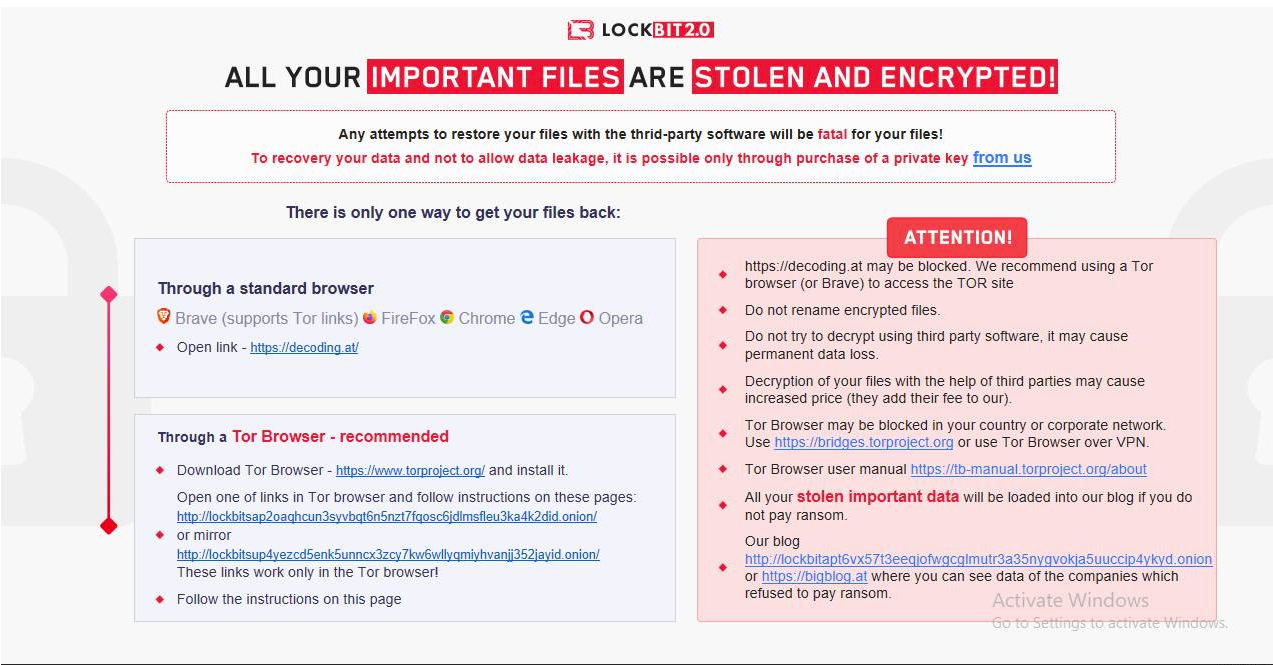
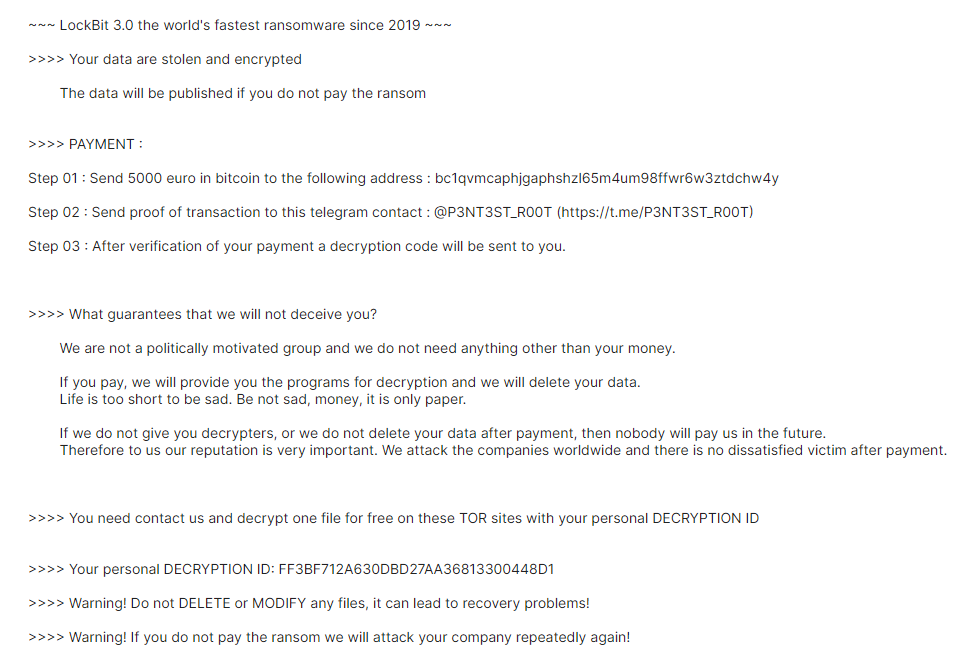
Through the study of multiple different samples obtained from various versions of LockBit across different time windows, we gain valuable insights into the attack stages and modus operandi of this formidable malware. Detonations of these samples provide crucial information (screenshots below) that offer a clear understanding of the sophisticated attack stages employed by LockBit Ransomware.
