Authors: Rajas Save (@RajasSave) and Sarthak Duggal (@Sarthak)
Introduction
In mid-January, reports started to surface about multiple cyber attacks against Ukrainian government websites. Hacktivism was spreading its wings in the form of DDoS attacks and Data Wipers. Relatively new, Data Wipers’ sole purposes are to destroy data beyond recovery. These tools can destroy large distributed systems and networks. This in turn can harm large and trivial organizations by attacking their availability, making them highly destructive malware.
This is not the first time Data Wipers were reported. They were first seen in 2012 in the form of the Shamoon Malware family and then resurfaced in 2016; starting January 2022, use of Wipers has exponentially increased during the Russia-Ukraine conflict.
According to MSTIC, this malware is designed to look like ransomware but lacks a ransom recovery mechanism. It’s intended to be destructive and is designed to render targeted devices inoperable rather than to obtain a ransom. In the same month, a new malware family called WhisperGate was reported by CISA, followed by multiple researchers. WhisperGate and its family of malware are prime examples of ongoing Hacktivism with non-financial destructive agendas.
Chronology of Data Wipers
Amid Russia’s invasion of Ukraine, multiple cyberattacks have allegedly surfaced, and various cybersecurity warnings continue to appear from various governments as well as cyber security organizations.
-
Between January 13th to 15th, 2022, around 70 Ukrainian government websites, including the Ministry of Foreign Affairs and the Ministry of Education, were attacked. “Be afraid and expect the worst” was a message posted by hackers.
- On January 15th , 2022, in the special report the Microsoft Threat Intelligence Center (MSTIC) disclosed that malware, known as WhisperGate, was being used to target organizations in Ukraine. According to Microsoft, WhisperGate is intended to be destructive and is designed to render targeted devices inoperable.
- On February 15th, 2022, Ukraine’s State Service of Special Communications, and Information Protection of Ukraine (SSSCIP) confirmed that a distributed denial of service (DDoS) attack hit the websites of Ukraine's defense ministry and armed forces and the websites of two Ukrainian banks.
-
On February 23rd, 2022, Multiple government sites and organizations in the financial and aviation sectors were targeted by a new type of wiper known as Hermetic Wiper.
-
On February 25th, 2022, attacks involving Isaac Wiper were reported against several government entities, followed by Candy Wiper in early March.
What is a Data Wiper?
As mentioned above, Data Wipers are remarkably like ransomware but without any recovery modules. Data wipers like ransomware iterate through the file system, with the intention of corrupting or encrypting files. Unlike ransomware, however, wipers destroy data using multiple techniques like deleting files, overwriting initial bytes, or corrupting the Master Boot Record (MBR) or Master File Table (MFT).
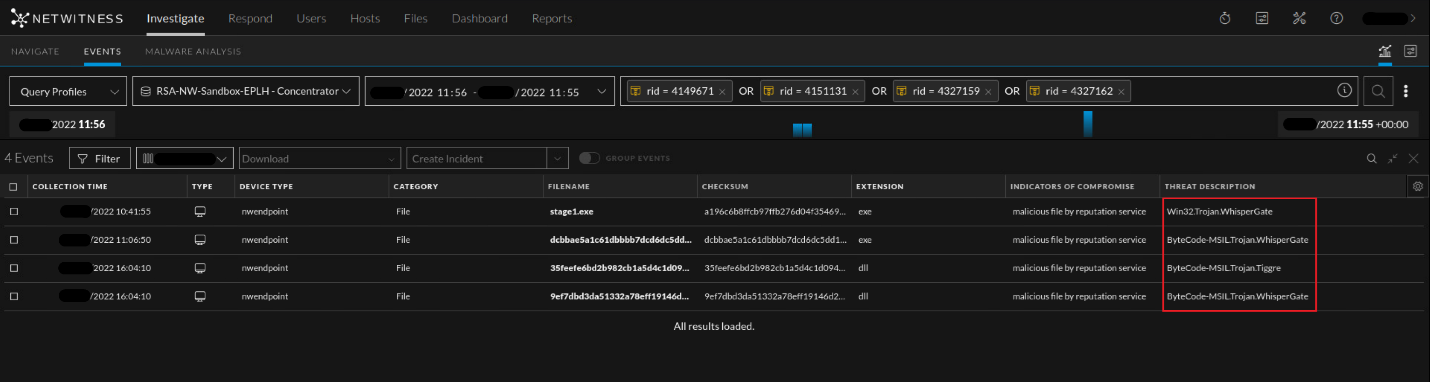
According to Microsoft Threat Intelligence Center (MSTIC)’s original advisory, WhisperGate malware is a multi-stage data wiper. It executes from Windows working directories, such as C:\PerfLogs, C:\ProgramData, C:\, and C:\temp etc., and is often named stage1.exe. Although initial delivery mechanisms are unclear, according to Cisco Talos, attackers had access to their victim’s network well in advance using a sophisticated advanced persistent threat operation (APT).