LockBit ransomware is a sophisticated threat that employs various techniques to compromise and encrypt victim networks. The attack follows a multi-stage process, starting with initial access and network expansion, followed by system information collection and encryption, and culminating in ransomware payload execution and persistence.
Initial Access and Network Expansion:
LockBit gains initial access through methods like SMB brute forcing, as observed in the emerging LockBit campaign. After obtaining access, the attackers deploy credential dumping tools like Mimikatz to collect login credentials and privilege escalation tools like ProxyShell to gain higher privileges.
To move laterally across the network, LockBit uses tools like PsExec or Cobalt Strike for remote execution.
Additionally, it employs obfuscated PowerShell and batch scripts to establish persistence and evade detection, as described in the Seqrite blog.
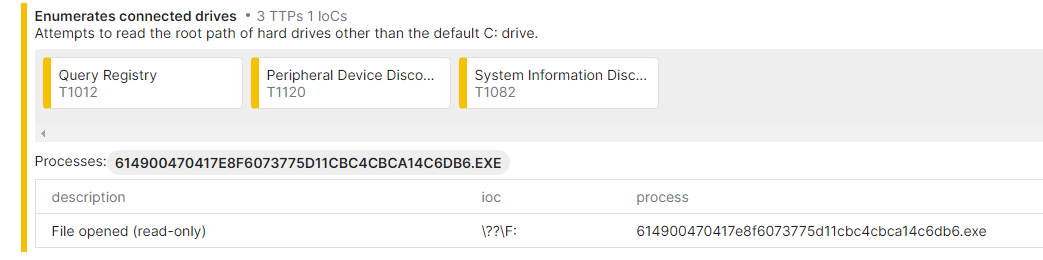
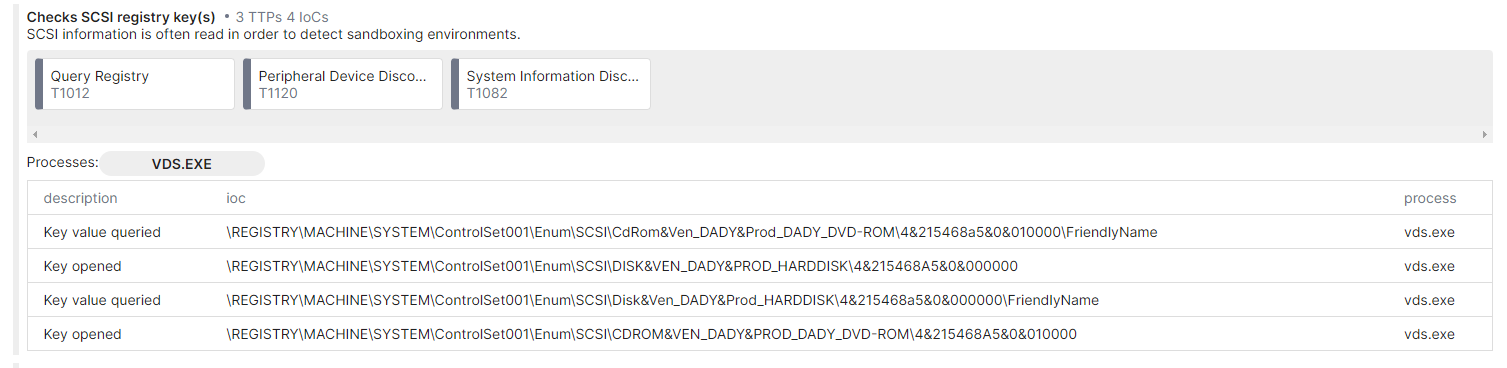
System Information Collection and Encryption:
LockBit ransomware, like LockBit Black, collects essential system information like hostname, domain details, and network configurations. It uses this data to identify valuable targets for encryption. The ransomware employs a multi-threaded approach to encrypt data rapidly, focusing on shared drives. Examples of this behavior can be seen in the attack chain and anti-forensic activity of LockBit Black.