Stage 1 executes using Impacket and overwrites the master boot record (MBR). It also loads the fake ransom note as a string on the MBR by using WriteFile() which contains a Bitcoin wallet and Tox ID.
Read more about Detecting Impacket with Netwitness Endpoint
Your hard drive has been corrupted.
In case you want to recover all hard drives
of your organization,
You should pay us $10k via bitcoin wallet
1AVNM68gj6PGPFcJuftKATa4WLnzg8fpfv and send message via
tox ID 8BEDC411012A33BA34F49130D0F186993C6A32DAD8976F6A5D82C1ED23054C057ECED5496F65
with your organization name.
We will contact you to give further instructions.
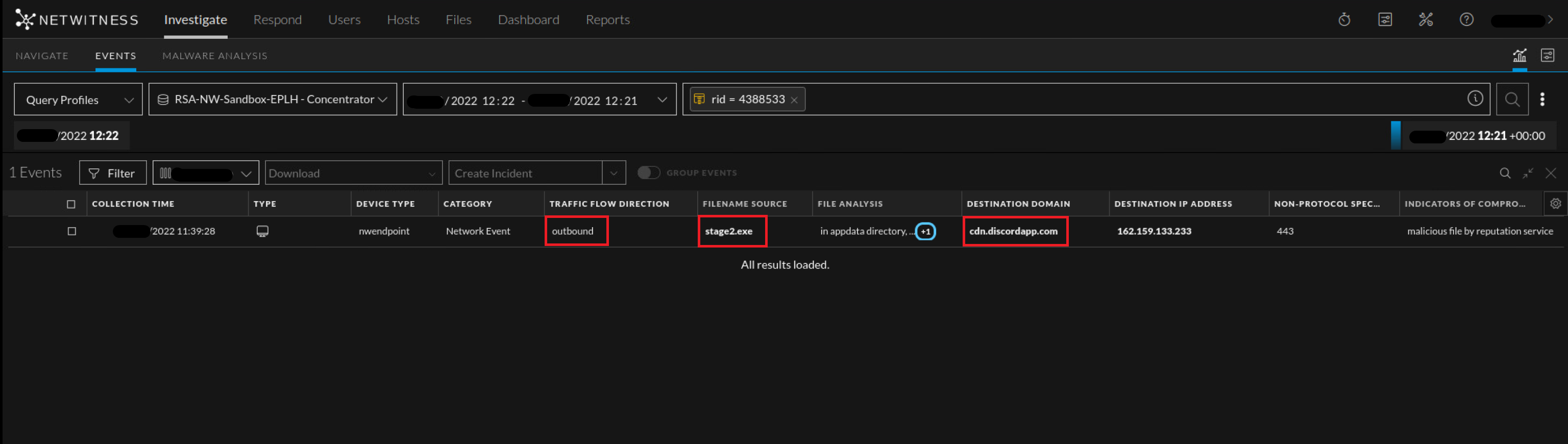
In Stage 2, upon execution, it connects to a discord server to download a malicious DLL payload as an image file using steganographic techniques to avoid AV detection. It uses a download link hardcoded in the Stage 2 binary executable.
The binary uses a sleep call with 10 seconds as a parameter as an added way of evading detection.