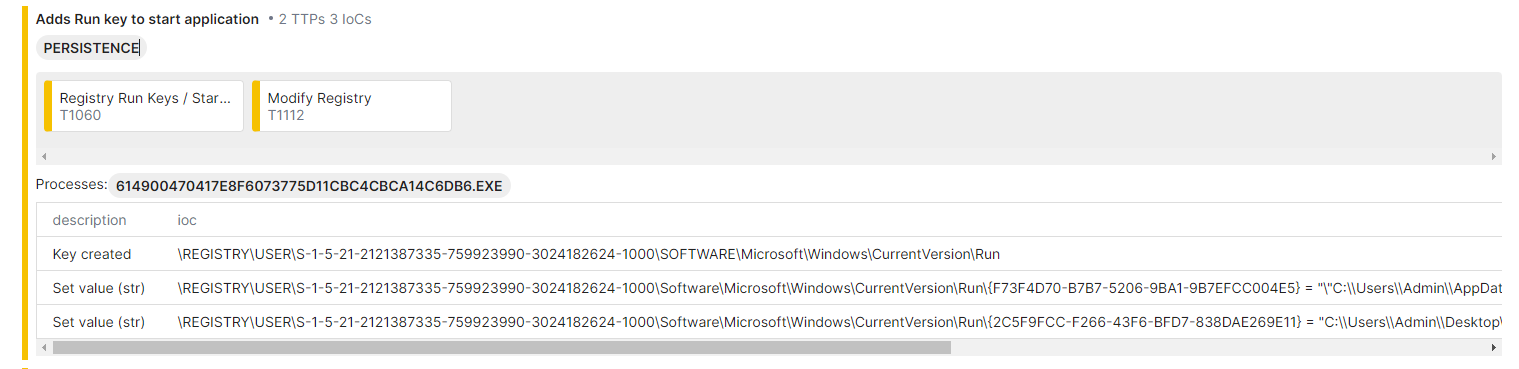
Ransomware Payload Execution and Persistence:
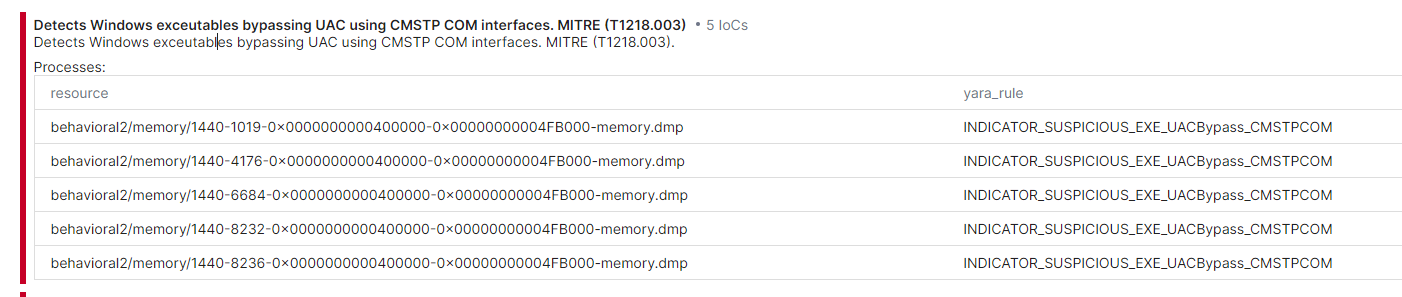
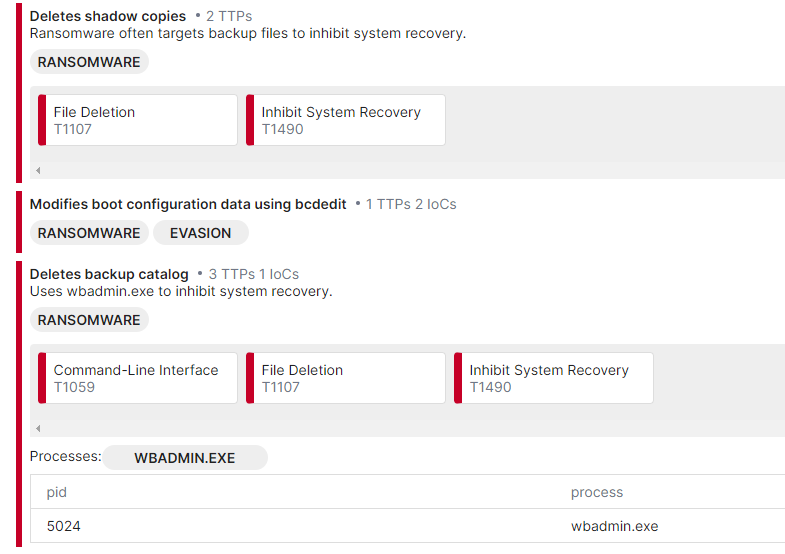
LockBit employs several techniques for persistence. It disables Windows volume shadow copies and deletes system and security logs to hinder recovery efforts. The ransomware uses UAC bypass methods, including abusing the legitimate fodhelper.exe, to elevate privileges without user approval. Persistence mechanisms involve modifying RDP and authentication settings, as evidenced in the Seqrite blog. LockBit also employs SysInternals Autologon to ensure automatic logins after system reboots.

The series of commands mentioned appears to be a part of the execution flow of the LockBit ransomware.
"C:\Windows\System32\cmd.exe" /c vssadmin delete shadows /all /quiet & wmic shadowcopy delete & bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no
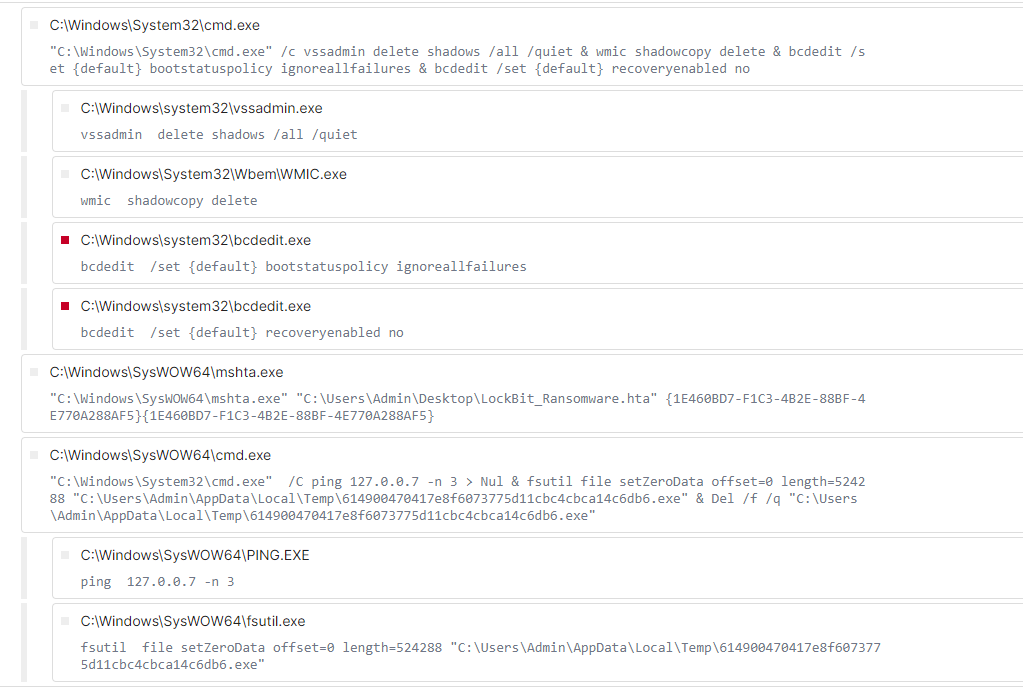
This is a compound command that performs multiple operations in sequence, separated by the & symbol. It consists of the following commands:
- vssadmin delete shadows /all /quiet: This command is used to delete all Volume Shadow Copies (VSS) on the system silently, potentially removing backup copies that could be used to restore files after encryption.