Stage 3 is then downloaded and executed in memory of the target system. This malicious DLL is coded in C# and obfuscated using packing software. Upon execution, 1st it tries to stop the Windows Defender service followed by deletion of the “C:\ProgramData\Microsoft\Windows Defender”. The code has a list of approximately 120 file extensions that will be encrypted if file extensions match. It destroys the filesystem by overwriting the contents of the file with a fixed number of bytes and renaming each file with a random four-byte extension.
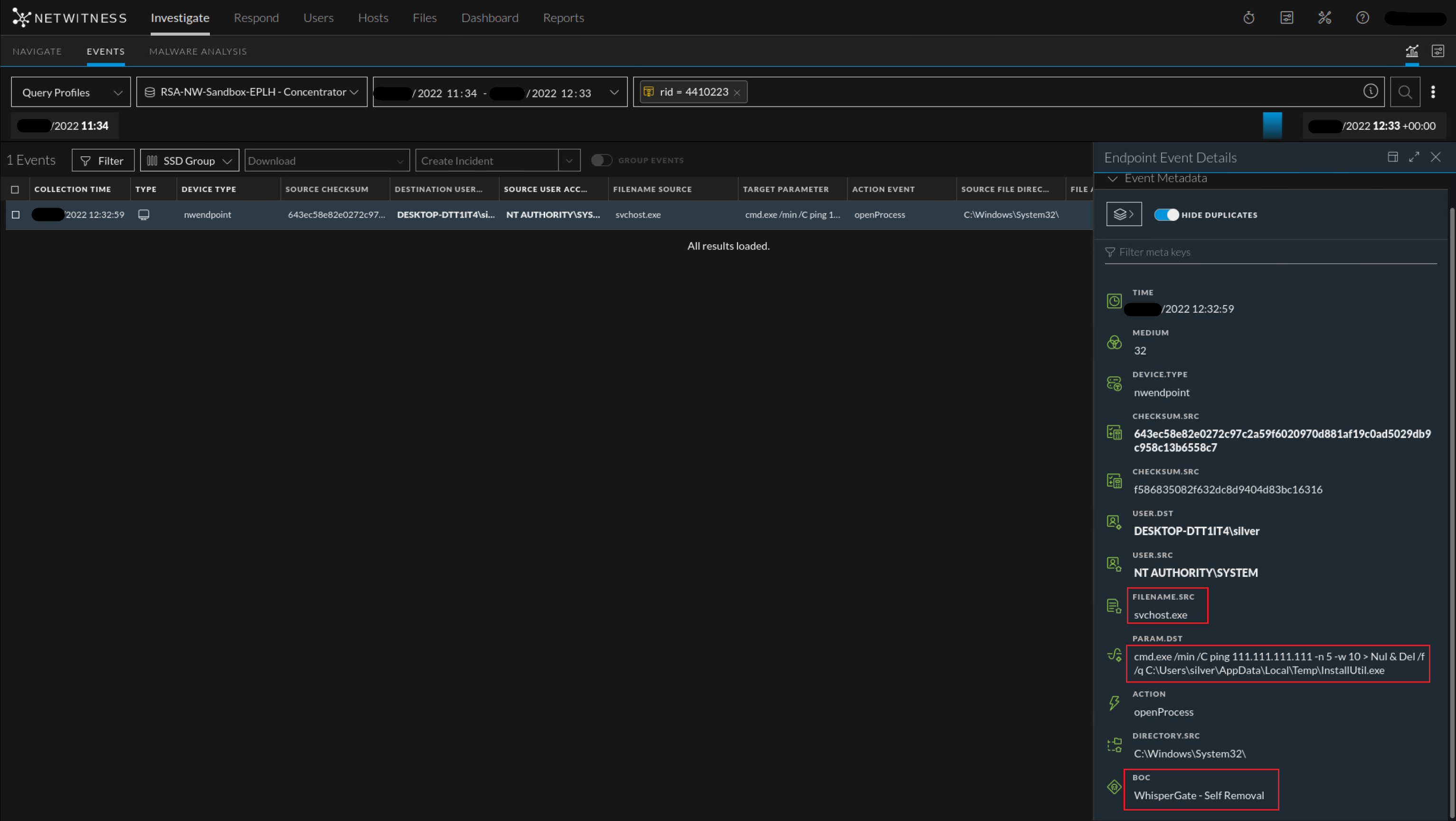
A few variants use a Ping command in loop along with self-delete commands after successful termination from the file corruption module.
MITRE Mapping:
Detailed MITRE breakdown of WhisperGate can be found here - WhisperGate, Software S0689 | MITRE ATT&CK
These are few important MITRE techniques we have observed during analysis:
- T1059.001/.003/.005 - Command and Scripting Interpreter: PowerShell - WhisperGate used PowerShell, Windows Command Shell as well as VB to support multiple actions including execution and defense evasion.
- T1485 - Data Destruction
- T1140 - Deobfuscate/Decode Files or Information - WhisperGate de-obfuscate downloaded files stored in reverse byte order and decrypt embedded resources using multiple XOR operations.
- T1561.001/.002 - Disk Wipe: Disk Content Wipe and Disk Structure Wipe
- T1083 - File and Directory Discovery - WhisperGate searches for files based on hardcoded file extensions.
- T1562.001 - Impair Defenses: Disable or Modify Tools - WhisperGate disables Windows Defender service.
- T1036 - Masquerading - WhisperGate has been disguised as a JPG extension to avoid detection as a malicious PE file.
- T1027 - Obfuscated Files or Information
- T1542.003 - Pre-OS Boot: Bootkit - WhisperGate overwrites the MBR with a bootloader part that performs destructive wiping operations on hard drives and displays a fake ransom note when the host boots.
- T1055 - Process Injection
- T1497.003 - Time Based Evasion - WhisperGate can pause for 20 seconds to bypass antivirus solutions.