- wmic shadowcopy delete: This command invokes Windows Management Instrumentation (WMI) to delete any remaining shadow copies, further preventing data recovery options.
- bcdedit /set {default} bootstatuspolicy ignoreallfailures: This command modifies the boot status policy to ignore all boot failures, likely to prevent the system from displaying any error messages during the ransomware execution process.
- bcdedit /set {default} recoveryenabled no: This command disables the Windows Recovery Environment (WinRE), another measure to hinder recovery attempts.
This is another compound command that performs multiple actions sequentially:
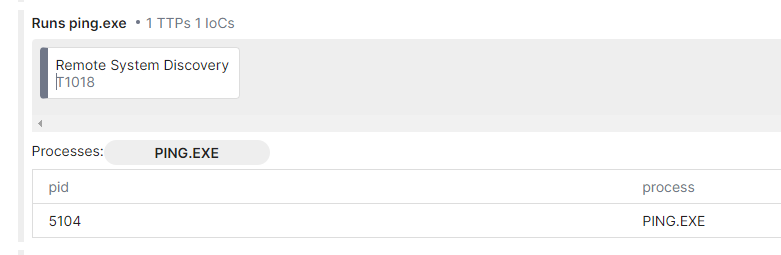
"C:\Windows\System32\cmd.exe" /C ping 127.0.0.7 -n 3 > Nul & fsutil file setZeroData offset=0 length=524288 "C:\Users\Admin\AppData\Local\Temp\614900470417e8f6073775d11cbc4cbca14c6db6.exe" & Del /f /q "C:\Users\Admin\AppData\Local\Temp\614900470417e8f6073775d11cbc4cbca14c6db6.exe"
- ping 127.0.0.7 -n 3: This command sends three ping requests to the loopback address (127.0.0.1) to introduce a delay in the script execution.
- fsutil file setZeroData offset=0 length=524288 "C:\Users\Admin\AppData\Local\Temp\x.exe": This command appears to zero-fill (overwrite with zeros) a specific portion of the file located at "C:\Users\Admin\AppData\Local\Temp\x.exe".
- This might be an attempt to remove traces of the ransomware executable.
- Del /f /q "C:\Users\Admin\AppData\Local\Temp\x.exe": This command is used to forcefully delete the same file mentioned above.
These commands are indicative of LockBit ransomware's attempt to carry out multiple activities, including disabling recovery options, deleting backup copies, and attempting to cover its tracks by removing traces of its executable. The ransomware aims to maximize its impact by hindering any means of data recovery or system restoration for the victim.
Ransom Note and Anti-Forensic Activities:
Upon completing the encryption process, LockBit changes the file icons with its own icon. It then drops a ransom note, altering the user's desktop wallpaper with instructions on how to contact the attackers. LockBit Black has been observed engaging in anti-forensic activities, including clearing event logs, terminating multiple tasks, and deleting services simultaneously.
MITRE ATT&CK Information
Following are some of the commonly observed MITRE Techniques used by LockBit2 and LockBit3 –
Initial Access
- Phishing(T1566) – Common use of phishing and spear phishing to gain access to victims’ networks.
- Exploit Public-Facing Application(T1190) - Exploiting vulnerabilities in internet-facing systems to gain access to victims’ systems.
Execution
- Command and Scripting Interpreter: Windows Command Shell (T1059.003) - Batch scripts to execute malicious commands.
- System Services: Service Execution (T1569.002) - LockBit 3.0 uses PsExec to execute commands or payloads.
Persistence
- Boot or Logon AutoStart Execution (T1547) - Enables automatic logon
Privilege Escalation
- Abuse Elevation Control Mechanism (T1548) – Uses User Account Control (UAC) bypass techniques.
- Boot or Logon AutoStart Execution (T1547) - Enable automatic logon for privilege escalation.
Defense Evasion
- Impair Defenses: Disable or Modify Tools (T1562.001) - Modifies and/or disables security tools including EDR and antivirus to avoid possible detection of malware, tools, and activities.
- Indicator Removal: Clear Windows Event Logs (T1070.001) - LockBit executable clears the Windows Event Logs files.
- Indicator Removal: File Deletion (T1070.004) - Delete itself from the disk.
- Obfuscated Files or Information (T1027) - Sends encrypted host and bot information to its command and control (C2) servers.
Discovery
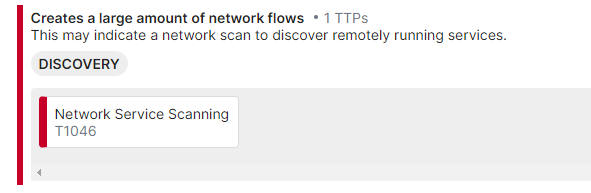
- Network Service Discovery (T1046) - LockBit uses Network Scanners, Advanced IP Scanners, or Advanced Port Scanners to scan target networks.
- System Information Discovery (T1082) - Enumerate system information to include hostname, host configuration, domain information, local drive configuration, remote shares, and mounted external storage devices.
Lateral Movement
- Remote Services: Server Message Block (SMB)/Admin Windows Shares (T1021.002) - Targets SMB shares for lateral movement.
Impact
- Data Destruction (T1485) - Deletes log files and empties the recycle bin.
- Data Encrypted for Impact (T1486) - Encrypts data on target systems to interrupt availability to system and network resources.
- Defacement: Internal Defacement (T1491.001) - Changes the host system’s wallpaper and icons to the LockBit 2.0/3.0 wallpaper and icons, respectively.
List of extracted IOCs are attached to this post. Stay tuned for new IOCs, rules, and other content that will be added via Netwitness Live.
Conclusion
With the infamous Conti ransomware group disbanded due to source code leaks during the Russia-Ukraine war, LockBit has risen to the forefront as a leading ransomware threat. Continuously evolving and expanding its tactics and capabilities, LockBit remains a formidable adversary, posing a significant challenge for cybersecurity professionals and organizations worldwide. As cyber threat actors continue to develop their own versions, it becomes crucial for organizations to take proactive steps to ensure their protection against these evolving threats.
Thanks a lot @Will_G and @ArthurF for valuable feedback. And thank you @Sarthak for initial research efforts.
References
- https://www.cisa.gov/sites/default/files/2023-06/aa23-165a_understanding_TA_LockBit_0.pdf
- Hunting LockBit Variations using Logpoint
- Lockbit change de couleur - GLIMPS
- Can You See It Now? An Emerging LockBit Campaign | FortiGuard Labs
- Recorded Future Triage
- PolySwarm - Crowdsourced threat detection
- vxintel | Dashboard
- https://www.seqrite.com/blog/uncovering-lockbit-blacks-attack-chain-and-anti-forensic-activity
- https://analyst1.com/ransomware-diaries-volume-1