NetWitness Analysis:
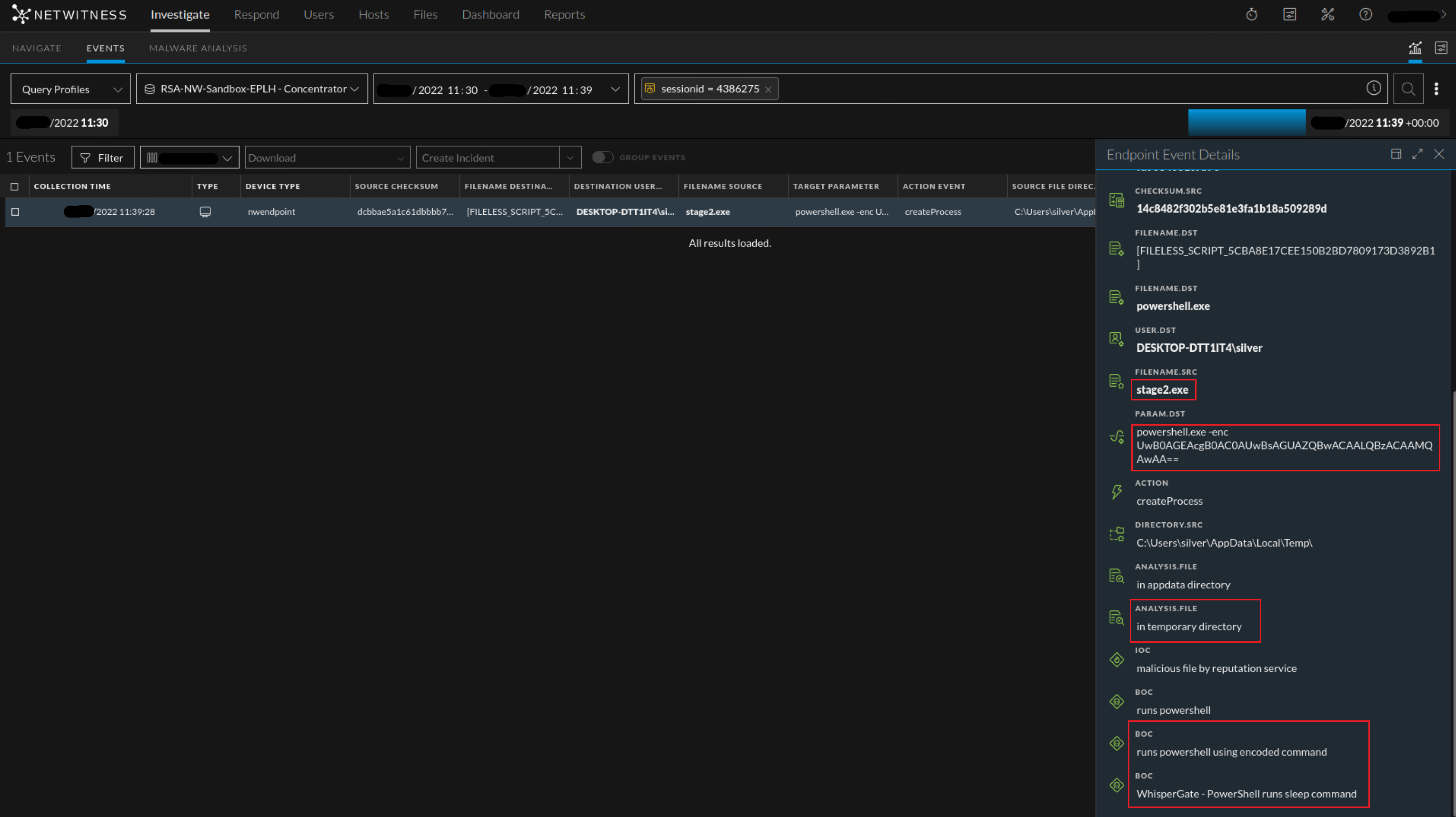
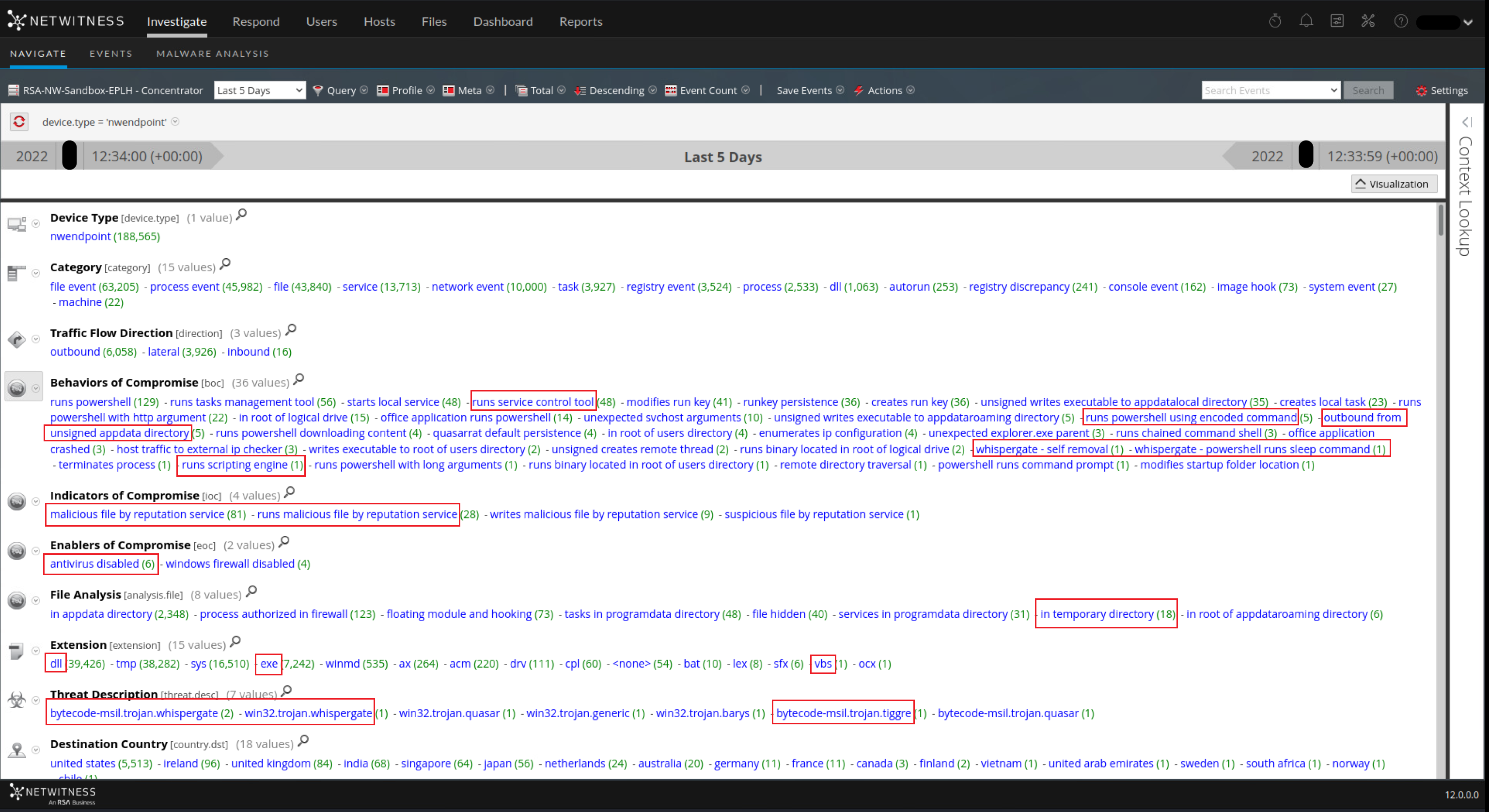
After analyzing samples from various sources and advisories, the following are few already existing NetWitness detections that can be useful for WhisperGate detection –
- boc = 'possible impacket host activity (wmiexec.py)'
- boc = 'evades scanning within windows defender'
- boc = 'stops security service'
- analysis.file = 'in temporary directory'
- boc = 'outbound from unsigned temporary directory'
- boc = 'runs powershell using encoded command'
- boc = 'runs scripting engine'
- boc = 'runs service control tool'
- eoc = 'antivirus disabled'
As a result of this investigation, NetWitness Threat Research team has added following new endpoint detections specific to WhiperGate and associated families -
- [Community] Possible Suspicious Access Read of Master Boot Record
- WhisperGate - PowerShell runs sleep command
- WhisperGate - AdvancedRun Kills Defender
- WhisperGate - Self Removal
Conclusion and Recommendations:
Our hope with this blog is to provide a quick overview of Data Wipers, particularly ‘WhisperGate’, and its recent spike in use as a destructive malware. Hopefully, this information will aid and enable analysts in their efforts to identify and respond to similar attacks more quickly. The NetWitness Application Rules in this post should provide defenders with alerts that can be used as strong indicators of suspicious activity within their own environments.
In addition to this, as recommended by CISA, common well-known strategies can be followed to strengthen an organization’s resilience against these destructive malwares such as:
- Network segmentation and access control
- Monitoring from multiple sources such as Logs, Packets and Endpoint to identify anomalies sooner than later
- Monitoring files closely along with System and Application Hardening
- Practicing regular backups and recovery methodologies.
Thanks goes to fellow researcher @Sarthak for contributing to this effort.
References:
- Update: Destructive Malware Targeting Organizations in Ukraine | CISA
- Destructive malware targeting Ukrainian organizations - Microsoft Security Blog
- Microsoft Special Report: Ukraine | An overview of Russia’s cyberattack activity in Ukraine
- WhisperGate: A destructive malware to destroy Ukraine computer systems - Infosec Resources
- Technical Analysis of the WhisperGate Malicious Bootloader | CrowdStrike
- The Anatomy of Wiper Malware, Part 1: Common Techniques | CrowdStrike
- cyberattaks timeline | Epthinktank | European Parliament
- Russia-linked cyberattacks on Ukraine: A timeline | CSO Online
- Detecting Impacket with Netwitness Endpoint - NetWitness Community - 683062
